Verwaltung der Erschöpfung öffentlicher IPs in Studentenwohnheimen
This guide provides a definitive technical reference for network architects deploying Carrier-Grade NAT (CGNAT) and Port Address Translation (PAT) to manage IPv4 exhaustion in dense student housing and multi-tenant WiFi environments. It covers NAT444 architecture, RFC 6598 shared address space, Port Block Allocation sizing, GDPR-compliant logging strategies, and a dual-stack IPv6 migration path. The guide is essential for any operator managing hundreds or thousands of concurrent devices on a constrained public IP pool, providing actionable configuration guidance, real-world case studies, and ROI analysis.
Diesen Leitfaden anhören
Podcast-Transkript ansehen
- Executive Summary
- Technical Deep-Dive
- The Scale Problem in Student Housing
- The Limitations of Standard PAT
- The CGNAT (NAT444) Architecture
- Port Block Allocation: The Critical Design Decision
- Dual-Stack IPv6 as the Long-Term Migration Path
- Implementation Guide
- Step 1: Audit Your Current IP Allocation and Device Density
- Step 2: Design the RFC 6598 Intermediate Network
- Step 3: Deploy and Configure the CGNAT Gateway
- Step 4: Integrate with the Identity and Authentication Layer
- Step 5: Configure IPv6 Dual-Stack
- Best Practices
- Troubleshooting & Risk Mitigation
- The Logging and Compliance Burden
- The CAPTCHA and IP Reputation Problem
- Application Compatibility Issues
- ROI & Business Impact
- Capital Expenditure Savings
- Operational Expenditure Reduction
- Competitive Differentiation in Student Housing
- Case Study 1: 800-Bed University Halls of Residence
- Case Study 2: 1,200-Room Purpose-Built Student Accommodation (PBSA) Operator
Executive Summary
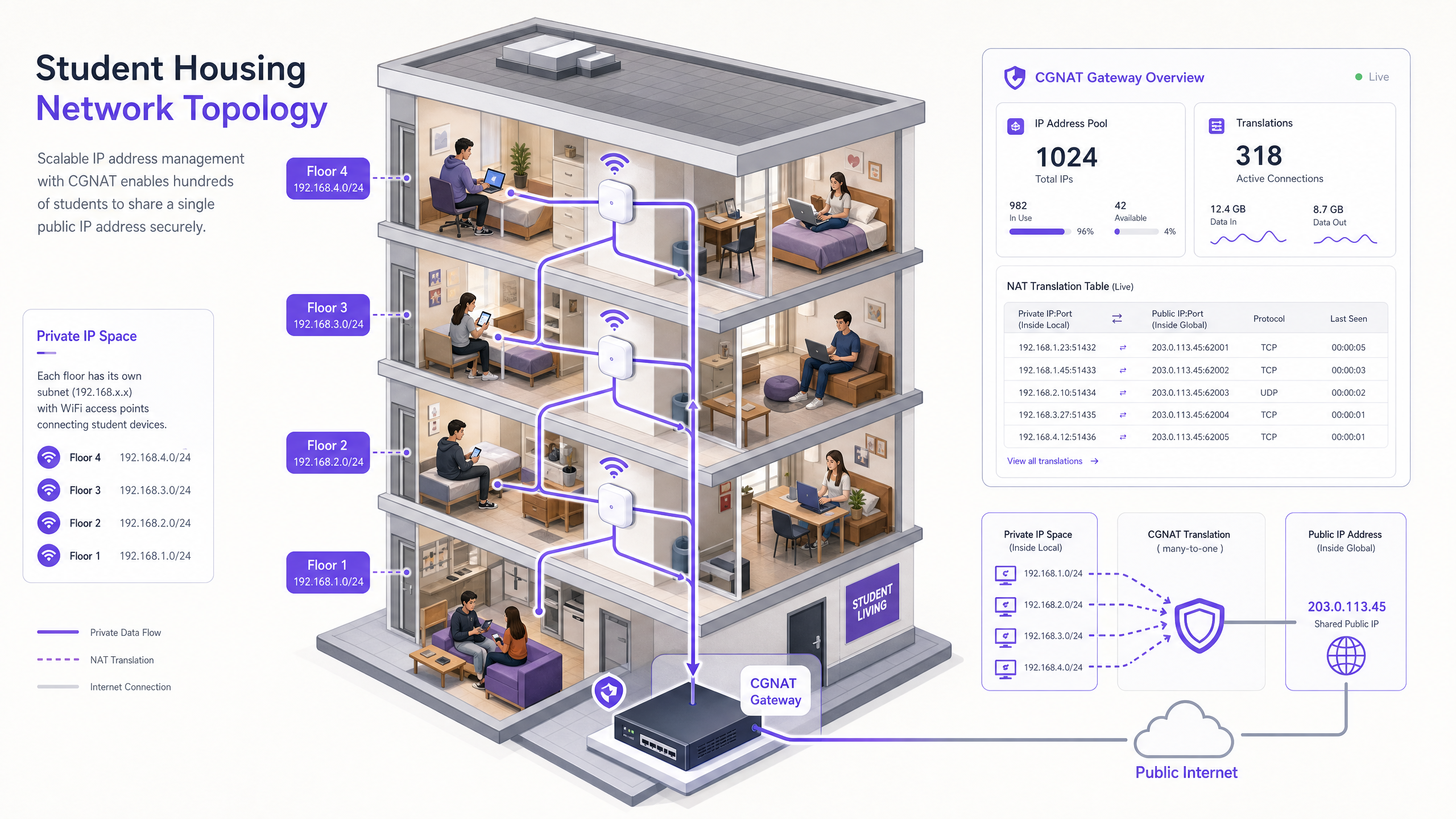
As IPv4 address exhaustion accelerates, IT managers and network architects in dense multi-tenant environments — such as student housing, hospitality , and large public venues — face significant operational challenges. A single student accommodation block with 1,000 residents can generate over 7,000 concurrent IP-connected devices. Standard Port Address Translation (PAT) architectures fail at this scale, leading to port exhaustion, dropped connections, and degraded user experience.
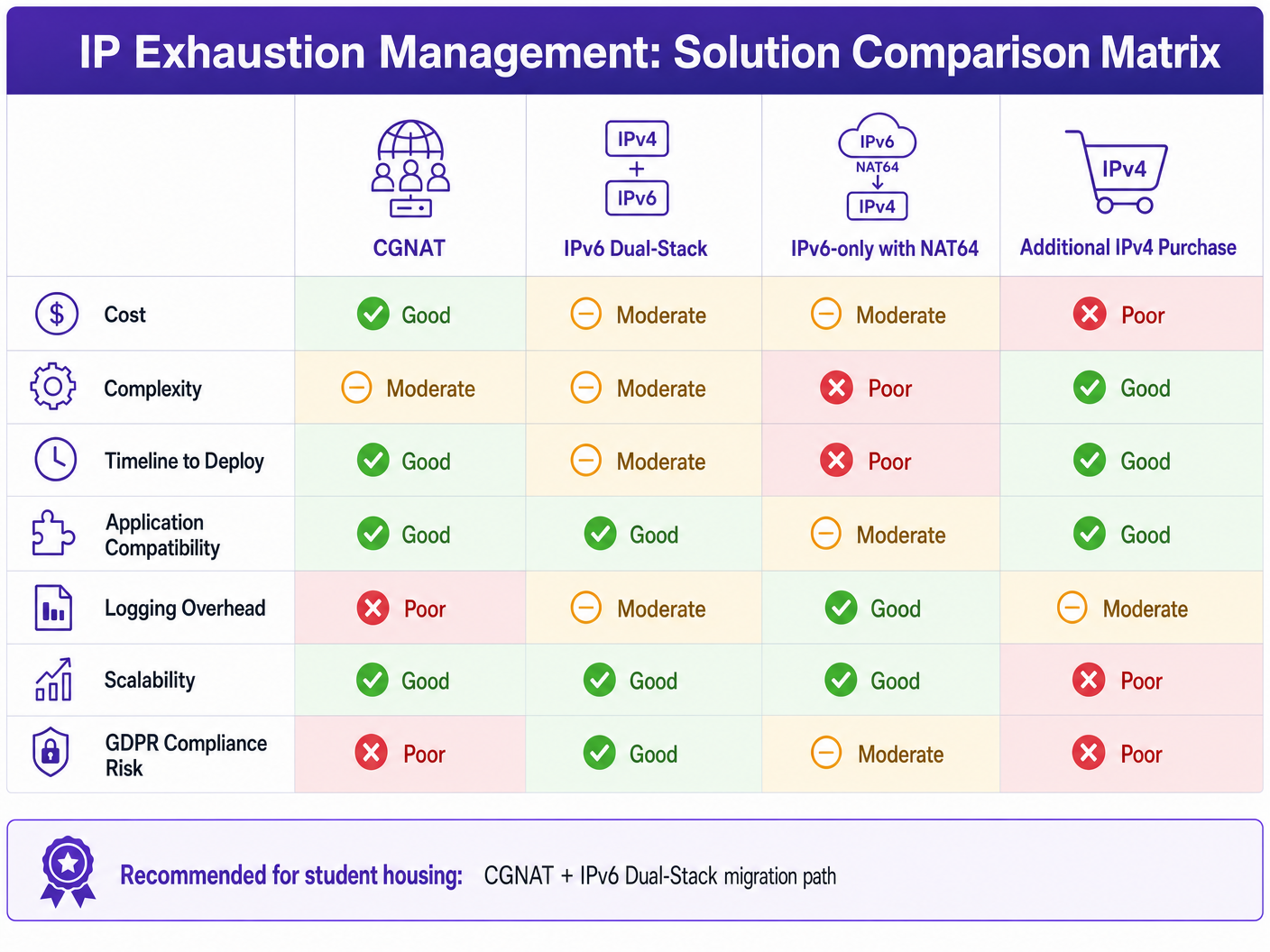
This technical reference guide outlines the architecture and deployment of Carrier-Grade NAT (CGNAT) using the NAT444 model to manage IP exhaustion. By leveraging RFC 6598 shared address space and implementing strategic Port Block Allocation (PBA), network operators can achieve high subscriber density — up to 128 users per public IP — while maintaining compliance with GDPR and lawful intercept regulations. For venues utilising platforms like Guest WiFi and WiFi Analytics , a robust CGNAT architecture ensures stable connectivity and accurate data collection without the capital expenditure of purchasing additional IPv4 blocks.
Technical Deep-Dive
The Scale Problem in Student Housing
The device density in modern student accommodation is unlike almost any other managed network environment. A single resident typically connects a smartphone, a laptop, a smart TV, a games console, and at least one smart home device. At five to seven devices per occupant, a 1,000-bed development presents a concurrent session load that dwarfs a comparably sized hotel. The challenge is compounded by usage patterns: evening peak hours (18:00–23:00) see near-simultaneous high-bandwidth activity across gaming, video streaming, and social media, all of which maintain persistent background connections.
The IPv4 address space is effectively exhausted at the Regional Internet Registry (RIR) level. RIPE NCC, which manages allocations across Europe and the Middle East, reached its final /8 allocation policy in 2019. Acquiring additional public IPv4 blocks on the open market now costs between $40 and $60 per address — a prohibitive CapEx for any operator managing hundreds of subnets.
The Limitations of Standard PAT
In traditional single-site deployments, Port Address Translation (PAT) maps an entire private LAN (RFC 1918 space: 10.0.0.0/8, 172.16.0.0/12, 192.168.0.0/16) to a single public IP address. A single IPv4 address has 65,535 available ports across TCP and UDP. While sufficient for a small office, in dense student housing, the proliferation of background applications — cloud synchronisation, messaging platforms, streaming services — means a single user can easily consume hundreds of ports simultaneously. When the PAT edge router exhausts its available ports, new session requests are silently dropped. This manifests as application timeouts, failed VoIP calls, and a surge in helpdesk tickets.
The CGNAT (NAT444) Architecture
To scale beyond the limitations of single-level NAT, enterprise networks must adopt a Carrier-Grade NAT architecture, specifically the NAT444 model. The name refers to the three layers of IPv4 address space involved in the translation chain.
Level 1 — CPE / Access Point Layer: Subscriber devices are assigned private IP addresses from RFC 1918 space (e.g., 192.168.x.x). The access point or Customer Premises Equipment (CPE) performs the first NAT translation.
Level 2 — CGNAT Gateway: The CPE translates private RFC 1918 addresses to the RFC 6598 Shared Address Space (100.64.0.0/10). This intermediate space is specifically reserved for use between service provider infrastructure and the CGNAT gateway. Using RFC 6598 — rather than another RFC 1918 range — prevents address overlap and routing conflicts in complex multi-tenant environments.
Level 3 — Public Internet: The CGNAT gateway performs the final translation from RFC 6598 addresses to a shared public IPv4 address. This is the address visible to external services.
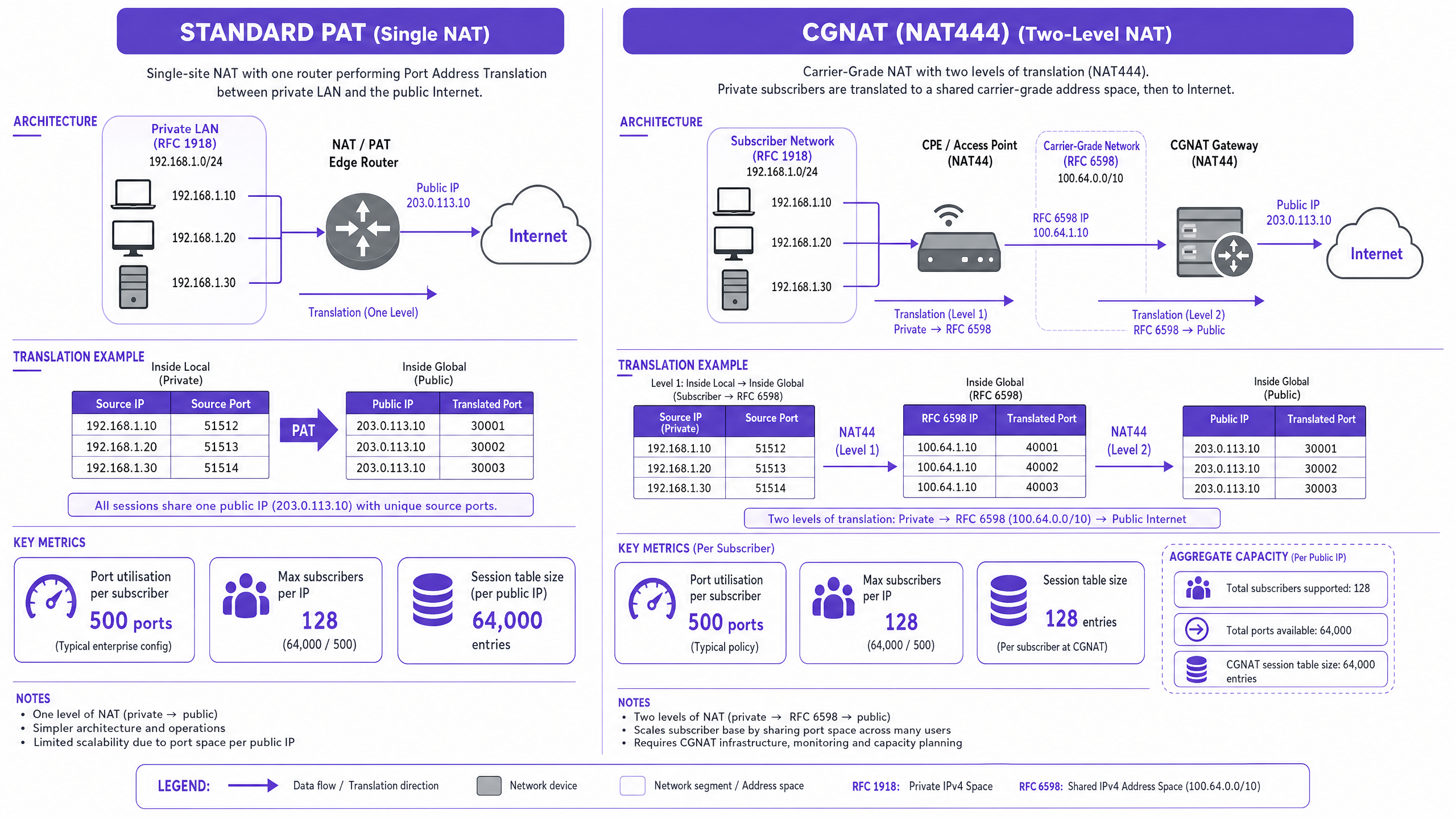
Port Block Allocation: The Critical Design Decision
The most consequential configuration choice in a CGNAT deployment is the port allocation strategy. Two approaches exist:
Dynamic Port Allocation (DPA): Ports are assigned on a per-session basis from a shared pool. This maximises port utilisation efficiency but generates a log entry for every single session setup and teardown — creating a compliance and infrastructure burden at scale.
Port Block Allocation (PBA): A contiguous block of ports is assigned to each subscriber upon their first session initiation. The block remains allocated until the subscriber's session expires. This approach generates logs only at block assignment and release, reducing log volume by up to 98%.
| Configuration Parameter | Recommended Value | Rationale |
|---|---|---|
| Ports per subscriber (PBA block size) | 500 | Sufficient for modern multi-app usage without pool starvation |
| Max subscribers per public IP | 128 | Maintains 500+ ports per user at 64,000 usable ports per IP |
| Max concurrent sessions per subscriber | 2,000 | Prevents a single compromised device from exhausting the block |
| Session timeout (TCP established) | 7,440 seconds (RFC 5382) | Aligns with IETF recommendations for NAT behaviour |
| Session timeout (UDP) | 300 seconds | Prevents stale UDP mappings from consuming port space |
Industry Benchmark: NFWare, a specialist CGNAT vendor with deployments across 100+ ISPs, recommends a maximum of 128 subscribers per public IP with 500 ports allocated per subscriber. Exceeding this threshold — for example, pushing to 256 subscribers per IP with 250 ports each — significantly increases the risk of session drops during peak load.
Dual-Stack IPv6 as the Long-Term Migration Path
CGNAT is a mitigation strategy, not a permanent solution. The correct architectural trajectory is a Dual-Stack deployment: running IPv6 natively alongside IPv4 with CGNAT. Modern devices and major CDNs (Google, Netflix, Meta, Cloudflare) strongly prefer IPv6 when available. In a well-configured dual-stack environment, 60–70% of total traffic can be offloaded to IPv6, dramatically reducing the load on the IPv4 CGNAT pool and extending its effective lifespan.
For healthcare and transport environments where legacy device support is critical, dual-stack also provides a clean migration path: IPv6-capable devices transition natively, while legacy IPv4-only devices continue to operate through CGNAT without any user-facing disruption.
Implementation Guide
Step 1: Audit Your Current IP Allocation and Device Density
Before deploying CGNAT, establish a baseline. Collect the following data from your existing network management system:
- Peak concurrent device count per subnet
- Average and peak sessions per device
- Current public IP utilisation percentage
- Existing NAT timeout configurations
This data directly informs your PBA block sizing and public IP pool requirements.
Step 2: Design the RFC 6598 Intermediate Network
Allocate the 100.64.0.0/10 block for the carrier-grade intermediate network. Plan the subnetting to match your campus topology — typically one /24 or /23 per building or access layer segment. Ensure your routing infrastructure does not leak RFC 6598 prefixes to the public internet or to peering partners.
Step 3: Deploy and Configure the CGNAT Gateway
The CGNAT gateway is typically a dedicated hardware appliance or a virtualised network function (VNF) running on commodity server hardware. Key configuration parameters:
- NAT Pool: Assign your public IPv4 block to the NAT pool. Ensure the pool is sized for your target subscriber-to-IP ratio.
- PBA Configuration: Set the block size to 500 ports. Configure the maximum blocks per subscriber to 1 (with the option to expand to 2 if a subscriber exhausts their initial block, rather than increasing the base block size).
- Logging: Configure syslog output to your SIEM. With PBA, each log entry records: subscriber internal IP, assigned public IP, assigned port block start, block end, timestamp of allocation, and timestamp of release.
- Session Limits: Enforce a maximum of 2,000 concurrent sessions per subscriber to prevent abuse.
Step 4: Integrate with the Identity and Authentication Layer
In environments utilising Guest WiFi platforms, the captive portal authentication must occur at or before the Level 1 NAT boundary. This ensures the identity provider can accurately map MAC addresses and user credentials to specific internal IP addresses before traffic is aggregated into the CGNAT pool. Purple's platform handles this at the access point level, maintaining a clean user-to-IP binding that persists through the NAT translation chain.
For passwordless access deployments — as described in How a wi fi assistant Enables Passwordless Access in 2026 — the same principle applies: the identity binding must be established upstream of the CGNAT gateway to ensure accurate session attribution.
Step 5: Configure IPv6 Dual-Stack
Enable IPv6 on all access points and distribute a /64 prefix per VLAN via DHCPv6 or SLAAC. Announce IPv6 routes via your upstream provider. Verify that major CDN traffic (Google, Netflix, YouTube) is resolving to AAAA records and routing via IPv6 before reducing the size of your IPv4 NAT pool.
Best Practices
Implement Deterministic NAT Where Possible. Deterministic NAT uses an algorithmic mapping between the subscriber's internal IP address and their assigned public IP and port block. Because the mapping is mathematically computable, there is no need to maintain or log a session table — the mapping can be reverse-engineered on demand for lawful intercept purposes. This is the gold standard for compliance-conscious deployments.
Distribute the CGNAT Gateway Load. Avoid centralising all CGNAT traffic through a single appliance. Distribute gateways across the campus or across buildings to prevent a single point of failure. Distributed gateways also mitigate the IP reputation risk: if one public IP in the pool is flagged by a CDN for suspicious traffic patterns (the CAPTCHA problem), only a fraction of users are affected.
Monitor IP Reputation Proactively. Subscribe to IP reputation feeds (e.g., Spamhaus, SURBL) and monitor your public NAT pool IPs. Maintain a reserve pool of clean IPs to rotate in if an active address is blacklisted. This is particularly important in student housing, where a small number of users may engage in activities that trigger abuse flags.
Enforce Per-Subscriber Session Caps. A hard limit of 2,000 concurrent sessions per subscriber prevents a single compromised device — for example, one participating in a DDoS amplification attack — from exhausting the entire port block allocated to that public IP. For more on monitoring network performance, see our guide on How to Measure WiFi Signal Strength and Coverage .
Align with IEEE 802.1X for Access Control. Deploying IEEE 802.1X port-based authentication at the access layer ensures that only authenticated devices receive IP assignments. This reduces the risk of rogue devices consuming port allocations and provides a clean audit trail for lawful intercept purposes.
Troubleshooting & Risk Mitigation
The Logging and Compliance Burden
In the UK and Europe, under GDPR and the Investigatory Powers Act 2016, network operators must be able to trace a public IP address and port number back to a specific user at a specific timestamp. This is a non-negotiable legal obligation.
The Risk: With dynamic CGNAT, logging every session setup and teardown generates terabytes of syslog data per day. A 1,000-user deployment with dynamic allocation can produce 500 million log entries daily. This overwhelms SIEM infrastructure, increases storage costs, and makes forensic investigation impractical.
The Mitigation: Port Block Allocation reduces logging volume by up to 98%. With PBA, you log only the block assignment and release events — typically two log entries per user per session, rather than hundreds or thousands. Ensure your SIEM retains these logs for a minimum of 12 months to comply with UK data retention requirements.
The CAPTCHA and IP Reputation Problem
When 128 users share a single public IP, the aggregated traffic volume can trigger rate-limiting or anti-bot protections on major websites. Google's reCAPTCHA, Cloudflare's bot management, and similar systems use IP-based heuristics that can misclassify a shared CGNAT IP as a bot source.
The Mitigation: Distribute your CGNAT pool across multiple public IPs. Proactively monitor reputation scores. Consider deploying DNS-over-HTTPS (DoH) or DNS-over-TLS (DoT) to prevent DNS-based reputation issues. Educate users that occasional CAPTCHA prompts are a known behaviour in shared-IP environments.
Application Compatibility Issues
Certain applications — particularly peer-to-peer protocols, some VoIP implementations, and legacy gaming platforms — rely on consistent port mappings or inbound connection initiation. These can break under double NAT.
The Mitigation: For VoIP, ensure your CGNAT gateway supports ALG (Application Layer Gateway) for SIP. For gaming, consider implementing a UPnP proxy or a dedicated gaming VLAN with a separate, less-dense NAT pool. For retail environments where point-of-sale systems require inbound connectivity, place those devices on a separate VLAN that bypasses the CGNAT layer entirely.
ROI & Business Impact
Capital Expenditure Savings
Deploying CGNAT offers immediate and substantial CapEx savings. At a market rate of $50 per IPv4 address, a university with 5,000 beds requiring a 1:1 device-to-IP ratio would need to purchase approximately 35,000 IP addresses — a cost of $1.75 million. By deploying CGNAT with a 128:1 ratio, the same deployment requires fewer than 300 public IPs, reducing the IP acquisition cost to approximately $15,000.
Even accounting for the cost of CGNAT gateway hardware or virtualised network functions (typically $20,000–$80,000 for a campus-scale deployment), the net saving is substantial.
Operational Expenditure Reduction
Stable connectivity directly reduces helpdesk overhead. Port exhaustion events — the primary failure mode of standard PAT at scale — generate a disproportionate volume of support tickets. A well-configured CGNAT deployment with appropriate session limits and PBA eliminates this failure mode, reducing network-related helpdesk volume by an estimated 30–40%.
Competitive Differentiation in Student Housing
In the competitive student accommodation market, network quality is a primary selection criterion for prospective tenants. Operators who can demonstrate consistent, high-throughput connectivity — validated through WiFi Analytics dashboards showing uptime, session quality, and device density metrics — command premium rental rates and achieve higher occupancy. This infrastructure stability is also the foundation for deploying advanced location-based services, as highlighted in Purple Launches Offline Maps Mode for Seamless, Secure Navigation to WiFi Hotspots .
Case Study 1: 800-Bed University Halls of Residence
A UK university operating 800-bed halls of residence was experiencing chronic connectivity issues during evening peak hours. Investigation revealed that their single-level PAT configuration, using a /29 public subnet (6 usable IPs), was exhausting available ports by 19:30 each evening. The operator deployed a CGNAT solution with PBA (500 ports per subscriber, 128 subscribers per IP), upgraded to a /27 public subnet (30 usable IPs), and enabled IPv6 dual-stack. Post-deployment metrics showed a 94% reduction in port exhaustion events, a 38% reduction in network-related helpdesk tickets, and a 65% reduction in CGNAT log volume compared to an initial dynamic allocation pilot. The IPv6 offload rate reached 62% within 60 days of deployment.
Case Study 2: 1,200-Room Purpose-Built Student Accommodation (PBSA) Operator
A private PBSA operator managing three sites across two UK cities needed to standardise their network architecture ahead of a fourth site opening. Their existing infrastructure used a mix of single-level NAT and ad-hoc VLAN segmentation, with no consistent logging strategy. A CGNAT deployment with deterministic NAT was implemented across all three sites, enabling mathematically computable subscriber-to-IP mapping without any session logging overhead. This approach satisfied the operator's legal team regarding lawful intercept compliance, eliminated the SIEM storage cost for session logs, and provided a consistent architecture template for the fourth site. The operator also integrated Purple's Guest WiFi platform for captive portal authentication, with the identity binding established upstream of the CGNAT gateway to ensure accurate user attribution in analytics reports.
Schlüsseldefinitionen
CGNAT (Carrier-Grade NAT)
A network architecture in which an operator performs Network Address Translation at a centralised gateway, enabling multiple subscribers to share a single public IPv4 address. Defined in RFC 6264 and RFC 6888. Also known as Large-Scale NAT (LSN) or CGN.
IT teams encounter CGNAT when a single public IP is insufficient to serve all devices on a network. In student housing, CGNAT is the primary mechanism for managing IPv4 exhaustion without purchasing additional public address space.
NAT444
A specific CGNAT topology involving three layers of IPv4 address space: subscriber private addresses (RFC 1918), carrier-grade shared addresses (RFC 6598), and public internet addresses. The name refers to the three IPv4 networks traversed.
NAT444 is the standard architecture for CGNAT deployments in multi-tenant environments. Network architects must understand the three-layer model to correctly design the intermediate network and avoid address overlap.
RFC 6598 Shared Address Space
The 100.64.0.0/10 IPv4 address block (100.64.0.0 to 100.127.255.255) reserved by IANA for use in the intermediate network between a CPE and a CGNAT gateway. This space is not routable on the public internet and is specifically designed to prevent address conflicts in NAT444 deployments.
IT teams must use RFC 6598 — not RFC 1918 — for the intermediate CGNAT network. Using RFC 1918 for this segment creates address overlap risks when the same RFC 1918 ranges are used in subscriber networks.
Port Block Allocation (PBA)
A CGNAT port assignment strategy in which a contiguous block of ports (e.g., 500 ports) is assigned to each subscriber for the duration of their session, rather than allocating ports individually per connection. Defined in RFC 7422.
PBA is the recommended approach for GDPR-compliant CGNAT deployments. It reduces logging overhead by up to 98% compared to dynamic port allocation, making lawful intercept compliance operationally feasible at scale.
Deterministic NAT
A CGNAT configuration in which the mapping between a subscriber's internal IP address and their assigned public IP and port block is computed algorithmically, without maintaining a session table. The mapping is reversible mathematically, enabling subscriber identification without log retrieval.
Deterministic NAT is the gold standard for compliance-conscious deployments. It eliminates logging overhead entirely while satisfying lawful intercept requirements, as the subscriber can be identified from a public IP, port, and timestamp using the known algorithm.
PAT (Port Address Translation)
A form of Network Address Translation in which multiple private IP addresses are mapped to a single public IP address by differentiating connections using unique source port numbers. Also referred to as NAT overload or many-to-one NAT.
PAT is the standard single-level NAT used in most enterprise edge routers. It is the predecessor to CGNAT and is insufficient for dense multi-tenant environments due to port exhaustion at scale.
Session Table
A data structure maintained by a NAT gateway that records the mapping between internal (private) IP address and port, and external (public) IP address and port, for each active connection. The session table is the primary memory and processing resource consumed by CGNAT.
Session table sizing is a critical capacity planning parameter for CGNAT gateways. A 1,000-subscriber deployment with 2,000 max sessions per subscriber requires a session table capacity of at least 2 million entries. Undersizing the session table causes connection failures.
Dual-Stack
A network configuration in which both IPv4 and IPv6 protocols are simultaneously active on the same network infrastructure and end devices. Devices with dual-stack capability will prefer IPv6 for connections to IPv6-capable destinations.
Dual-stack is the recommended transition strategy for CGNAT deployments. By offloading IPv6-capable traffic to the native IPv6 path, dual-stack reduces the load on the IPv4 CGNAT pool and provides a migration path toward an IPv6-primary network.
RFC 1918 Private Address Space
The three IPv4 address ranges reserved for private network use: 10.0.0.0/8, 172.16.0.0/12, and 192.168.0.0/16. These addresses are not routable on the public internet and are used for internal network addressing.
RFC 1918 addresses are used for subscriber device addressing in CGNAT deployments. Network architects must ensure RFC 1918 ranges used in subscriber networks do not overlap with those used in the intermediate CGNAT network — which is why RFC 6598 is used for the intermediate layer.
Lawful Intercept
The legally authorised interception of communications by law enforcement agencies. In the UK, governed by the Investigatory Powers Act 2016. Network operators must be able to identify the subscriber associated with a specific public IP address, port, and timestamp upon receipt of a lawful intercept request.
Lawful intercept compliance is the primary driver of CGNAT logging requirements. Operators must retain sufficient logs to identify subscribers from public IP and port data. PBA and Deterministic NAT are the two architectures that make this feasible at scale without overwhelming logging infrastructure.
Ausgearbeitete Beispiele
A 600-bed student accommodation block currently uses a single /29 public subnet (6 usable IPs) with standard PAT. During evening peak hours (19:00–23:00), users report widespread connectivity failures. The network team has confirmed port exhaustion on the PAT router. The operator has a budget for CGNAT gateway hardware but cannot acquire additional public IPs beyond a /27 (30 usable IPs). Design a CGNAT deployment that eliminates the port exhaustion issue and supports future growth to 900 beds.
Step 1 — Baseline Assessment: With 600 beds at 5 devices per occupant, peak concurrent device count is approximately 3,000. At 500 ports per subscriber (PBA), each public IP supports 128 subscribers. With 30 usable IPs in the /27, the theoretical maximum subscriber capacity is 3,840 — sufficient for 900 beds at 4.3 devices per occupant. Step 2 — RFC 6598 Intermediate Network: Allocate 100.64.0.0/20 for the intermediate carrier-grade network, providing 4,096 addresses for CPE-to-CGNAT gateway traffic. Subnet per building wing: 100.64.0.0/24, 100.64.1.0/24, etc. Step 3 — CGNAT Gateway Sizing: Deploy a CGNAT gateway with a session table capacity of at least 768,000 entries (3,000 subscribers × 2,000 max sessions per subscriber, with 20% headroom). Configure PBA with 500-port blocks. Set max blocks per subscriber to 1, with overflow to 2 blocks permitted for subscribers exceeding 500 concurrent sessions. Step 4 — IPv6 Dual-Stack: Enable IPv6 on all access points. Distribute /64 prefixes via SLAAC. Target 60% IPv6 offload within 90 days, which effectively reduces the IPv4 CGNAT load to 1,200 concurrent IPv4 subscribers — well within the /27 capacity. Step 5 — Logging: Configure syslog to SIEM with PBA block assignment/release events only. Retain logs for 12 months minimum. Step 6 — Session Limits: Enforce 2,000 max sessions per subscriber at the CGNAT gateway to prevent abuse.
A PBSA operator has deployed CGNAT across a 1,000-bed site using dynamic port allocation. Their legal team has flagged that the current logging approach generates 400GB of syslog data per day, which is overwhelming the SIEM and making lawful intercept requests from law enforcement impractical to fulfil. Redesign the logging strategy to meet UK lawful intercept obligations while reducing log volume to a manageable level.
Step 1 — Migrate to Port Block Allocation: Replace dynamic port allocation with PBA at 500 ports per subscriber. This immediately reduces log events from one-per-session to one-per-block-assignment and one-per-block-release. For a 1,000-user deployment with an average of 3 block assignment/release cycles per user per day, this generates approximately 6,000 log entries per day — a reduction of over 99% from the dynamic allocation baseline. Step 2 — Log Schema: Ensure each PBA log entry captures: (a) subscriber internal IP address, (b) assigned public IP address, (c) assigned port block start and end, (d) timestamp of block assignment (UTC), (e) timestamp of block release (UTC), (f) subscriber identifier (MAC address or RADIUS username). Step 3 — Deterministic NAT Option: If the CGNAT platform supports it, migrate to Deterministic NAT. This eliminates logging entirely for routine operations, as the mapping is mathematically computable. Retain PBA logs only for non-deterministic overflow cases. Step 4 — Retention Policy: Retain logs for 12 months in a tamper-evident log store (e.g., write-once S3-compatible object storage). Implement access controls so that log retrieval for lawful intercept requests requires dual authorisation. Step 5 — Incident Response Procedure: Document the procedure for responding to lawful intercept requests, including the formula for reverse-computing the subscriber from a public IP, port, and timestamp under Deterministic NAT.
A university IT team reports that students are experiencing frequent CAPTCHA challenges and rate-limiting from Google, Netflix, and gaming platforms. Investigation reveals that 200 students are sharing a single public IP address through CGNAT. The team has been told that acquiring more public IPs is not possible in the short term. What immediate mitigations can be implemented without changing the IP allocation?
Step 1 — Reduce Subscriber Density: The 200:1 ratio is the primary cause. Even without additional public IPs, review whether the CGNAT pool is being used efficiently. Ensure IPv6 dual-stack is fully enabled — if 60% of traffic offloads to IPv6, the effective IPv4 subscriber count drops to approximately 80 per IP, well within the 128:1 recommended threshold. Step 2 — IP Rotation: Implement a rotation policy for the public IP pool. If the CGNAT gateway supports it, configure periodic rotation of the public IP assigned to each subscriber group. This prevents any single IP from accumulating a persistent negative reputation. Step 3 — DNS Optimisation: Ensure the DNS resolvers provided to clients return AAAA records preferentially. Many CAPTCHA triggers are DNS-based — if a client resolves a service to an IPv4 address unnecessarily, it routes through CGNAT when it could use IPv6 natively. Step 4 — Session Timeout Tuning: Reduce UDP session timeouts from the default (often 300 seconds) to 60 seconds for non-DNS UDP traffic. This frees up port space faster and reduces the apparent session volume from the perspective of external services. Step 5 — Communicate with Affected Platforms: For persistent blacklisting issues, submit delisting requests to major IP reputation databases (Spamhaus, SURBL). Document that the IP is a shared CGNAT address serving a legitimate educational institution.
Übungsfragen
Q1. A 2,000-bed student accommodation campus has a /26 public subnet (62 usable IPs). The network team is planning a CGNAT deployment. Calculate: (a) the maximum number of subscribers supportable at the recommended 128:1 ratio, (b) the total port capacity available, (c) the recommended PBA block size, and (d) whether the existing /26 is sufficient or whether additional IPs are required.
Hinweis: Start with the total usable IPs in a /26, then apply the 128:1 subscriber ratio. Compare the result against the 2,000-bed device count at a realistic devices-per-occupant ratio. Consider IPv6 dual-stack offload in your final recommendation.
Musterlösung anzeigen
A /26 provides 62 usable public IPs. At 128 subscribers per IP, the maximum IPv4 CGNAT capacity is 62 × 128 = 7,936 subscribers. At 5 devices per occupant, 2,000 beds generates approximately 10,000 concurrent devices. Without IPv6, the /26 is insufficient (7,936 < 10,000). However, with IPv6 dual-stack achieving 60% offload, the effective IPv4 load drops to approximately 4,000 devices — well within the /26 capacity of 7,936. The recommended PBA block size is 500 ports per subscriber. Total port capacity: 62 IPs × 64,000 usable ports = 3,968,000 ports. At 500 ports per subscriber: 3,968,000 / 500 = 7,936 subscribers maximum. Recommendation: Deploy CGNAT with PBA at 500 ports/subscriber, enable IPv6 dual-stack as a prerequisite, and the existing /26 is sufficient. If IPv6 offload cannot be guaranteed above 50%, acquire an additional /27 as a buffer.
Q2. A CGNAT deployment at a 500-bed student hall is generating compliance concerns. The operator's legal team has received a lawful intercept request from law enforcement for a specific public IP address (203.0.113.45), port 51432, at timestamp 2025-11-15 21:47:33 UTC. The CGNAT gateway is configured with dynamic port allocation. The SIEM contains 180 days of logs but the forensic team reports that locating the specific subscriber from the logs is taking over 4 hours per request. Identify the root cause and propose a remediation that reduces response time to under 15 minutes.
Hinweis: The 4-hour response time is a symptom of the logging architecture, not a data retention problem. Consider what information is logged under dynamic allocation versus PBA, and how Deterministic NAT would change the response process entirely.
Musterlösung anzeigen
Root cause: Dynamic port allocation generates one log entry per session. With 500 users × hundreds of sessions per user per hour, the SIEM contains millions of log entries per day. Locating a single entry by IP, port, and timestamp requires a full-text search across potentially billions of records — hence the 4-hour response time. Remediation Option 1 (PBA): Migrate to Port Block Allocation. With PBA, the log entry for port 51432 would record the block assignment (e.g., ports 51001–51500 assigned to subscriber 192.168.1.23 at 21:30:00 UTC, released at 23:15:00 UTC). A single indexed query on public IP + port range + timestamp returns the result in seconds. Estimated response time: under 2 minutes. Remediation Option 2 (Deterministic NAT): If the platform supports it, migrate to Deterministic NAT. Port 51432 can be mathematically reverse-computed to the subscriber's internal IP without any log query. Response time: under 30 seconds. Immediate action: Index the existing SIEM logs on (public_ip, port, timestamp) to reduce current response time while the PBA migration is planned.
Q3. A network architect is designing the CGNAT infrastructure for a new 800-bed PBSA development. The upstream ISP has provided a /27 public subnet and confirmed that IPv6 transit is available. The operator also wants to deploy Purple's Guest WiFi platform for captive portal authentication. Describe the correct placement of the captive portal authentication relative to the CGNAT gateway, and explain why incorrect placement creates a compliance risk.
Hinweis: Consider what information the captive portal needs to capture (user identity, device MAC, internal IP) and at what point in the NAT translation chain this information is still available. Think about what happens to the internal IP address after it passes through the CGNAT gateway.
Musterlösung anzeigen
The captive portal authentication must occur at or before the Level 1 NAT boundary — that is, at the access point or CPE layer, before traffic enters the RFC 6598 intermediate network. Correct placement: Purple's Guest WiFi platform authenticates the user at the access point. The platform records the binding: user identity → MAC address → RFC 1918 internal IP → timestamp. This binding is established before the CGNAT gateway performs its translation. The CGNAT gateway then maps the RFC 1918 IP to a public IP and port block, and the PBA log records: RFC 1918 IP → public IP → port block → timestamp. The two log records can be joined on the RFC 1918 IP and timestamp to produce a complete chain: user identity → public IP + port. Incorrect placement (captive portal after CGNAT gateway): If authentication occurs after the CGNAT gateway, the platform only sees the public IP and port — not the internal IP. Multiple users behind the same CGNAT IP are indistinguishable at this point. The platform cannot create a reliable user-to-IP binding, making lawful intercept attribution impossible and violating GDPR accountability requirements. This is the compliance risk. With Purple's architecture, the identity binding is established upstream of the CGNAT layer, ensuring accurate user attribution in both the analytics platform and the compliance log chain.