Configuring RADIUS Policies for Fine-Grained Network Access Control
This authoritative guide provides IT managers, network architects, and venue operations directors with a complete technical blueprint for configuring RADIUS policies to achieve fine-grained network access control. It covers 802.1X architecture, dynamic VLAN assignment, EAP method selection, and phased deployment strategies. Real-world implementation scenarios from hospitality and retail demonstrate how these techniques deliver measurable compliance, security, and operational ROI.
Listen to this guide
View podcast transcript
- Executive Summary
- Technical Deep-Dive
- The Architecture of Context-Aware Access
- Dynamic VLAN Assignment and Micro-Segmentation
- EAP Method Selection
- Implementation Guide
- Phase 1: Identity Source Integration
- Phase 2: Policy Configuration and Attribute Mapping
- Phase 3: Phased Rollout and Monitoring
- Best Practices
- Troubleshooting & Risk Mitigation
- Common Failure Modes
- ROI & Business Impact

Executive Summary
For enterprise venues — from expansive retail complexes to high-density stadiums — network security and user experience are inextricably linked. Configuring RADIUS policies for fine-grained network access control provides the mechanism to segment traffic dynamically, ensuring that corporate assets remain isolated from guest networks and vulnerable IoT devices. This is no longer a discretionary upgrade; it is a fundamental requirement driven by compliance mandates including PCI DSS and GDPR.
This guide delivers a deep-dive technical blueprint for deploying RADIUS-based access control. We examine the architecture of IEEE 802.1X authentication, the mechanics of dynamic VLAN assignment via Vendor-Specific Attributes (VSAs), and the integration of identity providers including Active Directory, Entra ID, and Purple's OpenRoaming identity provider. By moving beyond basic pre-shared keys (PSKs) to context-aware policy enforcement, IT leaders can mitigate risk, streamline operations, and leverage platforms like Purple to transform guest WiFi from a cost centre into a strategic asset. The focus throughout is on actionable, vendor-neutral strategies that deliver measurable ROI and operational resilience.
Technical Deep-Dive
The Architecture of Context-Aware Access
At its core, configuring RADIUS policies for fine-grained network access control relies on the IEEE 802.1X standard. This framework facilitates port-based network access control, ensuring that only authenticated and authorised devices gain entry to specific network segments. The architecture consists of three primary components: the supplicant (client device), the authenticator (wireless access point or switch), and the authentication server (RADIUS).
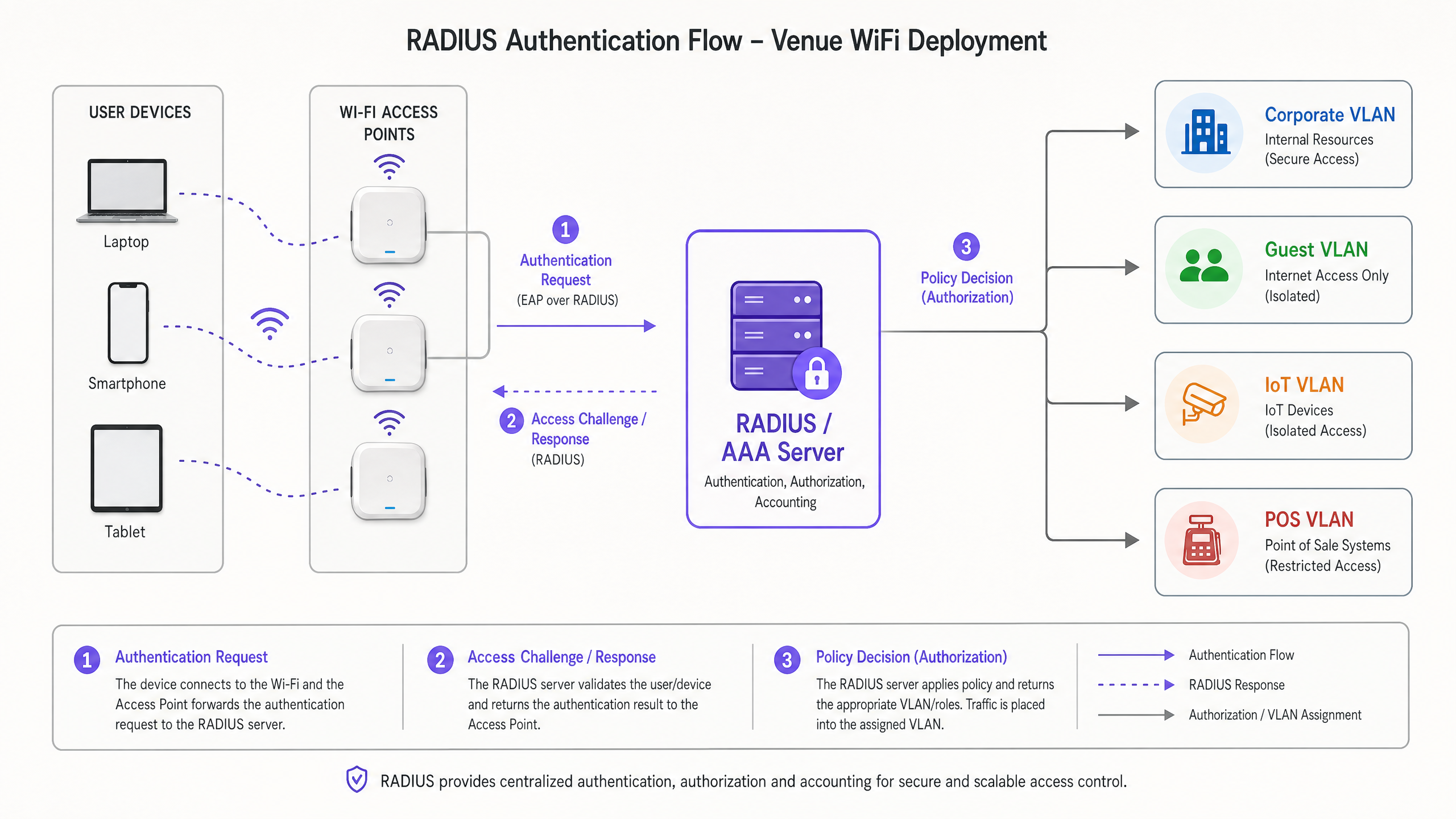
When a device connects, the authenticator encapsulates the Extensible Authentication Protocol (EAP) messages and forwards them to the RADIUS server. The RADIUS server evaluates the credentials against an identity store — such as Active Directory, LDAP, or a cloud-based identity provider. Crucially, modern RADIUS implementations do not merely return an Access-Accept or Access-Reject message. They return Vendor-Specific Attributes (VSAs) that dictate the user's network context: VLAN assignment, Access Control List (ACL) application, and bandwidth throttling parameters.
For enterprise deployments, understanding Wi Fi Frequencies: A Guide to Wi-Fi Frequencies in 2026 is essential, as physical layer characteristics directly impact the performance of authentication handshakes in high-density environments.
Dynamic VLAN Assignment and Micro-Segmentation
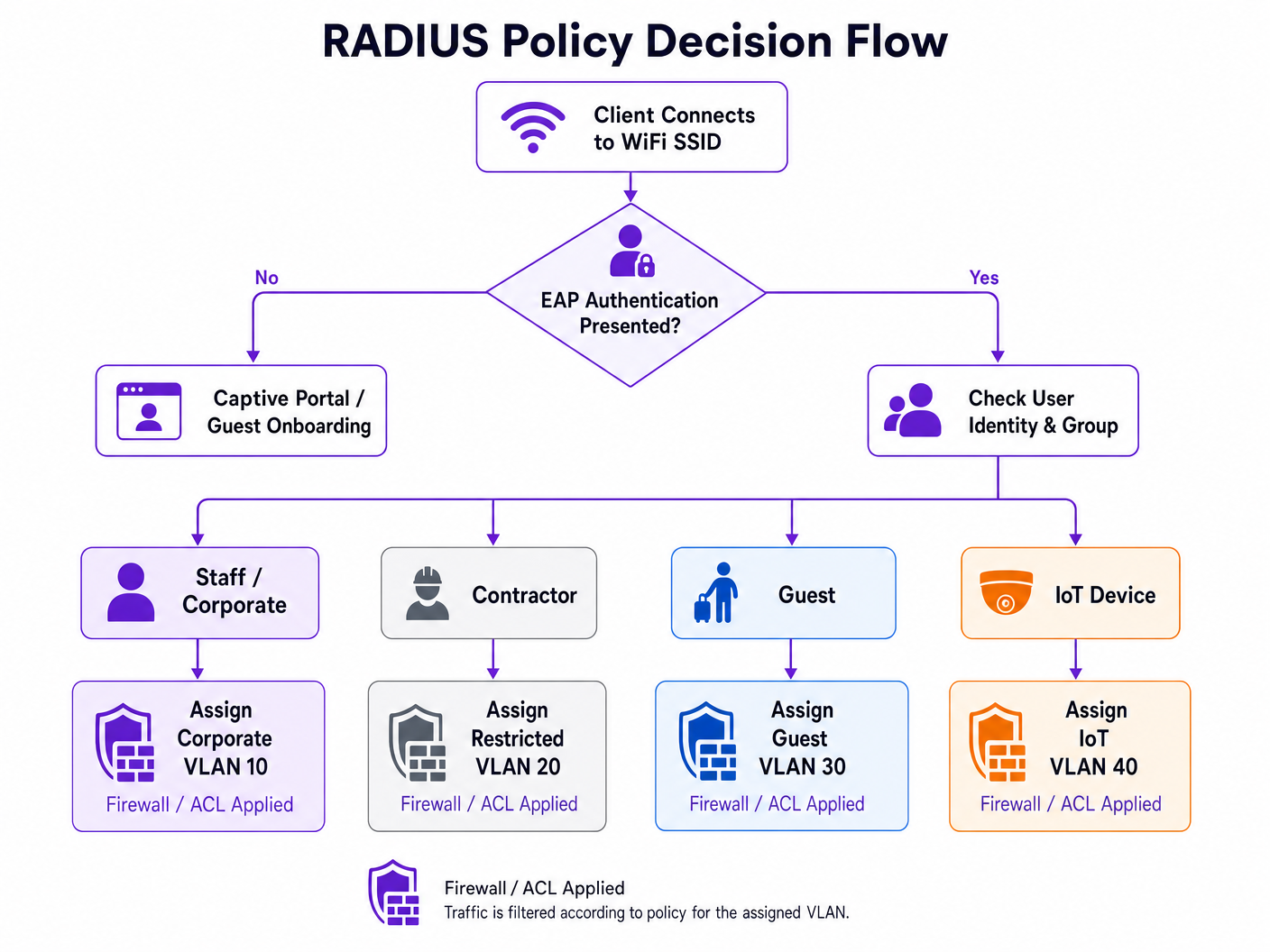
The most powerful application of RADIUS policies is dynamic VLAN assignment. Instead of broadcasting multiple SSIDs for different user groups — which degrades RF performance due to beacon overhead — a single 802.1X-enabled SSID can serve all corporate users. The RADIUS server determines the appropriate VLAN based on the user's group membership and contextual factors.
For example, when a member of the finance team authenticates, the RADIUS server instructs the access point to place their traffic on VLAN 10. When an IoT device authenticates via MAC Authentication Bypass (MAB), it is placed on an isolated VLAN 40 with strict ACLs. This approach drastically reduces the attack surface and simplifies the RF environment simultaneously. For specific vendor implementations, refer to How to Configure NAC Policies for VLAN Steering in Cisco Meraki .
EAP Method Selection
The choice of EAP method has significant implications for both security posture and operational complexity. The table below summarises the key options:
| EAP Method | Authentication Mechanism | Recommended Use Case | Security Level |
|---|---|---|---|
| EAP-TLS | Mutual certificate-based | Corporate managed devices with MDM | Highest |
| PEAP-MSCHAPv2 | Server cert + username/password | BYOD, staff devices | High |
| EAP-TTLS | Server cert + inner credentials | Mixed environments | High |
| MAB | MAC address as credential | Headless IoT, legacy devices | Low (use with strict ACLs) |
Avoid legacy protocols such as LEAP and EAP-MD5 entirely; they are cryptographically weak and should not appear in any modern deployment.
Implementation Guide
Deploying a robust RADIUS infrastructure requires meticulous planning and phased execution. The following steps outline a vendor-neutral approach to configuring RADIUS policies for fine-grained network access control.
Phase 1: Identity Source Integration
The foundation of any policy is a clean, well-structured identity directory. Whether utilising on-premises Active Directory or cloud-native solutions like Entra ID or Okta, the directory groups must map directly to your intended network segments.
- Audit Existing Groups: Ensure that user groups are logical and mutually exclusive where possible. Remove stale accounts and consolidate overlapping groups.
- Define Access Tiers: Establish clear tiers — Executive, Staff, Contractor, Guest, IoT — with documented access rights for each.
- Integrate Purple as an Identity Provider: For public-facing networks, Purple acts as a free identity provider for services like OpenRoaming under the Connect licence. This seamlessly bridges the gap between public Guest WiFi access and secure authentication frameworks, eliminating the need for a traditional captive portal for returning users.
Phase 2: Policy Configuration and Attribute Mapping
Configure the RADIUS server to evaluate incoming requests based on multiple contextual factors, not just credentials.
- Authentication Protocols: Mandate EAP-TLS for corporate devices. Deploy PEAP-MSCHAPv2 for BYOD. Enforce these via the RADIUS policy, rejecting connections that attempt weaker methods.
- Condition Matching: Build policies that evaluate the
NAS-IP-Address(the authenticator's IP), theCalled-Station-Id(the SSID), and the time of day. A contractor's access profile at 02:00 should differ materially from their profile at 09:00. - Enforcement Profiles: Define the RADIUS attributes to be returned. Standard VLAN assignment attributes are:
Tunnel-Type=VLAN,Tunnel-Medium-Type=802, andTunnel-Private-Group-Id=[VLAN_ID].
Phase 3: Phased Rollout and Monitoring
Never deploy 802.1X enforcement across an entire enterprise simultaneously.
- Monitor Mode: Deploy policies in monitor or audit mode where authentication failures are logged but access is still granted. This identifies misconfigured supplicants and legacy devices before enforcement begins.
- Targeted Enforcement: Enable enforcement on a per-location or per-department basis, resolving issues before expanding scope.
- Analytics Integration: Leverage platforms like Purple's WiFi Analytics to monitor authentication success rates, session durations, and roaming behaviour. This data is critical for identifying coverage gaps and authentication bottlenecks.
Best Practices
When configuring RADIUS policies for fine-grained network access control, adherence to industry standards ensures long-term stability and security.
Certificate-Based Authentication (EAP-TLS): Wherever possible, deploy EAP-TLS. It eliminates the risks associated with credential theft and password fatigue. Mobile Device Management (MDM) platforms can automate certificate provisioning at scale.
Implement MAC Randomisation Mitigation: Modern mobile operating systems utilise MAC address randomisation to protect user privacy. For Guest WiFi deployments, ensure your captive portal and RADIUS accounting systems handle changing MAC addresses gracefully — for example, by relying on session tokens or persistent device profiles generated during initial onboarding.
Redundancy and Failover: RADIUS is a critical infrastructure component. Deploy RADIUS servers in highly available clusters across geographically diverse locations. Configure authenticators with primary and secondary server IPs, and establish aggressive timeout and retry values to minimise authentication delays during failover events.
Leverage Contextual Data: Incorporate location data into policy decisions. A contractor might be granted access to internal resources when connected to an AP in the engineering block, but restricted to internet-only access when connected in the cafeteria. Technologies discussed in BLE Low Energy Explained for Enterprise can augment this location context with precision positioning data.
Troubleshooting & Risk Mitigation
The complexity of 802.1X deployments introduces specific failure modes. Proactive risk mitigation is essential for maintaining uptime.
Common Failure Modes
| Failure Mode | Root Cause | Mitigation |
|---|---|---|
| Mass authentication failure | Expired RADIUS server or root CA certificate | Certificate lifecycle management with automated alerts at 90/60/30 days |
| Individual device failures | Supplicant misconfiguration or missing root CA | MDM-pushed wireless profiles with correct trust store |
| EAP timeout | High WAN latency to centralised RADIUS | Optimise WAN path; consider distributed RADIUS or RADIUS proxy |
| IoT device failures | Device does not support 802.1X | Deploy MAB with strict VLAN isolation and ACLs |
For distributed enterprises, the architecture discussed in SD WAN vs MPLS: The 2026 Enterprise Network Guide is directly relevant to ensuring low-latency connectivity to centralised AAA services across multiple sites.
ROI & Business Impact
Investing the engineering effort required for configuring RADIUS policies for fine-grained network access control yields substantial, measurable returns across multiple dimensions.
Reduced Operational Overhead: Consolidating multiple SSIDs into a single 802.1X network with dynamic VLAN assignment reduces RF interference, improves available airtime, and simplifies ongoing management. Teams report a significant reduction in helpdesk tickets related to WiFi connectivity once a stable 802.1X deployment is in place.
Enhanced Compliance Posture: For sectors like Retail and Healthcare , strict network segmentation is a regulatory requirement — PCI DSS and HIPAA respectively. RADIUS policies provide the verifiable, auditable controls necessary to pass compliance audits and avoid substantial financial penalties. For public-sector organisations, GDPR obligations around data segregation are similarly addressed.
Improved User Experience: Seamless, secure authentication — particularly via EAP-TLS or OpenRoaming — eliminates the friction of captive portals for returning corporate users and VIP guests. In Hospitality and Transport venues, this directly impacts satisfaction metrics and repeat engagement.
Key Definitions
RADIUS (Remote Authentication Dial-In User Service)
A networking protocol that provides centralised Authentication, Authorisation, and Accounting (AAA) management for users who connect and use a network service. Defined in RFC 2865.
The core engine for enterprise network access control, determining who gets on the network, what they can access, and logging the activity for audit purposes.
IEEE 802.1X
An IEEE Standard for port-based Network Access Control (PNAC). It provides an authentication mechanism to devices wishing to attach to a LAN or WLAN, blocking all traffic until authentication is complete.
The standard that forces a device to prove its identity before it is allowed to send any data traffic on the network. The enforcement mechanism that makes RADIUS policies actionable.
EAP (Extensible Authentication Protocol)
An authentication framework frequently used in wireless networks and point-to-point connections. It provides a transport layer for authentication methods (EAP methods) such as TLS or MSCHAPv2.
The envelope that carries the actual authentication credentials between the client and the RADIUS server. The choice of EAP method determines the security level of the authentication exchange.
VSA (Vendor-Specific Attribute)
Attributes within a RADIUS message that allow vendors to support extended attributes not defined in the base RADIUS RFCs. Used to convey network policy instructions from the RADIUS server to the authenticator.
The mechanism by which RADIUS instructs network hardware to assign a user to a specific VLAN, apply a firewall role, or enforce bandwidth limits. Without VSAs, RADIUS can only permit or deny access.
Dynamic VLAN Assignment
The process where a RADIUS server instructs an access point or switch to place a user's traffic onto a specific Virtual LAN based on their identity, group membership, or contextual attributes.
The key technique for network micro-segmentation. Allows a single physical infrastructure to securely support multiple distinct user groups without broadcasting multiple SSIDs.
Supplicant
The software client on an end-user device (laptop, smartphone, IoT device) that initiates and negotiates the 802.1X authentication exchange with the network authenticator.
Built into modern operating systems (Windows, macOS, iOS, Android). Misconfigured supplicants — particularly incorrect certificate trust settings — are the most common source of 802.1X connectivity issues.
Authenticator
The network device (wireless access point or Ethernet switch) that acts as the enforcement point in an 802.1X deployment. It relays EAP messages between the supplicant and the RADIUS server, and enforces the policy decision.
The gatekeeper. The authenticator blocks all traffic from a port or wireless association until the RADIUS server returns an Access-Accept message, at which point it applies the returned VSAs.
MAB (MAC Authentication Bypass)
A fallback authentication method where the network device's MAC address is submitted as its credential to the RADIUS server. Used for devices that do not support 802.1X supplicants.
A necessary operational tool for legacy and headless IoT devices, but inherently less secure than cryptographic authentication. Should always be paired with strict VLAN isolation and ACLs.
EAP-TLS (EAP Transport Layer Security)
A certificate-based EAP method that provides mutual authentication between the client and the RADIUS server using X.509 certificates. Considered the most secure EAP method available.
The recommended authentication method for corporate-managed devices. Eliminates password-based credential risks entirely. Requires a PKI infrastructure and MDM for certificate provisioning.
Worked Examples
A large conference centre needs to provide secure, segmented WiFi access for event staff, exhibitors, and general attendees. They currently broadcast three separate SSIDs, which is causing significant co-channel interference and poor performance in high-density exhibition halls.
The venue transitions to a single, 802.1X-enabled SSID named 'Conference_Secure'. They implement a RADIUS server integrated with their event management database.
- Event staff authenticate using their corporate credentials via PEAP-MSCHAPv2. The RADIUS policy matches their Active Directory group and returns Tunnel-Private-Group-Id=10 (Staff VLAN), granting access to internal AV management systems.
- Exhibitors are provided unique, time-limited credentials tied to their stand booking. Upon authentication, the RADIUS server returns Tunnel-Private-Group-Id=20 (Exhibitor VLAN), which has ACLs permitting access to specific presentation servers and internet egress.
- General attendees use a separate open SSID with a captive portal integrated with Purple for marketing data collection, consent management, and basic internet access.
The result is a 40% reduction in management frame overhead, measurably improved throughput in exhibition halls, and a clear audit trail for compliance purposes.
A retail chain needs to secure thousands of wireless Point of Sale (POS) terminals across 500 locations. They are currently using WPA2-PSK, and IT is concerned about the operational risk of rotating the pre-shared key across 500 sites, as well as PCI DSS audit findings.
The IT team deploys a centralised RADIUS infrastructure and configures the POS terminals for EAP-TLS authentication.
- An MDM solution pushes a unique client certificate to each POS terminal during provisioning.
- The wireless access points at each store are configured to forward authentication requests to the central RADIUS servers over the SD-WAN fabric.
- The RADIUS policy verifies the client certificate against the internal PKI and returns attributes to place the device on the isolated POS VLAN (VLAN 50), satisfying PCI DSS network segmentation requirements.
- A certificate revocation list (CRL) is maintained, allowing IT to instantly quarantine a lost or stolen terminal by revoking its certificate — without impacting any other device.
Practice Questions
Q1. A hospital needs to deploy new wireless infusion pumps across three wards. These devices do not support 802.1X supplicants. The CISO requires that these devices are completely isolated from the corporate network and can only communicate with the specific clinical management server at 10.5.1.20. How should you configure the network access control policy?
Hint: Consider how devices without 802.1X capabilities can be identified and the principle of least privilege when defining the ACL.
View model answer
Implement MAC Authentication Bypass (MAB). Register the MAC addresses of all infusion pumps in the RADIUS database during the provisioning process. Create a specific RADIUS policy that matches these MAC addresses and returns VSAs assigning them to an isolated IoT VLAN (e.g., VLAN 60). Apply strict ACLs to this VLAN permitting outbound traffic only to 10.5.1.20 on the required clinical management ports, and blocking all other inter-VLAN and internet traffic. Additionally, configure DHCP snooping and dynamic ARP inspection on the IoT VLAN to prevent spoofing attacks.
Q2. Following a recent acquisition, an enterprise now has two distinct Active Directory domains: corp.acme.com and corp.legacy.com. They want all employees from both entities to use the same 'ACME_Corporate' SSID without migrating the legacy domain. How can RADIUS facilitate this?
Hint: Think about how RADIUS handles authentication routing based on the identity realm and how policy servers can proxy requests to different backend directories.
View model answer
Configure the RADIUS infrastructure (using a policy server such as Cisco ISE, Aruba ClearPass, or a RADIUS proxy) to evaluate the realm suffix provided in the user's EAP identity — for example, user@corp.acme.com versus user@corp.legacy.com . Create routing policies that forward authentication requests to the appropriate backend Active Directory domain based on the realm. Define standardised enforcement profiles that return consistent VLAN VSAs regardless of the backend domain, ensuring users from both entities receive the correct network placement. This approach avoids a disruptive directory migration while maintaining a unified user experience.
Q3. You are designing the WiFi for a 60,000-seat stadium. The client's current design specifies 8 separate SSIDs for different staff functions: Ticketing, Security, Concessions, Medical, Media, Operations, VIP, and Maintenance. What is your recommendation and why?
Hint: Consider the impact of management frame overhead on wireless performance in a high-density RF environment.
View model answer
Strongly advise against broadcasting 8 SSIDs. In a high-density environment, each SSID generates beacon frames on every access point at regular intervals, consuming significant airtime and reducing the capacity available for actual data traffic. The recommendation is to consolidate all staff functions onto a single 802.1X-enabled SSID. Utilise RADIUS dynamic VLAN assignment to segment the traffic on the backend — when a ticketing device authenticates, RADIUS places it on the Ticketing VLAN; when a medical device authenticates, it goes to the Medical VLAN with appropriate ACLs. This provides the required logical separation while optimising the physical RF environment. A separate open SSID with a captive portal can handle general public access.