Bar and Pub WiFi: A Complete Setup and Marketing Guide
This comprehensive technical guide details the architecture, deployment, and monetisation of enterprise-grade guest WiFi for bars and pubs. It provides actionable blueprints for IT leaders to implement secure, high-performance networks that drive compliance, capture first-party customer data, and power targeted marketing campaigns to increase ROI.
🎧 Listen to this Guide
View Transcript
- Executive Summary
- Technical Deep-Dive
- Network Architecture and Hardware Selection
- Network Segmentation and Security
- Implementation Guide
- Step 1: Site Survey and Capacity Planning
- Step 2: Hardware Procurement and Installation
- Step 3: Network Configuration and Segmentation
- Step 4: Captive Portal and Authentication Setup
- Step 5: Analytics and CRM Integration
- Best Practices
- Troubleshooting & Risk Mitigation
- ROI & Business Impact

Executive Summary
Deploying robust bar WiFi and pub WiFi is no longer simply an operational overhead; it is a foundational requirement for driving footfall, increasing customer retention, and unlocking new revenue streams. For IT managers, CTOs, and venue operations directors across the hospitality sector, the challenge lies in transitioning from legacy, unmanaged internet connections to enterprise-grade, secure, and data-rich networks. This guide provides a comprehensive blueprint for architecting, deploying, and monetising guest WiFi for restaurants, bars, and pubs.
By integrating a sophisticated captive portal with robust analytics, venues can seamlessly collect first-party customer data while remaining fully compliant with GDPR and PCI DSS standards. This infrastructure not only ensures a high-performance connectivity experience for patrons but also powers targeted marketing campaigns that turn casual visitors into loyal advocates. Whether you are managing a single premium location or a sprawling estate, implementing these vendor-neutral best practices will transform your WiFi from a cost centre into a measurable driver of ROI.
Technical Deep-Dive
Network Architecture and Hardware Selection
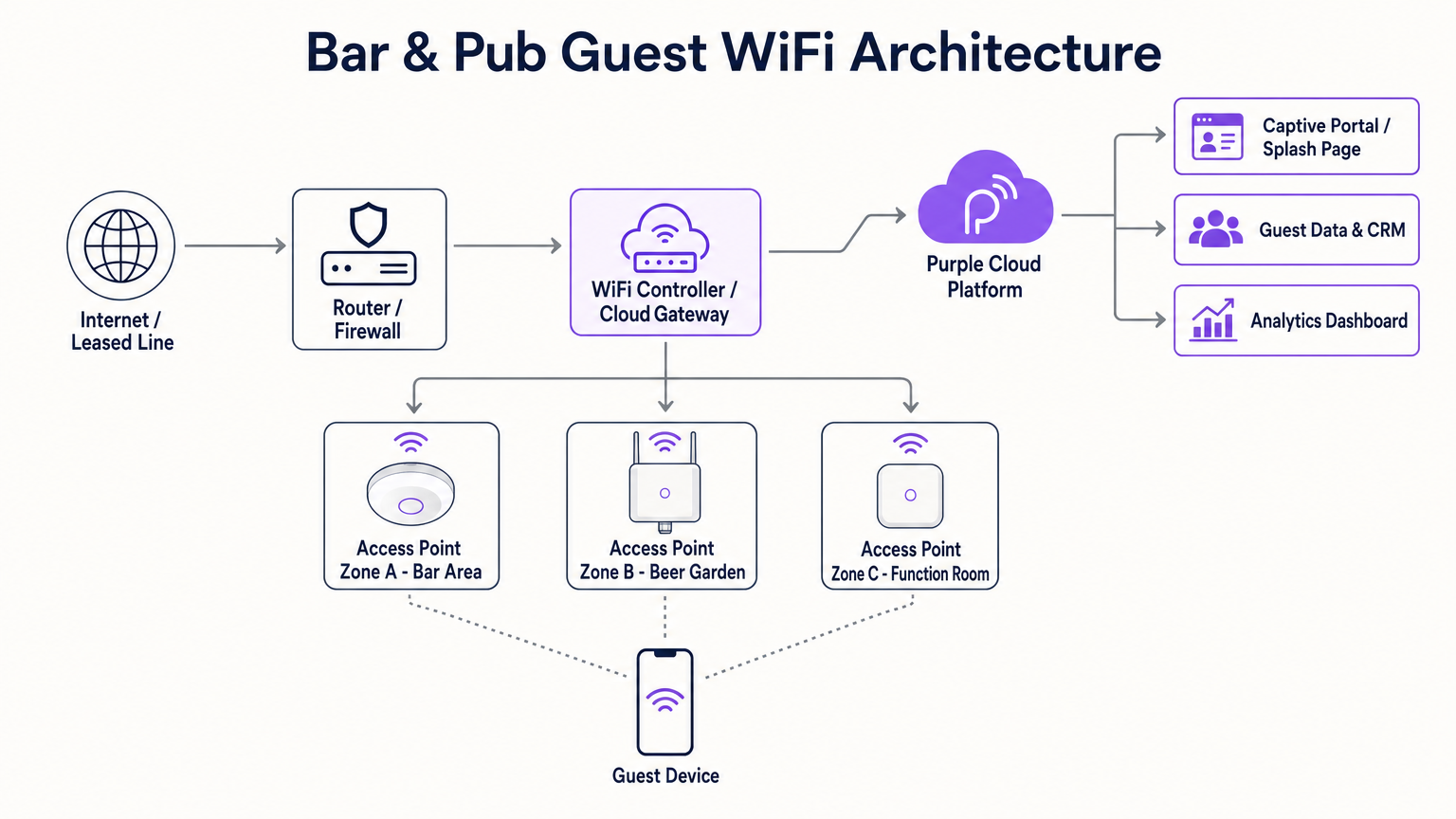
The foundation of any high-performing hospitality WiFi deployment is a resilient and scalable network architecture. Consumer-grade routers are entirely insufficient for the density and throughput demands of a modern bar or pub. Instead, venues require enterprise-grade access points (APs) managed via a centralised wireless LAN controller or cloud-based gateway. This enables seamless roaming, unified policy enforcement, and proactive monitoring across the entire estate.
When selecting hardware, dual-band APs supporting 802.11ac (Wi-Fi 5) or, preferably, 802.11ax (Wi-Fi 6) are essential. Wi-Fi 6 offers significant advantages in high-density environments, utilizing Orthogonal Frequency-Division Multiple Access (OFDMA) and Multi-User Multiple Input Multiple Output (MU-MIMO) to efficiently handle concurrent connections. For coverage planning, a general rule of thumb is one AP per 1,500 to 2,000 square feet of indoor space, though this must be validated through a professional predictive and active site survey to account for attenuation from brick walls, metal fixtures, and high patron density.
Outdoor areas, such as beer gardens and terraces, require specialised IP67-rated APs to withstand environmental factors. Furthermore, backhaul connectivity is critical. While a standard FTTC connection may suffice for a small pub, larger venues or those heavily reliant on cloud-based Point of Sale (POS) systems should invest in a dedicated leased line. As detailed in our guide on What Is a Leased Line? Dedicated Business Internet , this provides a symmetrical, uncontended connection, ensuring that guest traffic does not bottleneck critical business operations.
Network Segmentation and Security
Security and compliance are paramount. The guest WiFi network must be strictly segregated from the corporate network, particularly the POS and payment processing infrastructure. This is typically achieved through Virtual Local Area Networks (VLANs) and robust firewall rules. Failing to segment the network constitutes a severe breach of PCI DSS compliance, exposing the venue to significant financial and reputational risk.
Furthermore, the implementation of a captive portal is not merely a marketing tool; it is a critical security control. The portal authenticates users and enforces the acceptance of an Acceptable Use Policy (AUP), mitigating the venue's liability for illegal activities conducted over the network. Content filtering at the DNS or firewall level should also be implemented to block malicious domains and inappropriate content, ensuring a safe browsing environment.
Implementation Guide
Step 1: Site Survey and Capacity Planning
Before procuring hardware, conduct a comprehensive site survey. Identify high-density zones (e.g., the main bar, function rooms) and potential sources of interference. Calculate the expected concurrent device count, factoring in that most patrons carry at least one, and often two, connected devices. This data will dictate the required AP density, switch PoE budget, and internet backhaul capacity.
Step 2: Hardware Procurement and Installation
Select enterprise-grade networking equipment from reputable vendors. Ensure that switches provide sufficient Power over Ethernet (PoE+) to drive all APs. When mounting APs, ceiling placement is generally optimal for unobstructed propagation. Ensure that cabling runs are properly certified and that outdoor APs are correctly grounded and weather-sealed.
Step 3: Network Configuration and Segmentation
Configure the core router and switches to establish isolated VLANs for corporate traffic, POS systems, IoT devices (e.g., smart lighting, HVAC), and guest WiFi. Implement bandwidth shaping and Quality of Service (QoS) policies on the guest VLAN to prevent individual users from monopolising the connection, guaranteeing a baseline level of service for all patrons. For more insights on bandwidth planning, refer to our comprehensive guide: Hotel WiFi Speed: What Guests Expect and How to Deliver It . (German speakers can also review Hotel WiFi-Geschwindigkeit: Was Gäste erwarten und wie man es liefert ).
Step 4: Captive Portal and Authentication Setup
Integrate a robust captive portal solution, such as Purple's Guest WiFi platform. Design the splash page to align with the venue's branding, keeping the authentication process as frictionless as possible. Common authentication methods include email registration, SMS verification, or social login. Crucially, ensure that the data capture process includes explicit, granular opt-in checkboxes for marketing communications, accompanied by a clear link to the privacy policy to maintain GDPR compliance.
Step 5: Analytics and CRM Integration
Connect the WiFi platform to your existing CRM or email marketing software. This allows the seamless transfer of captured profile data and behavioural metrics (e.g., visit frequency, dwell time). Configure automated workflows, such as sending a welcome email to first-time visitors or a re-engagement offer to patrons who have not visited in the past 30 days.
Best Practices
- Prioritise Frictionless Onboarding: The captive portal should be intuitive and mobile-optimised. Avoid demanding excessive personal information upfront; an email address or phone number is sufficient for initial profiling.
- Leverage Profile-Based Authentication: As discussed in our analysis of the future of seamless secure WiFi, profile-based authentication (such as OpenRoaming) allows returning guests to connect automatically without re-authenticating, significantly enhancing the user experience while continuing to log valuable analytics data. Purple acts as a free identity provider for services like OpenRoaming under the Connect license.
- Ensure GDPR Compliance by Design: Never use pre-ticked boxes for marketing consent. Clearly separate the terms of service acceptance from marketing opt-ins.
- Monitor and Optimize Continuously: Regularly review the WiFi Analytics dashboard to identify coverage dead spots, monitor peak usage times, and assess the conversion rates of your marketing campaigns.

Troubleshooting & Risk Mitigation
Even the most meticulously designed networks encounter issues. Here are common failure modes and mitigation strategies:
- Failure Mode: DHCP Exhaustion. In high-turnover environments like busy pubs, the DHCP server may run out of IP addresses to assign, preventing new devices from connecting.
- Mitigation: Reduce the DHCP lease time on the guest VLAN to 1 or 2 hours, ensuring that IP addresses are quickly returned to the pool when patrons leave. Expand the DHCP subnet scope (e.g., from a /24 to a /22 or /21) to accommodate more concurrent devices.
- Failure Mode: Co-Channel Interference. If multiple APs operate on the same frequency channel, their signals interfere, severely degrading throughput.
- Mitigation: Implement dynamic channel assignment via the wireless controller. Ensure that 2.4 GHz radios only use non-overlapping channels (1, 6, and 11) and minimize the use of wide channels (e.g., 40 MHz or 80 MHz) in dense deployments unless operating exclusively in the 5 GHz or 6 GHz bands.
- Failure Mode: Captive Portal Bypass Issues. Modern mobile operating systems employ MAC randomization and strict security checks that can sometimes interfere with captive portal redirection.
- Mitigation: Ensure the network utilizes a trusted SSL certificate for the captive portal. Whitelist essential domains (e.g., Apple and Google captive portal detection URLs) in the firewall's "walled garden" configuration to ensure the OS can reliably trigger the login prompt.
ROI & Business Impact
The true value of bar wifi lies in its ability to generate actionable business intelligence. By transforming anonymous foot traffic into a structured customer database, venues can execute highly targeted marketing initiatives.
Consider a scenario where analytics reveal a significant drop in footfall on Tuesday evenings. Utilizing the data captured via the guest WiFi, the marketing team can segment the database to identify patrons who frequently visit on weekends but rarely on weekdays. An automated, personalized email campaign offering a Tuesday-only promotion can be dispatched to this specific cohort. This targeted approach yields vastly superior conversion rates compared to generic broadcast marketing.
The ROI is measured not just in the volume of data collected, but in the incremental revenue generated by these targeted campaigns, the reduction in customer churn, and the enhanced operational efficiency gained through insights into peak trading hours and dwell times. This data-driven approach is increasingly critical across all sectors, from Hospitality and Retail to Healthcare and Transport . Furthermore, as the industry evolves, leaders are recognizing the broader impact of connected infrastructure, a trend highlighted by developments such as Purple Signals Higher Education Ambitions with Appointment of VP Education Tim Peers and the growing importance of seamless connectivity in mobile environments, as detailed in Wi Fi in Auto: The Complete 2026 Enterprise Guide .
Key Terms & Definitions
Captive Portal
A web page that a user of a public-access network is obliged to view and interact with before access is granted.
Crucial for authenticating users, presenting Acceptable Use Policies, and capturing first-party data for marketing.
VLAN (Virtual Local Area Network)
A logical subnetwork that groups a collection of devices from different physical LANs.
Used to isolate guest WiFi traffic from sensitive corporate and POS traffic, ensuring security and compliance.
Leased Line
A dedicated, fixed-bandwidth, symmetric data connection connecting a business directly to the internet.
Necessary for high-capacity venues to ensure consistent throughput that isn't shared with neighboring premises.
Wi-Fi 6 (802.11ax)
The latest generation of the Wi-Fi standard, designed to improve efficiency and performance in dense environments.
Essential for venues with high concurrent device counts, utilizing technologies like OFDMA to handle multiple users simultaneously.
DHCP Exhaustion
A state where the DHCP server has allocated all available IP addresses in its pool, preventing new devices from connecting.
A common issue in high-turnover hospitality environments; mitigated by reducing DHCP lease times and expanding subnet sizes.
PCI DSS (Payment Card Industry Data Security Standard)
An information security standard for organizations that handle branded credit cards.
Mandates strict network segmentation to ensure guest WiFi users cannot access payment processing infrastructure.
Profile-Based Authentication
A method where returning users are automatically authenticated based on their device profile without needing to interact with the captive portal again.
Improves user experience and encourages seamless connectivity, facilitating ongoing analytics tracking.
Co-Channel Interference
Performance degradation caused when multiple access points operate on the same frequency channel, causing them to compete for airtime.
Addressed through careful RF planning, dynamic channel assignment, and utilizing non-overlapping channels.
Case Studies
A busy city-centre pub with a capacity of 300 patrons and a large outdoor beer garden is experiencing severe WiFi performance degradation on Friday nights. The current setup consists of two consumer-grade ISP routers. The venue wants to upgrade the network to ensure reliable connectivity and begin capturing customer data for marketing.
- Replace the consumer routers with a dedicated enterprise firewall/router and a PoE+ managed switch. 2. Provision a dedicated leased line (e.g., 100Mbps symmetrical) to handle the backhaul traffic. 3. Deploy three indoor Wi-Fi 6 access points (ceiling-mounted) in the main bar area and two IP67-rated outdoor APs in the beer garden. 4. Configure the switch to create isolated VLANs for the corporate network, POS terminals, and guest WiFi. 5. Integrate the Purple Guest WiFi platform, configuring a branded captive portal with email authentication and explicit GDPR-compliant marketing opt-ins. 6. Reduce the DHCP lease time on the guest VLAN to 2 hours to prevent IP exhaustion.
A regional chain of 15 sports bars wants to standardize their guest WiFi to build a centralized CRM database. Currently, each venue manages its own standalone network with varying SSIDs and no data capture mechanisms.
- Standardize the hardware stack across all venues using cloud-managed APs and switches from a single vendor. 2. Deploy a centralized cloud controller to manage configurations and firmware updates across the entire estate. 3. Implement a unified SSID (e.g., 'Free_SportsBar_WiFi') across all 15 locations. 4. Deploy the Purple analytics platform centrally, configuring a consistent captive portal experience. 5. Enable profile-based authentication so a guest registering at Venue A automatically connects when visiting Venue B. 6. Integrate the centralized WiFi database via API with the chain's primary CRM system to trigger automated loyalty campaigns.
Scenario Analysis
Q1. A historic pub with thick stone walls is planning a WiFi upgrade. The manager wants to place a single high-powered AP in the centre of the venue to save on cabling costs. As the IT architect, what is your recommendation?
💡 Hint:Consider how building materials affect RF propagation and the limitations of client device transmit power.
Show Recommended Approach
Advise against a single AP deployment. Thick stone walls severely attenuate RF signals, particularly in the 5 GHz band. Even if a high-powered AP can transmit a signal to the edges of the venue, mobile devices (which have weak transmitters) will struggle to send data back, resulting in a poor user experience. Recommend a professional site survey and a multi-AP deployment using lower transmit power to ensure adequate coverage and capacity throughout the venue.
Q2. During an audit, you discover that the guest WiFi network is operating on the same VLAN as the venue's cloud-based EPOS system. The venue owner argues that because the EPOS is cloud-based, local segmentation is unnecessary. How do you respond?
💡 Hint:Focus on compliance standards and the risks of lateral movement within a flat network.
Show Recommended Approach
Explain that this configuration is a critical security vulnerability and a direct violation of PCI DSS compliance. Even if the EPOS communicates with the cloud, placing guest devices on the same local subnet allows malicious actors to attempt lateral movement, sniff local traffic, or launch attacks against the EPOS hardware. Immediate remediation is required to implement VLAN segregation and strict firewall rules isolating the guest network.
Q3. A venue's marketing team complains that they are capturing thousands of email addresses via the captive portal, but their email marketing campaigns have an extremely high bounce rate and low engagement. What technical or configuration issue might be causing this?
💡 Hint:Consider the user experience during onboarding and how users might bypass data entry requirements.
Show Recommended Approach
The high bounce rate is likely due to users entering fake or disposable email addresses to bypass the captive portal quickly. To mitigate this, implement email verification (requiring the user to click a link in an email to gain full internet access) or SMS authentication. Additionally, review the captive portal design to ensure it is not overly demanding, which incentivizes users to provide false information.



