Patient WiFi: A Complete Guide for NHS Trusts and Hospital Operators
A definitive technical and commercial guide for NHS Trusts and hospital operators on deploying, securing, and monetising patient WiFi. Covers network segmentation, DSPT compliance, content filtering, and leveraging analytics to improve patient outcomes.
🎧 Listen to this Guide
View Transcript
- Executive Summary
- Technical Deep-Dive: Architecture and Standards
- Network Segmentation and VLAN Design
- Access Point Density and RF Planning
- Backhaul and Throughput Requirements
- Implementation Guide: Compliance and Filtering
- DSPT Compliance
- Content Filtering
- Captive Portals and GDPR
- ROI & Business Impact: Free vs. Paid Models
- The Free WiFi Model
- The Concessionaire Model

Executive Summary
Providing robust, secure, and compliant patient WiFi is no longer a "nice-to-have" amenity for NHS Trusts and private hospital operators—it is a critical infrastructure requirement. Patients expect connectivity to manage their lives, communicate with family, and access digital health services during their stay. However, delivering this connectivity in a clinical environment introduces significant technical and governance challenges.
This guide provides a comprehensive framework for IT managers, network architects, and CTOs to design, deploy, and manage patient WiFi networks. We explore the necessity of strict network segmentation, the complexities of Data Security and Protection Toolkit (DSPT) compliance, the implementation of rigorous content filtering, and the commercial models that sustain these deployments. By treating patient WiFi as an enterprise-grade service rather than a consumer broadband overlay, Trusts can mitigate risk, ensure clinical system integrity, and leverage platforms like Guest WiFi to capture actionable insights and improve patient satisfaction.
Technical Deep-Dive: Architecture and Standards
The foundation of any hospital WiFi deployment is absolute segregation between patient traffic and clinical systems. A hospital is a high-density, high-interference RF environment where life-critical devices operate in close proximity to consumer smartphones.
Network Segmentation and VLAN Design
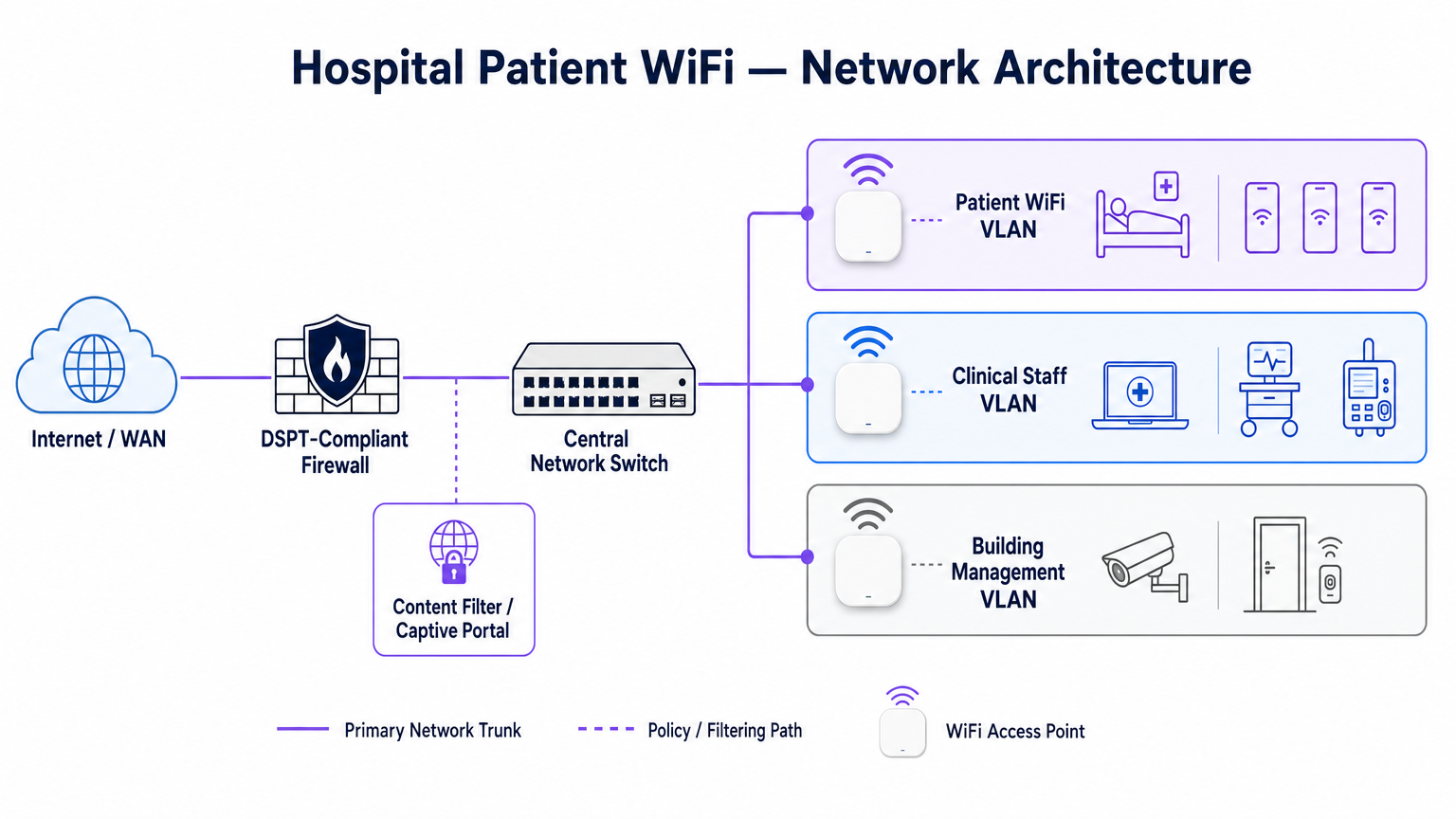
To protect clinical integrity, patient WiFi must operate on a dedicated Virtual Local Area Network (VLAN). The standard enterprise architecture dictates a minimum of three distinct segments:
- Patient/Guest VLAN: Routes through a captive portal, enforces strict content filtering, and provides internet-only access.
- Clinical VLAN: Dedicated to staff devices and medical equipment (e.g., infusion pumps, mobile workstations). Bypasses the captive portal and routes through a monitored, secure path.
- Building Management VLAN: Supports IoT devices, CCTV, and environmental controls.
Traffic on the Patient VLAN must be isolated at the switch level and restricted by firewall rules that explicitly deny routing to internal subnets.
Access Point Density and RF Planning
Deploying WiFi in a hospital requires overcoming significant physical barriers—lead-lined walls, heavy machinery, and dense concrete. Relying on "hallway coverage" is a common failure mode. A predictive RF survey, followed by an active post-installation validation, is mandatory.
For new deployments, IEEE 802.11ax (Wi-Fi 6) is the baseline standard. Its implementation of Orthogonal Frequency-Division Multiple Access (OFDMA) and BSS Colouring is crucial for handling the high device density typical of modern hospital wards, reducing latency and mitigating interference from medical telemetry systems operating in the 2.4 GHz band.
Backhaul and Throughput Requirements
A common pitfall is provisioning enterprise-grade access points but starving them with insufficient backhaul. A 500-bed hospital can easily generate 1 Gbps of concurrent demand during evening peak hours. Operators must provision dedicated, uncontended leased lines rather than shared broadband circuits to guarantee throughput and avoid bottlenecking the core network. For further context on dedicated connectivity, see What Is a Leased Line? Dedicated Business Internet .
Implementation Guide: Compliance and Filtering
Deploying the physical infrastructure is only half the challenge; the governance and compliance overlay is equally critical.
DSPT Compliance
For NHS Trusts, adherence to the Data Security and Protection Toolkit (DSPT) is non-negotiable. Patient WiFi deployments must evidence:
- Strict network segmentation.
- Robust access controls and audit logging (connection logs retained for a minimum of 12 months).
- Annual third-party penetration testing.
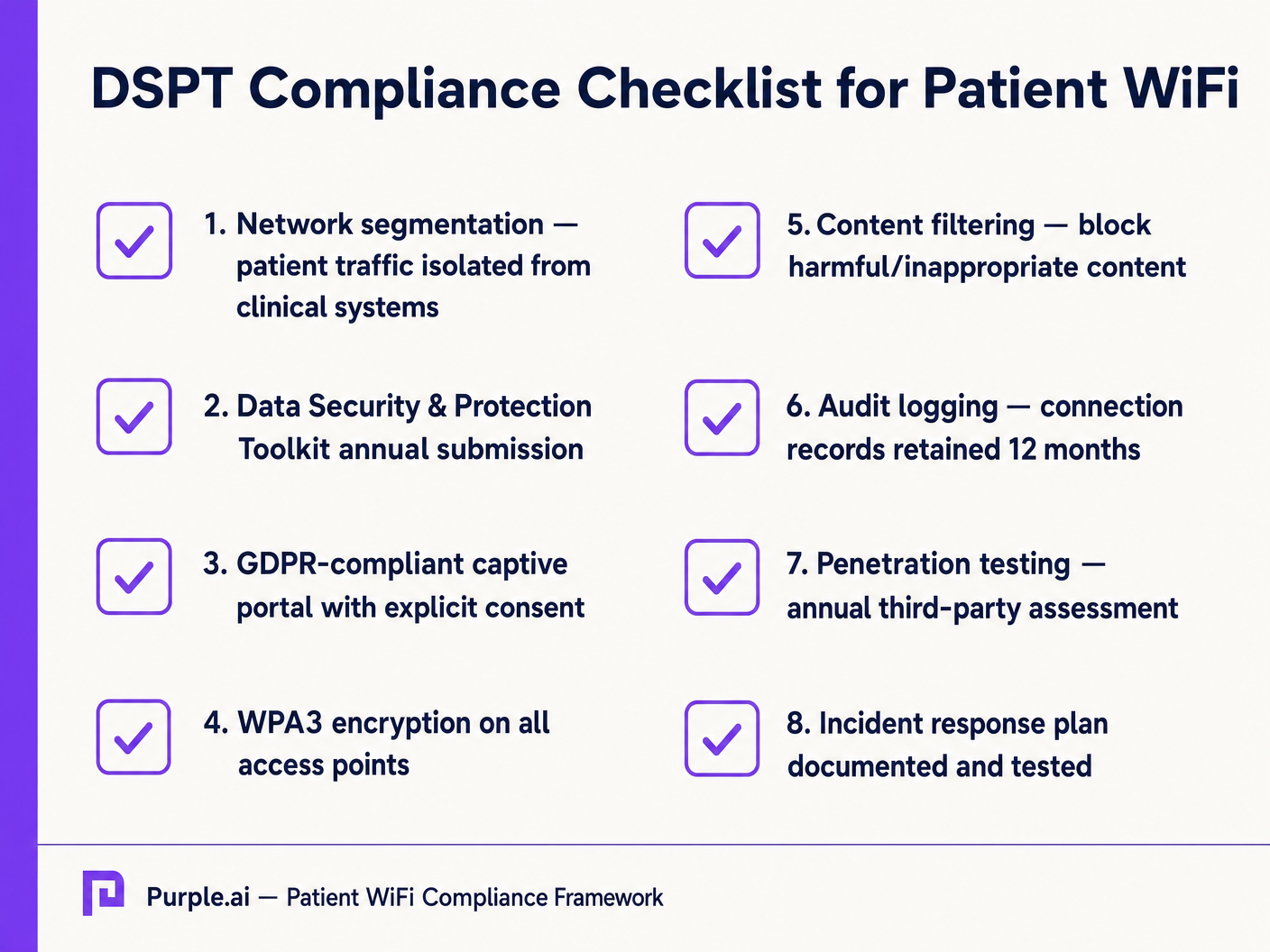
Content Filtering
NHS guidance mandates that patient WiFi must block access to inappropriate or harmful content, including adult material, extremist sites, and gambling platforms. This is typically achieved via DNS-based or proxy-based filtering applied directly to the Patient VLAN. The filtering solution must ingest real-time threat intelligence feeds to block newly identified malicious domains dynamically.
Captive Portals and GDPR
The captive portal is the gateway to the network and the primary mechanism for capturing user consent. Under GDPR, Trusts must obtain explicit, informed consent before processing personal data (such as MAC addresses or email addresses). The portal must present a clear privacy policy and explicit opt-ins. Utilizing a robust platform ensures compliance while enabling the collection of valuable demographic data.
ROI & Business Impact: Free vs. Paid Models
The commercial strategy behind patient WiFi defines its long-term sustainability.
The Free WiFi Model
The vast majority of NHS Trusts offer patient WiFi free of charge at the point of use. This model is typically funded through capital expenditure or operational budgets. The ROI is measured in patient satisfaction (often reflected in Friends and Family Test scores) and the reduction of administrative burden on clinical staff, who no longer need to field connectivity complaints.
The Concessionaire Model
Some larger Trusts employ a concessionaire model, where a third-party managed service provider (MSP) funds the infrastructure in exchange for monetisation rights. This can involve serving targeted advertising through the captive portal or offering a tiered service (free basic browsing, paid premium streaming). If adopting this model, Trusts must ensure that advertising content is strictly vetted to align with NHS values and that data monetisation practices comply with GDPR.
By integrating WiFi Analytics , Trusts can monitor network utilisation, track patient dwell times, and trigger automated feedback surveys post-connection, transforming a cost centre into a strategic asset for operational improvement. This data-driven approach mirrors successful deployments in other sectors, such as Healthcare and Retail .
Key Terms & Definitions
VLAN (Virtual Local Area Network)
A logical subnetwork that groups a collection of devices from different physical LANs. Essential for isolating patient traffic from clinical systems.
Used by network architects to ensure that a compromised patient device cannot access sensitive medical equipment or electronic health records.
DSPT (Data Security and Protection Toolkit)
An online self-assessment tool that allows NHS organisations to measure their performance against the National Data Guardian's 10 data security standards.
Mandatory for all NHS Trusts; failure to properly segment patient WiFi or log access can result in a failed DSPT submission.
Captive Portal
A web page that a user of a public-access network is obliged to view and interact with before access is granted.
The primary interface for capturing user consent, presenting terms of use, and applying brand identity to the WiFi experience.
802.11ax (Wi-Fi 6)
The sixth generation of the Wi-Fi standard, designed specifically to improve performance in high-density environments.
Crucial for hospital wards where dozens of patients, visitors, and staff devices are competing for airtime simultaneously.
OFDMA (Orthogonal Frequency-Division Multiple Access)
A feature of Wi-Fi 6 that allows a single transmission to deliver data to multiple devices simultaneously.
Reduces latency and improves efficiency in crowded hospital environments, preventing the network from grinding to a halt during peak hours.
Content Filtering
The use of software or hardware to restrict the content that a reader is authorised to access over the network.
Required by NHS guidance to prevent access to illegal, extremist, or adult content on patient networks.
Leased Line
A dedicated, fixed-bandwidth, symmetric data connection connecting a business directly to the internet exchange.
Necessary for hospital WiFi backhaul to ensure guaranteed throughput, avoiding the contention issues of shared broadband.
MAC Address
A unique identifier assigned to a network interface controller (NIC) for use as a network address in communications.
Considered personal data under GDPR; its collection and storage by the WiFi analytics platform requires explicit user consent.
Case Studies
A 400-bed NHS Trust is experiencing severe network congestion on its legacy patient WiFi during the hours of 6 PM to 9 PM, leading to patient complaints and staff distraction. The current setup uses a shared 500 Mbps broadband connection and Wi-Fi 4 (802.11n) access points in the corridors.
- Upgrade backhaul to a dedicated 1 Gbps symmetrical leased line to guarantee peak-hour throughput. 2. Replace corridor-based Wi-Fi 4 APs with in-room Wi-Fi 6 (802.11ax) APs to improve RF penetration and handle high device density via OFDMA. 3. Implement traffic shaping on the firewall to cap individual user bandwidth at 5 Mbps, preventing single users from monopolising the connection with 4K streaming.
A private hospital group wants to deploy a new patient WiFi network but is concerned about the DSPT compliance implications of capturing patient data on the captive portal.
Deploy a GDPR-compliant captive portal solution (like Purple) that separates authentication data from clinical data. Configure the portal to require explicit opt-in for any data processing beyond the minimum required for network access. Ensure the Patient VLAN is strictly isolated from the Clinical VLAN via the core firewall. Implement DNS-based content filtering to block malicious and inappropriate categories.
Scenario Analysis
Q1. An NHS Trust wants to implement a single SSID for both staff and patients to 'simplify the user experience'. They plan to use a captive portal to differentiate user types. Is this approach recommended?
💡 Hint:Consider the DSPT requirements for network segmentation and the risk of a compromised patient device.
Show Recommended Approach
No, this approach is highly discouraged and introduces significant security risks. Patient and clinical staff traffic must be segregated at the VLAN level with separate SSIDs. Relying solely on a captive portal for differentiation does not provide adequate Layer 2 isolation, putting clinical systems at risk from malware or lateral movement originating from untrusted patient devices.
Q2. A hospital is planning to upgrade its patient WiFi and wants to ensure adequate coverage. The IT manager suggests placing access points in the main corridors to cover the adjacent patient rooms and save on hardware costs. What is the flaw in this plan?
💡 Hint:Think about the physical construction of hospital environments and RF attenuation.
Show Recommended Approach
Corridor placement is a flawed strategy in hospitals. Hospital walls often contain lead lining (for X-ray rooms), heavy concrete, and dense infrastructure that severely attenuates RF signals. This results in poor in-room coverage, high latency, and dropped connections. Access points should be deployed inside patient rooms or wards based on a professional predictive RF survey.
Q3. A Trust has deployed patient WiFi but is receiving complaints about slow speeds during the evening. The APs are Wi-Fi 6, and the core switches are 10G capable. The internet connection is a 1 Gbps shared broadband line. What is the likely bottleneck?
💡 Hint:Differentiate between local network capacity and WAN backhaul.
Show Recommended Approach
The bottleneck is the shared broadband internet connection. Even with high-capacity local infrastructure (Wi-Fi 6 and 10G switches), a shared broadband line suffers from contention ratios, meaning the bandwidth is shared with other premises in the area. During evening peak hours, this contention severely degrades throughput. The Trust should upgrade to a dedicated, uncontended leased line.



