802.1X Authentication Explained for Corporate Networks
This authoritative guide provides IT leaders and network architects with a deep technical breakdown of 802.1X authentication for corporate networks. It covers architecture, EAP methods, deployment strategies, and risk mitigation to ensure secure, compliant WiFi access across multi-site environments.
Listen to this guide
View podcast transcript
- Executive Summary
- Technical Deep-Dive
- The 802.1X Architecture
- Extensible Authentication Protocol (EAP) Methods
- RADIUS Infrastructure and Integration
- Implementation Guide
- Phase 1: Network Discovery and Profiling
- Phase 2: RADIUS Infrastructure Deployment
- Phase 3: Policy Configuration and Segmentation
- Phase 4: Supplicant Provisioning
- Phase 5: Phased Rollout and Testing
- Best Practices
- Troubleshooting & Risk Mitigation
- Common Failure Modes
- Risk Mitigation Strategies
- ROI & Business Impact
Executive Summary
For enterprise environments spanning hospitality, retail, and public sector operations, the perimeter has dissolved. Hybrid workforces, BYOD policies, and an explosion of connected devices mean that securing corporate networks via Pre-Shared Keys (PSKs) is no longer a viable strategy. Modern compliance frameworks—including PCI DSS v4.0 and GDPR—demand stringent, identity-based access controls for any network handling sensitive data.
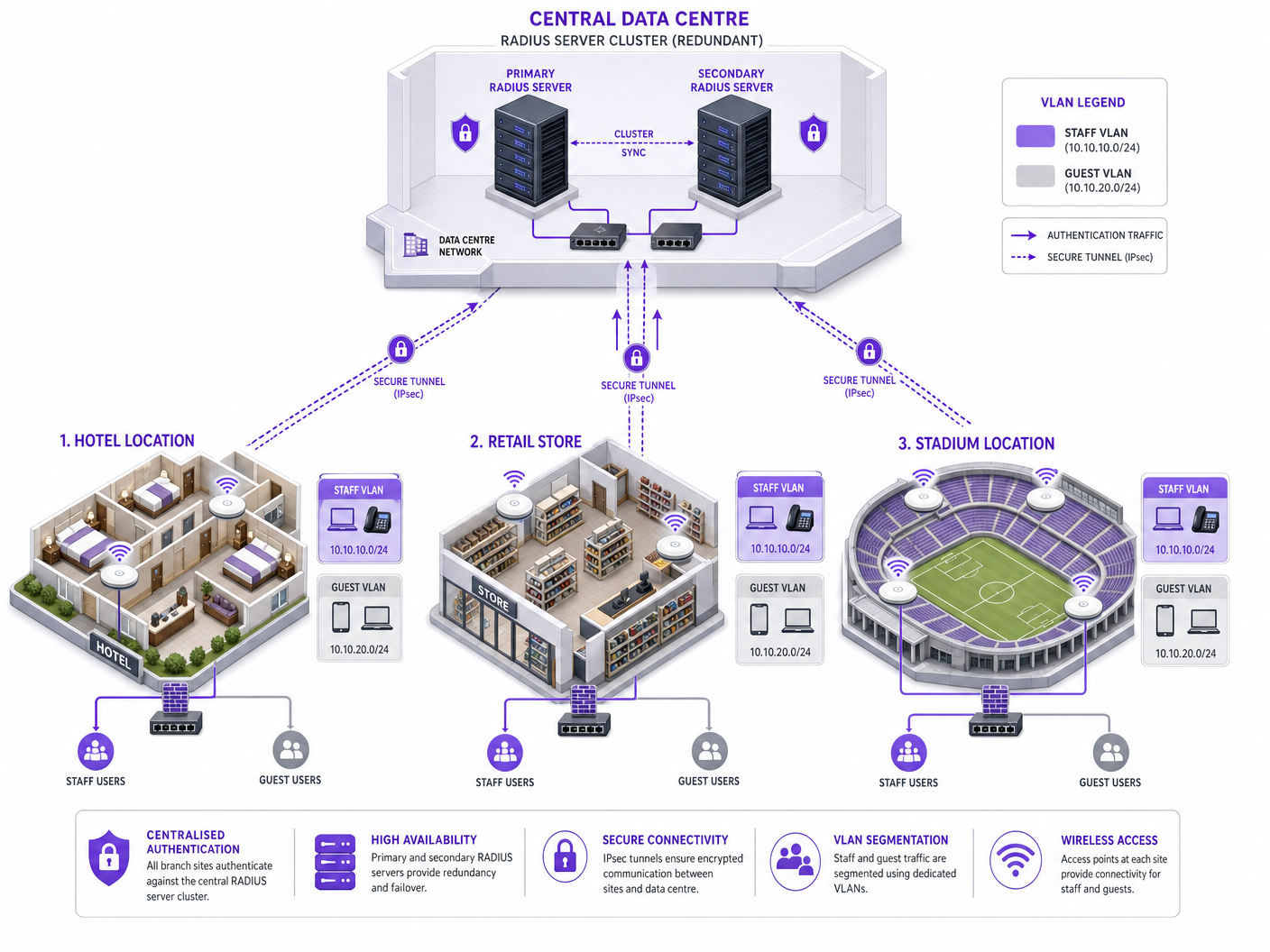
This guide details the architecture and implementation of IEEE 802.1X, the standard for port-based network access control. By shifting authentication from a shared password to a verified identity backed by a central RADIUS infrastructure, organisations can enforce dynamic segmentation, mitigate credential theft, and ensure that only authorised devices access corporate resources. Designed for network architects and IT directors, this document provides the technical depth required to architect, deploy, and troubleshoot 802.1X across complex, multi-site topologies.
Technical Deep-Dive
The 802.1X Architecture
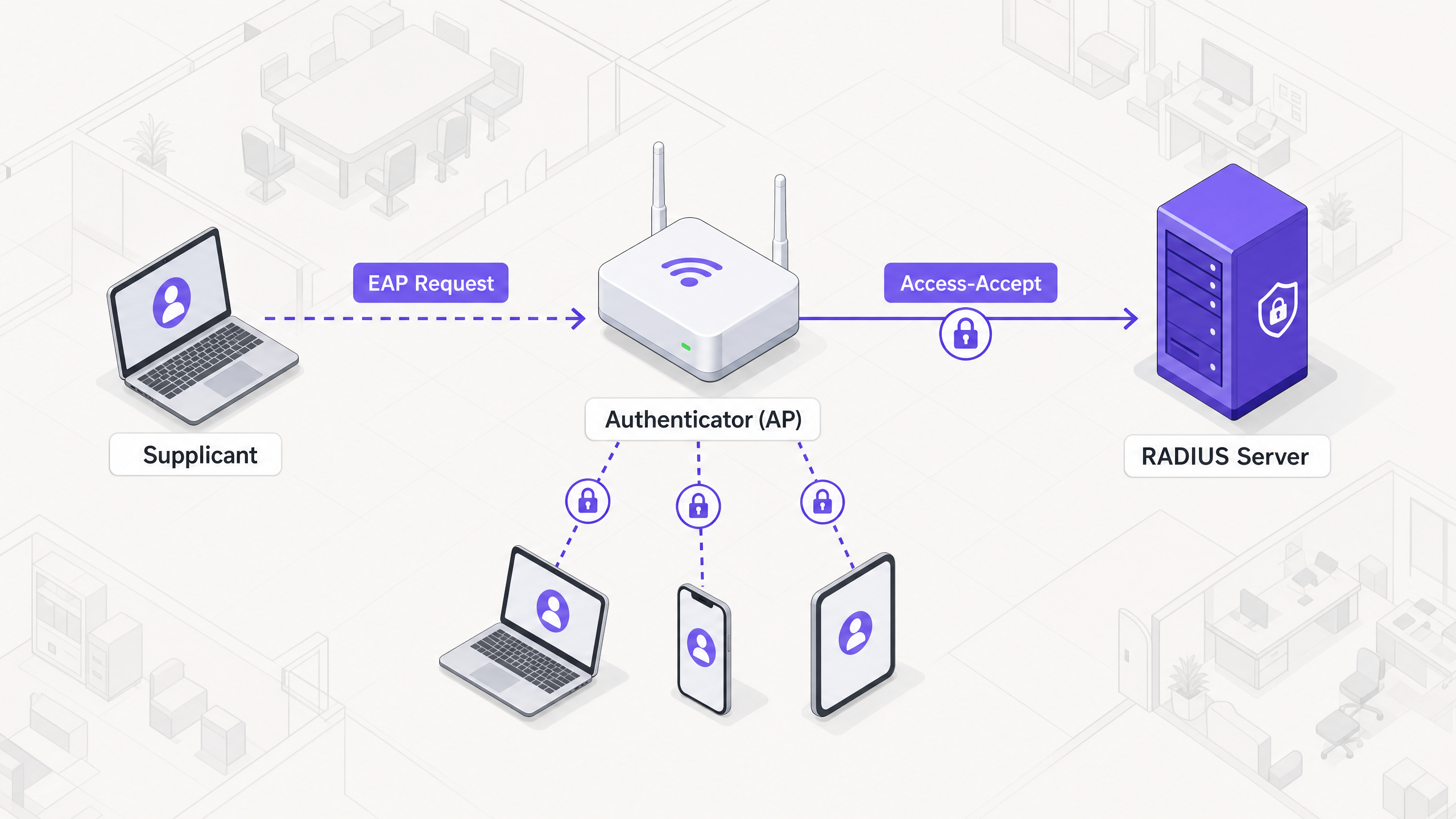
The 802.1X framework relies on three distinct components working in concert to secure network access:
- Supplicant: The endpoint device (e.g., laptop, smartphone) requesting access to the network.
- Authenticator: The network device (typically a wireless access point or switch) that controls physical or logical access to the network.
- Authentication Server: The central database (almost exclusively a RADIUS server) that validates the supplicant's credentials and authorises access.
When a supplicant attempts to connect to an 802.1X-secured SSID, the authenticator places the connection in an unauthorised state, blocking all traffic except Extensible Authentication Protocol (EAP) frames. The authenticator acts as a pass-through, encapsulating EAP messages from the supplicant into RADIUS packets and forwarding them to the authentication server.
Extensible Authentication Protocol (EAP) Methods
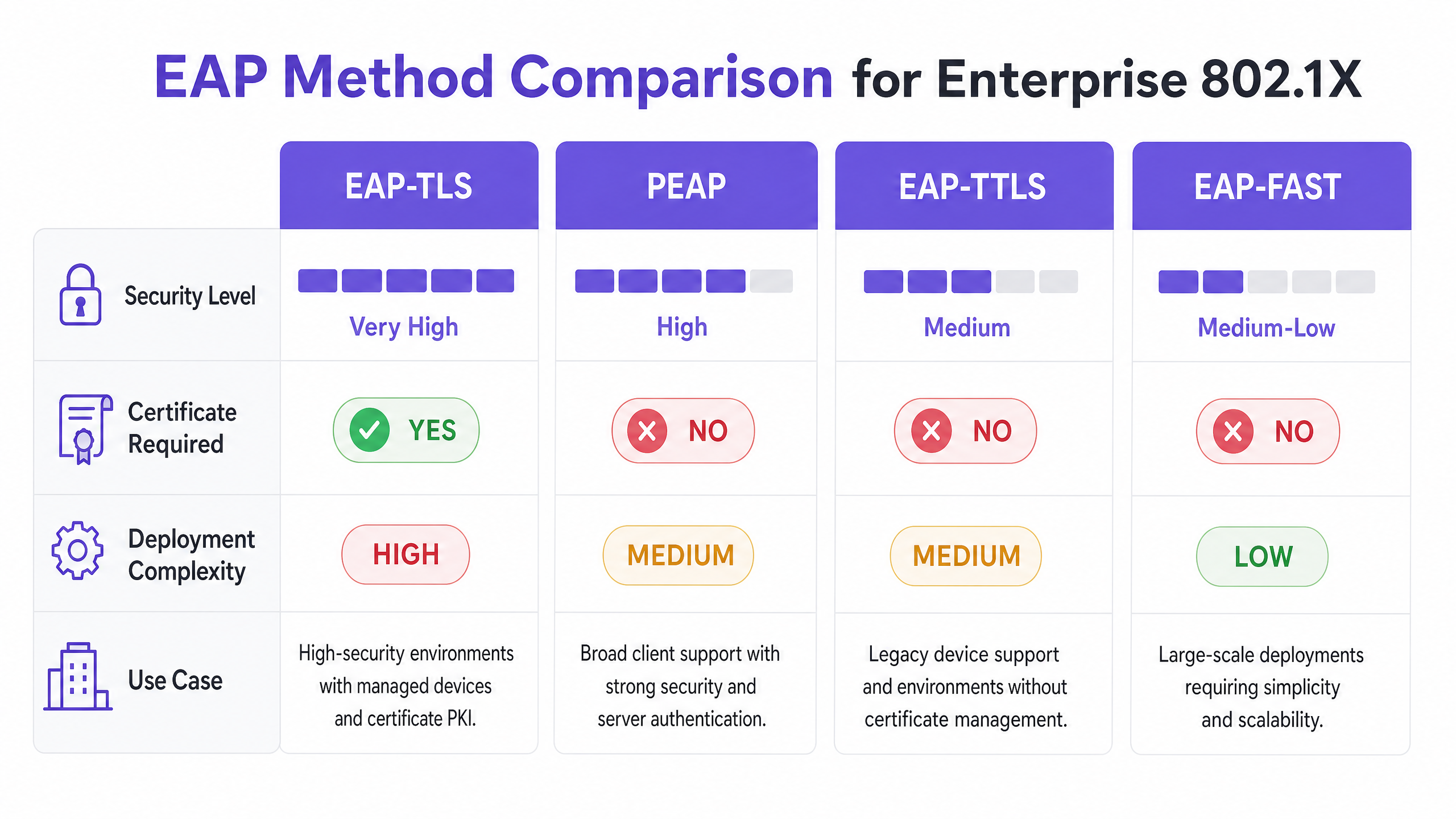
EAP is the transport mechanism for the actual authentication credentials. Selecting the appropriate EAP method is a critical architectural decision, balancing security requirements with deployment complexity.
- EAP-TLS (Transport Layer Security): The gold standard for enterprise security. It requires both a server certificate and a client certificate, providing mutual authentication. Because it relies on certificates rather than passwords, it is immune to credential phishing and offline dictionary attacks. However, it requires a robust Public Key Infrastructure (PKI) and Mobile Device Management (MDM) solution to provision and manage client certificates at scale.
- PEAP (Protected EAP): The most widely deployed method due to its balance of security and ease of deployment. PEAP requires a certificate only on the RADIUS server. It establishes a secure TLS tunnel between the supplicant and the server, inside of which the user's credentials (username and password) are transmitted securely. Proper configuration requires locking down the supplicant to trust only the specific RADIUS server certificate to prevent rogue AP attacks.
- EAP-TTLS (Tunneled TLS): Similar to PEAP, it establishes a secure tunnel using a server certificate. However, EAP-TTLS supports a wider range of inner authentication protocols, making it suitable for environments with legacy systems or non-Windows endpoints that do not support MSCHAPv2.
- EAP-FAST (Flexible Authentication via Secure Tunneling): Developed by Cisco as a faster alternative to certificate-based methods. It uses Protected Access Credentials (PACs) established dynamically between the client and server. While efficient, it is less commonly deployed in modern, vendor-neutral architectures.
RADIUS Infrastructure and Integration
The RADIUS server is the engine of 802.1X. Common enterprise solutions include Microsoft Network Policy Server (NPS), FreeRADIUS, and commercial offerings like Cisco ISE or Aruba ClearPass. The RADIUS server integrates with the organisation's identity provider (IdP)—such as Active Directory, Entra ID, or Okta—to validate credentials.
Crucially, the RADIUS server can return specific attributes in the Access-Accept message, enabling dynamic network configuration. The most powerful of these is dynamic VLAN assignment. Based on the user's group membership or device posture, the RADIUS server instructs the authenticator to place the connection into a specific VLAN. This allows for seamless micro-segmentation: a staff member is placed in the corporate VLAN, a contractor in a restricted VLAN, and a device failing posture checks in a quarantine VLAN.
Implementation Guide
Deploying 802.1X across a multi-site enterprise requires a phased, methodical approach to minimise disruption.
Phase 1: Network Discovery and Profiling
Before altering any configurations, conduct a comprehensive audit of all devices connecting to the network. This is particularly critical in environments like Hospitality and Retail , where headless devices (printers, POS terminals, IoT sensors) are prevalent. These devices typically lack an 802.1X supplicant. You must identify them and plan for alternative authentication methods, such as MAC Authentication Bypass (MAB), ensuring they are isolated in restricted VLANs.
Phase 2: RADIUS Infrastructure Deployment
Deploy a highly available RADIUS architecture. A single RADIUS server is a single point of failure that can take down the entire corporate network. Implement a primary and secondary server cluster, ideally distributed across distinct data centres or cloud availability zones. Configure authenticators (APs and switches) to failover automatically if the primary server becomes unresponsive.
Phase 3: Policy Configuration and Segmentation
Define granular access policies within the RADIUS server. Map Active Directory groups to specific VLANs and Access Control Lists (ACLs). Ensure that the policies enforce the principle of least privilege. For example, in a Healthcare setting, clinical staff should have access to patient record systems, while administrative staff are segmented into a different VLAN with access only to billing systems.
Phase 4: Supplicant Provisioning
For PEAP deployments, use Group Policy Objects (GPOs) or MDM profiles to push the required wireless network settings to managed devices. Crucially, configure the profile to strictly validate the server certificate and specify the exact RADIUS server names to trust. This prevents users from inadvertently connecting to rogue access points.
For unmanaged devices, refer to our guide on Secure BYOD Policies for Staff WiFi Networks for strategies on onboarding personal devices securely without compromising the corporate network.
Phase 5: Phased Rollout and Testing
Never execute a "big bang" deployment. Begin with a pilot group in a single location. Monitor RADIUS logs meticulously for authentication failures. Test edge cases, including server failover, certificate expiration, and roaming between access points. Only proceed to a wider rollout once the pilot is stable.
Best Practices
- Enforce Server Certificate Validation: This is the most critical security control for PEAP deployments. If supplicants do not validate the server certificate, the network is vulnerable to Man-in-the-Middle (MitM) attacks.
- Implement Dynamic VLAN Assignment: Do not rely on static VLANs per SSID. Use RADIUS attributes to dynamically assign VLANs based on user identity, drastically reducing the attack surface.
- Secure Headless Devices with MAB: Use MAC Authentication Bypass strictly for devices that cannot support 802.1X. Ensure these devices are placed in heavily restricted VLANs, as MAC addresses are easily spoofed.
- Separate Guest and Corporate Traffic: Maintain a strict logical separation between 802.1X-secured corporate networks and open or portal-based guest networks. For advanced guest access management, consider solutions like Purple's Guest WiFi platform.
Troubleshooting & Risk Mitigation
Common Failure Modes
- Certificate Expiration: An expired RADIUS server certificate will cause widespread authentication failures for PEAP and EAP-TLS clients. Implement robust monitoring and alerting for certificate validity periods.
- Clock Skew: 802.1X relies heavily on accurate timekeeping, particularly for certificate validation. Ensure all infrastructure components (RADIUS servers, IdPs, APs) are synchronised to a reliable NTP source.
- RADIUS Server Unreachability: Network connectivity issues between the authenticator and the RADIUS server will result in access denial. Implement redundant network paths and configure APs with multiple RADIUS server IPs.
- Supplicant Misconfiguration: Incorrectly configured supplicants (e.g., wrong EAP method, missing root CA) are a common source of helpdesk tickets. Use MDM to enforce consistent configurations.
Risk Mitigation Strategies
To mitigate the risk of deployment-induced downtime, establish a robust audit trail for all configuration changes to the RADIUS infrastructure. This ensures rapid rollback capabilities in the event of an unforeseen issue.
ROI & Business Impact
Implementing 802.1X delivers significant business value beyond basic security compliance:
- Reduced Operational Overhead: By eliminating the need to rotate Pre-Shared Keys when staff leave or keys are compromised, IT teams save significant administrative time.
- Enhanced Compliance: 802.1X provides the identity-based access controls required to meet stringent regulatory frameworks (PCI DSS, HIPAA, GDPR), avoiding costly fines and reputational damage.
- Improved Threat Containment: Dynamic VLAN assignment ensures that if a device is compromised, the blast radius is limited to a specific network segment, preventing lateral movement across the enterprise.
- Data-Driven Insights: When combined with platforms like Purple's WiFi Analytics , the identity data provided by 802.1X can offer deep insights into network utilisation and capacity planning.
Key Definitions
Supplicant
The client device or software requesting access to the network.
Essential for understanding where the authentication request originates and how credentials are provided.
Authenticator
The network device (AP or switch) that acts as a gatekeeper, blocking access until authentication succeeds.
The authenticator does not verify credentials; it merely passes them to the RADIUS server.
RADIUS Server
Remote Authentication Dial-In User Service; the central server that validates credentials against an identity store.
The core decision engine of an 802.1X deployment.
EAP (Extensible Authentication Protocol)
A framework for transporting authentication credentials securely over the network.
Understanding EAP is crucial for selecting the right authentication method (e.g., PEAP vs. EAP-TLS).
Dynamic VLAN Assignment
The process where a RADIUS server instructs the authenticator to place a user in a specific VLAN based on their identity.
A key benefit of 802.1X, enabling automated network segmentation.
MAC Authentication Bypass (MAB)
A fallback authentication method that uses a device's MAC address as its credential.
Required for onboarding IoT and legacy devices that cannot support 802.1X.
PKI (Public Key Infrastructure)
The system used to issue, manage, and validate digital certificates.
A prerequisite for deploying EAP-TLS authentication.
Rogue AP Attack
An attack where a malicious access point impersonates the corporate network to harvest credentials.
Highlighting the importance of enforcing server certificate validation in PEAP deployments.
Worked Examples
A 200-room hotel needs to secure its staff WiFi network. The current setup uses a single PSK for all staff devices (laptops, tablets) and IoT devices (smart thermostats, IP cameras). How should they transition to 802.1X?
- Deploy a redundant RADIUS infrastructure (e.g., FreeRADIUS) integrated with the hotel's Active Directory. 2. Audit all devices. 3. Configure the wireless controller to use 802.1X (PEAP-MSCHAPv2) for the staff SSID. 4. Push MDM profiles to staff laptops and tablets enforcing server certificate validation. 5. For IoT devices, configure MAC Authentication Bypass (MAB) on the RADIUS server, placing them in an isolated IoT VLAN. 6. Use RADIUS attributes to dynamically assign staff devices to the corporate VLAN upon successful authentication.
A retail chain is rolling out 802.1X across 50 stores. During the pilot phase in Store 1, users report intermittent authentication failures, particularly when moving between the stockroom and the shop floor.
The issue is likely related to roaming and re-authentication delays. The solution is to enable Fast BSS Transition (802.11r) and Opportunistic Key Caching (OKC) on the wireless controller and access points. This allows the client device to cache the Pairwise Master Key (PMK) derived during the initial 802.1X authentication, enabling rapid roaming between APs without requiring a full RADIUS round-trip.
Practice Questions
Q1. Your organisation is migrating from PSK to 802.1X. You have a fleet of 5,000 corporate-owned Windows laptops managed via Microsoft Intune. You want the highest level of security to prevent credential theft. Which EAP method should you deploy?
Hint: Consider which method eliminates the use of passwords entirely.
View model answer
EAP-TLS. Since the devices are corporate-owned and managed via Intune, you can leverage MDM to deploy client certificates at scale. EAP-TLS provides mutual authentication and is immune to password-based attacks like phishing or offline dictionary attacks.
Q2. During a security audit, it is discovered that users can connect to the corporate 802.1X network using their personal smartphones without any MDM profile installed. What is the primary security risk, and how should it be remediated?
Hint: Think about how PEAP validates the server.
View model answer
The primary risk is a Man-in-the-Middle (MitM) or Rogue AP attack. If users manually configure the connection, they often accept any server certificate presented to them. To remediate this, the organisation must enforce a policy where only managed devices (with an MDM profile that strictly validates the specific RADIUS server certificate) are allowed on the corporate SSID. Personal devices should be directed to a separate BYOD or Guest network.
Q3. A remote branch office loses WAN connectivity to the central data centre where the primary and secondary RADIUS servers reside. What happens to the wireless clients at the branch office?
Hint: Consider where the authentication decision is made.
View model answer
New clients attempting to connect will fail authentication because the authenticator (AP) cannot reach the RADIUS server to validate credentials. Existing connected clients may remain connected until their session times out or they need to re-authenticate (e.g., roaming to a new AP), at which point they will also lose access. To mitigate this, survivable branch architectures often deploy a local, read-only domain controller and a local RADIUS proxy or server at critical branch sites.