How to Collect Customer Data In-Store: A Retailer's Guide
This technical reference guide equips IT managers, network architects, and venue operations directors with a practical framework for building first-party customer datasets in physical retail locations. It covers the deployment architecture, compliance obligations, and integration strategies for Guest WiFi, POS systems, loyalty programmes, and survey kiosks. The guide maps each collection method to measurable business outcomes, with concrete implementation scenarios from retail, hospitality, and events environments.
🎧 Listen to this Guide
View Transcript
- Executive Summary
- Technical Deep-Dive
- The In-Store Data Collection Ecosystem
- Network Architecture and Security Standards
- MAC Address Randomisation: The Critical Technical Challenge
- Implementation Guide
- Phase 1: Infrastructure Assessment and Data Mapping
- Phase 2: Captive Portal Configuration and Optimisation
- Phase 3: Integration and Workflow Automation
- Best Practices
- Troubleshooting and Risk Mitigation
- ROI and Business Impact

Executive Summary
For modern retailers and venue operators, the physical store represents the largest untapped source of first-party customer data. While e-commerce platforms natively capture every click, dwell time, and conversion event, brick-and-mortar locations frequently operate with critical visibility gaps — knowing what was sold at the till, but not who bought it, how long they stayed, or whether they will return. This guide provides the technical architecture and deployment strategies required to capture, secure, and activate in-store customer data at scale.
IT managers and network architects must balance seamless user experiences with stringent compliance requirements under GDPR and PCI DSS, alongside robust network security standards including WPA3 and IEEE 802.1X. By deploying integrated solutions across Guest WiFi , Point of Sale systems, and loyalty programmes, organisations can transform anonymous footfall into actionable intelligence. This reference provides a vendor-neutral framework for deploying these technologies, with specific integration points for Purple's WiFi Analytics platform.
Technical Deep-Dive
The In-Store Data Collection Ecosystem
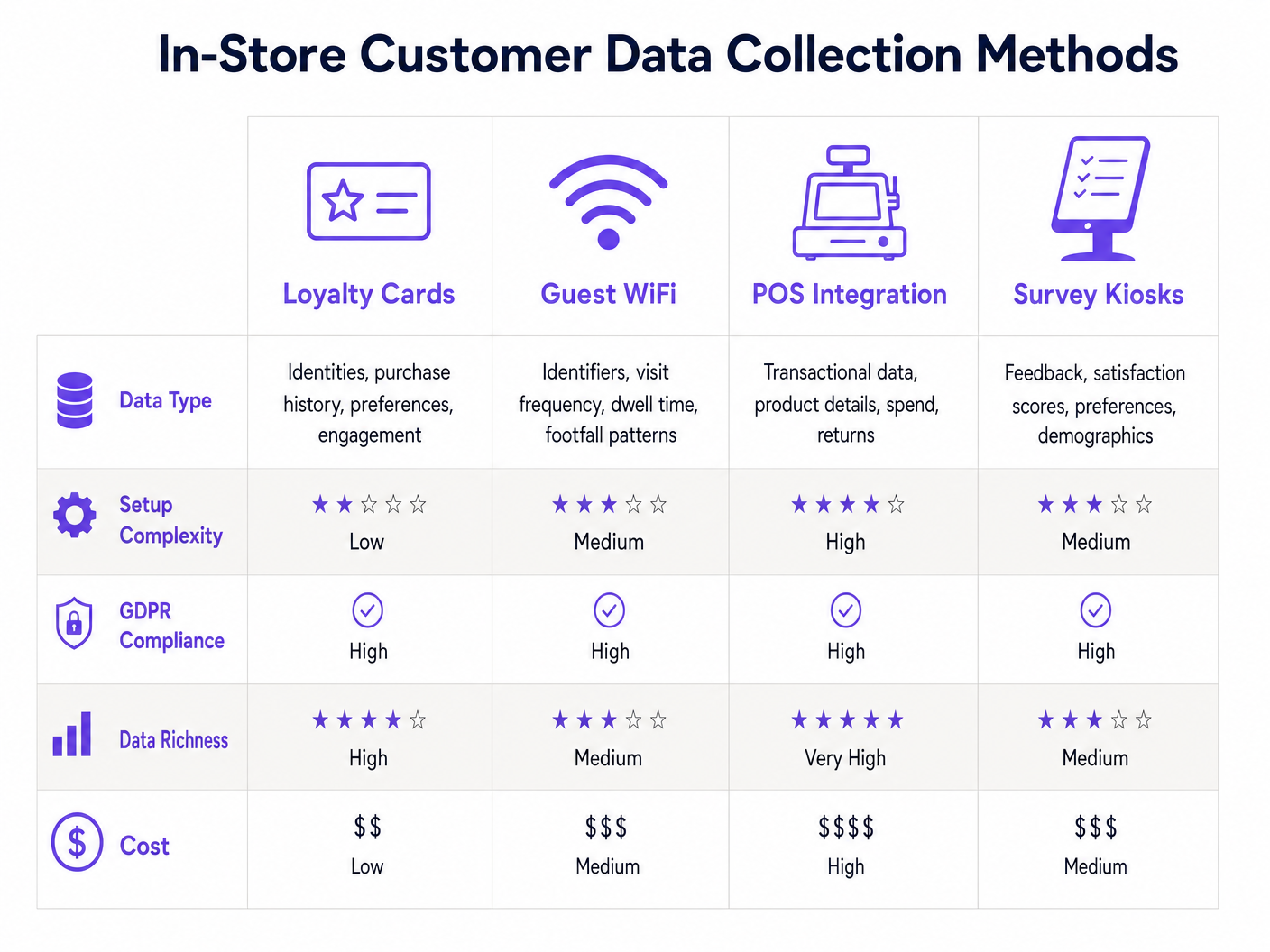
Building a comprehensive first-party dataset in a physical location requires a multi-layered approach. No single collection method provides a complete picture; the strongest implementations combine complementary vectors that capture different dimensions of the customer relationship.
The ecosystem comprises four primary collection vectors. First, Guest WiFi Authentication captures verified user identities — email addresses, phone numbers, and social profiles — along with device identifiers when users connect to the venue network. Second, Location and Presence Analytics uses WiFi access points and Bluetooth Low Energy (BLE) beacons to track device movement, dwell times, and footfall heatmaps, even for users who do not authenticate. Third, POS and Loyalty Integration links transactional data — basket size, SKU-level purchases, return behaviour — to customer identities via loyalty cards, digital wallets, or e-receipts. Fourth, Interactive Kiosks and Surveys capture explicit zero-party data regarding customer satisfaction, preferences, and demographics at the point of experience.
For a broader perspective on how these technologies intersect with connected venue infrastructure, see our Internet of Things Architecture: A Complete Guide .
Network Architecture and Security Standards
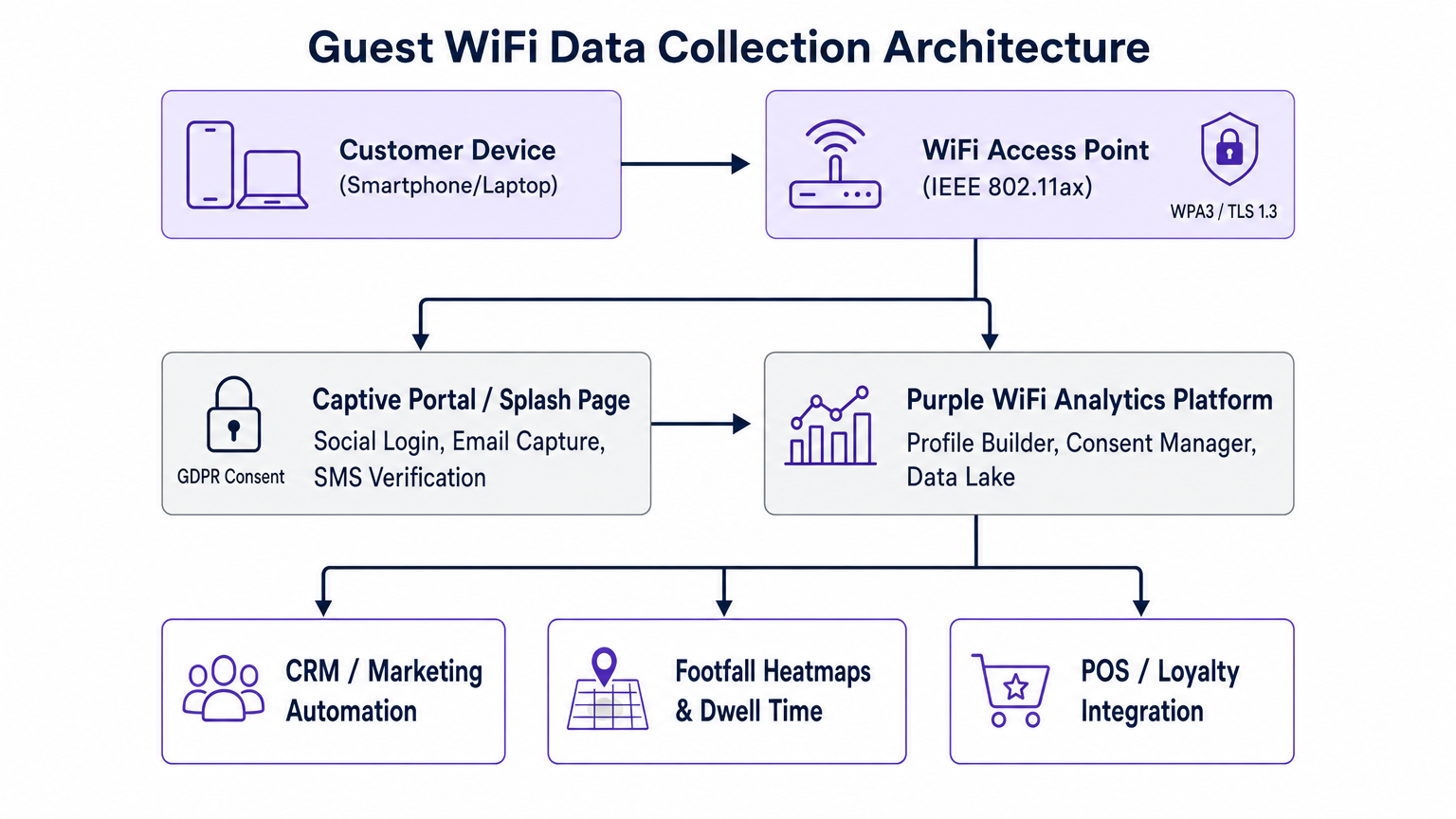
Deploying enterprise-grade data collection requires a robust and well-segmented network architecture. A standard deployment in Retail or Hospitality environments mandates strict separation of corporate and guest traffic using distinct VLANs at both the switch and access point level. This is a non-negotiable security baseline — guest devices must never have layer-2 visibility of POS terminals, back-office servers, or payment infrastructure.
Access Point Standards: Modern deployments should target IEEE 802.11ax (Wi-Fi 6) access points for high client density environments. Wi-Fi 6 introduces OFDMA and BSS Colouring, which significantly improve performance in dense environments such as retail floors, stadium concourses, and conference centres. For venues with outdoor coverage requirements, Wi-Fi 6E extends into the 6 GHz band, reducing interference from legacy devices.
Authentication Protocols: Captive portal deployments use RADIUS (Remote Authentication Dial-In User Service) to manage guest session authorisation. When a user attempts to connect, the access point redirects HTTP traffic to a captive portal hosted in the cloud. Upon successful authentication via OAuth (Social Login) or standard form submission, the RADIUS server authorises the device's MAC address for a defined session duration and logs the event to the analytics platform. WPA3-SAE should be enforced on the guest SSID where device compatibility permits, with WPA2-PSK as a fallback for legacy devices.
Data Privacy and Compliance: Collecting customer data introduces significant obligations under GDPR (for UK and EU deployments) and equivalent frameworks. Implementations must include explicit opt-in mechanisms for marketing communications, clearly separated from the network access consent. Data minimisation principles apply — collect only what is necessary for the stated purpose. Retention policies must be automated, with records purged after a defined period of inactivity. For a comprehensive treatment of the compliance architecture, see our guide on How to Protect Customer Data Collected via WiFi .
MAC Address Randomisation: The Critical Technical Challenge
Every network architect deploying presence analytics must account for MAC address randomisation. Apple introduced per-network MAC randomisation by default in iOS 14 (2020), with Android following in Android 10. In practice, this means the hardware MAC address of a customer's device changes periodically, making it an unreliable long-term identifier for unauthenticated users.
The architectural response is to design the system to prioritise authenticated sessions. For unauthenticated presence analytics, focus on aggregate metrics — total device count, average dwell time, heatmap patterns — rather than individual device tracking. For cross-visit attribution and individual customer journeys, the customer must be incentivised to authenticate. This is why the value exchange is a technical requirement, not merely a marketing consideration.
Implementation Guide
Deploying a comprehensive in-store data collection strategy requires coordinated effort across IT, marketing, and operations teams. The following three-phase framework provides a structured deployment path.
Phase 1: Infrastructure Assessment and Data Mapping
Before deploying any data collection tooling, conduct a thorough audit of the existing network infrastructure. Verify that access points support the required client density and modern security standards. Confirm that VLAN segmentation is correctly configured at the switch level and enforced at the access point. Assess firewall rules to ensure captive portal redirect traffic is permitted while guest devices are blocked from internal network segments.
Concurrently, complete a data mapping exercise. Document every data element you intend to collect, the legal basis for processing it, where it will be stored, how long it will be retained, and which downstream systems will receive it. This document forms the foundation of your GDPR Record of Processing Activities (RoPA) and is a prerequisite for any compliant deployment.
Phase 2: Captive Portal Configuration and Optimisation
The captive portal — the branded splash page presented to connecting users — is the primary user interface for your data collection strategy. Its design directly determines the volume and quality of data captured.
The most common deployment error is requesting too many data fields on the initial login screen. Presenting a form with five or more fields will result in significant abandonment, reducing overall network adoption and data capture rates. The recommended approach is progressive profiling: ask for a name and email address (or offer one-click social login) on the first visit. On subsequent visits, the system recognises the returning user and prompts for one additional data point — a date of birth, a postcode, or a product preference. Over multiple visits, a rich customer profile is built without ever presenting a daunting form.
Authentication method selection also matters. Social login via Google or Apple ID consistently delivers the highest conversion rates because it eliminates the need to remember a password and pre-populates verified data. Email-based login provides a directly actionable marketing identifier. SMS verification provides a phone number for SMS marketing but introduces additional friction.
Phase 3: Integration and Workflow Automation
Data collected in-store has limited commercial value if it remains in a silo. The WiFi analytics platform must be integrated with the CRM, marketing automation tools, and the central data lake. Purple's platform provides pre-built integrations with Salesforce, HubSpot, Microsoft Dynamics, and Mailchimp, along with a REST API and webhook framework for custom integrations.
Configure event-driven workflows to activate data in real time. A first-time visitor should trigger a welcome email within minutes of connecting. A customer who has not visited for 60 days should enter a re-engagement campaign. A customer who connects to the WiFi within 24 hours of receiving a promotional email provides a confirmed store visit attribution event — closing the loop on digital marketing spend.
Best Practices
Enforce the Value Exchange: Customers will only provide first-party data if the perceived value of the reward exceeds the perceived privacy cost. High-speed WiFi access, exclusive in-store discounts, and loyalty points are all effective incentives. Make the value proposition explicit on the splash page — do not assume users understand the exchange.
Segment by Venue Type: Data collection strategies must be calibrated to the venue context. A Transport hub like a train station requires a frictionless, high-throughput authentication flow to handle peak footfall. A hotel or Hospitality venue can afford a more detailed onboarding flow because guests have more time and a longer relationship with the property.
Implement Bandwidth Governance: Per-user bandwidth limits and session time caps must be enforced via RADIUS attributes to prevent network abuse. Guest bandwidth consumption must never be allowed to degrade the performance of POS terminals, payment processing systems, or back-office applications.
Audit Consent Records Regularly: Consent records must be auditable. For any given customer record, you must be able to demonstrate when consent was obtained, through which channel, and for which specific processing activities. Automated consent expiry and re-consent workflows should be configured for records older than 24 months.
Troubleshooting and Risk Mitigation
Low Authentication Rates: If users are connecting to the SSID but abandoning the captive portal, the most likely causes are excessive form fields, slow portal load times, or an unclear value proposition. Audit the splash page load time (target under two seconds on a 3G connection), reduce the required fields to a minimum, and A/B test the headline copy. Social login options should always be presented as the primary call to action.
Data Silos and Fragmented Customer Records: If in-store WiFi data is not integrated with e-commerce profiles and POS records, the customer view remains fragmented and commercially unusable. Prioritise the implementation of a common customer identifier — typically the email address — that is normalised and deduplicated across all systems. A Customer Data Platform (CDP) can serve as the unifying layer.
Compliance Drift: GDPR compliance is not a one-time configuration. Conduct quarterly audits of data retention policies, consent records, and data subject access request (DSAR) workflows. Ensure that Right to be Forgotten requests are propagated across all integrated systems — the WiFi platform, the CRM, the marketing automation tool, and the data lake — not just the primary collection point.
Network Performance Degradation: If guest WiFi traffic is impacting POS system performance, review the VLAN configuration and QoS policies. POS traffic should be assigned the highest priority queue. Guest traffic should be rate-limited at the per-user level via RADIUS attributes.
ROI and Business Impact
Implementing a robust in-store data collection strategy delivers measurable returns across three primary dimensions.
Customer Lifetime Value: By understanding in-store behaviour and linking it to purchase history, retailers can deliver personalised marketing campaigns that drive repeat visits and higher average order values. Venues operating Purple's platform report average email open rates of 35-40% for WiFi-captured audiences, compared to industry averages of 20-25% for purchased lists, reflecting the higher quality and consent status of first-party data.
Operational Efficiency: Footfall heatmaps and dwell time analytics allow venue operators to make evidence-based decisions about staff scheduling, store layout, and product placement. A retailer that identifies a high-dwell, low-conversion zone in their store can test layout changes and measure the impact in real time — a capability that was previously only available to e-commerce teams.
Marketing Attribution: By tracking when a customer receives a promotional email and subsequently connects to the in-store WiFi, retailers can close the attribution loop on digital marketing spend for physical store visits. This is a significant capability gap for most retail organisations today, and one that a well-integrated WiFi analytics deployment can address directly.
For organisations operating across multiple venue types, the Retail and Hospitality industry pages on Purple's platform provide sector-specific deployment guidance and benchmarking data.
Key Terms & Definitions
Captive Portal
A web page that a user of a public-access network is required to view and interact with before network access is granted. It serves as the primary interface for capturing customer identity and consent.
The captive portal is the most important UX touchpoint in a Guest WiFi data collection deployment. Its design directly determines authentication conversion rates and data quality.
MAC Address Randomisation
A privacy feature in modern operating systems (iOS 14+, Android 10+) that periodically changes the device's hardware MAC address to prevent passive cross-venue tracking.
Forces IT architects to design data collection systems that rely on authenticated user sessions rather than hardware device identifiers for long-term customer identification and cross-visit attribution.
First-Party Data
Information a company collects directly from its own customers through direct interactions, which the company owns and controls.
The primary commercial asset generated by in-store data collection. Increasingly critical as third-party cookies are deprecated and data brokers face regulatory pressure.
Zero-Party Data
Data that a customer intentionally and proactively shares with a brand, such as preferences, survey responses, and declared interests.
Collected via in-store survey kiosks or questions embedded in the captive portal flow. Highly valuable because it is explicit, consensual, and directly actionable for personalisation.
Dwell Time
The length of time a visitor's device remains detectable within a defined zone of a store or venue, used as a proxy for engagement with that area.
A key operational metric for retail layout optimisation, staff scheduling, and measuring the effectiveness of in-store displays and promotions.
Presence Analytics
The use of WiFi probe request detection or BLE beacon signals to measure the count, location, and movement of devices within a physical space, without requiring user authentication.
Provides aggregate footfall and heatmap data for operational decision-making. Subject to accuracy limitations due to MAC randomisation in modern devices.
RADIUS (Remote Authentication Dial-In User Service)
A networking protocol that provides centralised Authentication, Authorisation, and Accounting (AAA) management for users connecting to a network.
The backend protocol used to manage Guest WiFi sessions, enforce bandwidth policies, and log session data. The integration point between the captive portal and the access point infrastructure.
Progressive Profiling
The practice of gradually collecting customer information across multiple interactions rather than requesting all data fields at a single point of contact.
The recommended approach for captive portal design. Reduces initial login friction while enabling the construction of rich customer profiles over time.
VLAN (Virtual Local Area Network)
A logical segmentation of a physical network that isolates traffic between different groups of devices, even when they share the same physical infrastructure.
Essential for separating Guest WiFi traffic from corporate systems, POS terminals, and payment infrastructure. A baseline security requirement for any venue deploying public WiFi.
WPA3-SAE (Simultaneous Authentication of Equals)
The current generation of WiFi security protocol, replacing WPA2-PSK. Provides stronger encryption and resistance to offline dictionary attacks.
Should be enforced on Guest SSIDs where device compatibility permits. Protects customer data in transit between the device and the access point.
Case Studies
A national fashion retail chain with 50 locations wants to understand the conversion rate of window shoppers to actual store visitors, and then correlate that with in-store purchase behaviour. They currently only track POS transactions and have no visibility of footfall.
Deploy presence analytics using the existing enterprise WiFi access points across all 50 locations. Configure the access points to detect unauthenticated device probe requests and define a geofence at each storefront entrance. By comparing the count of devices detected in the storefront zone (passerby traffic) against devices that enter the store and dwell for more than two minutes (engaged traffic), the platform calculates a capture rate per location. Simultaneously, deploy a captive portal to authenticate connecting users, linking their WiFi profile to POS transaction records via a shared email identifier. After 90 days of data collection, the retailer can segment stores by capture rate, identify underperforming locations, and correlate WiFi dwell time with average basket size.
A large conference centre hosting 5,000-delegate events needs to collect verified attendee data for sponsors, but faces severe network congestion during peak registration periods and has GDPR obligations to manage consent on behalf of multiple event organisers.
Implement a tiered bandwidth model via the captive portal. Offer a basic, speed-limited tier (5 Mbps per user) in exchange for an email address and event registration confirmation. Offer a premium, high-speed tier (25 Mbps per user) for delegates who complete a detailed demographic survey or authenticate via LinkedIn, providing higher-quality B2B data for sponsors. Use RADIUS attributes to enforce bandwidth policies dynamically per user tier. For GDPR compliance, configure separate consent flows per event organiser, with consent records stored against the event identifier. Implement a data export API that allows each event organiser to retrieve only the records for their specific event, with consent status clearly flagged.
Scenario Analysis
Q1. A retail client wants to track the exact path of individual customers through their store using only WiFi presence analytics, without requiring any login. Their marketing director argues this is technically straightforward. How do you advise them?
💡 Hint:Consider the impact of MAC address randomisation on passive device tracking in modern smartphones.
Show Recommended Approach
Advise the client that tracking the exact path of individual unauthenticated users is highly unreliable on modern devices due to MAC address randomisation, which is enabled by default on iOS 14+ and Android 10+. Passive presence analytics is reliable for aggregate metrics — total footfall, average dwell time, zone-level heatmaps — but not for individual customer journey reconstruction. To track individual journeys, the customer must be incentivised to authenticate to the Guest WiFi. Once authenticated, the session is tied to a verified identity rather than a hardware MAC address, enabling accurate cross-visit tracking. Recommend designing a compelling value exchange on the captive portal to maximise authentication rates.
Q2. The marketing team wants to ask for Name, Email, Phone Number, Date of Birth, and Postcode on the initial WiFi login screen to build comprehensive customer profiles from day one. What is your architectural recommendation?
💡 Hint:Balance data richness with user friction and authentication conversion rates.
Show Recommended Approach
Recommend implementing Progressive Profiling. Presenting five required fields on the initial connection will result in high abandonment rates, reducing overall network adoption and data capture volume. The net result is fewer profiles, not richer ones. Advise capturing only Name and Email (or offering Social Login as the primary option) on the first visit. On subsequent visits, the captive portal recognises the returning user and prompts for one additional data point — Date of Birth on visit two, Postcode on visit three. This approach builds rich profiles over time while keeping the initial friction minimal. Configure the platform to track profile completeness and trigger re-engagement campaigns when a profile reaches a defined completeness threshold.
Q3. A venue operator is concerned that offering free Guest WiFi will result in bandwidth abuse by a small number of users, degrading the performance of their POS systems, which share the same physical access point infrastructure.
💡 Hint:Focus on network segmentation, Quality of Service policies, and RADIUS-based session management.
Show Recommended Approach
Address this with a two-part solution. First, ensure strict VLAN segmentation: POS systems must be on a dedicated corporate VLAN, completely isolated from the Guest SSID at both the switch and access point level. Guest devices must have no layer-2 visibility of POS terminals. Second, implement per-user bandwidth throttling via RADIUS attributes — a limit of 5-10 Mbps per guest user is sufficient for typical browsing and streaming while preventing any single user from saturating the uplink. Configure QoS policies to assign POS traffic to the highest priority queue, ensuring it is never pre-empted by guest traffic even during peak periods. Additionally, set session time limits (e.g., 4-hour maximum sessions) to prevent devices from holding connections indefinitely.
Q4. Six months after deploying a Guest WiFi data collection system, the data protection officer flags that the organisation has received a Right to be Forgotten request from a customer. The IT team deletes the record from the WiFi platform but the DPO is not satisfied. What has been missed?
💡 Hint:Consider all downstream systems that may have received the customer's data via API integrations or webhooks.
Show Recommended Approach
The Right to be Forgotten obligation under GDPR Article 17 requires deletion of the customer's personal data from all systems in which it is held, not just the primary collection point. The IT team must identify every system that received the customer's data via integration: the CRM, the marketing automation platform, the email marketing tool, the data lake or CDP, and any third-party analytics platforms. Each system must process the deletion request independently. The organisation should have a documented DSAR (Data Subject Access Request) workflow that maps the data flow from the WiFi platform to all downstream systems and provides a checklist for complete deletion. This workflow should be tested quarterly as part of the compliance audit cadence.



