Improving Network Visibility with NAC and MDM Integration
This technical reference guide details the architecture, integration, and business impact of combining Network Access Control (NAC) with Mobile Device Management (MDM). It provides actionable deployment guidance for IT managers and network architects operating complex multi-use environments like hospitality, retail, and public venues.
Listen to this guide
View podcast transcript
- Executive Summary
- Technical Deep-Dive: Architecture and Standards
- The Enforcement Layer: Network Access Control (NAC)
- The Visibility Layer: MDM Integration and Posture Assessment
- Managing the Unmanaged: Guest and IoT Devices
- Implementation Guide
- Phase 1: Device Discovery and Taxonomy
- Phase 2: Read-Only MDM Integration
- Phase 3: Enforcing Posture-Based Access
- Phase 4: Guest and IoT Segmentation
- Best Practices
- Troubleshooting & Risk Mitigation
- ROI & Business Impact
Executive Summary
For enterprise IT teams managing large physical venues—whether a 500-room hotel, a major stadium, or a national retail chain—the network perimeter has dissolved. Today's physical network infrastructure carries a volatile mix of corporate endpoints, BYOD smartphones, unmanaged guest devices, payment terminals, and a rapidly expanding fleet of headless IoT sensors. Operating these environments without granular, real-time network visibility is a significant compliance and security risk.
This guide provides a technical blueprint for improving network visibility with NAC and MDM integration. By bridging the gap between identity, device posture, and network access control, IT architects can transition from static VLAN assignments to dynamic, posture-based segmentation. We will explore the technical architecture required to achieve this, the integration points with guest authentication platforms like Guest WiFi , and the practical implementation steps required to secure multi-use environments without disrupting operations.
Technical Deep-Dive: Architecture and Standards
Network visibility fundamentally requires answering three questions in real-time: What is connecting? Who owns it? Is it compliant? Answering these questions requires an integrated architecture spanning the network edge, the identity provider, and the device management platform.
The Enforcement Layer: Network Access Control (NAC)
At the core of the architecture is the Network Access Control (NAC) system, acting as the Policy Decision Point (PDP). The industry standard for robust NAC implementation remains IEEE 802.1X, utilizing a RADIUS server to authenticate supplicants before granting network access.
When a corporate endpoint attempts to associate with an access point or authenticate to a switch port, the 802.1X framework securely transports the device's credentials (typically via EAP-TLS using digital certificates) to the RADIUS server. The RADIUS server evaluates these credentials against a defined policy matrix to determine the appropriate network segment, dynamically assigning the VLAN via RADIUS attributes.
However, 802.1X alone only verifies identity; it does not verify the security posture of the endpoint. This is where MDM integration becomes critical.
The Visibility Layer: MDM Integration and Posture Assessment
Mobile Device Management (MDM) platforms (e.g., Microsoft Intune, Jamf, Workspace ONE) maintain a continuous inventory of managed devices, tracking OS versions, patch levels, installed applications, and overall compliance states.
The integration between NAC and MDM typically occurs via REST APIs. When a device authenticates via 802.1X, the NAC system intercepts the authentication request and queries the MDM platform using the device's MAC address or certificate identity. The MDM platform returns the device's real-time compliance posture.
If the MDM reports the device as compliant, the NAC system authorizes access to the corporate VLAN. If the device is non-compliant (e.g., missing critical OS updates or running unauthorized software), the NAC system dynamically assigns the device to a remediation VLAN with restricted routing, allowing the device to reach only the MDM server or update servers to self-heal.
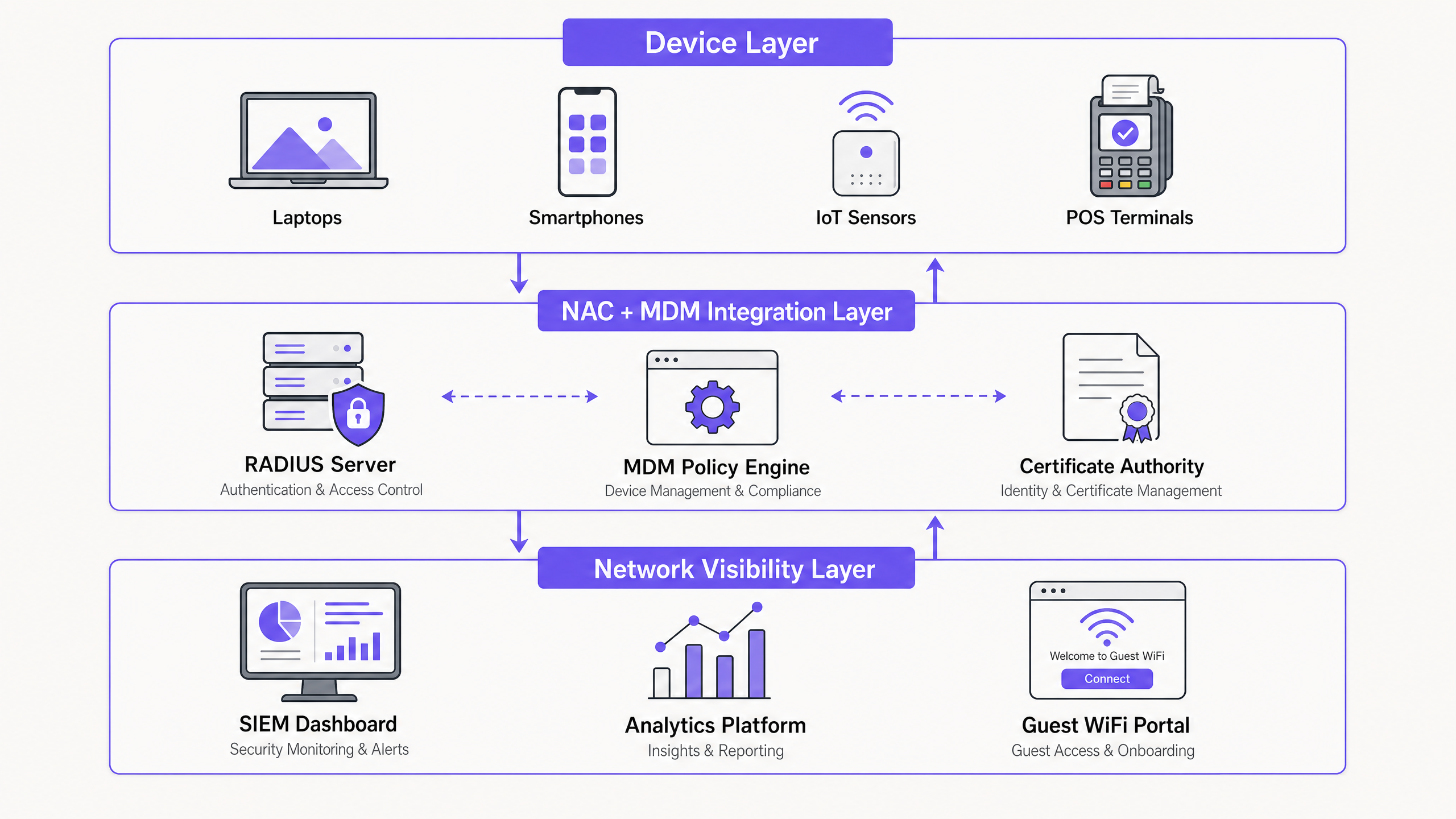
Managing the Unmanaged: Guest and IoT Devices
The primary challenge in venues like Hospitality and Retail environments is the sheer volume of unmanaged devices. These endpoints cannot participate in 802.1X authentication or MDM enrollment.
Guest Devices: For unmanaged guest devices, visibility is achieved through a captive portal architecture. Platforms like Purple's WiFi Analytics intercept the initial HTTP/HTTPS request, redirecting the user to an authentication portal. This layer captures user identity, enforces terms of service, and manages consent in compliance with GDPR. The guest is then placed on an isolated guest VLAN, physically or logically separated from corporate traffic.
IoT Endpoints: Headless devices like HVAC controllers, digital signage, and POS terminals typically rely on MAC Authentication Bypass (MAB). Because MAC addresses are easily spoofed, MAB must be combined with deep device profiling. Modern NAC systems analyze DHCP fingerprints, HTTP user agents, and traffic behavioral patterns to accurately classify IoT devices and assign them to heavily restricted, micro-segmented IoT VLANs.
Implementation Guide
Deploying an integrated NAC and MDM architecture requires a phased, methodical approach to avoid widespread operational disruption.
Phase 1: Device Discovery and Taxonomy
Before configuring any enforcement policies, you must establish a comprehensive baseline of your current network state. Deploy the NAC system in "Monitor Mode" (often utilizing SPAN ports or NetFlow data) to passively observe traffic and catalog every connected endpoint.
Develop a strict device taxonomy. Define distinct categories: Corporate Managed, BYOD, Guest, IoT (Sub-categorized by function), and Contractor. Each category must map to a specific authentication method, policy set, and target VLAN.
Phase 2: Read-Only MDM Integration
Integrate the NAC system with the MDM API, but configure the policies to log compliance failures without enforcing quarantine. This read-only phase is critical. In enterprise deployments, the initial posture check frequently reveals a high percentage of non-compliant devices due to delayed patch cycles or certificate sync issues. Enforcing posture checks before understanding this baseline will result in a self-inflicted denial of service. Use this phase to remediate the baseline through standard IT processes.
Phase 3: Enforcing Posture-Based Access
Once the compliance baseline is stable, transition the corporate policies from monitor to enforcement mode. Begin with a pilot group of IT users before rolling out across the wider organization. Ensure that the remediation VLAN is correctly routed to allow access to the MDM platform and necessary update servers, but strictly firewalled from internal resources.
Phase 4: Guest and IoT Segmentation
Implement the guest authentication portal and MAB profiling for IoT. For environments subject to PCI DSS, ensure that the POS terminal VLAN is completely isolated from the guest and corporate segments. Validate the segmentation using automated penetration testing tools to confirm that cross-VLAN routing is explicitly denied.
Best Practices
- Prioritize Certificate-Based Authentication (EAP-TLS): Relying on usernames and passwords for 802.1X (PEAP-MSCHAPv2) is increasingly vulnerable to credential harvesting. Deploy a robust PKI and use the MDM platform to automatically provision machine and user certificates to managed endpoints.
- Implement WPA3-Enterprise: When deploying new wireless infrastructure, mandate WPA3-Enterprise. The 192-bit security mode provides cryptographic enhancements that protect the authentication exchange from offline dictionary attacks. For more context on modern wireless standards, refer to our guide on Wi Fi Frequencies: A Guide to Wi-Fi Frequencies in 2026 .
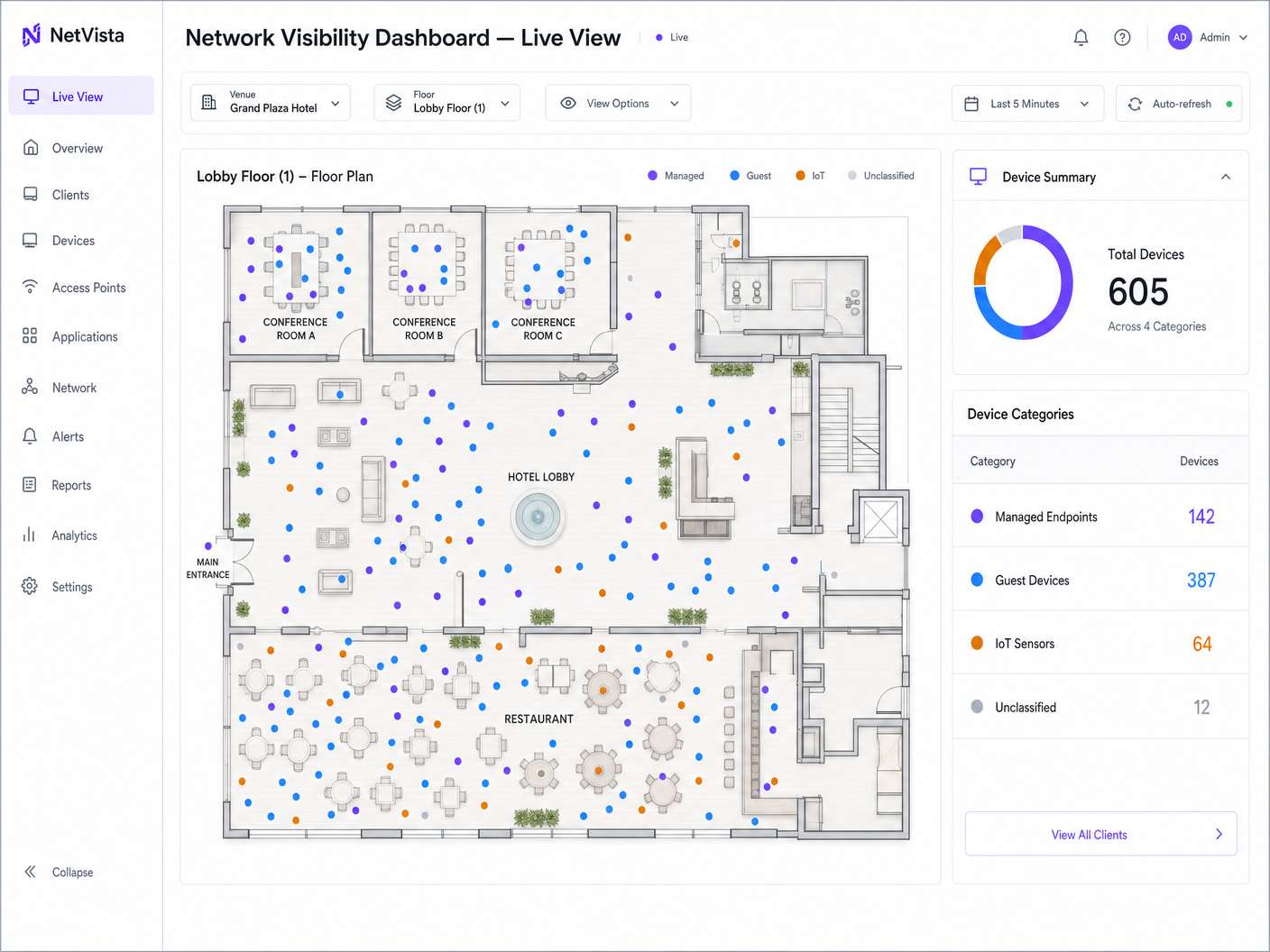
- Unify Visibility in a SIEM: Network visibility is only actionable if it is centralized. Forward all NAC authentication logs, MDM compliance events, and guest WiFi analytics to a central Security Information and Event Management (SIEM) platform. This enables correlation between network behavior, device posture, and physical location (leveraging Indoor WiFi Positioning Systems: How They Work and How to Deploy Them ).
Troubleshooting & Risk Mitigation
- Failure Mode: API Rate Limiting: High-density environments (like a stadium on match day) can generate thousands of simultaneous authentications. If the NAC system queries the MDM API for every request, it may trigger rate limits, causing authentications to fail open or fail closed.
- Mitigation: Implement caching on the NAC system for MDM posture status, typically caching the result for 15-30 minutes, or utilize webhook-based push notifications from the MDM to the NAC for real-time state changes.
- Failure Mode: Certificate Expiry: A lapsed root or intermediate CA certificate will instantly invalidate all EAP-TLS authentications, locking all managed devices off the network.
- Mitigation: Implement aggressive monitoring and alerting for PKI infrastructure. Ensure auto-enrollment policies in the MDM are functioning and devices are checking in regularly.
- Failure Mode: MAB Spoofing: An attacker clones the MAC address of an authorized printer to gain access to the internal VLAN.
- Mitigation: Do not rely solely on MAB. Implement endpoint profiling that continually monitors the device's behavior. If a "printer" suddenly initiates an SSH connection or runs an Nmap scan, the NAC system must detect the anomaly and immediately quarantine the port.
ROI & Business Impact
The business case for integrating NAC and MDM extends beyond security compliance. The primary return on investment is realized through risk mitigation and operational efficiency.
By automating device onboarding and posture enforcement, IT helpdesks see a significant reduction in tickets related to network access and compliance remediation. From a security perspective, dynamic segmentation dramatically reduces the blast radius of a compromised endpoint, lowering the potential cost and operational impact of a breach.
Furthermore, in public-facing venues like Transport hubs or retail centers, separating the complex corporate and IoT infrastructure from the guest experience ensures that guest services remain highly available and performant, supporting broader business objectives around customer engagement and data capture.
Key Definitions
Network Access Control (NAC)
A security solution that enforces policy on devices attempting to access a network, acting as the gatekeeper to ensure only authorized and compliant devices connect.
IT teams deploy NAC to prevent unauthorized devices from plugging into switch ports or connecting to corporate SSIDs.
Mobile Device Management (MDM)
Software used by IT departments to monitor, manage, and secure employees' mobile devices, laptops, and tablets across multiple operating systems.
MDM is the source of truth for device compliance, telling the network whether a device is patched and secure.
IEEE 802.1X
An IEEE Standard for port-based Network Access Control, providing an authentication mechanism to devices wishing to attach to a LAN or WLAN.
This is the underlying protocol that allows a laptop to securely present its certificate to the network infrastructure.
MAC Authentication Bypass (MAB)
A fallback authentication method for devices that do not support 802.1X (like printers or IoT sensors), using the device's MAC address as its identity.
Crucial for venue operations where headless IoT devices must connect to the network without user intervention.
Device Profiling
The process of analyzing network traffic, DHCP requests, and behavioral patterns to accurately identify the type and operating system of an unmanaged device.
Used alongside MAB to ensure a device claiming to be a printer actually behaves like a printer, mitigating MAC spoofing attacks.
Dynamic VLAN Assignment
The ability of the network infrastructure to assign a device to a specific Virtual LAN based on its authentication credentials and posture, rather than the physical port it connects to.
Allows a single physical switch or access point to securely service corporate, guest, and IoT devices simultaneously.
Captive Portal
A web page that the user of a public-access network is obliged to view and interact with before access is granted.
The primary mechanism for managing guest WiFi access, capturing marketing data, and enforcing terms of service.
Posture-Based Access Control
An access model where network privileges are dynamically adjusted based on the real-time security state (posture) of the connecting device.
The ultimate goal of NAC and MDM integration, ensuring compromised devices are automatically quarantined.
Worked Examples
A 400-room hotel needs to secure its network infrastructure. The current setup uses a single flat network for staff laptops, smart TVs in guest rooms, point-of-sale (POS) terminals in the restaurant, and guest WiFi. How should the IT architect redesign this using NAC and MDM integration?
- Deploy a NAC appliance and integrate it with the corporate MDM. 2. Create distinct VLANs: Corporate, Guest, IoT (Smart TVs), and PCI (POS). 3. Push EAP-TLS certificates to staff laptops via MDM; configure NAC to assign these to the Corporate VLAN only if the MDM reports them as compliant. 4. Configure MAB with device profiling for the Smart TVs, assigning them to the IoT VLAN with strict ACLs preventing internet access. 5. Isolate POS terminals on the PCI VLAN with hardcoded MAC access lists and micro-segmentation. 6. Deploy Purple Guest WiFi for the public SSID, capturing user consent and assigning them to the isolated Guest VLAN.
A national retail chain is deploying new handheld inventory scanners across 500 stores. The scanners are Android-based and managed by an MDM. Store managers report that scanners frequently drop off the network when moving between the stockroom and the shop floor.
- Review the roaming configuration on the wireless LAN controller (WLC) to ensure 802.11r (Fast Transition) is enabled for the corporate SSID. 2. Check the NAC policy: ensure that the MDM API query isn't introducing latency during the roam. 3. Implement posture caching on the NAC system so that an MDM compliance check is only performed upon initial association, not during every AP transition. 4. Verify that the MDM is pushing the correct WPA3-Enterprise profile to the scanners.
Practice Questions
Q1. Your organization is rolling out a new MDM platform and wants to enforce strict posture checks (e.g., OS patched within 30 days) via the NAC system starting next Monday. What is the primary risk of this approach?
Hint: Consider the difference between theoretical compliance and actual device state in a large enterprise.
View model answer
The primary risk is a widespread denial of service for legitimate users. It is highly likely that a significant portion of the fleet is currently non-compliant due to delayed update cycles or offline devices. The correct approach is to run the integration in 'Monitor Mode' first to establish a baseline, remediate the non-compliant devices through standard IT processes, and only enforce the posture check once the compliance rate is acceptable.
Q2. A stadium IT director wants to use 802.1X for all devices connecting to the network, including digital signage and POS terminals, to maximize security. Why is this architecturally flawed?
Hint: Think about the capabilities of headless devices.
View model answer
This is flawed because most IoT devices, digital signage, and many legacy POS terminals are 'headless' and do not have an 802.1X supplicant; they cannot present credentials or certificates. Attempting to force 802.1X will result in these devices failing to connect. The architect must use MAC Authentication Bypass (MAB) combined with deep device profiling to secure these endpoints on dedicated, restricted VLANs.
Q3. During a PCI DSS audit, the QSA asks you to prove that the guest WiFi network cannot communicate with the POS terminals in the retail stores. How does your NAC architecture demonstrate this?
Hint: Focus on the outcome of the authentication process.
View model answer
The NAC architecture demonstrates this through dynamic VLAN assignment. When a guest connects, they are routed through the captive portal and assigned to an isolated Guest VLAN. When a POS terminal connects, it is profiled via MAB and assigned to a dedicated PCI VLAN. The core network switches and firewalls are configured with Access Control Lists (ACLs) that explicitly deny routing between the Guest VLAN and the PCI VLAN, satisfying the segmentation requirement.