WPA3: La próxima generación de seguridad WiFi explicada
Esta guía de referencia técnica exhaustiva explica los cambios arquitectónicos introducidos por WPA3, incluyendo SAE, OWE y Forward Secrecy. Ofrece estrategias de implementación prácticas para que los gerentes de TI y los arquitectos de red actualicen de forma segura las redes empresariales y de espacios públicos.
🎧 Escuchar esta guía
Ver transcripción
- Resumen Ejecutivo
- Análisis Técnico Detallado
- Simultaneous Authentication of Equals (SAE)
- Secreto Hacia Adelante
- Opportunistic Wireless Encryption (OWE)
- WPA3-Enterprise y seguridad de 192 bits
- Guía de Implementación
- Fase 1: Evaluación y Auditoría
- Fase 2: Transición a WPA3Implementación en modo
- Fase 3: Segmentación y Aplicación
- Integración con Captive Portals
- Mejores Prácticas
- Resolución de Problemas y Mitigación de Riesgos
- Modos de Fallo Comunes
- ROI e Impacto Empresarial
- Escuche el Informe Técnico

Resumen Ejecutivo
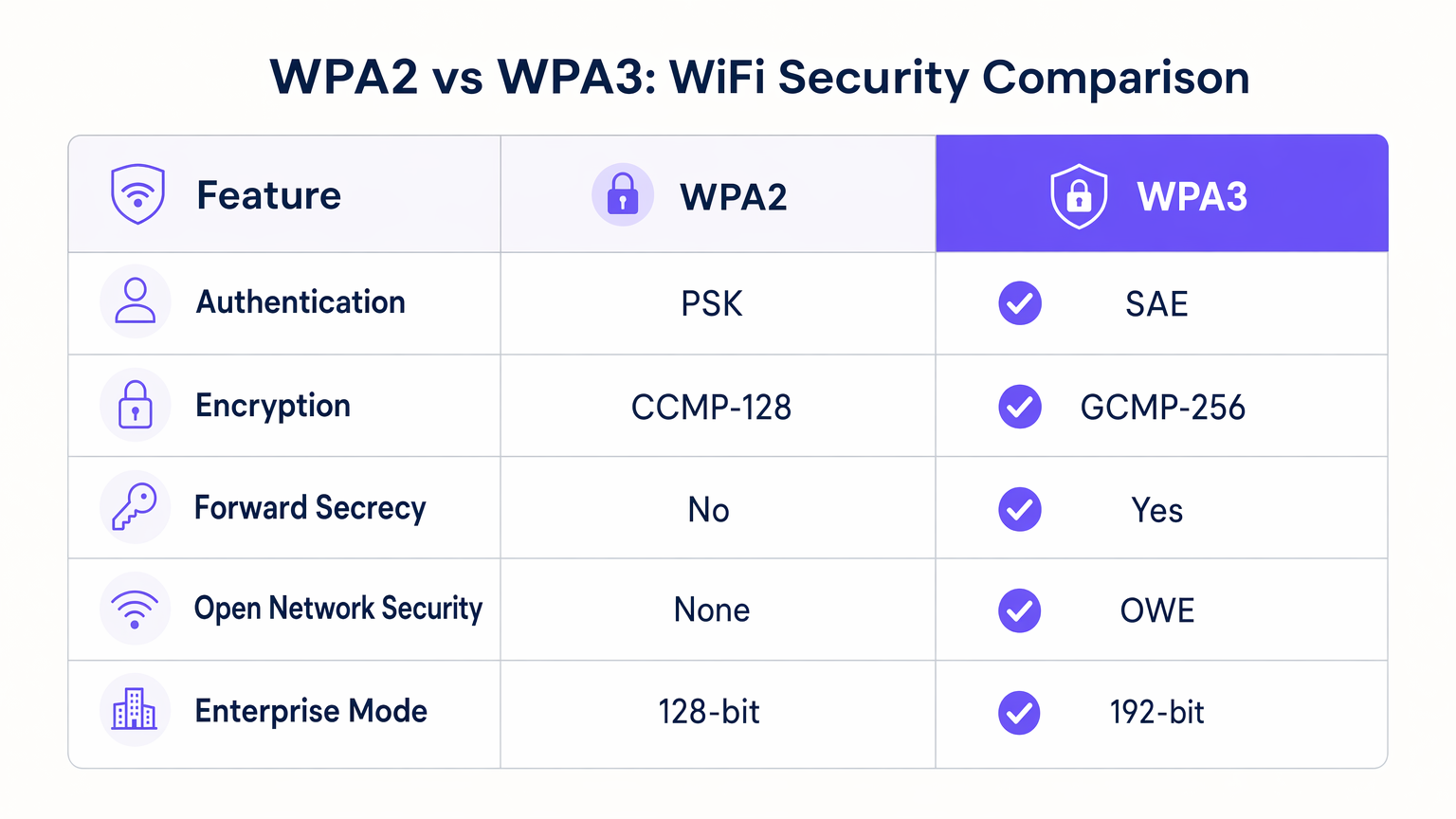
Para los gerentes de TI, arquitectos de red y directores de operaciones de recintos, la transición a WPA3 representa el cambio más significativo en la arquitectura de seguridad inalámbrica en dos décadas. Aunque WPA2 ha sido el estándar de la industria desde 2004, su dependencia de las Claves Precompartidas (PSK) y su vulnerabilidad a los ataques de diccionario offline lo hacen cada vez más inadecuado para los entornos empresariales modernos. WPA3 aborda estas fallas arquitectónicas fundamentales al tiempo que introduce nuevas capacidades críticas para los espacios públicos.
Esta guía de referencia técnica proporciona orientación práctica sobre la implementación de WPA3 en redes de hostelería, comercio minorista y sector público. Cubre los cuatro pilares fundamentales del nuevo estándar: Autenticación Simultánea de Iguales (SAE) para una autenticación robusta basada en contraseña, Cifrado Inalámbrico Oportunista (OWE) para asegurar redes abiertas, Secreto Hacia Adelante (Forward Secrecy) para proteger el tráfico histórico, y un conjunto de seguridad de 192 bits para implementaciones empresariales altamente reguladas.
Al comprender estos mecanismos, los operadores de red pueden planificar una estrategia de migración por fases que mejore la postura de seguridad sin interrumpir los dispositivos cliente heredados ni la experiencia del usuario. Fundamentalmente, esta guía relaciona estas capacidades técnicas con resultados empresariales tangibles, demostrando cómo una seguridad inalámbrica robusta se integra con las plataformas de Guest WiFi y WiFi Analytics para ofrecer experiencias de invitado seguras, conformes y ricas en datos.
Análisis Técnico Detallado
La transición de WPA2 a WPA3 no es simplemente una actualización criptográfica incremental; es un rediseño fundamental de los procesos de negociación de cifrado y de handshake de autenticación. Comprender la mecánica de estos cambios es esencial para los arquitectos que diseñan redes inalámbricas de próxima generación.
Simultaneous Authentication of Equals (SAE)
La vulnerabilidad más significativa en WPA2-Personal es el handshake de cuatro vías utilizado para establecer una conexión segura mediante una Clave Precompartida (PSK). Si un atacante captura este handshake, puede tomar los datos offline y ejecutar ataques de diccionario de fuerza bruta contra ellos indefinidamente hasta que se recupere la contraseña.
WPA3 reemplaza el mecanismo PSK con la Autenticación Simultánea de Iguales (SAE), una variante del protocolo de intercambio de claves Dragonfly. SAE utiliza un intercambio al estilo Diffie-Hellman donde tanto el cliente como el punto de acceso demuestran conocimiento de la contraseña sin transmitirla nunca por el aire, ni siquiera en formato hash. Esta prueba de conocimiento cero elimina completamente el vector para ataques de diccionario offline. Incluso si un atacante captura cada paquete del intercambio SAE, no puede derivar la clave de sesión ni la contraseña original de los datos capturados.
Secreto Hacia Adelante
Un beneficio operativo crítico de SAE es la introducción del Secreto Hacia Adelante. Bajo WPA2, si un atacante registra tráfico cifrado hoy y logra obtener la contraseña de la red mañana (por ejemplo, a través de un ataque de ingeniería social o un dispositivo de empleado comprometido), puede descifrar retroactivamente todo el tráfico grabado previamente.
El SAE de WPA3 genera una clave de cifrado efímera única para cada sesión. Debido a que las claves de sesión no se derivan matemáticamente de la contraseña maestra de forma reversible, comprometer la contraseña de la red no compromete el tráfico pasado. Para los espacios de Hostelería que manejan información sensible de los huéspedes, esto proporciona una capa significativa de mitigación de riesgos contra la escucha pasiva a largo plazo.
Opportunistic Wireless Encryption (OWE)
Para los espacios públicos, el Cifrado Inalámbrico Oportunista (OWE) — comercializado por la Wi-Fi Alliance como Wi-Fi Certified Enhanced Open — es la característica más transformadora de WPA3. Históricamente, las redes abiertas (aquellas sin contraseña) transmiten datos en texto plano, dejando a los usuarios vulnerables a la captura de paquetes y al secuestro de sesiones.
OWE negocia automáticamente una conexión cifrada entre el dispositivo cliente y el punto de acceso sin requerir autenticación de usuario ni contraseña. La experiencia del usuario sigue siendo idéntica a la de una red abierta tradicional — el usuario simplemente selecciona el SSID y se conecta — pero las tramas 802.11 subyacentes están cifradas. Esto es particularmente relevante para entornos de Comercio minorista donde se requiere una incorporación sin fricciones, pero la privacidad de los datos (y el cumplimiento del GDPR) debe mantenerse.
WPA3-Enterprise y seguridad de 192 bits
Para entornos altamente regulados, WPA3-Enterprise introduce un modo de seguridad mínimo opcional de 192 bits alineado con el conjunto de algoritmos de seguridad nacional comercial (CNSA). Este modo exige el uso de GCMP-256 (Protocolo de Modo Galois/Contador) para el cifrado y HMAC-SHA-384 para la verificación de integridad, proporcionando una protección robusta para redes financieras, gubernamentales y de Atención médica .
Guía de Implementación
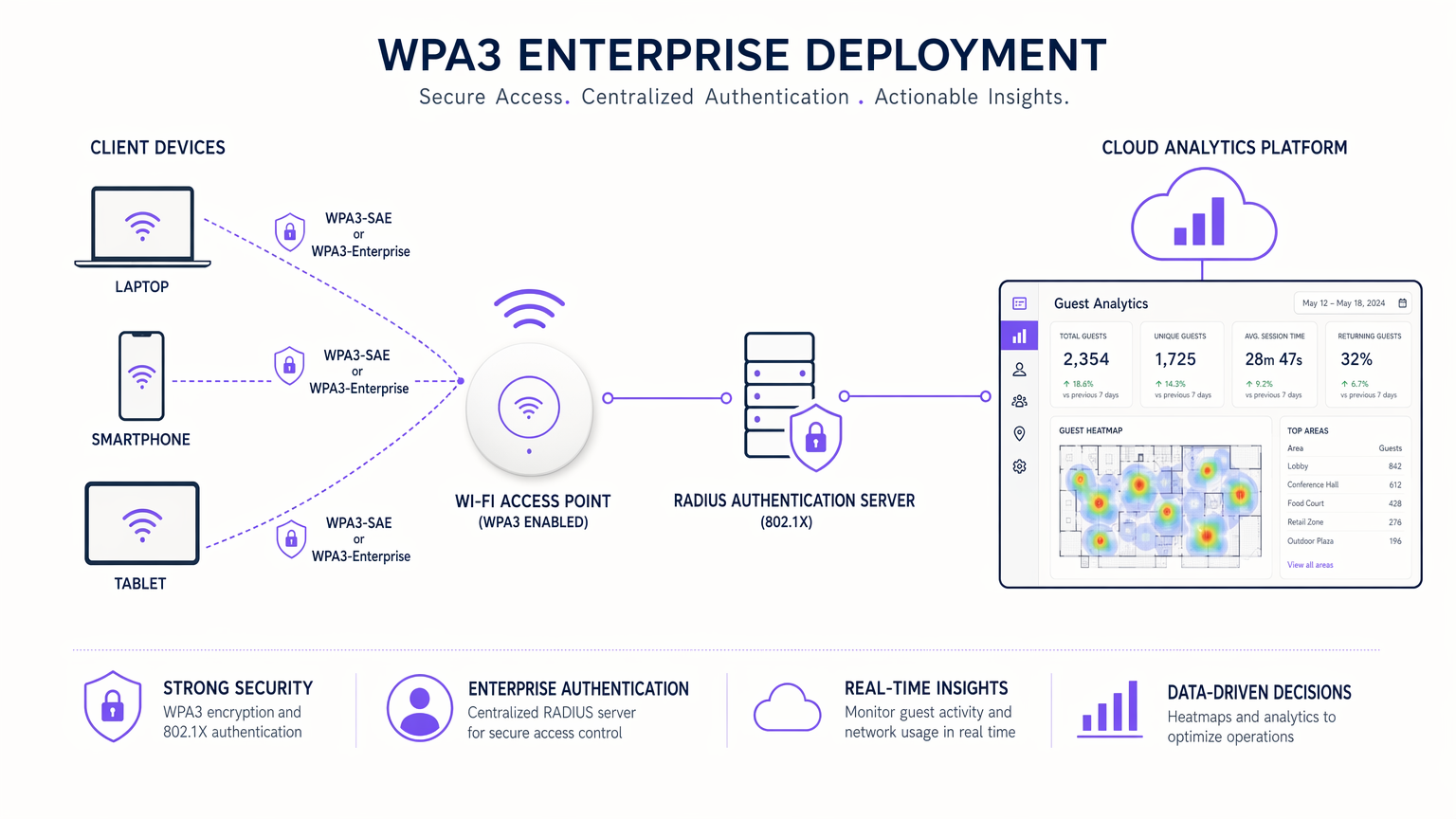
La implementación de WPA3 en un entorno empresarial requiere un enfoque por fases para acomodar los dispositivos heredados mientras se maximiza la seguridad para los clientes compatibles.
Fase 1: Evaluación y Auditoría
Comience auditando las versiones de firmware de sus puntos de acceso existentes y controladores de LAN inalámbrica. La mayoría del hardware de grado empresarial fabricado después de 2018 es compatible con WPA3 mediante actualizaciones de firmware. Simultáneamente, perfile su parque de dispositivos cliente utilizando su plataforma de gestión de red o el panel de control de WiFi Analytics para determinar el porcentaje de dispositivos compatibles con WPA3.
Fase 2: Transición a WPA3Implementación en modo
Para soportar un entorno mixto, implemente el Modo de Transición WPA3. Esto permite que un único SSID acepte conexiones WPA2 (PSK) y WPA3 (SAE).
- Configure el SSID: Habilite el Modo de Transición WPA3 en el SSID objetivo.
- Monitorice las conexiones: Utilice análisis para seguir la proporción de conexiones WPA2 a WPA3 a lo largo del tiempo.
- Identifique dispositivos heredados: Aísle los dispositivos que no se conectan o que recurren constantemente a WPA2 (por ejemplo, dispositivos IoT antiguos o terminales POS heredados).
Nota: El Modo de Transición WPA3 es susceptible a ataques de degradación en los que un adversario activo fuerza a un cliente compatible con WPA3 a conectarse utilizando WPA2. Por lo tanto, debe considerarse un paso de migración temporal, no una arquitectura permanente.
Fase 3: Segmentación y Aplicación
Una vez que el volumen de dispositivos heredados caiga por debajo de un umbral aceptable, pase a la aplicación completa de WPA3.
- Aísle el IoT heredado: Mueva los dispositivos no conformes (smart TVs, sistemas de gestión de edificios antiguos) a un SSID WPA2 dedicado y oculto en una VLAN aislada.
- Aplique solo WPA3: Deshabilite WPA2 en los SSID principales de invitados y corporativos, asegurando que todos los dispositivos compatibles se beneficien de SAE y Forward Secrecy.
Integración con Captive Portals
Al implementar OWE para redes públicas, asegúrese de que su solución de Captive Portal sea compatible. Plataformas como Purple actúan como proveedor de identidad y mecanismo de consentimiento por encima de la capa de transporte OWE cifrada. El punto de acceso gestiona el cifrado OWE, mientras que el Captive Portal administra el recorrido del usuario, la aceptación de los términos de servicio y la captura de datos.
Mejores Prácticas
- Mantenimiento del Firmware: Asegúrese de que todos los puntos de acceso ejecuten el firmware más reciente para mitigar las vulnerabilidades tempranas de WPA3, como la inundación de tramas de confirmación SAE.
- Segmentación de VLAN: Independientemente de la versión de WPA, mantenga una estricta segmentación de VLAN entre el tráfico de invitados, los datos corporativos y los dispositivos IoT. Esto es fundamental para el cumplimiento de PCI DSS.
- Evite el modo mixto en SSID de alta seguridad: Para redes corporativas críticas, omita completamente el Modo de Transición e implemente un SSID WPA3-Enterprise dedicado para prevenir ataques de degradación.
- Eduque al Helpdesk: Asegúrese de que el soporte de TI de primera línea comprenda la diferencia entre WPA2 y WPA3, particularmente en lo que respecta a la compatibilidad con dispositivos heredados y el comportamiento de OWE.
Para una perspectiva más amplia sobre la optimización de la arquitectura de red, considere leer sobre Los beneficios clave de SD WAN para empresas modernas .
Resolución de Problemas y Mitigación de Riesgos
Modos de Fallo Comunes
- Problemas de conectividad de clientes heredados: Algunos dispositivos cliente más antiguos (particularmente dispositivos Android heredados y sensores IoT baratos) pueden no conectarse a un SSID que emita el Modo de Transición WPA3, incluso si solo admiten WPA2.
- Mitigación: Mantenga un SSID dedicado solo para WPA2 para estos dispositivos específicos hasta que puedan ser dados de baja.
- Fallos de redirección de Captive Portal: En algunas implementaciones tempranas de OWE, los clientes pueden tener dificultades con la redirección del Captive Portal.
- Mitigación: Pruebe a fondo con una combinación de dispositivos iOS, Android y Windows. Asegúrese de que su plataforma de WiFi para invitados esté explícitamente validada para entornos OWE.
- Sobrecarga del Handshake SAE: En entornos de muy alta densidad (por ejemplo, estadios), la sobrecarga computacional del handshake SAE puede afectar marginalmente la utilización de la CPU del AP.
- Mitigación: Monitorice el rendimiento del AP durante la carga máxima y ajuste los umbrales de equilibrio de carga del cliente si es necesario.
ROI e Impacto Empresarial
La actualización a WPA3 no suele ser un proyecto generador de ingresos, pero es una iniciativa crítica de mitigación de riesgos y habilitación de cumplimiento.
- Reducción de Riesgos: La eliminación de ataques de diccionario offline y la implementación de Forward Secrecy reducen drásticamente el radio de impacto potencial de un compromiso de red inalámbrica, protegiendo la reputación de la marca y evitando multas regulatorias.
- Habilitación de Cumplimiento: El modo WPA3-Enterprise de 192 bits y OWE soportan directamente el cumplimiento de marcos estrictos como PCI DSS y GDPR al garantizar la confidencialidad de los datos en tránsito.
- Preparación para el Futuro: La Wi-Fi Alliance requiere WPA3 para todas las certificaciones Wi-Fi 6 (802.11ax) y Wi-Fi 6E. Migrar ahora asegura que su infraestructura esté lista para soportar la próxima generación de estándares inalámbricos de alto rendimiento.
Al combinar la seguridad robusta de WPA3 con una plataforma integral de Guest WiFi , los recintos pueden ofrecer una experiencia de conectividad segura y sin fricciones que genera confianza en el cliente al tiempo que captura los datos de primera parte necesarios para impulsar la lealtad y el compromiso. Para una comparación detallada de los estándares heredados, revise nuestra guía: WPA, WPA2 y WPA3: ¿Cuál es la diferencia y cuál debería usar? .
Escuche el Informe Técnico
Para una inmersión más profunda en las implicaciones operativas de WPA3, escuche nuestro podcast técnico de 10 minutos:
Términos clave y definiciones
WPA3 (Wi-Fi Protected Access 3)
The latest generation of Wi-Fi security certified by the Wi-Fi Alliance, introducing significant cryptographic upgrades over WPA2.
When IT teams are refreshing network hardware or updating security policies to meet modern compliance standards.
SAE (Simultaneous Authentication of Equals)
A secure key establishment protocol used in WPA3-Personal that replaces the Pre-Shared Key (PSK) method, providing resistance against offline dictionary attacks.
When configuring the authentication method for new SSIDs, ensuring robust protection against brute-force password guessing.
OWE (Opportunistic Wireless Encryption)
A standard that provides individualized data encryption for open Wi-Fi networks without requiring user authentication.
When deploying public guest WiFi in retail or hospitality environments where frictionless access must be balanced with user privacy.
Forward Secrecy
A cryptographic feature ensuring that session keys are not compromised even if the long-term master password is later discovered.
When evaluating the risk of long-term passive eavesdropping and data interception in enterprise environments.
WPA3 Transition Mode
A configuration allowing a single SSID to support both WPA2 and WPA3 clients simultaneously.
When planning a phased migration to WPA3 in an environment with a mix of modern and legacy client devices.
Downgrade Attack
A security exploit where an attacker forces a system to abandon a high-security mode of operation (like WPA3) in favor of an older, more vulnerable standard (like WPA2).
When assessing the risks of running WPA3 Transition Mode for extended periods.
CNSA (Commercial National Security Algorithm)
A suite of cryptographic algorithms promulgated by the NSA for protecting classified information, supported by WPA3-Enterprise 192-bit mode.
When designing networks for highly regulated sectors such as government, defense, or healthcare.
VLAN Segmentation
The practice of dividing a physical network into multiple logical networks to isolate traffic and improve security.
When isolating vulnerable legacy IoT devices from the primary corporate or guest networks during a WPA3 migration.
Casos de éxito
A 200-room hotel needs to upgrade its guest WiFi to WPA3 but has a significant number of legacy smart TVs in the guest rooms that only support WPA2. How should the network architect proceed?
The architect should implement a split-SSID strategy. First, create a dedicated, hidden SSID configured strictly for WPA2-Personal and assign it to an isolated VLAN with no access to the corporate network or other guest devices. Connect all legacy smart TVs to this SSID. Second, configure the primary, public-facing guest SSID to use WPA3 Transition Mode (or pure WPA3 if all guest devices are modern) and route this traffic through the Purple captive portal for authentication and analytics.
A large retail chain wants to implement frictionless WiFi for shoppers without requiring a password, but the CISO is concerned about GDPR compliance and plaintext data transmission over open networks. What is the recommended architecture?
The deployment should utilize WPA3 Opportunistic Wireless Encryption (OWE), also known as Wi-Fi Certified Enhanced Open. The access points will broadcast an open SSID, allowing shoppers to connect without a password. However, OWE will automatically negotiate unique, encrypted sessions for every client. Once connected, the traffic is routed through the Purple Guest WiFi platform to present a captive portal where users accept the terms of service and provide consent for data processing.
Análisis de escenarios
Q1. Your university campus is deploying a new wireless network for students. You want to ensure maximum security for student laptops while still allowing older gaming consoles to connect. Which deployment strategy should you choose?
💡 Sugerencia:Consider the limitations of WPA3 Transition Mode and the benefits of network segmentation.
Mostrar enfoque recomendado
Deploy two separate SSIDs. The primary student network should use WPA3-Enterprise (or WPA3-Personal) to ensure maximum security and Forward Secrecy for modern laptops and smartphones. A secondary, hidden SSID should be configured with WPA2-Personal on an isolated VLAN specifically for legacy gaming consoles. This prevents downgrade attacks on the primary network while maintaining compatibility.
Q2. A stadium IT director notices that during large events, the access points serving the main concourse are showing unusually high CPU utilization since enabling WPA3 Transition Mode. What is the likely cause?
💡 Sugerencia:Think about the cryptographic processes involved in client authentication.
Mostrar enfoque recomendado
The high CPU utilization is likely caused by the computational overhead of processing Simultaneous Authentication of Equals (SAE) handshakes in a high-density environment, combined with the mixed-mode processing of WPA2 connections. The IT director should monitor the AP performance and consider adjusting client load-balancing or upgrading AP hardware if the utilization impacts throughput.
Q3. You are configuring a public WiFi network at a busy airport. The legal department requires that user traffic be protected from passive sniffing, but the marketing department insists that users should not have to enter a password to connect. How do you satisfy both requirements?
💡 Sugerencia:Look for a WPA3 feature specifically designed for open networks.
Mostrar enfoque recomendado
Implement Opportunistic Wireless Encryption (OWE). This allows users to connect to the network without entering a password, satisfying the marketing department's requirement for frictionless access. Simultaneously, OWE automatically encrypts the data transmitted between the client and the access point, satisfying the legal department's requirement for protection against passive packet sniffing.



