Cisco Meraki vs. Aruba: Ein technischer Vergleich für Gast-WiFi
Ein maßgeblicher technischer Vergleich von Cisco Meraki und HPE Aruba für Enterprise-Gast-WiFi-Implementierungen. Dieser Leitfaden bietet IT-Managern und Architekten umsetzbare Einblicke in Architektur, Authentifizierung, Netzwerksegmentierung und hardwareunabhängige Analyseintegration.
Diesen Leitfaden anhören
Podcast-Transkript ansehen
- Zusammenfassung für die Geschäftsleitung
- Technischer Deep-Dive: Architektur und Authentifizierung
- Architektur der Managementebene
- Gast-Authentifizierung und Netzwerkzugriffskontrolle
- Implementierungsleitfaden: Best Practices für die Enterprise-Bereitstellung
- 1. Netzwerksegmentierung und VLAN-Design
- 2. HF-Design für hohe Dichte
- Fehlerbehebung & Risikominderung
- Häufige Fehlerursachen
- ROI & Geschäftlicher Nutzen
- Hören Sie das technische Briefing

Zusammenfassung für die Geschäftsleitung
Für CTOs und Netzwerkarchitekten in den Bereichen Gastgewerbe, Einzelhandel und öffentlicher Sektor ist die Auswahl der richtigen drahtlosen Enterprise-Infrastruktur eine entscheidende Entscheidung, die den Betriebsaufwand und das Gasterlebnis für den nächsten Aktualisierungszyklus bestimmt. Dieser technische Leitfaden vergleicht die beiden Marktführer: Cisco Meraki und HPE Aruba.
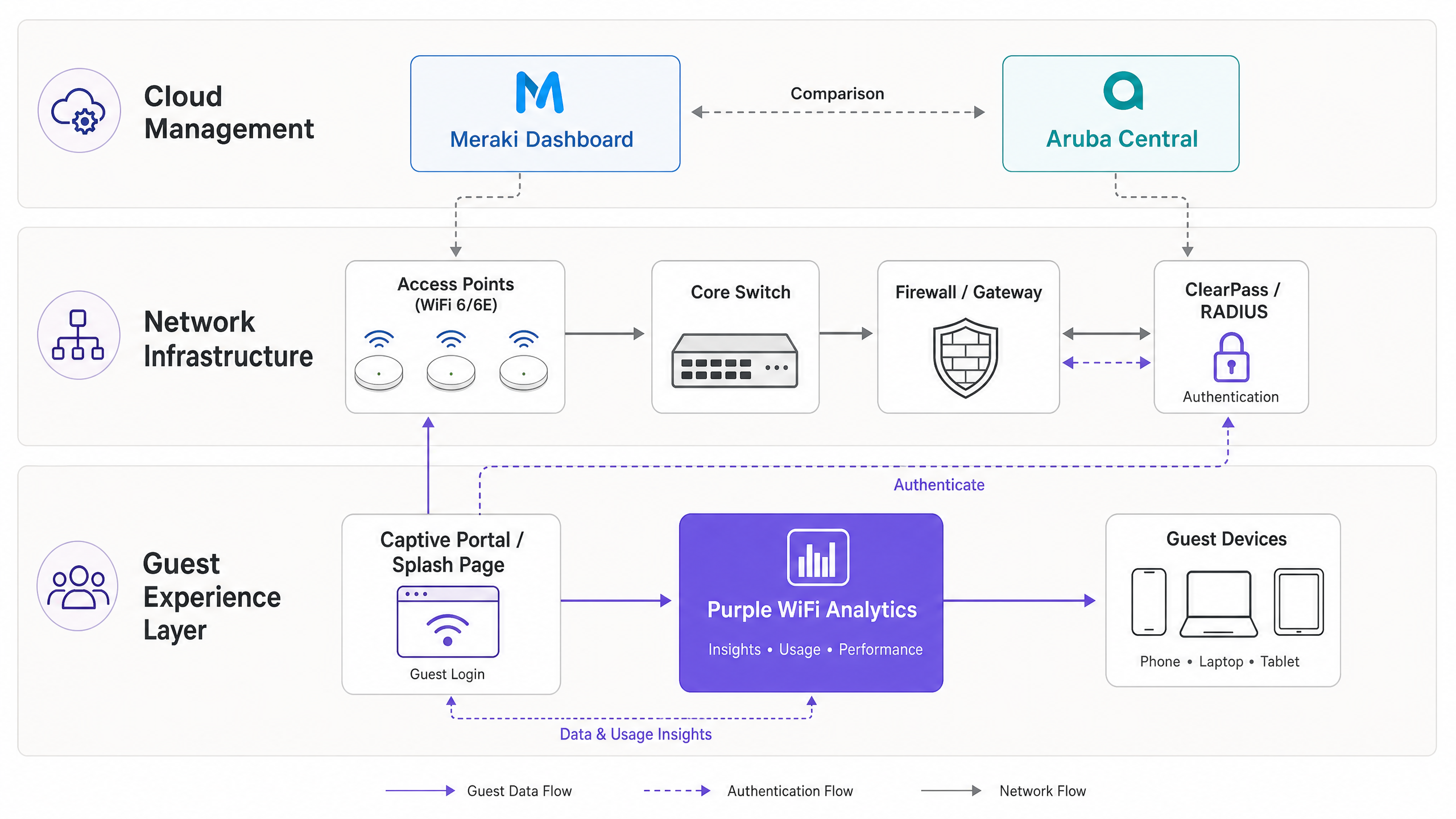
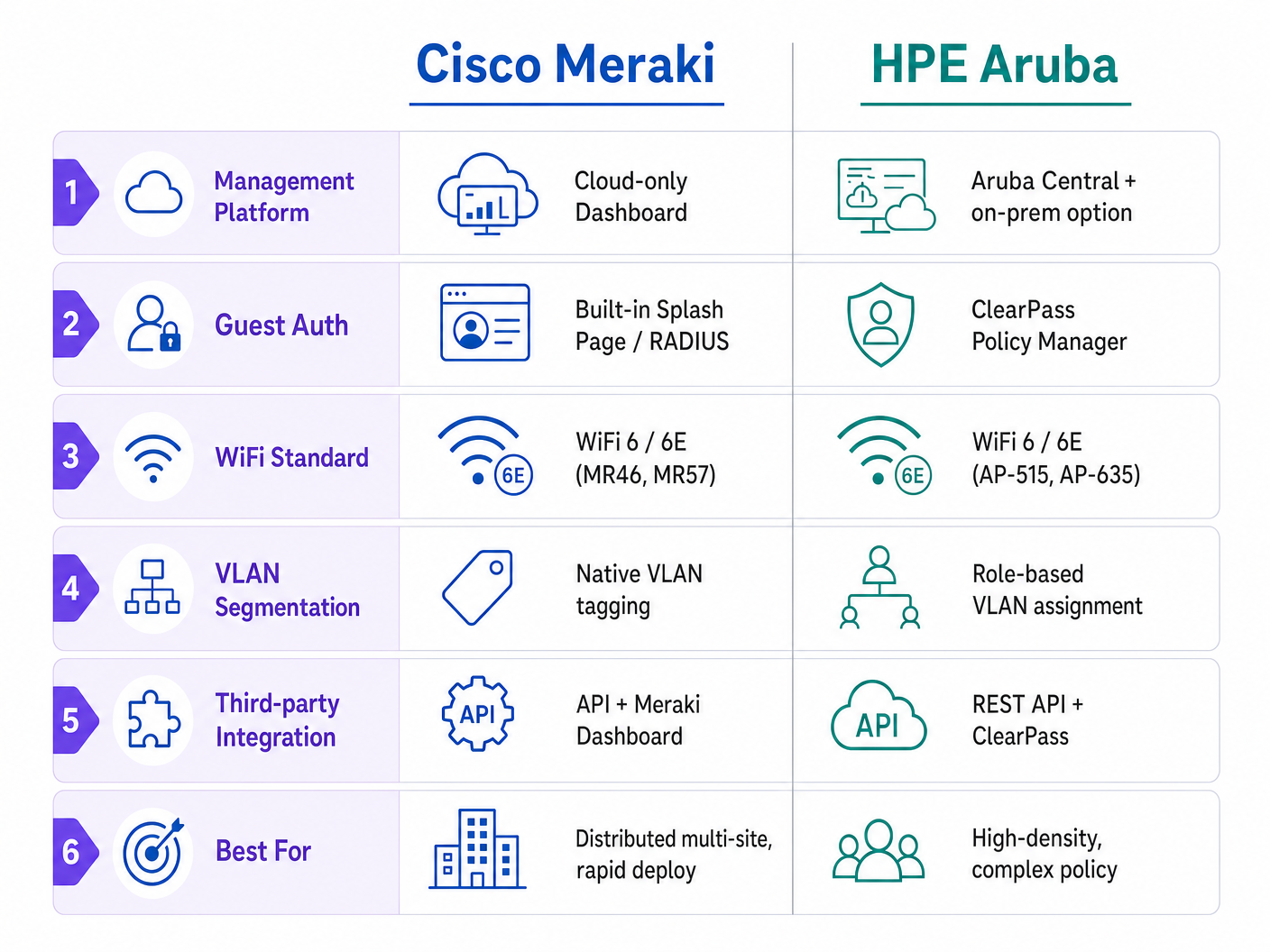
Während beide Plattformen eine robuste WiFi 6/6E-Leistung bieten, unterscheiden sie sich grundlegend in ihrer Managementarchitektur und ihrem Ansatz zur Netzwerkzugriffskontrolle. Cisco Meraki setzt auf ein Cloud-First-, Zero-Touch-Provisioning-Modell, das sich hervorragend für verteilte Multi-Site-Implementierungen eignet. HPE Aruba bietet hybride Bereitstellungsflexibilität und eine ausgeklügelte rollenbasierte Richtliniendurchsetzung über ClearPass, was es zum Standard für hochdichte, komplexe HF-Umgebungen macht.
Unabhängig von der gewählten Hardware müssen Enterprise-Betreiber ihre Gast-Intelligence-Schicht abstrahieren. Durch die Integration einer hardwareunabhängigen Plattform wie Purple stellen Unternehmen die Compliance sicher, bewahren ihre WiFi Analytics -Kontinuität und ermöglichen eine erweiterte Identitätsbereitstellung über jeden Hardware-Aktualisierungszyklus hinweg.
Technischer Deep-Dive: Architektur und Authentifizierung
Architektur der Managementebene
Die bedeutendste architektonische Divergenz zwischen den beiden Anbietern liegt in ihren Managementebenen.
Cisco Meraki verwendet eine streng Cloud-verwaltete Architektur. Das Meraki Dashboard dient als zentrale Oberfläche für alle Konfigurations-, Überwachungs- und Firmware-Verwaltungsaufgaben. Access Points (APs) sind "headless" und benötigen Konnektivität zur Meraki Cloud, um Richtlinien-Updates zu erhalten. Dieses Modell ermöglicht echtes Zero-Touch-Provisioning: APs können an entfernte Einzelhandels -Filialen geliefert, an PoE-Switches angeschlossen werden und rufen ihre Konfigurationsvorlagen automatisch ab.
HPE Aruba bietet einen hybriden Ansatz. Während Aruba Central ein mit Meraki vergleichbares Cloud-Management bietet, unterstützt Aruba auch lokale Controller (Mobility Controllers). Dies ist eine zwingende Anforderung für viele Gesundheitswesen - und öffentliche Sektor-Implementierungen, bei denen Datensouveränität oder strenge NHS-Governance das Routing von Management-Traffic über eine öffentliche Cloud verhindern.
Gast-Authentifizierung und Netzwerkzugriffskontrolle
Das Gast-Onboarding ist der Punkt, an dem Netzwerkrichtlinien auf Benutzererfahrung treffen.
Meraki verwaltet den Gastzugang über integrierte Splash Pages oder externe RADIUS-Integration. Das native Captive Portal ist funktional, aber es fehlen die ausgeklügelten Datenerfassungs- und Einwilligungsmanagementfunktionen, die für die moderne GDPR-Compliance erforderlich sind. Für Enterprise-Implementierungen umfasst die Standardarchitektur die Konfiguration der Meraki SSID mit einer "Anmelden mit"-Anforderung, die auf eine externe Captive Portal URL (wie Purple) verweist und die Authentifizierung über RADIUS.
Aruba geht dies über den ClearPass Policy Manager an, eine dedizierte Network Access Control (NAC)-Appliance. ClearPass Guest bietet umfangreiche Funktionen für die Selbstregistrierung, Sponsor-Genehmigung und granulare rollenbasierte Zugriffskontrolle (RBAC). ClearPass ist jedoch ein komplexes, separates Produkt, das spezielle Lizenzen und Fachkenntnisse für eine effektive Verwaltung erfordert.
Implementierungsleitfaden: Best Practices für die Enterprise-Bereitstellung
1. Netzwerksegmentierung und VLAN-Design
Eine ordnungsgemäße Netzwerksegmentierung ist für Sicherheit und PCI DSS-Compliance unerlässlich. Gast-Traffic muss von Unternehmens-, IoT- und Point-of-Sale (PoS)-Netzwerken isoliert werden.
- Meraki-Implementierung: Erstellen Sie eine dedizierte Gast-SSID und weisen Sie diese einem bestimmten VLAN zu (z.B. VLAN 100). Verwenden Sie die Layer 3/7-Firewall-Regeln von Meraki, um den Traffic zu lokalen LAN-Subnetzen explizit zu verweigern und sicherzustellen, dass Gäste nur Internetzugang haben.
- Aruba-Implementierung: Nutzen Sie die rollenbasierte Firewall von Aruba. Weisen Sie der SSID die Rolle "Gast" zu und definieren Sie Richtlinien, die jeglichen Traffic, der für den privaten IP-Bereich nach RFC 1918 bestimmt ist, verwerfen, bevor HTTP/HTTPS-Traffic zum WAN zugelassen wird.
Für einen tieferen Einblick in Segmentierungsstrategien siehe unseren Leitfaden zu Vergleich von Controller-basierten vs. Cloud-verwalteten Access Points .
2. HF-Design für hohe Dichte
In Gastgewerbe -Umgebungen (Konferenzzentren) oder Verkehrs -Knotenpunkten sind die AP-Platzierung und Kanalplanung entscheidend.
- Setzen Sie WiFi 6E (6 GHz) APs wie den Meraki MR57 oder Aruba AP-635 ein, um Überlastungen im 5 GHz-Band zu reduzieren.
- Beschränken Sie 2,4 GHz-Funkgeräte auf die Bereitstellung einer grundlegenden Abdeckung für ältere IoT-Geräte, während Gastgeräte auf die 5 GHz- und 6 GHz-Bänder gelenkt werden.
- Arubas ClientMatch-Technologie bietet historisch eine hervorragende Client-Steuerung in extrem dichten Umgebungen, während Merakis Auto RF die dynamische Kanal- und Leistungszuweisung für verteilte Standorte effektiv handhabt.
Fehlerbehebung & Risikominderung
Häufige Fehlerursachen
- Fehler bei der Captive Portal-Weiterleitung: Oft verursacht durch aggressive HTTPS-Abfangung (HSTS) oder DNS-Auflösungsprobleme vor der Authentifizierung. Stellen Sie sicher, dass Ihr Walled Garden die notwendigen Domains für die Captive Portal-Plattform, Identitätsanbieter (Apple, Google, Facebook) und Zertifikatsperrlisten (CRLs) enthält.
- VLAN Leaking: Fehlkonfigurierte Switch-Trunk-Ports können Gast-Traffic ermöglichen, in Unternehmensnetzwerke zu gelangen. Verwenden Sie immer explizit getaggte VLANs für AP-Uplinks und vermeiden Sie die Verwendung des nativen VLANs für Gast-Traffic.
- Asymmetrisches Routing in hybriden Umgebungen: Beim Migrieren oder Mischen von Anbietern stellen Sie sicher, dass das Standard-Gateway für das Gast-Subnetz konsistent ist und NAT korrekt verarbeitet, um den Verlust von zustandsbehafteten Verbindungen zu vermeiden.
ROI & Geschäftlicher Nutzen
Der Einsatz von Unternehmens-WiFi ist eine erhebliche Investition in CapEx und OpEx. Um einen ROI zu erzielen, muss das Netzwerk mehr leisten als nur grundlegende Konnektivität.
Durch die Integration der hardwareunabhängigen Plattform von Purple über Meraki oder Aruba verwandeln Veranstaltungsorte ein Kosten- in ein umsatzgenerierendes Asset. Die profilbasierte Authentifizierung von Purple (mit über 440 Millionen globalen Nutzern) reduziert Reibungsverluste und erfasst gleichzeitig Erstanbieterdaten. Dies ermöglicht die Monetarisierung von Retail Media, gezieltes Marketing und detaillierte Besucherfrequenzanalysen.
Wie in unserem aktuellen Playbook How To Improve Guest Satisfaction: The Ultimate Playbook beschrieben, ist nahtlose Konnektivität die Basis; intelligentes Engagement ist das Unterscheidungsmerkmal.
Hören Sie das technische Briefing
Für einen 10-minütigen Einblick in diesen Vergleich hören Sie unseren Podcast mit dem Briefing unseres leitenden Architekten:
Schlüsseldefinitionen
Zero-Touch Provisioning (ZTP)
The ability to configure network hardware via the cloud before it arrives on site, allowing it to download its configuration automatically upon connecting to the internet.
Critical for IT teams deploying WiFi across hundreds of retail branches without sending engineers to each site.
Network Access Control (NAC)
A security solution that enforces policy on devices and users attempting to access the network, ensuring only authorized entities gain entry.
Aruba ClearPass is a dedicated NAC; it determines what a user can access based on their role, device type, and location.
Walled Garden
A limited list of IP addresses or domains that a user can access before they have fully authenticated on the captive portal.
Essential for allowing devices to reach the Purple splash page, identity providers (like Google/Facebook for social login), and certificate validation servers before granting full internet access.
RADIUS (Remote Authentication Dial-In User Service)
A networking protocol that provides centralized Authentication, Authorization, and Accounting (AAA) management for users connecting to a network service.
The standard protocol used by Meraki and Aruba to communicate with Purple or ClearPass to verify if a guest should be allowed on the WiFi.
VLAN (Virtual Local Area Network)
A logical subnetwork that groups a collection of devices from different physical LANs, isolating their broadcast traffic.
The primary method for keeping guest WiFi traffic completely separate from sensitive back-office or Point of Sale (PoS) systems.
WiFi 6E (802.11ax in 6 GHz)
An extension of the WiFi 6 standard that utilizes the newly available 6 GHz spectrum, providing wider channels and less interference.
Crucial for future-proofing high-density venues like stadiums, ensuring the network can handle thousands of concurrent connections without legacy device congestion.
Captive Portal
A web page that the user of a public-access network is obliged to view and interact with before access is granted.
The primary guest touchpoint where terms are accepted, marketing consent is gathered, and brand engagement occurs.
Profile-Based Authentication
A method where users authenticate once and are subsequently recognized seamlessly across a network of venues without repeatedly entering credentials.
Purple's approach to creating a frictionless guest experience, leveraging a global network of over 440 million users.
Ausgearbeitete Beispiele
A 400-room resort hotel needs to deploy guest WiFi across accommodation blocks, a high-density conference centre, and outdoor pool areas. They have a lean IT team of two engineers and require GDPR-compliant marketing data capture.
Deploy Cisco Meraki MR46 APs in the accommodation blocks and MR57 (WiFi 6E) APs in the conference centre for high-density support. Use Meraki Dashboard for zero-touch provisioning and unified management, reducing the burden on the lean IT team. For the marketing requirement, configure the Meraki Guest SSID to use a custom splash URL pointing to Purple WiFi. Purple will handle the captive portal, GDPR consent, and data capture, integrating with Meraki via RADIUS for authentication.
A large public-sector hospital trust requires guest WiFi for patients and visitors. Strict NHS data governance mandates that no network management traffic can traverse a public cloud. They also need to integrate with existing Active Directory for staff BYOD access on a separate SSID.
Deploy HPE Aruba AP-515 access points managed by on-premises Aruba Mobility Controllers. This ensures all management and control plane traffic remains within the hospital's data centre. Deploy ClearPass Policy Manager to handle the complex NAC requirements: integrating with AD for staff BYOD, and providing a secure, segmented guest portal for patients. Purple can still be integrated via ClearPass to provide advanced analytics and seamless roaming (like OpenRoaming) without violating the on-prem management constraint.
Übungsfragen
Q1. A retail chain with 150 small branches needs to deploy guest WiFi. They have no dedicated IT staff at the branch level and rely on a small central team. Which platform architecture is more suitable?
Hinweis: Consider the operational overhead of deploying hardware to 150 locations without on-site technical expertise.
Musterlösung anzeigen
Cisco Meraki is the recommended approach. Its cloud-only architecture and zero-touch provisioning allow the central IT team to configure templates in the Dashboard. Hardware can be shipped directly to branches, plugged in by store staff, and it will automatically download its configuration, significantly reducing deployment complexity and costs.
Q2. You are configuring a guest WiFi network in a hotel. You need to ensure that guests cannot access the hotel's reservation system servers located on the same physical network infrastructure. What is the standard approach?
Hinweis: Think about Layer 2 isolation and Layer 3 boundary control.
Musterlösung anzeigen
The standard approach is strict network segmentation. The Guest SSID must be mapped to a dedicated VLAN (e.g., VLAN 200), completely separate from the corporate VLAN (e.g., VLAN 10). Additionally, Layer 3/7 firewall rules must be applied at the AP or gateway level to explicitly deny any traffic from the Guest VLAN destined for RFC 1918 private IP addresses (the internal network), allowing only traffic destined for the public internet.
Q3. A venue wants to capture guest data for marketing purposes and ensure GDPR compliance. Why is relying solely on the native splash pages provided by hardware vendors often insufficient for enterprise requirements?
Hinweis: Consider the difference between network access control and data privacy/consent management.
Musterlösung anzeigen
Native vendor splash pages are designed primarily for basic network access control (accepting terms and conditions). They generally lack the sophisticated features required for modern marketing and compliance, such as granular consent management, data retention policies, right-to-erasure workflows, social login integrations, and seamless CRM synchronization. An overlay platform like Purple is required to handle the complex compliance burden and abstract the guest intelligence layer from the underlying hardware.