Securing Hybrid Working: Combining NAC with ZTNA for Seamless Access
This authoritative technical guide covers the architectural convergence of Network Access Control (NAC) and Zero Trust Network Access (ZTNA) to secure hybrid working environments across corporate, retail, hospitality, and public sector venues. It provides a phased deployment blueprint, real-world case studies, and compliance guidance for IT architects and CTOs who need to eliminate the security gaps created by isolated on-premises and cloud access domains.
Listen to this guide
View podcast transcript
- Executive Summary
- Technical Deep-Dive: The Convergence Architecture
- The Limitations of Isolated Security Domains
- Unified Identity and Context Brokerage
- Implementation Guide: Step-by-Step Deployment
- Phase 1: Identity and Asset Discovery
- Phase 2: Policy Definition and Micro-Segmentation
- Phase 3: Enforcement and Optimisation
- Best Practices for Enterprise Environments
- Troubleshooting & Risk Mitigation
- ROI & Business Impact

Executive Summary
For enterprise network architects and CTOs managing distributed environments, the perimeter has irrevocably dissolved. The traditional model of securing a corporate headquarters with robust Network Access Control (NAC) while relying on legacy VPNs for remote access is no longer viable. Modern enterprises require a unified security posture that seamlessly bridges on-premises infrastructure with cloud-native applications. This guide details the architectural integration of NAC and Zero Trust Network Access (ZTNA), providing a blueprint for securing hybrid working environments without compromising user experience or network throughput.
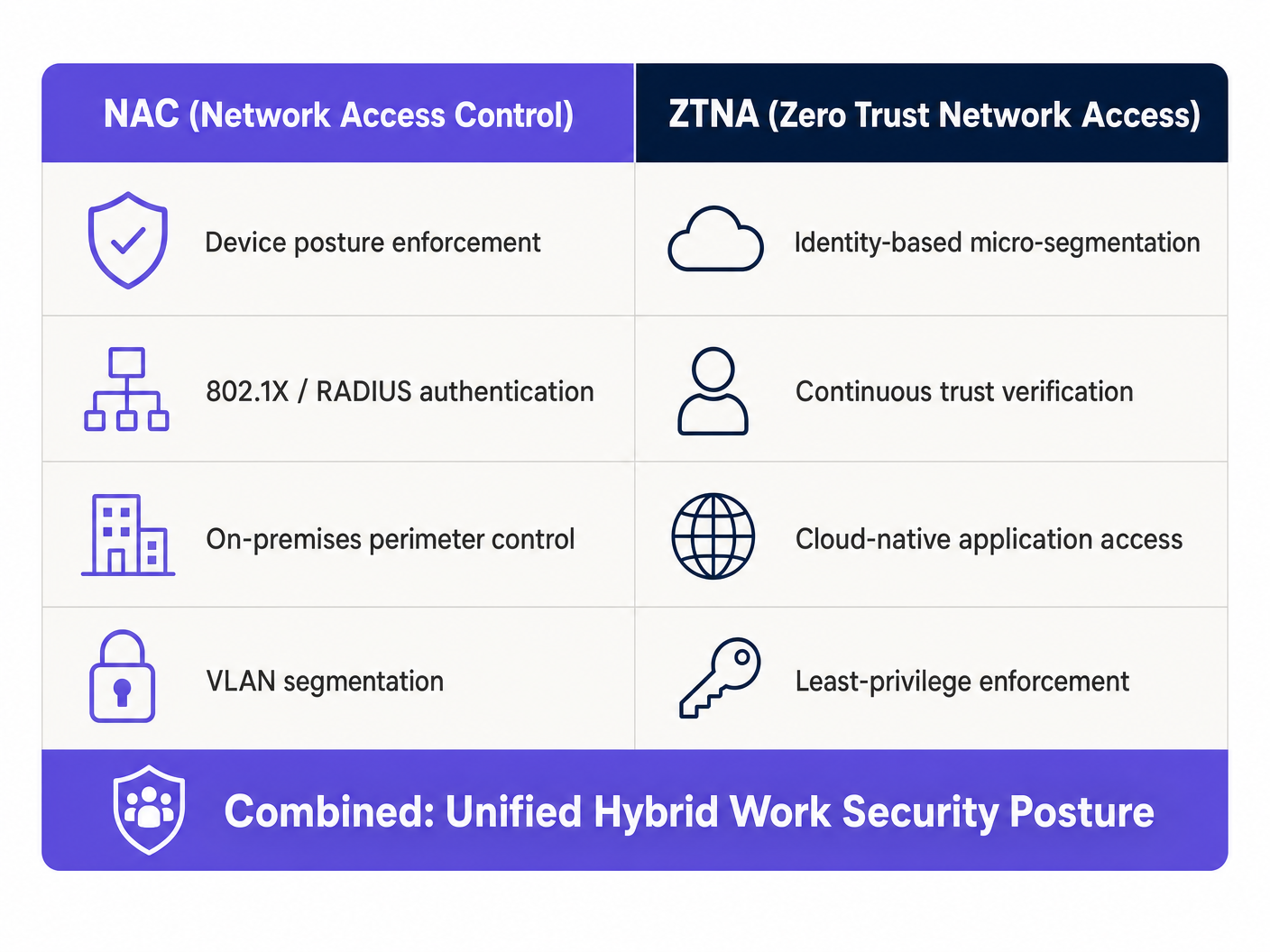
By combining the device-level posture enforcement of NAC with the identity-centric micro-segmentation of ZTNA, organisations can achieve continuous trust verification regardless of the user's location. This convergence is particularly critical for sectors with high footfall and complex compliance requirements, such as Retail , Healthcare , and Hospitality . Furthermore, leveraging platforms like Purple's Guest WiFi infrastructure can extend these zero-trust principles to guest networks, ensuring robust isolation and data protection aligned with GDPR and PCI DSS obligations.
Technical Deep-Dive: The Convergence Architecture
The Limitations of Isolated Security Domains
Historically, NAC and ZTNA operated as isolated security domains. NAC, leveraging IEEE 802.1X and RADIUS, excelled at controlling physical and wireless access within the corporate perimeter. It provided robust device profiling, posture assessment, and VLAN assignment. Conversely, ZTNA emerged to secure remote access to cloud and on-premises applications, operating on the principle of "never trust, always verify" based on user identity and context, rather than network location.
The friction arises when hybrid workers transition between these domains. A user authenticating seamlessly via ZTNA at home often faces a disjointed experience when entering the corporate office, where NAC policies may not align with their ZTNA context. This fragmentation introduces security blind spots and operational overhead that directly impacts both IT efficiency and end-user productivity.
Unified Identity and Context Brokerage
The architectural solution lies in establishing a unified identity and context brokerage layer that synchronises telemetry between the NAC and ZTNA policy engines. This integration allows for continuous posture assessment that persists across network boundaries.
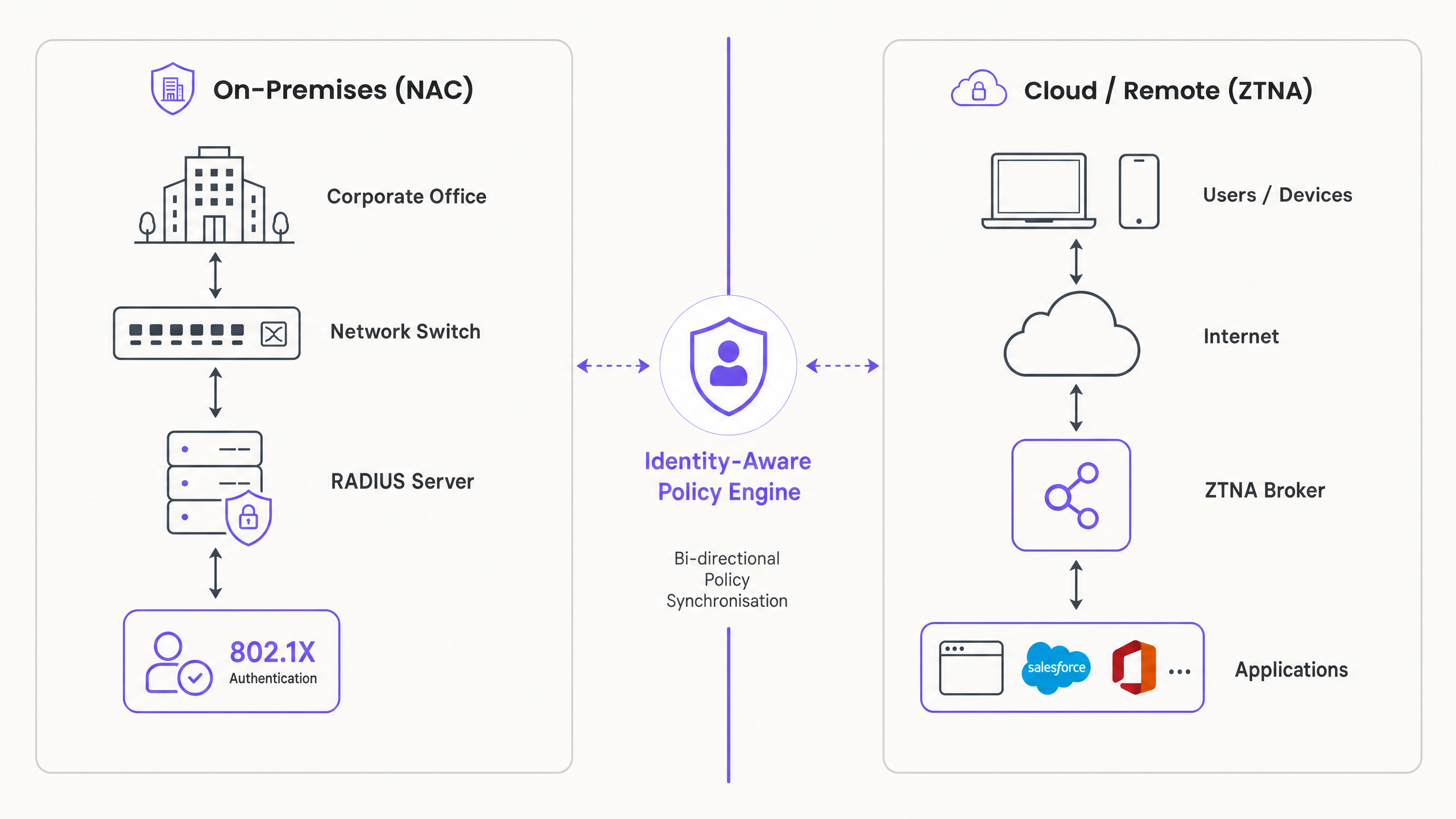
The integration operates across three key mechanisms. First, Continuous Posture Assessment: when a device connects to the corporate network, the NAC solution performs a comprehensive posture check covering OS version, AV status, and certificate validation. This context is immediately shared with the ZTNA broker via API integration. Second, Dynamic Policy Enforcement: if the device's posture degrades — for example, malware is detected — the NAC system quarantines the device on the local network, while simultaneously instructing the ZTNA broker to revoke access to critical cloud applications. Third, Seamless Transition: as the user moves from the office to a remote location, the ZTNA client maintains the established trust context, eliminating the need for re-authentication and ensuring uninterrupted access to authorised resources.
For a deeper understanding of the underlying wireless technologies supporting these deployments, refer to our guide on Wi Fi Frequencies: A Guide to Wi-Fi Frequencies in 2026 .
Implementation Guide: Step-by-Step Deployment
Deploying a converged NAC/ZTNA architecture requires a phased approach to minimise disruption and ensure robust policy enforcement.
Phase 1: Identity and Asset Discovery
Before implementing enforcement policies, you must achieve complete visibility into your network environment. Deploy your NAC solution in monitor-only mode — configure it to discover and profile all connected devices, including corporate laptops, BYOD, IoT, and guest devices, without blocking access. Consolidate user identities by integrating both NAC and ZTNA solutions with a central Identity Provider such as Azure AD or Okta. This ensures consistent authentication policies across both domains. Simultaneously, utilise your ZTNA solution to monitor application access patterns, identifying which users require access to specific applications and forming the basis for your micro-segmentation policies.
Phase 2: Policy Definition and Micro-Segmentation
Transition from visibility to control by defining granular access policies based on the principle of least privilege. Establish baseline security requirements for corporate devices, including minimum OS version and active EDR agent requirements, and configure the NAC solution to enforce these requirements for on-premises access. Define ZTNA policies that restrict access to applications based on user role and device context, ensuring alignment with the posture requirements defined in the NAC solution. Critically, configure the API integration between your NAC and ZTNA platforms to enable bidirectional context sharing, ensuring that a change in device posture detected by NAC immediately triggers a policy update in the ZTNA broker.
Phase 3: Enforcement and Optimisation
Gradually enable enforcement mode, monitoring for anomalies and refining policies as needed. Transition the NAC solution from monitor mode to enforcement mode, starting with a pilot group of users or locations, and monitor for authentication failures. Roll out the ZTNA client to all corporate endpoints, ensuring seamless access to cloud and on-premises applications. Extend robust guest access policies using platforms like Purple's Guest WiFi , ensuring guest traffic is strictly isolated from corporate resources. Leverage WiFi Analytics to monitor usage patterns and detect potential anomalies across the guest estate.
Best Practices for Enterprise Environments
Prioritise user experience throughout the deployment. Security should not impede productivity, and the transition between on-premises and remote access must be transparent to the user, leveraging single sign-on and continuous authentication mechanisms. For on-premises access, mandate IEEE 802.1X authentication for all corporate devices, as this provides robust cryptographic validation of device identity at the port level.
Integrate AI-driven threat detection capabilities into your NAC and ZTNA solutions to identify anomalous behaviour and automatically quarantine compromised devices. For a forward-looking perspective on this capability, see The Future of Wi-Fi Security: AI-Driven NAC and Threat Detection and the Spanish-language equivalent El Futuro de la Seguridad Wi-Fi: NAC Impulsado por IA y Detección de Amenazas . For distributed enterprises, integrating ZTNA with SD-WAN can optimise application routing and improve performance across multiple sites — review our comparison on SD WAN vs MPLS: The 2026 Enterprise Network Guide .
Troubleshooting & Risk Mitigation
Context Synchronisation Delays represent the most critical failure mode. If the API integration between NAC and ZTNA experiences latency, a compromised device might retain access to cloud applications longer than acceptable. The mitigation is to implement webhook-based push notifications rather than relying solely on polling mechanisms, ensuring near real-time policy updates.
Overly Restrictive Policies can cause significant helpdesk ticket spikes when implementing strict posture checks without adequate user communication. Utilise captive portals to inform users of non-compliance and provide self-service remediation instructions before blocking access entirely.
IoT Device Authentication Failures are inevitable in venue environments. Headless IoT devices cannot support 802.1X or ZTNA clients. The solution is MAC Authentication Bypass (MAB) combined with rigorous device profiling and strict VLAN segmentation to isolate IoT traffic from corporate resources.
API Integration Health Monitoring is frequently overlooked. If the synchronisation between NAC and ZTNA breaks, a security gap exists that neither system can independently resolve. Implement dedicated monitoring and alerting on the integration health, and define fail-safe policies that trigger automatic access restrictions if the sync is lost for more than a defined threshold.
ROI & Business Impact
The convergence of NAC and ZTNA delivers measurable business value beyond risk mitigation. Consolidating policy management reduces the administrative burden on IT teams, allowing them to focus on strategic initiatives rather than managing disparate security silos. Eliminating legacy VPNs significantly improves the hybrid work experience, reducing downtime and frustration while improving application performance for remote users.
The ability to demonstrate continuous posture assessment and identity-based access control simplifies compliance reporting for frameworks such as PCI DSS and GDPR, particularly relevant in Transport and retail environments where cardholder data and personal data protection obligations are stringent. Organisations that have deployed converged architectures consistently report a reduction in mean time to contain (MTTC) security incidents, as the bidirectional policy enforcement enables automated quarantine without requiring manual intervention.
Key Definitions
Network Access Control (NAC)
A security solution that enforces policy on devices seeking access to a network infrastructure, typically utilising IEEE 802.1X for authentication and posture assessment to determine VLAN assignment and access rights.
Critical for securing on-premises environments, ensuring only compliant and authorised devices can connect to corporate switches and wireless access points. IT teams encounter this when managing physical office and venue networks.
Zero Trust Network Access (ZTNA)
An IT security solution that provides secure remote access to applications and services based on defined access control policies, operating on the principle of least privilege and continuous identity verification rather than network location.
Replaces legacy VPNs by providing identity-based micro-segmentation, granting access only to specific applications rather than the entire network. Relevant when securing remote workers and cloud application access.
Micro-segmentation
The practice of dividing a network into isolated segments to reduce the attack surface and prevent lateral movement by threat actors, applied at the application or workload level rather than the network perimeter.
ZTNA applies this concept at the application level, ensuring a compromised endpoint cannot pivot to access unauthorised resources. IT teams encounter this when designing zero-trust architectures.
Posture Assessment
The process of evaluating a device's security state — including OS version, active antivirus, installed certificates, and patch level — before granting network or application access.
A core function of NAC, ensuring that vulnerable or compromised devices are quarantined or remediated before they can interact with the corporate network. Relevant during device onboarding and continuous monitoring.
IEEE 802.1X
An IEEE standard for port-based Network Access Control, providing an authentication mechanism to devices wishing to attach to a LAN or WLAN, using EAP (Extensible Authentication Protocol) over the network medium.
The gold standard for enterprise network authentication, providing robust cryptographic validation of device identity. IT teams encounter this when configuring switches, wireless controllers, and RADIUS servers.
RADIUS (Remote Authentication Dial-In User Service)
A networking protocol that provides centralised Authentication, Authorisation, and Accounting (AAA) management for users who connect and use a network service, acting as the communication layer between NAC and identity providers.
The backend protocol utilised by NAC solutions to communicate with identity providers and enforce access policies. Relevant when integrating NAC with Active Directory or cloud IdPs.
MAC Authentication Bypass (MAB)
A fallback authentication method used by NAC solutions for devices that do not support 802.1X, relying on the device's MAC address as an identifier to assign network access policies.
Necessary for accommodating headless devices — printers, IoT sensors, digital signage — in enterprise environments. Less secure than 802.1X and requires strict VLAN segmentation to mitigate MAC spoofing risks.
Identity Provider (IdP)
A system entity that creates, maintains, and manages identity information for principals while providing authentication services to relying applications within a federation or distributed network.
The central source of truth for user identities, integrating with both NAC and ZTNA to ensure consistent authentication policies. IT teams encounter this when configuring SSO and MFA across enterprise systems.
VLAN (Virtual Local Area Network)
A logical subdivision of a physical network that groups devices into isolated broadcast domains, enabling traffic segmentation without requiring separate physical infrastructure.
The primary mechanism for isolating different device classes — corporate, guest, IoT — within a shared physical network. Critical for compliance with PCI DSS requirements for cardholder data environment isolation.
Worked Examples
A global retail chain with 500 locations needs to secure access for regional managers who frequently travel between stores, corporate headquarters, and remote home offices. They currently experience frequent VPN disconnects and inconsistent access to cloud-hosted inventory management applications.
Implement a converged NAC/ZTNA architecture across all locations. Deploy 802.1X via NAC for seamless, secure access when managers are physically in-store or at HQ, authenticating against a centralised RADIUS server integrated with Azure AD. Deploy a ZTNA client on all corporate laptops. Integrate the NAC and ZTNA policy engines via API, configuring webhook notifications for immediate posture updates. When a manager connects to the in-store network, the NAC authenticates the device and shares the 'trusted internal' context with the ZTNA broker. The ZTNA broker then grants direct, optimised access to the cloud-hosted inventory application without requiring a VPN tunnel, reducing latency and eliminating disconnection issues. When the manager works from home, the ZTNA client establishes a secure micro-tunnel to the application, maintaining the same access policies without relying on the corporate network perimeter. Guest and IoT devices in-store are isolated on separate VLANs managed via Purple's Guest WiFi platform.
A large conference centre needs to provide secure WiFi for corporate staff while isolating thousands of daily guest connections and third-party vendor IoT devices including digital signage, BLE beacons, and environmental sensors.
Deploy a robust NAC solution configured with strict VLAN segmentation across three distinct tiers. Tier one: corporate staff devices authenticate via 802.1X and are assigned to a secure internal VLAN with full access to internal management systems. Tier two: implement Purple's Guest WiFi platform to manage public access, capturing valuable analytics while ensuring complete isolation from the corporate network via a dedicated guest VLAN with internet-only access. Tier three: for vendor IoT devices, utilise MAC Authentication Bypass (MAB) combined with deep device profiling — analysing DHCP fingerprints, HTTP user agents, and traffic patterns — to accurately identify device types and assign them to restricted, internet-only VLANs. Integrate ZTNA for corporate staff to access internal management applications securely from any location within the venue or remotely. For BLE beacon infrastructure, refer to the guide on BLE Low Energy Explained for Enterprise for integration considerations.
Practice Questions
Q1. Your organisation is deploying ZTNA to replace a legacy VPN. However, users returning to the corporate office are experiencing latency when accessing applications hosted locally in the on-premises data centre, as ZTNA traffic is routing through a cloud-hosted broker. What is the recommended architectural solution?
Hint: Consider how the ZTNA client determines the optimal path to the application based on the user's physical network context.
View model answer
Implement a Local Edge or On-Premises ZTNA Broker within the corporate data centre. Configure the ZTNA client to detect when the device is authenticated on the internal corporate network via NAC and route traffic directly to the local application via the internal broker, rather than hair-pinning through the cloud-hosted broker. This reduces latency for on-premises applications while maintaining the same identity-based access controls. The NAC context sharing via API should signal to the ZTNA broker that the device is on a trusted internal network, enabling the local routing decision.
Q2. A hospital IT team needs to secure hundreds of connected medical devices — infusion pumps, patient monitors, imaging equipment — that cannot run 802.1X supplicants or ZTNA clients. How should these devices be secured within a converged NAC/ZTNA architecture?
Hint: Consider fallback authentication methods and the principle of network-level isolation for devices that cannot participate in identity-based controls.
View model answer
Utilise MAC Authentication Bypass (MAB) on the NAC solution, combined with deep device profiling using DHCP fingerprints, HTTP user agents, and traffic behaviour analysis to accurately identify and classify each medical device type. Once identified, the NAC dynamically assigns these devices to highly restricted, isolated VLANs that only permit communication with specific, required medical servers and systems — blocking all other traffic by default. ZTNA is not applicable to these devices; security relies entirely on strict network segmentation and continuous traffic monitoring for anomalous behaviour. Ensure the medical device VLANs are completely isolated from the cardholder data environment to maintain PCI DSS compliance.
Q3. During a production deployment, the API integration between your NAC and ZTNA solutions fails silently — no alerts are triggered. A user's laptop on the corporate network subsequently becomes infected with malware. Describe the expected security outcome and identify the architectural gap that allowed it.
Hint: Analyse the impact of broken context synchronisation on each policy engine independently, and consider what monitoring should have been in place.
View model answer
The NAC solution will detect the degraded posture via EDR integration and quarantine the device on the local network, preventing lateral movement within the corporate environment. However, because the API integration has failed silently, the ZTNA broker has not received the updated posture context. If the user attempts to access a cloud application, the ZTNA client may still establish a connection if the initial identity authentication token remains valid and has not expired. The architectural gap is twofold: first, the absence of health monitoring on the API integration itself; second, the lack of a fail-safe policy that triggers automatic access restrictions if context synchronisation is lost beyond a defined threshold. The remediation is to implement dedicated monitoring with alerting on integration health, configure the ZTNA broker to require periodic posture re-validation (not just initial authentication), and define a default-deny policy that activates if the NAC context feed is unavailable for more than a specified interval.