Micro-Segmentation Best Practices for Shared WiFi Networks
This technical reference guide provides actionable strategies for implementing micro-segmentation on shared WiFi infrastructure. It details how IT managers and network architects can securely isolate guest, IoT, and staff traffic to mitigate risk, ensure compliance, and optimise network performance.
Listen to this guide
View podcast transcript
- Executive Summary
- Technical Deep-Dive
- The Authentication Layer: IEEE 802.1X and WPA3
- The Three Core Segments
- Implementation Guide
- Phase 1: Network Discovery and Auditing
- Phase 2: Policy Definition
- Phase 3: Infrastructure Configuration
- Phase 4: Phased Rollout
- Best Practices
- Troubleshooting & Risk Mitigation
- ROI & Business Impact

Executive Summary
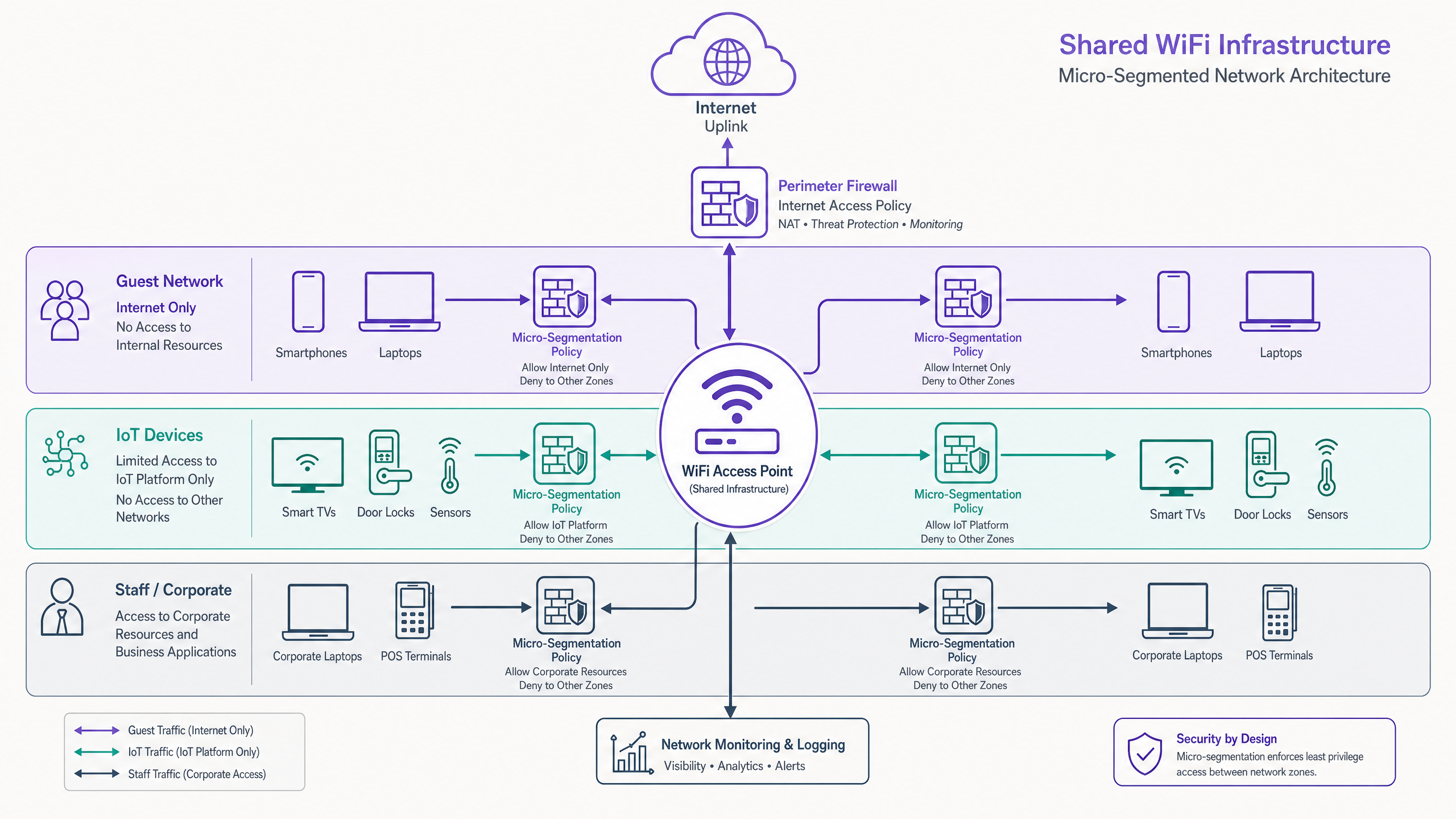
Operating a shared WLAN infrastructure without granular micro-segmentation is a significant security liability for modern venues. As the perimeter dissolves, the internal network becomes the primary attack surface. This guide details the architectural principles and deployment methodologies required to enforce zero-trust isolation between guest traffic, IoT fleets, and corporate endpoints on a unified physical access layer.
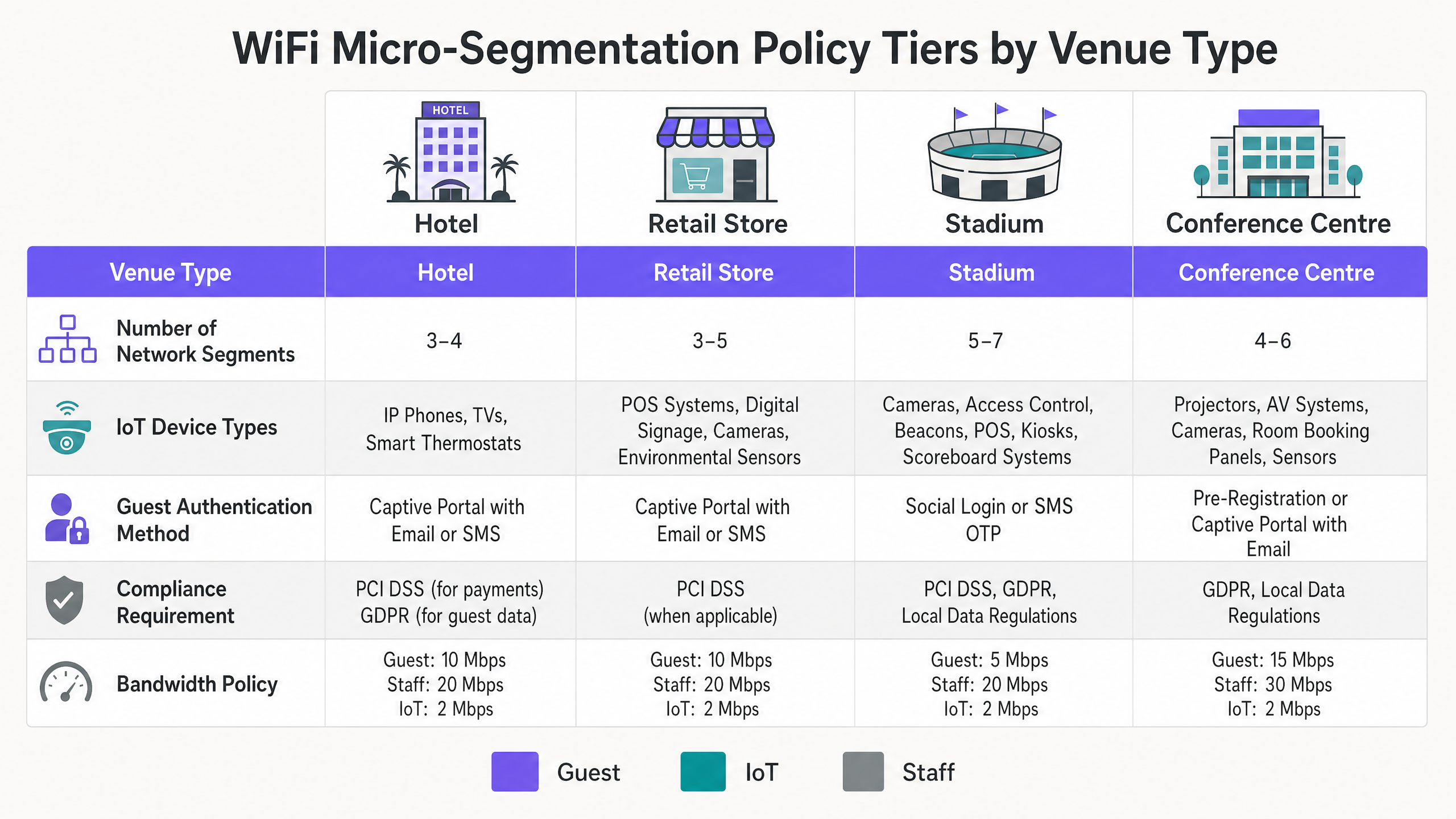
For CTOs and network architects in Hospitality , Retail , Healthcare , and Transport , the mandate is clear: traditional VLANs are insufficient. By implementing dynamic, policy-driven micro-segmentation using IEEE 802.1X and RADIUS, organisations can significantly reduce their PCI DSS and GDPR compliance scope while mitigating the risk of lateral movement from compromised embedded devices.
Listen to the technical briefing podcast for an audio summary:
Technical Deep-Dive
Micro-segmentation on a shared WLAN requires moving beyond static SSID-to-VLAN mapping. It demands dynamic, identity-driven policy enforcement at the edge.
The Authentication Layer: IEEE 802.1X and WPA3
The foundation of effective segmentation is robust authentication. Relying solely on Pre-Shared Keys (PSKs) across multiple SSIDs provides an illusion of separation. True micro-segmentation leverages IEEE 802.1X to authenticate the device or user against a RADIUS backend, dynamically assigning the client to the appropriate VLAN and applying specific Access Control Lists (ACLs) based on identity.
For modern deployments, WPA3 is non-negotiable. Guest networks should utilise WPA3-Personal with Simultaneous Authentication of Equals (SAE) to protect against offline dictionary attacks, while corporate segments must mandate WPA3-Enterprise (192-bit mode where hardware permits).
The Three Core Segments
Guest Traffic (Untrusted): Guests represent the highest volume and lowest trust segment. Authentication is typically handled via a captive portal ( Guest WiFi ) using email, SMS, or social login. The critical control here is Client Isolation (Layer 2 isolation) to prevent peer-to-peer communication between guest devices. Traffic must be strictly internet-only, with DNS filtering applied to block malicious domains. See our guide on What is DNS Filtering? How to Block Harmful Content on Guest WiFi for implementation details.
IoT Devices (Semi-Trusted, High Risk): IoT devices—from smart TVs to HVAC sensors—are notorious for poor security hygiene. They must reside in an isolated segment with egress-only policies. An IoT device should only be able to communicate with its specific management platform. Implementing BLE Low Energy Explained for Enterprise tracking or sensor networks requires this strict isolation to prevent lateral movement.
Staff and Corporate (Trusted): This segment handles sensitive data, including POS transactions and HR systems. Access must require certificate-based mutual authentication (EAP-TLS). Corporate devices should be enrolled via MDM, ensuring seamless and secure connectivity.
Implementation Guide
Deploying micro-segmentation across a distributed venue estate requires a phased, methodical approach.
Phase 1: Network Discovery and Auditing
You cannot segment what you cannot see. Begin with a comprehensive audit of all connected devices, mapping them to their required network access levels. Utilize flow monitoring (NetFlow/sFlow) to baseline normal communication patterns.
Phase 2: Policy Definition
Define your segmentation matrix. Map each device class to a specific VLAN and define the inter-VLAN routing rules. The default posture must be deny-all, with explicit permit exceptions only where strictly necessary.
Phase 3: Infrastructure Configuration
Configure your RADIUS server to return the correct Vendor-Specific Attributes (VSAs) for dynamic VLAN assignment. Ensure your access points and upstream switches are configured to tag and trunk these VLANs correctly.
Phase 4: Phased Rollout
Do not attempt a "big bang" migration. Begin by isolating the IoT fleet—this offers the highest immediate security return with minimal user disruption. Follow with the guest segment, and finally, migrate corporate devices to the secure 802.1X segment.
Best Practices
- Enforce Client Isolation: Always enable client isolation on guest SSIDs to prevent lateral attacks between untrusted devices.
- Utilise Dynamic VLAN Assignment: Move away from static SSID mapping. Use RADIUS to assign VLANs based on user role or device profiling.
- Implement DNS Filtering: Apply segment-specific DNS filtering policies to prevent malware communication and enforce acceptable use policies.
- Optimize for Your Environment: Tailor your RF design and segmentation strategy to your specific venue type. Read more on Office Wi Fi: Optimize Your Modern Office Wi-Fi Network and understand the impact of Wi Fi Frequencies: A Guide to Wi-Fi Frequencies in 2026 .
- Leverage Analytics: Use WiFi Analytics to monitor segment utilization and identify anomalous behavior.

Troubleshooting & Risk Mitigation
The most common failure mode in micro-segmentation deployments is misconfigured inter-VLAN routing. If a firewall rule inadvertently permits traffic between the IoT and Corporate segments, the segmentation is compromised.
Common Pitfalls:
- Management Interface Exposure: Leaving AP or switch management interfaces accessible from the guest or IoT segments. Management traffic must reside on a dedicated, highly restricted out-of-band VLAN.
- RADIUS Failures: A misconfigured RADIUS server dropping 802.1X authentications will result in widespread connectivity failure for corporate devices. Implement redundant RADIUS infrastructure.
- Asymmetric Routing: Ensure return traffic paths are correctly defined in your firewall policies to prevent dropped connections.
ROI & Business Impact
Implementing robust micro-segmentation delivers measurable business value:
- Reduced Compliance Scope: By cryptographically isolating POS terminals and payment systems, you significantly reduce the scope and cost of PCI DSS audits.
- Risk Mitigation: Containing a potential breach to a single segment (e.g., a compromised digital signage player) prevents catastrophic lateral movement into core corporate systems.
- Operational Efficiency: Dynamic VLAN assignment reduces the administrative overhead of manually configuring switch ports and managing multiple static SSIDs.
Key Definitions
Micro-Segmentation
The practice of dividing a network into granular, isolated zones to enforce strict security policies and contain potential breaches.
Essential for venue operators running diverse device types (Guest, IoT, Staff) on a single physical network infrastructure.
IEEE 802.1X
A standard for port-based network access control that provides an authentication mechanism to devices wishing to attach to a LAN or WLAN.
The engine for dynamic VLAN assignment and robust corporate device onboarding.
Dynamic VLAN Assignment
The process where a RADIUS server instructs the access point or switch which VLAN a client should be placed in upon successful authentication.
Allows a single SSID to securely serve multiple user roles without static configuration.
Client Isolation
A wireless network feature that prevents connected clients from communicating directly with each other.
A mandatory configuration for any guest WiFi network to prevent peer-to-peer attacks and ensure privacy.
MAC Authentication Bypass (MAB)
A technique used to authenticate devices that do not support 802.1X by using their MAC address as the credential.
Commonly used to onboard headless IoT devices like smart TVs or sensors onto a segmented network.
EAP-TLS
Extensible Authentication Protocol-Transport Layer Security; a highly secure authentication method requiring client and server certificates.
The gold standard for authenticating corporate devices and POS systems to prevent credential theft.
WPA3-Enterprise
The latest WiFi security standard for enterprise networks, offering stronger encryption and robust authentication.
Should be mandated for all new deployments to protect sensitive corporate and staff traffic.
Quality of Service (QoS)
Technologies that manage data traffic to reduce packet loss, latency, and jitter on the network.
Used in conjunction with segmentation to ensure critical applications (like POS) are prioritized over guest or IoT traffic.
Worked Examples
A 200-room hotel needs to deploy new smart TVs in every guest room, upgrade their POS systems in the restaurant, and provide high-speed guest WiFi, all on the existing physical network infrastructure. How should they architect the segmentation?
- Implement three distinct VLANs: Guest (VLAN 10), IoT (VLAN 20), and Corporate/POS (VLAN 30).
- Configure the APs to broadcast two SSIDs: 'Hotel_Guest' (Open with Captive Portal, mapped to VLAN 10) and 'Hotel_Secure' (802.1X).
- Enable Client Isolation on the 'Hotel_Guest' SSID.
- Use MAC-based RADIUS authentication (MAB) for the Smart TVs to dynamically assign them to VLAN 20.
- Use EAP-TLS certificate authentication for the POS terminals to assign them to VLAN 30.
- Configure the perimeter firewall to deny all inter-VLAN traffic, permitting VLAN 10 and 20 internet-only access, and restricting VLAN 30 to the corporate VPN tunnel.
A large retail chain is experiencing network congestion and suspects their digital signage media players (IoT) are saturating the uplink, impacting the performance of their mobile POS tablets.
- Audit the current network configuration to confirm if digital signage and POS tablets share the same segment.
- Implement micro-segmentation by moving the digital signage players to a dedicated IoT VLAN.
- Apply Quality of Service (QoS) policies at the access switch or AP level: rate-limit the IoT VLAN to 5 Mbps per device, and prioritize traffic from the POS VLAN.
- Ensure the IoT VLAN has a strict egress-only firewall policy to the specific content delivery network (CDN) used by the signage vendor.
Practice Questions
Q1. You are deploying a new WiFi network for a large conference centre. The venue requires a public guest network, a dedicated network for AV equipment (projectors, digital signage), and a secure network for venue staff. You have been instructed to minimize the number of broadcasted SSIDs. How do you architect the wireless access layer?
Hint: Consider how different device types authenticate and how RADIUS can dynamically assign VLANs.
View model answer
Broadcast two SSIDs. SSID 1 ('Conference_Guest'): Open network with a captive portal for guest access, mapped to a Guest VLAN with client isolation and internet-only firewall rules. SSID 2 ('Conference_Secure'): 802.1X enabled. Venue staff authenticate via EAP-TLS (certificates) and are dynamically assigned to the Staff VLAN. AV equipment authenticates via MAC Authentication Bypass (MAB) against the RADIUS server and is dynamically assigned to the isolated AV/IoT VLAN.
Q2. During a security audit, a penetration tester successfully compromises a smart thermostat in the hotel lobby. From the thermostat, they are able to access the hotel's reservation database server. What architectural failure allowed this, and how should it be remediated?
Hint: Consider inter-VLAN routing policies and the principle of least privilege.
View model answer
The architectural failure is a lack of micro-segmentation and permissive inter-VLAN routing. The IoT device (thermostat) was either placed on the same VLAN as the corporate servers, or the firewall separating the VLANs allowed inbound traffic from the IoT segment to the corporate segment. Remediation: Move all thermostats to a dedicated IoT VLAN. Configure the perimeter firewall with a default-deny policy between VLANs. The IoT VLAN should only be permitted egress traffic to the specific cloud controller required for the thermostats, with no access to internal corporate resources.
Q3. A retail client complains that their guest WiFi is extremely slow during peak hours, and they notice that the POS systems are also experiencing latency. Both are running on the same physical access points. What is the most likely cause, and what are the recommended steps to resolve it?
Hint: Think about bandwidth contention and traffic prioritization.
View model answer
The likely cause is bandwidth contention on the shared uplink, with guest traffic saturating the connection and impacting critical POS traffic. Resolution: Implement Quality of Service (QoS) and rate-limiting. 1. Ensure POS and Guest traffic are on separate VLANs. 2. Apply a rate-limit policy to the Guest VLAN (e.g., 5 Mbps per client) to prevent any single guest from hogging bandwidth. 3. Configure QoS rules on the switch and firewall to prioritize traffic originating from the POS VLAN over the Guest VLAN.