How to Improve WiFi Speed Without Buying New Access Points
This guide details how enterprise venues can reclaim 30%+ of their WiFi bandwidth without purchasing new access points. By implementing DNS filtering, band steering, and QoS policies, IT teams can extend hardware lifespans, reduce CapEx, and improve network performance and security.
Listen to this guide
View podcast transcript

Executive Summary
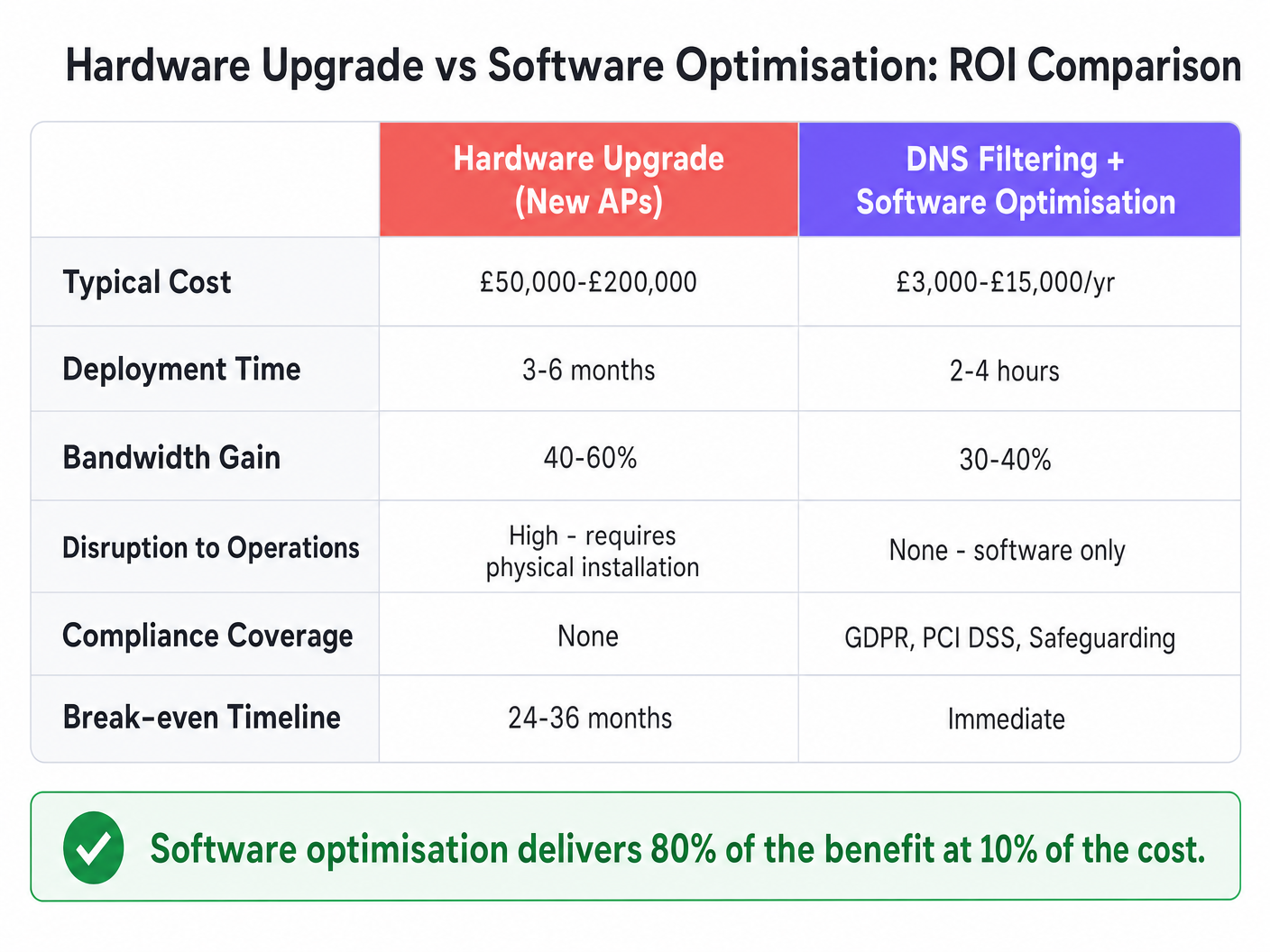
For IT directors and CTOs managing large-scale venue networks, the default response to bandwidth exhaustion is often a costly hardware refresh. However, up to 40% of guest network bandwidth is typically consumed by non-value-adding background telemetry, advertising trackers, and malicious traffic. By implementing software-layer optimization—specifically DNS filtering, intelligent band steering, and QoS policy enforcement—venues can reclaim 30%+ of existing bandwidth without deploying a single new access point.
This guide details how to implement these optimizations to extend the lifespan of current hardware, reduce CapEx, and improve the user experience across Hospitality , Retail , Healthcare , and Transport environments.
Technical Deep-Dive
The Bandwidth Drain: Telemetry and Trackers
When examining the traffic profile of a typical Guest WiFi network, the volume of non-user-initiated traffic is significant. Advertising networks and third-party trackers account for 25% to 40% of DNS query volume. Every app launch triggers dozens of background lookups to analytics platforms and tracking pixels, none of which deliver value to the guest but all of which consume uplink capacity.
Furthermore, compromised devices on the network generate malware and botnet traffic, constantly attempting to contact command-and-control servers. This wastes bandwidth and introduces severe compliance and security risks.
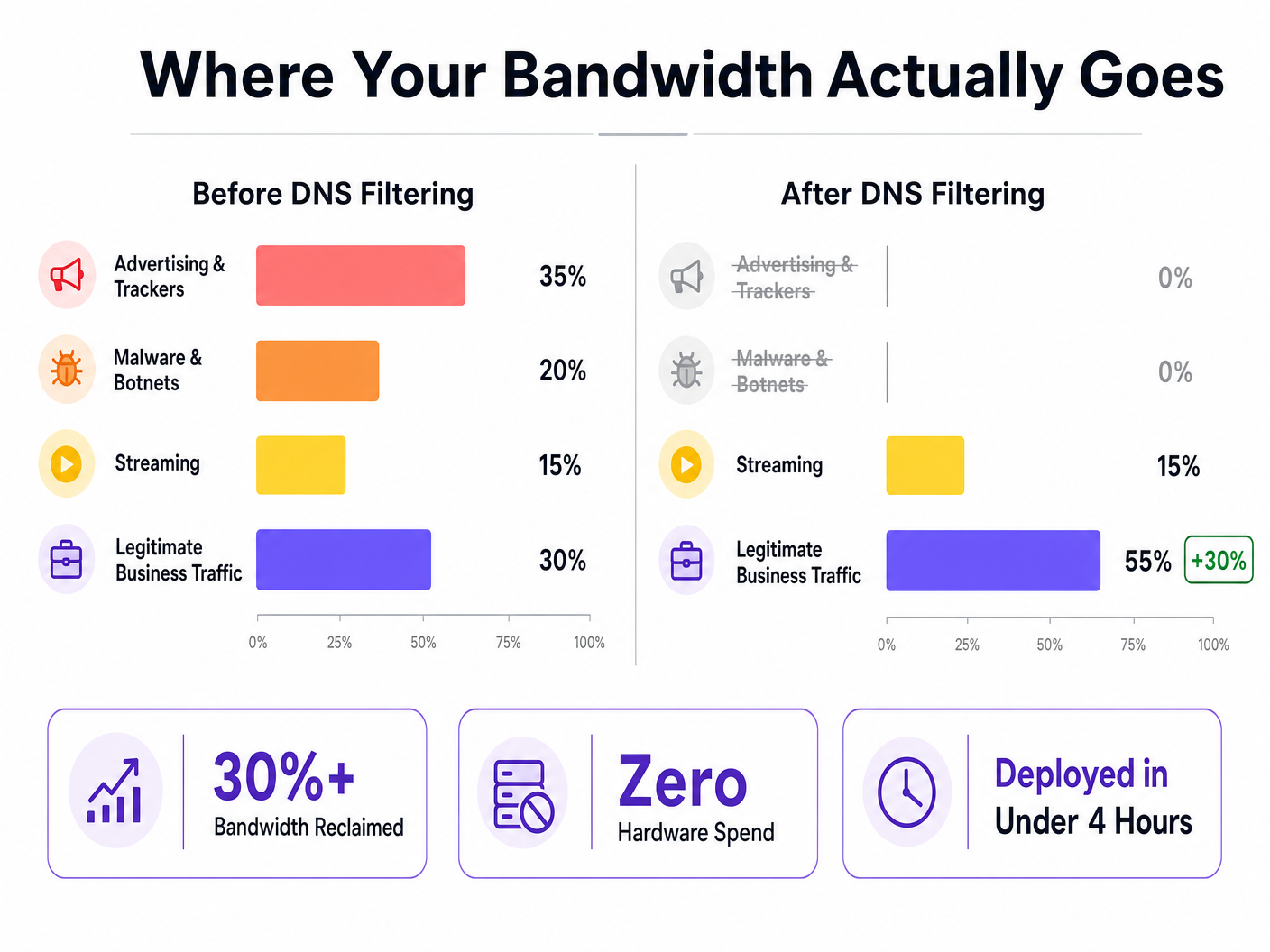
The DNS Filtering Solution
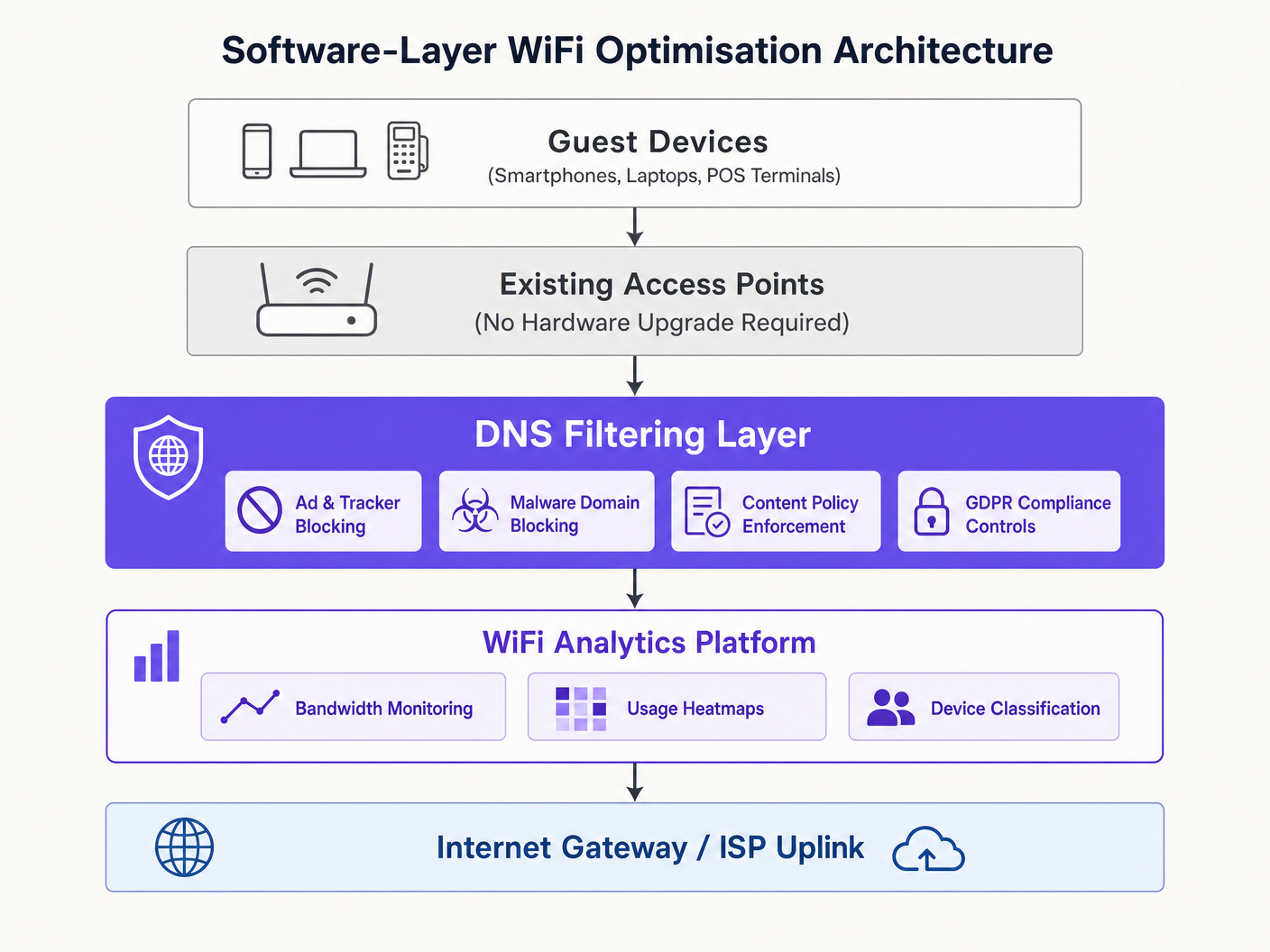
DNS filtering operates at the resolution layer. It intercepts DNS queries before they reach the uplink. If a domain resolves to an advertising network, a known malware host, or a policy-restricted category, the query is blocked, returning a null response to the device. No data is transferred; no bandwidth is consumed.
Unlike firewalls that inspect packets post-arrival or proxies that intercept mid-stream, DNS filtering prevents the request from initiating. This architectural advantage makes it highly efficient for bandwidth reclamation.
Addressing DNS over HTTPS (DoH)
A critical technical consideration is the rise of DNS over HTTPS (DoH). DoH encrypts DNS queries, bypassing network-level DNS and circumventing traditional filtering rules. To maintain filtering efficacy, networks must enforce DoH interception by identifying DoH traffic (typically on port 443 to known resolvers) and redirecting it to a DoH-capable filtering resolver. For further details, refer to our guide on DNS Over HTTPS (DoH): Implications for Public WiFi Filtering (or the Portuguese version: DNS Over HTTPS (DoH): Implicações para a Filtragem de WiFi Público ).
Implementation Guide
Deploying software-layer optimization is straightforward and can be managed centrally for multi-site operators, utilizing platforms like WiFi Analytics to monitor impact.
- Baseline Measurement: Instrument the network to capture DNS query volume by category and per-client bandwidth consumption. This establishes the baseline for ROI calculations.
- Monitoring Mode: Deploy DNS filtering in passive monitoring mode for 48-72 hours to understand traffic composition without blocking, preventing false positives.
- Phased Blocking: Enable blocking for high-confidence categories first (e.g., known malware, botnets, ad networks). Review logs daily to adjust policies.
- Complementary Optimizations:
- Band Steering: Push capable devices to the 5GHz band to free up the congested 2.4GHz band.
- SSID Consolidation: Reduce management overhead by consolidating SSIDs and using VLAN tagging for segmentation.
- QoS Enforcement: Implement per-client rate limiting to protect business-critical traffic (e.g., VoIP, POS) from bulk streaming.
- Document and Measure: After 30 days, compare bandwidth utilization against the baseline to quantify the ROI.
Best Practices
- Segment IoT Traffic: IoT devices often generate significant telemetry. Place them on a separate VLAN with tailored filtering policies to avoid breaking functionality when tightening rules.
- Avoid Over-Blocking: Start with conservative blocking policies and expand gradually based on log reviews to prevent disrupting legitimate business SaaS applications.
- Regular RF Surveys: Periodically re-optimize channel assignments and transmit power to mitigate co-channel interference as the physical environment changes.
Troubleshooting & Risk Mitigation
- Legitimate Services Blocked: If users report broken applications, check DNS logs for broad category blocks affecting required domains (e.g., cloud storage, payment gateways) and whitelist them.
- Declining Filtering Efficacy: If bandwidth consumption creeps back up, verify that DoH bypass policies are actively intercepting and redirecting encrypted DNS queries.
- Legacy Device Connectivity Issues: If older devices struggle to connect after enabling band steering, ensure the 2.4GHz band is still adequately provisioned and consider adjusting steering aggressiveness.
ROI & Business Impact
Software optimization delivers immediate ROI. While a hardware upgrade can cost £50,000-£200,000 and take months to deploy, DNS filtering and configuration changes cost a fraction of that and deploy in hours. Venues typically see a 30-40% reduction in uplink utilization, extending the life of existing APs by 2-4 years while simultaneously strengthening GDPR and PCI DSS compliance.
Listen to our full technical briefing:
Key Definitions
DNS Filtering
The process of blocking access to certain domains at the DNS resolution stage, preventing the connection before data is transferred.
Used to reclaim bandwidth by stopping ad, tracker, and malware traffic before it consumes uplink capacity.
Band Steering
A wireless network feature that encourages dual-band capable clients to connect to the less congested 5GHz band instead of the 2.4GHz band.
Crucial for optimizing airtime and improving throughput in dense environments.
DNS over HTTPS (DoH)
A protocol for performing remote Domain Name System resolution via the HTTPS protocol, encrypting the data.
Creates challenges for network administrators as it can bypass traditional, unencrypted DNS filtering controls.
SSID Consolidation
Reducing the number of broadcasted network names (SSIDs) to minimize management frame overhead.
Each SSID consumes airtime; fewer SSIDs mean more airtime available for actual data transmission.
Quality of Service (QoS)
Technologies that manage data traffic to reduce packet loss, latency, and jitter on the network.
Used to prioritize critical business traffic (like POS transactions) over guest streaming.
VLAN Tagging
The practice of inserting a VLAN ID into a packet header to identify which virtual LAN the packet belongs to.
Allows for logical segmentation of network traffic (e.g., Guest vs. Staff) without requiring separate physical networks or SSIDs.
Beacon Frames
Management frames in IEEE 802.11 based WLANs that contain information about the network.
Broadcasting too many SSIDs generates excessive beacon frames, consuming valuable airtime and slowing down the network.
Co-Channel Interference
Crosstalk from two different radio transmitters using the same frequency channel.
Mitigated by proper channel planning and transmit power optimization to ensure APs don't shout over each other.
Worked Examples
A 200-room hotel is experiencing severe WiFi complaints during the evening peak. The infrastructure vendor recommends a £80,000 AP upgrade. How can software optimization address this?
- Deploy DNS filtering to block ad networks and malware, reclaiming ~30% of bandwidth. 2. Enable band steering to move capable devices to 5GHz. 3. Implement QoS to rate-limit video streaming to 5Mbps per client, prioritizing VoIP and operational traffic. 4. Consolidate from 8 SSIDs to 3 using VLAN tagging.
A large retail chain with 500 stores needs to improve network performance for POS terminals while still offering Guest WiFi.
- Segment POS devices and Guest WiFi onto separate VLANs. 2. Apply aggressive DNS filtering on the Guest VLAN to block high-bandwidth non-essential traffic. 3. Configure strict QoS rules prioritizing the POS VLAN traffic over the Guest VLAN. 4. Manage policies centrally via a unified dashboard.
Practice Questions
Q1. A stadium network is experiencing severe congestion on the 2.4GHz band, while the 5GHz band is underutilized. What is the most immediate software-layer action to take?
Hint: Consider how to force capable devices to use the better frequency.
View model answer
Enable and configure Band Steering on the wireless controller to actively push dual-band capable clients to the 5GHz band, freeing up 2.4GHz capacity for legacy devices.
Q2. After deploying DNS filtering, you notice that overall bandwidth consumption has only dropped by 5%, much lower than the expected 30%. What is the most likely technical reason for this?
Hint: Think about modern browser default behaviors regarding DNS.
View model answer
Client devices are likely using DNS over HTTPS (DoH), bypassing the network's standard DNS resolver. The network must be configured to intercept DoH traffic and redirect it to the filtering resolver.
Q3. A hospital IT team wants to implement DNS filtering but is concerned about blocking critical medical telemetry from IoT devices. How should they architect the deployment?
Hint: How can you apply different rules to different types of devices?
View model answer
Segment the IoT devices onto a dedicated VLAN. Apply a highly specific, permissive DNS filtering policy to the IoT VLAN that allows required telemetry, while applying the stricter ad/malware blocking policy to the Guest and Staff VLANs.