How WiFi Can Enhance Patient Experience in Hospitals
This authoritative technical guide explains how hospitals can utilise enterprise guest WiFi infrastructure and analytics to measurably enhance the inpatient experience. It covers network architecture, compliance requirements (HIPAA, DSPT, GDPR), Captive Portal design, wayfinding integration, and ROI frameworks — providing IT decision-makers with the tools to build a compelling internal business case and execute a successful deployment.
🎧 Listen to this Guide
View Transcript

Executive Summary
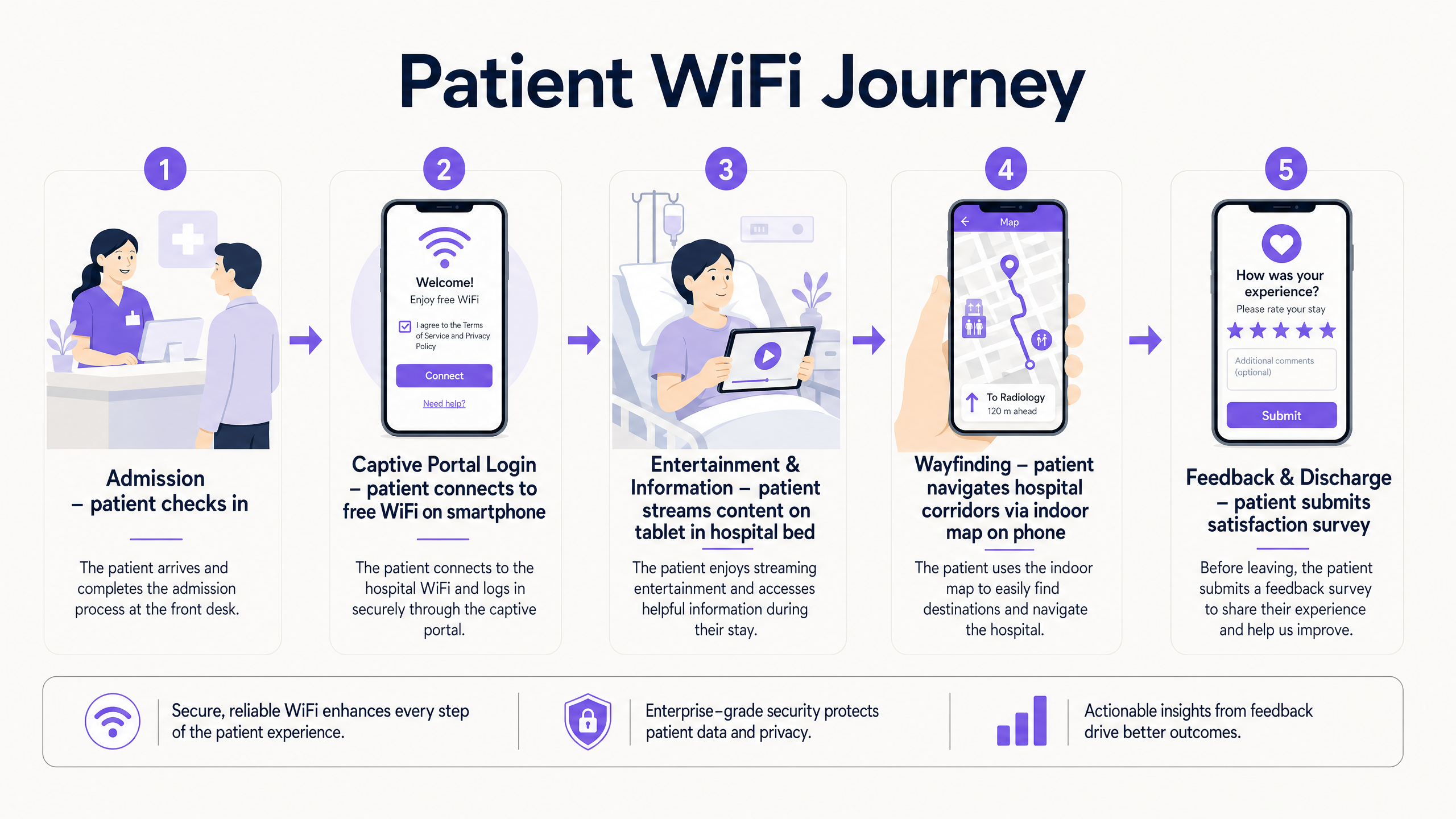
For modern healthcare facilities, free WiFi in hospitals has evolved from a basic amenity into a critical layer of patient experience and operational infrastructure. As hospitals digitise patient records, introduce telemedicine, and rely on connected medical devices, the underlying network architecture must simultaneously support clinical demands and rising patient expectations. This guide is for IT directors, network architects, and operations leaders who need to architect, deploy, and optimise a Guest WiFi solution that delivers measurable enhancements to the inpatient experience — from entertainment and wayfinding to real-time feedback collection.
The core argument is straightforward: a well-deployed patient WiFi network, integrated with a WiFi Analytics platform, transforms the network from a passive utility into an active intelligence layer. It reduces missed appointments through indoor navigation, enhances HCAHPS satisfaction scores through automated feedback, and provides operations teams with the footfall data they need to optimise staffing and resource allocation. This guide covers the architecture, compliance requirements, implementation steps, and ROI framework to make that case internally and execute it successfully.
Technical Deep-Dive
Network Architecture for Healthcare Environments
Deploying enterprise-grade Guest WiFi in a hospital requires a fundamentally different approach to a standard commercial deployment. The primary constraint is the co-existence of clinical and guest traffic on the same physical infrastructure, which demands strict logical separation. The standard architecture uses 802.1Q VLANs to segment traffic into at a minimum of three tiers: clinical systems (EHR, PACS, telemetry), staff administrative networks, and the patient/visitor guest SSID.
The guest VLAN must be routed directly to a dedicated internet uplink — ideally a separate leased line — with no routing path to clinical VLANs. Firewall ACLs should enforce this at the distribution layer, not just at the perimeter. This is a non-negotiable architectural requirement under both HIPAA and the NHS DSPT framework. For a detailed breakdown of compliance obligations, refer to Healthcare WiFi: HIPAA, DSPT and WiFi Compliance Explained .
Access Point placement in hospitals presents unique RF challenges. Lead-lined radiology suites, reinforced concrete floors between wards, and high-density patient room clusters all create attenuation profiles that differ significantly from office environments. The design target for patient areas should be a minimum RSSI of -67 dBm with at least 20 dB signal-to-noise ratio. Crucially, design for capacity, not just coverage. A ward with 30 beds may have 60-90 active devices at peak visiting hours — each potentially streaming video. AP selection should target devices supporting Wi-Fi 6 (802.11ax) or Wi-Fi 6E to handle that density efficiently.
Spectrum management is equally important. The 2.4 GHz band is heavily contended in hospital environments by legacy telemetry equipment, nurse call systems, and Bluetooth devices. Band steering should be configured to push capable devices to 5 GHz or 6 GHz bands. Automatic channel selection algorithms should be reviewed manually after deployment — they rarely produce optimal results in high-interference healthcare environments.
Captive Portal Architecture and Identity Management
The Captive Portal is the patient's first interaction with the hospital's digital services layer. It must be fast, reliable, and accessible across a wide range of devices — from the latest iPhone to a five-year-old Android tablet running a legacy browser. A poorly designed portal that fails to redirect correctly on certain devices will generate immediate complaints and support tickets.
Modern deployments move away from pre-shared keys entirely. The recommended approach is a social login or email-based Captive Portal that presents the hospital's terms of service and privacy notice, collects explicit consent for marketing communications (separately from network access consent, per GDPR Article 7), and authenticates the session. This flow, when integrated with a platform like Purple's Guest WiFi solution, simultaneously onboards the patient into a CRM-compatible data layer, enabling post-discharge communications and feedback surveys.
DNS-level security filtering should be applied to all guest traffic at the resolver level. This prevents access to known malicious domains, blocks inappropriate content categories, and provides an audit trail for compliance purposes. See Protect Your Network with Strong DNS and Security for implementation guidance on DNS filtering in guest network contexts.
WPA3-SAE (Simultaneous Authentication of Equals) should be the target encryption standard for any new SSID deployment. For legacy device compatibility, a WPA2/WPA3 transition mode is acceptable in the short term, but a migration timeline to WPA3-only should be planned. Client Isolation must be enabled on the guest SSID — this prevents device-to-device communication on the same network segment, which is critical for both security and GDPR compliance.
WiFi Analytics and Location Intelligence
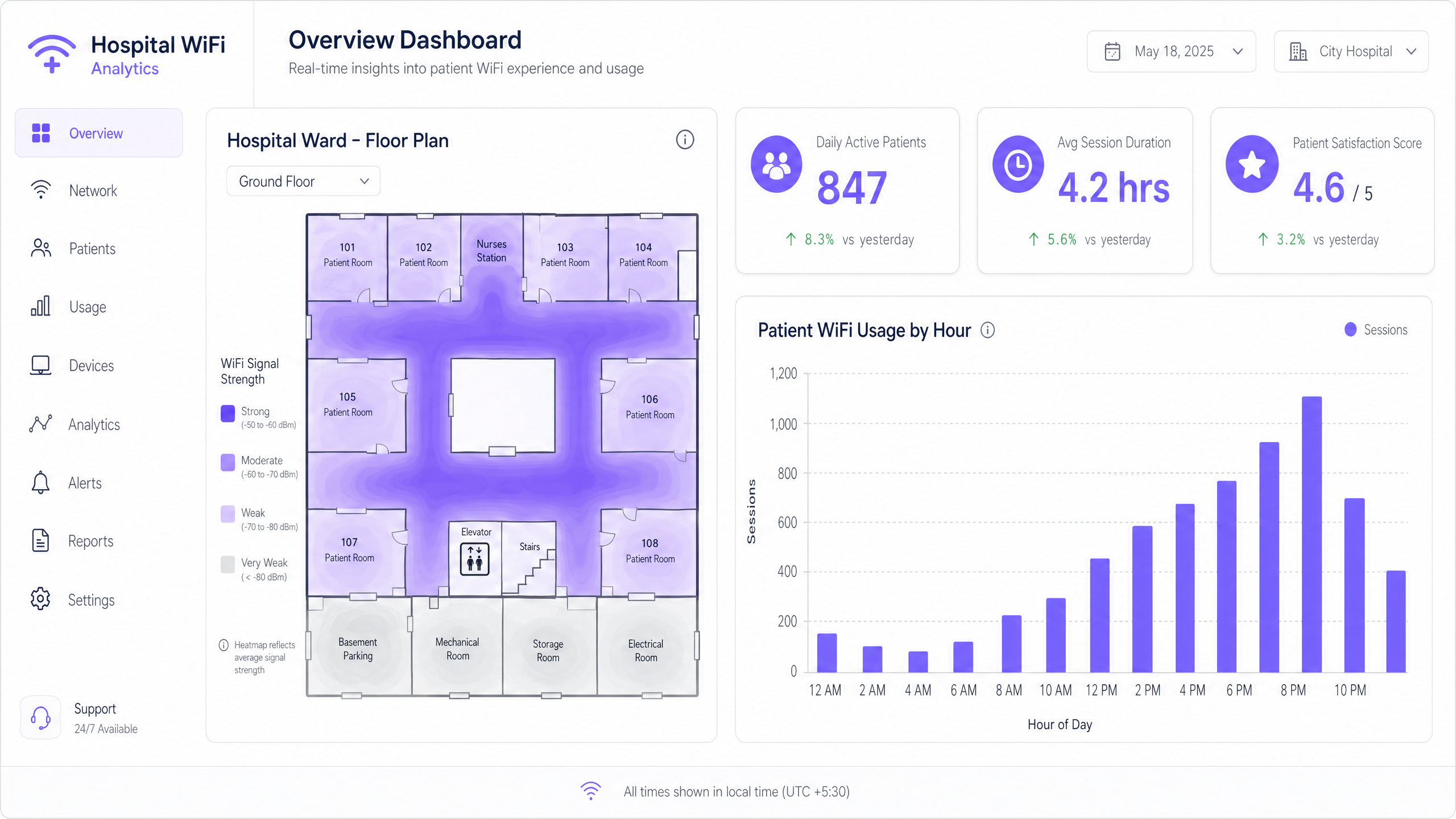
The analytics layer is where patient WiFi transitions from a cost centre to a strategic asset. A properly instrumented network, feeding data into a platform like Purple's WiFi Analytics , provides three categories of actionable intelligence.
Network Performance Monitoring delivers real-time visibility into AP health, channel utilisation, client association rates, and throughput per SSID. This enables proactive fault resolution before patients experience degraded service. Threshold-based alerting on RSSI drops or AP disassociation events is standard practice.
Footfall and Dwell Analytics work by analysing probe request data and association patterns to generate footfall heatmaps showing patient and visitor movement through the facility. This data is directly applicable to staffing decisions — if analytics show a consistent 45-minute queue build-up in the outpatient waiting area between 10:00 and 11:30, that is an operational insight with a direct staffing solution.
Feedback and Satisfaction Loops are enabled through automated post-discharge survey triggers, delivered via the email address captured at captive portal login, providing real-time HCAHPS-relevant data. Response rates for WiFi-triggered surveys consistently outperform paper-based alternatives because the contact is timely and the channel is already established.
Implementation Guide
A phased deployment approach reduces risk and allows for iterative optimisation.
Phase 1 — Discovery and Design (Weeks 1-4)
Commission a professional predictive RF design using the hospital's architectural drawings, followed by an active site survey of any existing infrastructure. Document all sources of RF interference. Define VLAN architecture, firewall policy, and internet uplink strategy. Engage the Information Governance team early to align the captive portal data collection with GDPR and DSPT requirements.
Phase 2 — Infrastructure Deployment (Weeks 5-10)
Deploy and configure switching infrastructure, ensuring PoE++ budget is sufficient for high-density APs. Install APs per the validated RF design. Configure SSIDs, VLAN tagging, and QoS policies. Implement QoS markings to prioritise voice (DSCP EF) and video (DSCP AF41) traffic over best-effort bulk data. This ensures telemedicine sessions and video calls remain stable even under network load.
Phase 3 — Captive Portal and Analytics Integration (Weeks 9-12)
Deploy and brand the captive portal. Integrate with the hospital's CRM or patient engagement platform. Configure the analytics platform with custom venue maps. Establish baseline metrics: daily active users, average session duration, peak concurrent connections, and portal completion rate. Set up automated reporting dashboards for the IT and operations teams.
Phase 4 — Wayfinding Integration (Weeks 12-16)
Integrate indoor positioning with the WiFi infrastructure. Publish the hospital's indoor map to the guest portal or a dedicated patient app. Configure points of interest (wards, departments, cafeteria, car parks). Measure wayfinding adoption rates and correlate with missed appointment data.
Best Practices
| Practice | Rationale | Standard Reference |
|---|---|---|
| Strict VLAN segmentation (clinical vs. guest) | Prevents lateral movement from compromised guest devices | HIPAA Security Rule, NHS DSPT |
| WPA3-SAE encryption | Protects against offline dictionary attacks on guest credentials | IEEE 802.11-2020 |
| Client Isolation on guest SSID | Prevents inter-device communication and data exposure | GDPR Article 25 (Privacy by Design) |
| Band Steering to 5/6 GHz | Reduces congestion and interference from legacy 2.4 GHz devices | Wi-Fi Alliance best practices |
| QoS for voice and video | Maintains call quality under network load | IEEE 802.11e / WMM |
| DNS filtering on guest traffic | Blocks malicious domains and inappropriate content | NCSC network security guidance |
| Dedicated internet uplink for guest traffic | Guarantees clinical network performance is unaffected | NHS DSPT, HIPAA |
| Automated post-discharge feedback surveys | Provides timely, actionable HCAHPS-relevant data | NHS Friends and Family Test guidance |
Troubleshooting & Risk Mitigation
RF Interference from Medical Equipment: Conduct regular spectrum analysis using a dedicated spectrum analyser tool. Legacy nurse call systems and patient monitoring equipment operating on 2.4 GHz are common culprits. The solution is typically a combination of channel reassignment and power reduction on affected APs, combined with a migration plan for the interfering equipment.
Captive Portal Redirect Failures: Modern operating systems use Captive Network Assistant (CNA) probes to detect captive portals. Ensure the portal server responds correctly to HTTP requests to known probe URLs (e.g., connectivitycheck.gstatic.com, captive.apple.com). HTTPS-only portal configurations frequently break CNA detection — maintain an HTTP redirect path even if the portal itself is served over HTTPS.
Coverage Gaps in Shielded Areas: Radiology suites, MRI rooms, and some operating theatres use RF shielding that creates complete signal blackouts. The only solution is to deploy APs inside the shielded space, connected via a penetrating cable entry point. Coordinate with the medical physics team before any cabling work in these areas.
GDPR Compliance Risk: The most common compliance failure is collecting marketing consent as part of the terms of service acceptance, rather than as a separate, explicit opt-in. This is a clear GDPR violation. Audit your captive portal flow to ensure consent for network access and consent for marketing communications are presented as separate, independent choices.
Bandwidth Contention: Without per-user bandwidth policies, a small number of heavy users can degrade the experience for everyone. Implement a per-device rate limit of 5-10 Mbps on the guest SSID. This is sufficient for HD streaming while preventing any single device from monopolising capacity.
ROI & Business Impact
The business case for investing in patient WiFi infrastructure rests on four measurable pillars.
HCAHPS Score Improvement: Patient satisfaction scores directly influence hospital reimbursement rates under value-based care models. Hospitals that have implemented automated WiFi-triggered feedback surveys report response rate improvements of 3-5x over paper-based methods, providing a statistically significant data set for quality improvement programmes.
Reduced Missed Appointments: Indoor wayfinding reduces the rate of patients arriving late or missing appointments due to navigation difficulties. A typical 500-bed hospital with 10% of outpatient appointments affected by navigation issues, at an average appointment cost of £150, represents a significant recoverable revenue opportunity.
Operational Efficiency: Footfall analytics from the WiFi network enable data-driven staffing decisions. Correlating waiting area dwell times with staffing levels allows operations managers to reduce average wait times without increasing headcount — simply by optimising shift patterns against actual demand data.
First-Party Data Asset: Every patient who connects to the guest WiFi and completes the captive portal flow represents a consented first-party data record. For a 500-bed hospital with an average length of stay of 4 days, this generates thousands of new, compliant data records per month — a valuable asset for patient engagement, health promotion communications, and service improvement research.
The Healthcare sector is increasingly recognising that the network is not just IT infrastructure — it is a patient experience platform. Organisations that treat it as such are consistently outperforming peers on satisfaction metrics and operational efficiency.
Key Terms & Definitions
Captive Portal
A web page presented to a user before they are granted access to a public WiFi network, used to display terms of service, collect authentication credentials or consent, and redirect to the internet.
The primary patient touchpoint on a hospital guest WiFi network. Design quality directly affects portal completion rates and data capture quality. Must be tested across all major mobile operating systems.
VLAN (Virtual Local Area Network)
A logical network segment created within a physical switched infrastructure using 802.1Q tagging, allowing traffic from different user groups to be isolated at Layer 2 without requiring separate physical cabling.
Essential for separating patient guest traffic from clinical EHR and administrative networks. The absence of proper VLAN segmentation is the most common network security finding in healthcare IT audits.
Band Steering
A wireless network management technique that encourages dual-band capable client devices to associate with the less congested 5 GHz or 6 GHz radio band rather than the 2.4 GHz band.
Particularly valuable in hospital environments where legacy medical equipment generates significant 2.4 GHz interference. Reduces congestion and improves throughput for streaming applications.
Client Isolation
A wireless network security feature that prevents devices associated with the same SSID from communicating directly with each other at Layer 2, forcing all traffic through the gateway.
Mandatory on healthcare guest SSIDs. Prevents malware on one patient's device from scanning or attacking other devices on the same network segment. Also has GDPR implications around data exposure.
WPA3-SAE (Simultaneous Authentication of Equals)
The authentication protocol used in WPA3-certified wireless networks, replacing the Pre-Shared Key handshake of WPA2 with a Dragonfly key exchange that is resistant to offline dictionary attacks.
The current recommended encryption standard for new SSID deployments. Protects patient credentials and session data from interception even on open or lightly secured networks.
RSSI (Received Signal Strength Indicator)
A measurement of the power level of a received radio signal, expressed in dBm (decibels relative to one milliwatt). More negative values indicate weaker signal.
Used during site surveys to validate AP placement. The target for patient areas is -67 dBm or better. Values below -75 dBm typically result in connection instability and poor streaming performance.
QoS (Quality of Service)
Network traffic management policies that classify and prioritise different types of data packets to ensure latency-sensitive applications (voice, video) receive preferential treatment over best-effort traffic.
Critical for maintaining telemedicine call quality and patient video call stability during periods of high network utilisation. Implemented using DSCP markings: EF for voice, AF41 for video.
Location Analytics
The process of deriving movement, dwell time, and footfall data from the WiFi probe requests and association events generated by mobile devices as they move through a venue.
Enables hospital operations teams to generate footfall heatmaps, identify bottlenecks in patient flow, and optimise staffing levels based on actual demand data rather than scheduled assumptions.
HCAHPS (Hospital Consumer Assessment of Healthcare Providers and Systems)
A standardised, publicly reported survey of patients' perspectives on hospital care, used to measure and compare patient experience across healthcare providers.
WiFi quality and digital service availability are increasingly correlated with HCAHPS communication and responsiveness scores. Automated WiFi-triggered surveys improve response rates and data timeliness.
DNS Filtering
A security control that intercepts DNS resolution requests and blocks queries to domains categorised as malicious, inappropriate, or policy-violating before a connection is established.
Applied at the resolver level for all guest WiFi traffic. Provides a lightweight but effective layer of protection against malware distribution, phishing, and inappropriate content access on patient networks.
Case Studies
A 500-bed regional NHS hospital is experiencing severe network congestion on their patient WiFi during evening visiting hours (18:00-20:00), leading to complaints about buffering video streams and failed video calls with family members.
- Run a spectrum analysis during peak hours to confirm whether the issue is RF congestion or backhaul saturation. 2. If RF: enable band steering to force 5 GHz-capable devices off the 2.4 GHz band; review AP channel assignments and reduce transmit power to tighten cell boundaries and reduce co-channel interference. 3. If backhaul: review the internet uplink utilisation during peak hours — if a shared connection is being saturated, implement traffic shaping to prioritise real-time traffic (DSCP EF for voice, DSCP AF41 for video) over bulk downloads. 4. Implement a per-device bandwidth cap of 8 Mbps on the guest SSID to ensure fair access. 5. Deploy additional APs in the highest-density wards if per-AP client counts exceed 30 during peak hours. 6. Review the analytics dashboard for the specific wards generating the most complaints — the problem is rarely uniform across the facility.
A private hospital group is deploying a new outpatient clinic and wants to use the guest WiFi captive portal to collect patient data for post-visit feedback surveys and marketing communications, while ensuring strict separation from the clinical network containing EHR data.
- Create a dedicated VLAN (e.g., VLAN 100) for the guest SSID, with a separate DHCP scope and no routing adjacency to clinical VLANs. 2. Route all guest traffic to a dedicated internet uplink via a separate firewall zone — do not use the same perimeter firewall that protects clinical systems. 3. Enable client isolation on the guest SSID. 4. Design the captive portal with two separate consent checkboxes: one for accepting network terms of service (required for access), and one for opting into marketing communications (optional, clearly labelled). This is a GDPR Article 7 requirement — consent for marketing must be freely given and separate from the service condition. 5. Integrate the portal with Purple's Guest WiFi platform to capture consented data into a CRM-compatible format. 6. Configure automated post-visit survey triggers to fire 24 hours after the patient's session ends. 7. Implement DNS filtering on the guest VLAN to block malicious domains.
Scenario Analysis
Q1. A hospital administrator proposes using the guest WiFi network to track the real-time location of expensive mobile medical equipment (infusion pumps, portable ECG monitors). As the IT Director, how do you respond, and what alternative do you recommend?
💡 Hint:Consider the architectural separation between guest and clinical infrastructure, and the reliability requirements for asset tracking in a clinical context.
Show Recommended Approach
I would advise against using the guest WiFi network for clinical asset tracking for two reasons. First, the guest SSID is architecturally separated from clinical systems — any asset tracking data would need to traverse a firewall boundary to reach clinical management systems, introducing unnecessary complexity and potential security risk. Second, guest WiFi location accuracy (typically 5-15 metres using RSSI triangulation) is insufficient for reliable room-level asset tracking in a clinical environment. The recommended alternative is a dedicated RTLS using active BLE tags on the equipment, with dedicated BLE readers installed in each room. This provides sub-metre accuracy, operates independently of the guest network, and integrates directly with clinical asset management systems. The BLE infrastructure can often share the same physical cabling as the WiFi APs, reducing deployment cost.
Q2. During a post-deployment audit, you discover that the hospital's captive portal presents a single checkbox that reads: 'I accept the terms of service and agree to receive communications from the hospital.' What is the compliance risk, and what is the remediation?
💡 Hint:Consider GDPR Article 7 requirements for valid consent, specifically the conditions under which consent is considered freely given.
Show Recommended Approach
This is a clear GDPR Article 7 violation. Consent for marketing communications must be freely given, which means it cannot be bundled with consent for network access as a condition of service. The remediation is to split the captive portal into two distinct consent mechanisms: (1) a mandatory acceptance of the network terms of service (required for access), and (2) a separate, optional opt-in checkbox for marketing communications, clearly labelled and unchecked by default. Any existing records captured under the bundled consent should be reviewed with the DPO — they may need to be treated as non-consented for marketing purposes until re-consent is obtained.
Q3. A new 200-bed oncology wing is being added to an existing hospital. The project manager asks whether the existing guest WiFi infrastructure can simply be extended to cover the new wing. What questions do you ask before making a recommendation?
💡 Hint:Think about capacity planning, backhaul, and the specific RF challenges of a new building structure before assuming the existing infrastructure can scale.
Show Recommended Approach
Before making any recommendation, I would ask: (1) What is the current utilisation of the existing backhaul uplink during peak hours? If it is already above 70%, adding 200 beds will cause contention. (2) What is the construction specification of the new wing — specifically, are there any lead-lined rooms or reinforced concrete floors that will require APs inside shielded spaces? (3) What is the per-AP client count on the existing infrastructure during peak hours? If existing APs are already handling 40+ clients, the existing AP hardware may not be sufficient even with additional units. (4) Is the existing switching infrastructure PoE++ capable, or will new switches be required? (5) Has a predictive RF design been run against the new wing's architectural drawings? I would not recommend simply extending the existing infrastructure without a formal capacity assessment and predictive design.



