How to Improve Marketing ROI Using WiFi Data
A practical, tactical guide for IT managers and marketers on integrating WiFi analytics into the existing marketing stack. It details how to leverage first-party venue data to reduce CPA, improve ROAS, and drive measurable revenue through closed-loop attribution.
🎧 Listen to this Guide
View Transcript
Executive Summary
For enterprise venues—whether in Retail , Hospitality , Healthcare , or Transport —the physical space is the largest untapped data asset. While digital marketing teams optimize campaigns using cookie data and online tracking, they often lack visibility into real-world customer behavior. This guide details how to bridge that gap by turning your existing network infrastructure into a first-party data engine. By deploying a robust WiFi Analytics solution over your Guest WiFi network, IT teams can provide marketing with the deterministic, consent-compliant data required to reduce Cost Per Acquisition (CPA), increase Return on Ad Spend (ROAS), and implement true closed-loop attribution. This is not about ripping and replacing infrastructure; it is about activating the data your access points are already generating.
Technical Deep-Dive
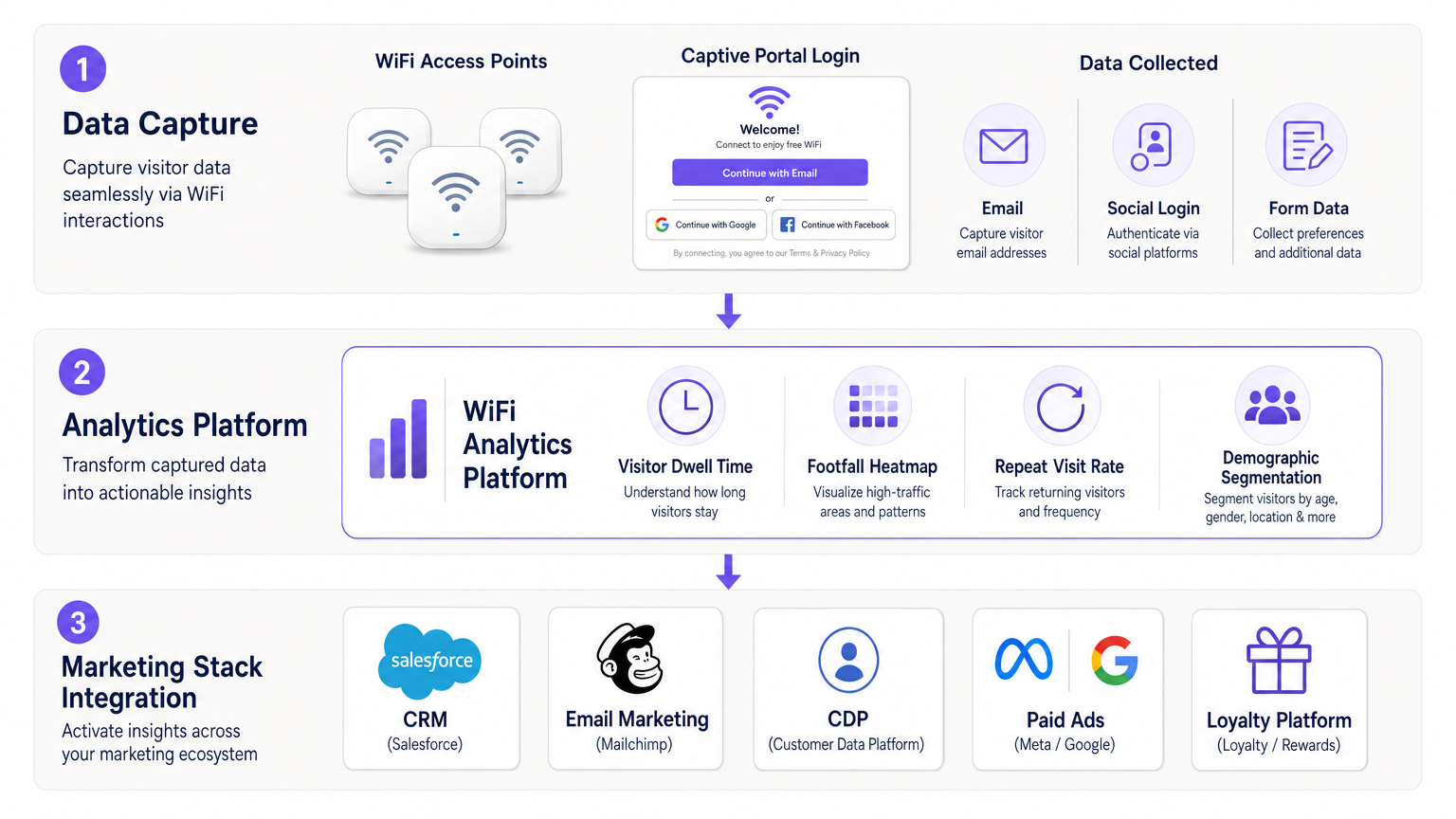
The architecture required to improve marketing ROI using WiFi data relies on three distinct layers: passive capture, active authentication, and data syndication.
1. The Capture Layer
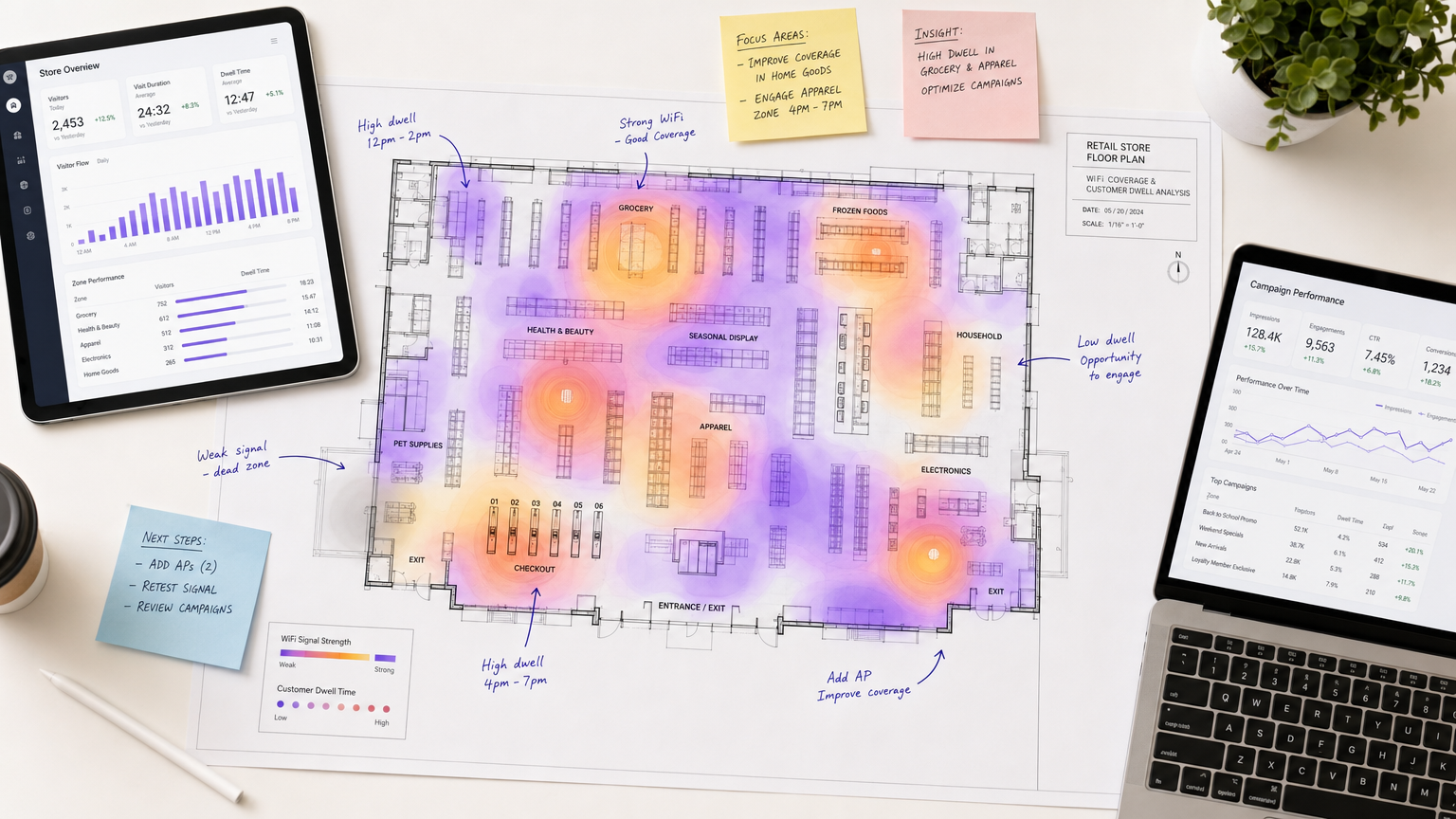
Modern enterprise access points (APs) continuously monitor for 802.11 probe requests. This allows the network to passively track device MAC addresses (often randomized by modern OS implementations, but still useful for session-level analytics), signal strength (RSSI), and timestamp data. This passive data provides baseline metrics: total footfall, zone-level dwell times, and physical journey mapping. For a deeper dive into spatial tracking, refer to our Indoor Positioning System: UWB, BLE, & WiFi Guide .
2. The Authentication Layer
The transition from anonymous footfall to actionable marketing data occurs at the captive portal. When a user authenticates via the Guest WiFi, they provide explicit consent (GDPR/CCPA compliant) alongside identity data—typically an email address, phone number, or social login profile. At this stage, the platform associates the physical MAC address session with a known user identity. This is where profile-based authentication, such as OpenRoaming, becomes a significant advantage, reducing friction for returning visitors.
3. The Syndication Layer
Data residing solely in the WiFi platform has limited ROI. The technical requirement for IT is to build seamless API integrations or webhooks from the WiFi platform into the marketing stack (CRM, CDP, ESP). For instance, when evaluating platforms like Purple vs Cisco Spaces (DNA Spaces): When to Choose Each , a key consideration is how easily the platform syndicates clean, structured data to downstream systems like Salesforce or Mailchimp.
Implementation Guide
Deploying a marketing-centric WiFi architecture requires tight alignment between Network Operations and Marketing. Follow these deployment phases:
Phase 1: Network Optimization for Location Accuracy Ensure your AP density and placement support accurate location analytics. While basic presence analytics require only a few APs, zone-level dwell time requires a higher density deployment and proper calibration of RSSI thresholds. (See Wi Fi in Auto: The Complete 2026 Enterprise Guide for advanced deployment scenarios).
Phase 2: Captive Portal Configuration & Compliance Design the captive portal to maximize data capture without degrading the user experience. Implement real-time email validation APIs to prevent bad data from entering the CRM. Ensure the privacy policy explicitly covers data sharing with third-party ad platforms (Meta, Google) via hashed email matching.
Phase 3: Stack Integration
Do not build point-to-point integrations if avoidable. Route WiFi data (identity + behavioral events like zone_entered or dwell_exceeded) into a central Customer Data Platform (CDP) or data warehouse. The CDP then handles the logic of updating CRM records and triggering email workflows.
Best Practices
- Value Exchange: Offer tangible value for authentication. A 10% discount code delivered immediately upon login drives significantly higher conversion rates than standard free access.
- Real-Time Triggers: The value of WiFi data decays rapidly. Trigger post-visit surveys or personalized offers within 2 hours of a customer leaving the venue.
- Hashed Audiences: For paid media, use SHA-256 hashed emails to build custom audiences in Meta and Google. This allows you to retarget physical visitors without exposing raw PII.
Troubleshooting & Risk Mitigation
Risk: MAC Randomization Modern iOS and Android devices randomize MAC addresses to prevent tracking. Mitigation: Rely on active authentication (captive portal logins) rather than passive MAC tracking for long-term customer identification. Once authenticated, the session is tied to the identity, bypassing the MAC randomization issue.
Risk: CRM Data Pollution
Users entering fake emails (e.g., test@test.com) will degrade your email deliverability score.
Mitigation: Implement inline email verification at the captive portal. Reject invalid domains or syntax errors before the session is granted.
ROI & Business Impact
The ultimate goal is shifting marketing from probabilistic targeting to deterministic targeting. By utilizing WiFi data, venues can build highly specific audience segments (e.g., "Customers who visited the apparel section for >15 minutes but haven't returned in 30 days").
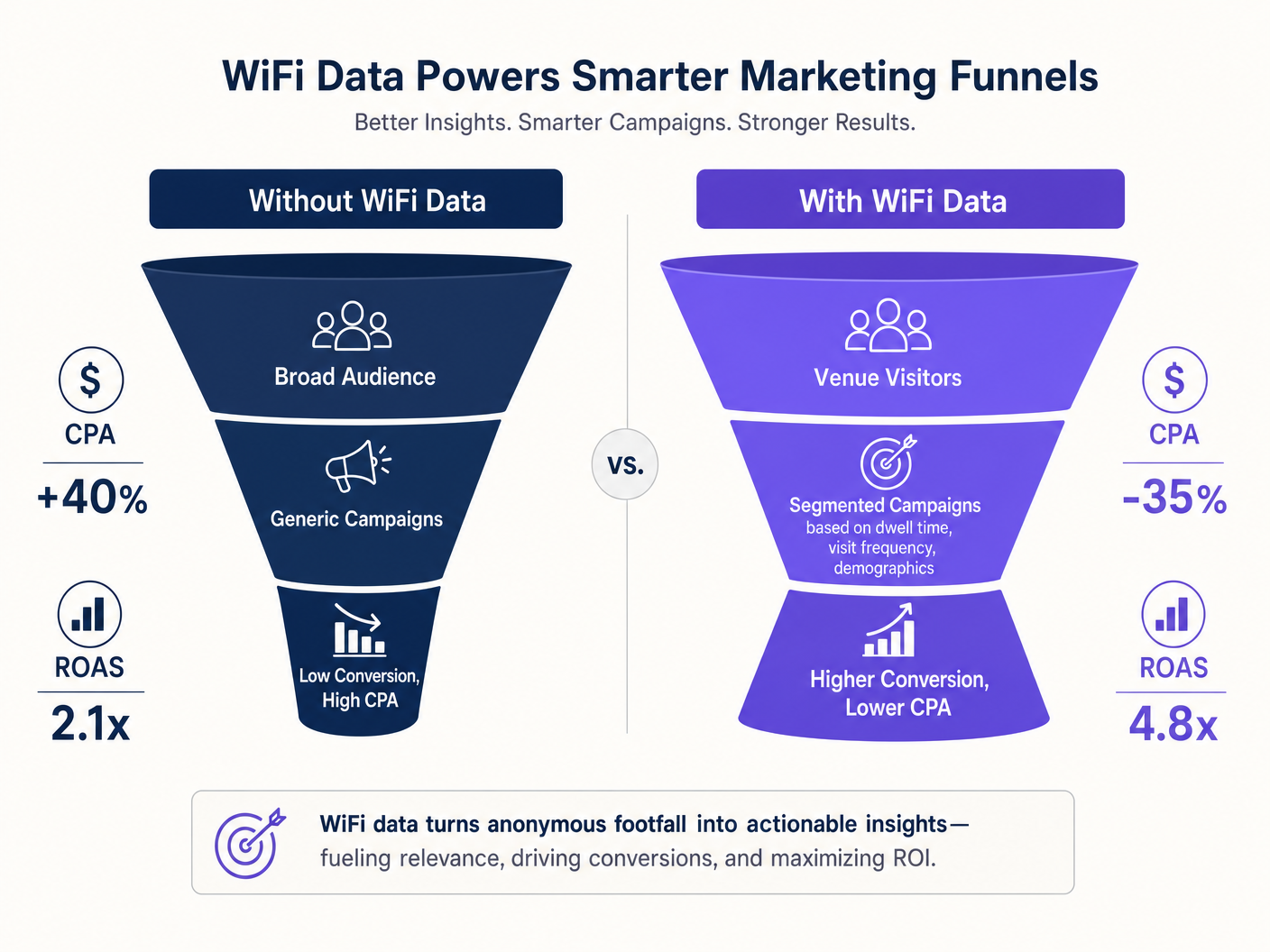
When integrated correctly, we typically observe:
- CPA Reduction: 30-40% lower Cost Per Acquisition on paid social, driven by higher match rates and intent-based targeting.
- ROAS Improvement: 2x to 4x higher Return on Ad Spend for retargeting campaigns.
- Closed-Loop Attribution: The ability to prove that a specific email campaign resulted in a physical venue visit within a 7-day window.
Listen to our deep-dive briefing on this topic:
Key Terms & Definitions
Captive Portal
A web page that users must view and interact with before access is granted to a public WiFi network. It is the primary mechanism for capturing first-party identity data and consent.
IT teams configure this to ensure legal compliance and data capture, while marketing teams design the UX to maximize conversion rates.
MAC Randomization
A privacy feature in modern mobile operating systems that periodically changes the device's MAC address to prevent long-term passive tracking.
This requires venues to rely on active authentication (logins) rather than passive tracking to build long-term customer profiles.
Dwell Time
The duration a connected device remains within the coverage area of a specific access point or zone.
Marketing uses this metric to segment audiences—for example, targeting users with high dwell times in specific retail departments.
Closed-Loop Attribution
A measurement model that tracks a customer's journey from an initial marketing touchpoint (e.g., an email) to a final physical action (e.g., a venue visit).
WiFi data provides the 'physical visit' data point required to close the loop and prove campaign ROI to the business.
First-Party Data
Information a company collects directly from its customers with their consent, rather than purchasing it from data brokers.
Guest WiFi is one of the most scalable methods for brick-and-mortar venues to acquire high-quality first-party data.
Hashed Audience
A list of customer identifiers (usually emails) that have been cryptographically scrambled (e.g., using SHA-256) before being uploaded to an ad platform.
This allows IT to securely share customer lists with Meta or Google for retargeting without exposing raw Personally Identifiable Information (PII).
RSSI (Received Signal Strength Indicator)
A measurement of the power present in a received radio signal. Used to estimate the distance between a device and an access point.
IT uses RSSI thresholds to define physical 'zones' within a venue for location-based marketing triggers.
Data Syndication
The automated process of pushing structured data from one platform (e.g., WiFi Analytics) to downstream systems (e.g., CRM, CDP).
Without syndication, WiFi data remains siloed and cannot generate marketing ROI.
Case Studies
A 200-location retail chain wants to reduce their Facebook Ads CPA. Currently, they target broad demographic lookalike audiences, resulting in a high CPA and low conversion rate. How should the IT and Marketing teams collaborate to solve this using existing network infrastructure?
- IT configures the Guest WiFi captive portal across all 200 locations to require an email address for access, incorporating real-time validation and GDPR-compliant consent for marketing.
- IT sets up an API integration to push authenticated user emails and their associated 'Last Visit Date' to the company's CDP.
- The CDP automatically hashes the emails (SHA-256) and syncs them to Meta Ads Manager as a Custom Audience.
- Marketing runs a targeted 'Welcome Back' campaign specifically to users who visited a physical store in the last 90 days but haven't purchased online.
A large stadium operator needs to increase food and beverage (F&B) revenue during the 45 minutes before kickoff. How can WiFi analytics drive this?
- IT calibrates the APs in the concourse zones to accurately measure dwell time.
- The WiFi Analytics platform is configured with a webhook that triggers when a known (authenticated) user dwells in a specific concourse zone for more than 10 minutes.
- The webhook payload (User ID, Zone ID) is sent to the stadium's marketing automation platform.
- The platform instantly triggers an SMS or push notification to the user with a time-limited 15% discount for the nearest F&B concession stand.
Scenario Analysis
Q1. A hospitality group wants to retarget past guests on Facebook. They export a CSV of emails from the WiFi platform and upload it manually to Meta Ads Manager every month. What are the two primary technical and business risks with this approach?
💡 Hint:Consider data security (PII) and the timeliness of the data.
Show Recommended Approach
- Security/Compliance Risk: Uploading raw, unhashed CSVs of PII manually exposes the data to interception or mishandling, violating best practices and potentially GDPR/CCPA. 2. Business Risk: A monthly manual sync means the data is stale. A guest who visited on day 1 won't be retargeted until day 30, missing the critical post-visit engagement window. The solution is an automated API integration that syncs hashed emails in real-time.
Q2. During a network audit, the IT manager notices that while total connection counts are high, the marketing team is reporting very low CRM match rates. What is the most likely configuration issue at the capture layer?
💡 Hint:Think about what happens between the device connecting to the AP and the data entering the CRM.
Show Recommended Approach
The captive portal is likely lacking real-time validation, allowing users to input fake or malformed email addresses (e.g., ' a@a.com ') to bypass the login screen. IT needs to implement an inline email verification API to ensure only valid data passes through to the CRM.
Q3. A retail venue has dense AP coverage but the marketing team reports that 'zone dwell time' metrics are inaccurate, showing users jumping between opposite ends of the store instantly. How should the network architect address this?
💡 Hint:Consider how APs determine device location and what physical factors affect this.
Show Recommended Approach
The architect needs to recalibrate the RSSI (Received Signal Strength Indicator) thresholds and review the AP placement. The 'jumping' indicates that devices are associating with APs further away due to line-of-sight propagation or signal reflection, rather than the closest AP. Tuning the transmit power and adjusting the location analytics algorithm to require multiple AP triangulations will stabilize the zone data.



