WiFi Guest Portal: What It Is and How to Optimise It
This authoritative guide details the architecture, implementation, and optimisation of WiFi guest portals. It provides actionable strategies for IT leaders to increase login completion rates, ensure GDPR compliance, and capture high-quality first-party data.
🎧 Listen to this Guide
View Transcript

Executive Summary
The WiFi guest portal—frequently referred to as a captive portal or splash page—is the critical intersection between network access control, user experience, and enterprise data strategy. For IT managers, network architects, and venue operations directors, deploying a guest portal is no longer simply about providing internet access. It is about architecting a secure, compliant gateway that captures high-quality first-party data while minimising user friction.
This guide provides a comprehensive technical reference on what a guest portal is, how the underlying authentication protocols function, and the precise levers available to optimise the login journey. Whether you are deploying across a retail chain, a stadium, or a global hospitality brand, the principles remain consistent: secure the network, reduce form fatigue, and integrate the captured data into downstream business systems. By moving beyond basic click-through access, organisations can transform their Guest WiFi infrastructure from a cost centre into a measurable driver of customer engagement and revenue.
Technical Deep-Dive
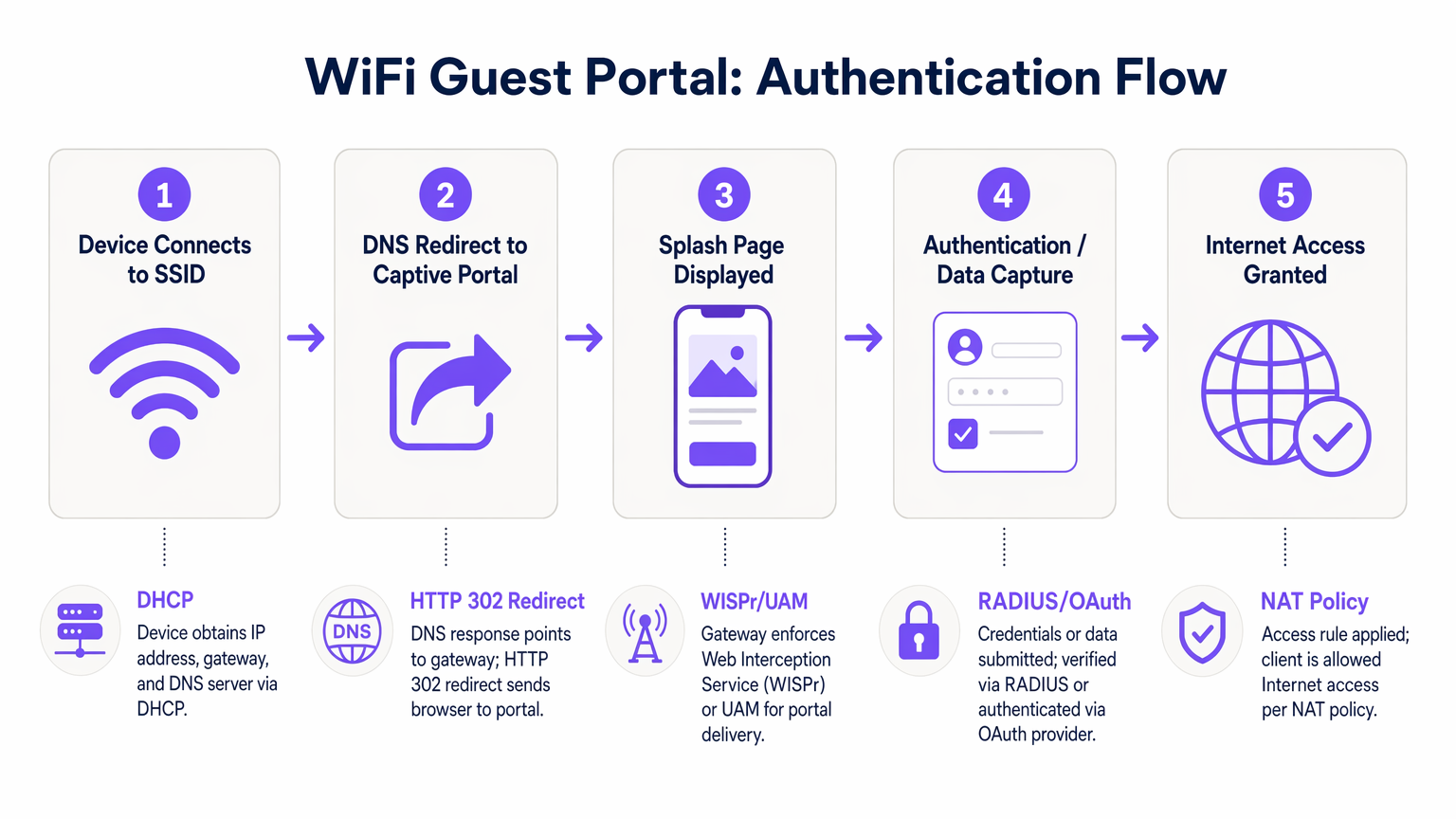
Understanding the mechanics of a guest WiFi portal requires examining the sequence of events that occur from the moment a device associates with an SSID to the point full internet access is granted. This process relies on a combination of network protocols and web redirection mechanisms.
When a client device connects to the guest network, it first negotiates an IP address, subnet mask, and default gateway via DHCP. At this stage, the device is placed in a "walled garden" state by the access controller. The walled garden is a restricted network environment where all outbound HTTP and HTTPS traffic is intercepted. The controller permits access only to explicitly whitelisted domains—such as the portal's hosting servers, authentication providers, and necessary CDN resources.
Upon the user opening a browser or the device's native Captive Network Assistant (CNA) detecting the walled garden, the controller issues an HTTP 302 redirect. This redirect points the client to the splash page URL. This interception is governed by the Wireless Internet Service Provider roaming (WISPr) protocol or the Universal Access Method (UAM).
Authentication then takes place on the splash page. The primary methods include:
- Click-Through: The user accepts terms and conditions without providing personal data.
- Form-Based Registration: The user submits details such as name and email.
- Social Login: Authentication via OAuth 2.0 using providers like Google, Facebook, or Apple.
- SMS Verification: The user receives a One-Time Passcode (OTP) via SMS to verify their identity.
Once the user successfully authenticates, the portal communicates with the access controller, typically via RADIUS (Remote Authentication Dial-In User Service) or a proprietary API. The controller then updates its NAT policies or firewall rules, transitioning the client's MAC address from the walled garden to an authorised state, granting full internet access.
Implementation Guide
Deploying a robust guest portal requires a systematic approach that prioritises security, user experience, and data integration. The following steps outline a vendor-neutral deployment methodology.
First, establish network segmentation. The guest SSID must be isolated from the corporate network using dedicated VLANs. This prevents guest devices from accessing internal resources, point-of-sale systems, or management interfaces. Implement client isolation within the guest VLAN to prevent devices from communicating with one another, mitigating the risk of lateral movement by malicious actors.
Second, configure the walled garden precisely. The most common cause of portal failure is an incomplete walled garden whitelist. Ensure that all resources required to render the splash page—including CSS files, fonts, and authentication provider endpoints (e.g., accounts.google.com)—are accessible before authentication. Failure to do so will result in broken page rendering or failed social logins.
Third, design the data model and authentication flow. Determine the minimum viable data required from the user. For most commercial deployments, an email address and explicit marketing consent are sufficient for the initial login. Implement social login options to reduce friction and improve data accuracy. When integrating with WiFi Analytics platforms, ensure that the data model aligns with your CRM's schema.
Fourth, integrate downstream systems. The value of a guest portal is fully realised when the captured data flows seamlessly into marketing automation platforms or CRM systems. Configure webhooks or API integrations to transfer profile data in real-time, enabling automated post-login engagement, such as welcome emails or loyalty programme invitations.
Best Practices
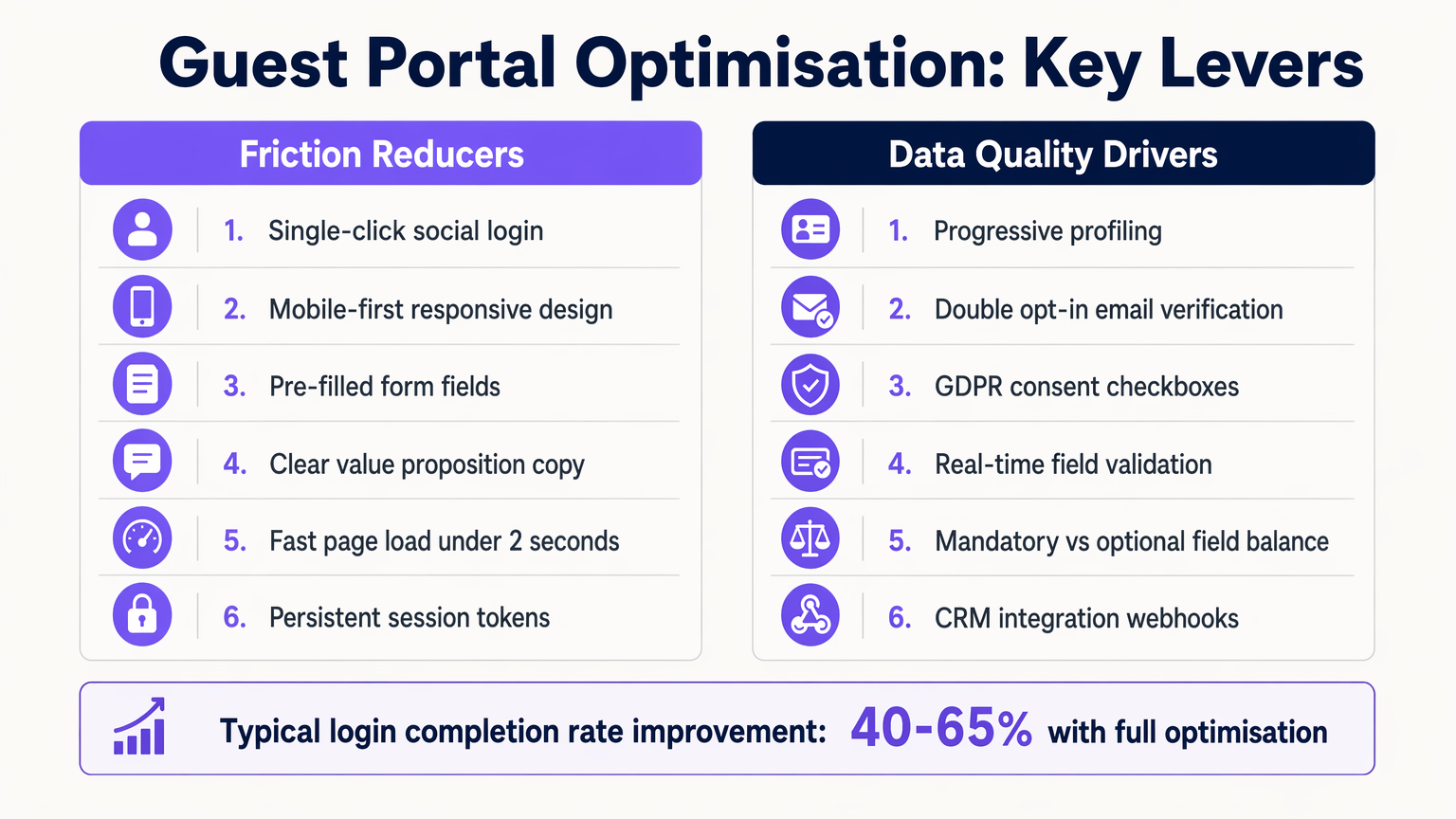
Optimising the guest portal experience is an ongoing process. Industry-standard best practices dictate a focus on speed, mobile responsiveness, and progressive profiling.
1. Mobile-First Design The vast majority of guest portal interactions occur on mobile devices. Ensure the splash page is fully responsive, with touch targets sized appropriately (minimum 44x44 pixels) and form fields that trigger the correct virtual keyboard (e.g., the email keyboard for email fields).
2. Progressive Profiling Avoid form fatigue by collecting only essential data during the first connection. On subsequent visits, use MAC address recognition or persistent session tokens to identify returning users and prompt them for additional information, such as date of birth or preferences. This approach significantly increases the overall completion rate.
3. Clear Value Exchange The copy on the splash page must clearly articulate the benefit to the user. Replace generic phrasing like "Register to access the network" with compelling value propositions such as "Enjoy high-speed WiFi—connect in seconds."
Troubleshooting & Risk Mitigation
Even well-architected deployments can encounter issues. Understanding common failure modes is essential for maintaining uptime and user satisfaction.
Captive Network Assistant (CNA) Failures
Modern operating systems use CNAs to detect captive portals automatically. If the access controller does not respond correctly to the OS's initial probe (e.g., Apple's captive.apple.com), the CNA may fail to launch, leaving the user confused. Ensure controller firmware is up-to-date and correctly handles these probes.
Session Timeout Misconfiguration Setting the session timeout too short forces users to re-authenticate frequently, degrading the experience. Conversely, setting it too long can inflate concurrent user metrics and exhaust IP address pools. A typical commercial venue should configure a session timeout of 8 to 24 hours, with returning users seamlessly authenticated via MAC caching.
Compliance Risks Under GDPR and similar frameworks, explicit consent is required for marketing communications. Pre-ticked boxes or bundled consent (e.g., combining Terms of Service with marketing opt-in) are non-compliant. Ensure the portal maintains an immutable audit log of consent records, including timestamps and the specific privacy policy version accepted.
ROI & Business Impact
The ultimate measure of a guest portal's success is its contribution to business objectives. By transitioning from a simple access mechanism to an intelligent data capture platform, organisations can drive measurable ROI.
In Retail environments, capturing email addresses allows for targeted re-marketing campaigns, driving footfall and increasing customer lifetime value. In Hospitality , integrating the portal with property management systems enables personalised guest experiences and automated TripAdvisor review requests.
The impact is quantified through metrics such as the Login Completion Rate (the percentage of users who see the portal and successfully authenticate), the Opt-In Rate (the percentage of users granting marketing consent), and the Data Quality Score (the percentage of valid, deliverable email addresses). Platforms like Purple provide the necessary analytics to track these KPIs, demonstrating the tangible value of the WiFi infrastructure.
Key Terms & Definitions
Captive Portal
A web page that the user of a public-access network is obliged to view and interact with before access is granted.
The fundamental mechanism for controlling guest access and capturing data.
Walled Garden
A restricted network environment that allows access only to explicitly permitted IP addresses or domains prior to authentication.
Critical for allowing the splash page and authentication providers to load before the user has full internet access.
WISPr
Wireless Internet Service Provider roaming. A protocol that allows users to roam between different wireless providers.
The underlying standard that enables the HTTP redirect to the captive portal.
RADIUS
Remote Authentication Dial-In User Service. A networking protocol that provides centralized Authentication, Authorization, and Accounting (AAA) management.
The backend system that verifies credentials and tells the controller to grant access.
MAC Caching
The process of storing a device's Media Access Control address after initial authentication to automatically recognize and authorize it on subsequent visits.
Essential for providing a seamless experience for returning visitors without requiring re-login.
Progressive Profiling
A method of gradually gathering information about a user across multiple interactions rather than asking for all data upfront.
Used to balance the need for detailed marketing data with the necessity of high login completion rates.
Captive Network Assistant (CNA)
A feature in modern operating systems (like iOS and Android) that automatically detects a captive portal and opens a pseudo-browser for login.
IT teams must ensure their controllers respond correctly to CNA probes to trigger the automatic popup.
VLAN Segmentation
The practice of dividing a physical network into multiple logical networks. Guest traffic is placed on a separate VLAN from corporate traffic.
A non-negotiable security requirement to protect internal enterprise systems from guest devices.
Case Studies
A 200-room hotel is experiencing a 60% drop-off rate on their guest WiFi portal. The current portal requires guests to input their First Name, Last Name, Room Number, Email Address, and Date of Birth on a single screen before granting access. How should the IT Director redesign this flow to improve completion rates?
The IT Director should implement a progressive profiling strategy. The initial login screen should be reduced to two options: 'Connect with Google/Apple' (Social Login) or a simple form requiring only 'Email Address' and an unchecked GDPR consent box. The Room Number requirement should be removed unless PMS integration is actively used for tiered bandwidth billing. The Date of Birth field should be moved to a post-login email campaign ('Tell us your birthday for a free drink at the bar'). Finally, MAC address caching should be enabled so returning guests bypass the form entirely for the duration of their stay.
A large stadium IT team is deploying a new guest portal for 50,000 concurrent users. During testing, users report that the splash page takes over 8 seconds to load, and many abandon the process. The portal features a 3MB high-resolution background image and loads three external tracking scripts. What immediate technical remediations are required?
The IT team must immediately optimize the portal payload. First, the 3MB background image must be compressed and resized, ideally replaced with a CSS-based gradient or an optimized WebP image under 200KB. Second, all non-essential third-party tracking scripts must be removed from the critical rendering path; only essential scripts should load asynchronously. Third, the team must verify the Walled Garden configuration on the access controllers to ensure the CDN hosting the portal assets is explicitly whitelisted, preventing the controller from throttling or blocking the asset delivery.
Scenario Analysis
Q1. You are designing the portal for a busy transport hub. The marketing team wants to collect Name, Email, Phone Number, and Destination. The network team is concerned about throughput and user complaints. What is the optimal approach?
💡 Hint:Consider the impact of form length on completion rates and the principle of progressive profiling.
Show Recommended Approach
Push back on the marketing team's request for all four fields upfront. Implement a portal requiring only Email Address and marketing consent, or offer Social Login. Use post-login email automation to ask for the Destination data once the user is connected and settled. This satisfies marketing's need for data over time while addressing the network team's concern about immediate throughput and user friction.
Q2. After deploying a new guest portal, users report that the splash page appears, but when they click 'Login with Facebook', the page times out and fails to authenticate. What is the most likely technical cause?
💡 Hint:Think about the network state the device is in before authentication is complete.
Show Recommended Approach
The Walled Garden whitelist is incomplete. The access controller is blocking the device from reaching Facebook's OAuth servers (e.g., graph.facebook.com) because the device is not yet authenticated. The IT team must add the necessary Facebook domains to the Walled Garden whitelist so the authentication handshake can complete.
Q3. Your organisation is updating its guest WiFi to comply with GDPR. The current portal has a single checkbox that says 'I agree to the Terms of Service and to receive marketing emails'. Why is this problematic, and how must it be fixed?
💡 Hint:Review the requirements for lawful consent under GDPR regarding 'bundling'.
Show Recommended Approach
This is non-compliant because it relies on 'bundled consent'. Under GDPR, consent for marketing must be freely given, specific, informed, and unambiguous. You cannot make access to the service (WiFi) conditional on accepting marketing. The fix is to separate this into two actions: a mandatory acceptance of the Terms of Service, and an optional, unticked checkbox for marketing consent.



