PIPEDA Compliance for Guest WiFi in Canada
This guide provides a definitive technical and operational reference for Canadian venue operators deploying guest WiFi under PIPEDA. It covers the OPC's meaningful consent framework, the accountability principle, enforcement precedents from the Tim Hortons and Google WiFi investigations, and the architectural changes required to meet the incoming Consumer Privacy Protection Act (CPPA) under Bill C-27. IT managers and compliance leads will find actionable captive portal design specifications, data minimisation requirements, and a clear roadmap for future-proofing against GDPR-scale penalties.
🎧 Listen to this Guide
View Transcript
- Executive Summary
- Technical Deep-Dive: PIPEDA and the Captive Portal
- The Meaningful Consent Mandate
- The Tim Hortons Precedent: A Warning for Location Analytics
- Implementation Guide: Building a Compliant Onboarding Flow
- Step 1: Data Minimisation at the Edge
- Step 2: Layered Captive Portal UI Architecture
- Step 3: API Integration and Data Residency
- Step 4: Bilingual Compliance
- Step 5: Privacy Management Programme
- Best Practices and Future-Proofing for Bill C-27 (CPPA)
- Troubleshooting and Risk Mitigation
- ROI and Business Impact
- References

Executive Summary
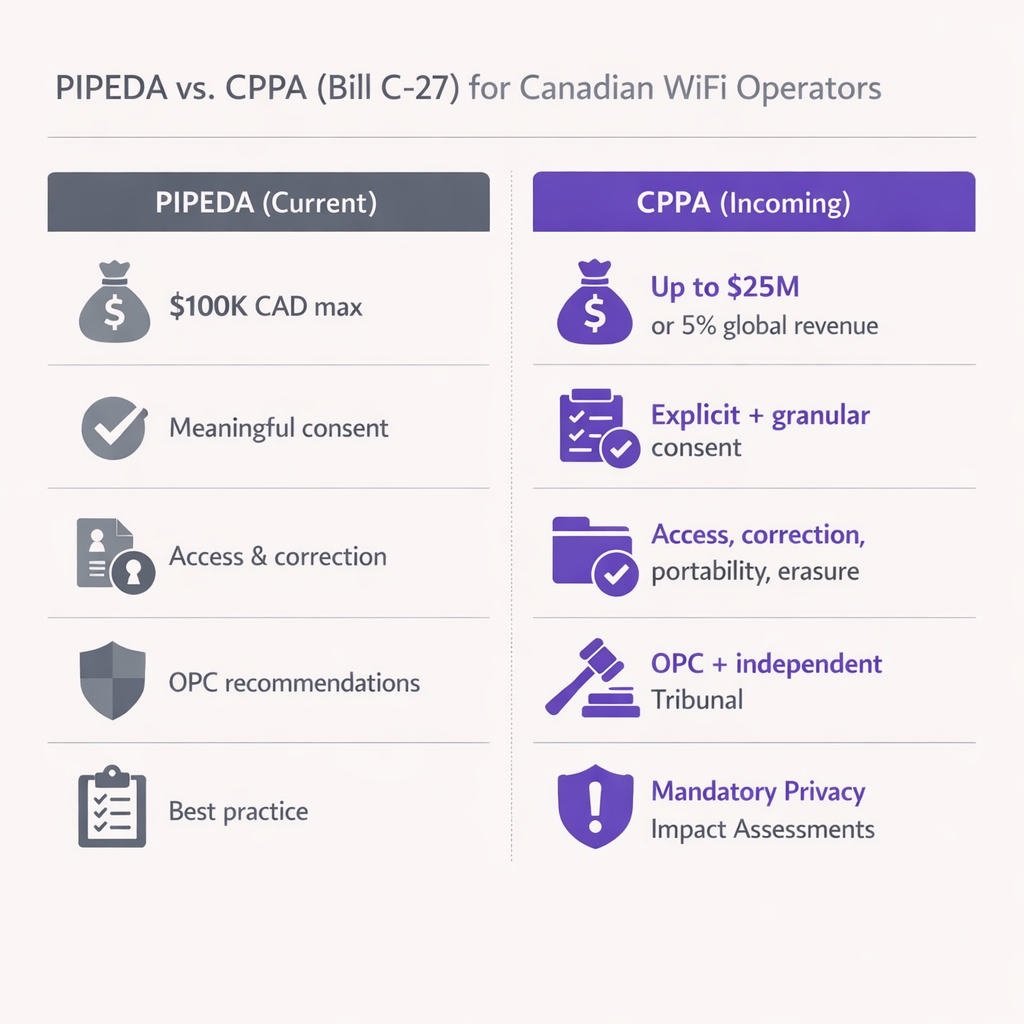
For Canadian venue operators and IT leaders, offering guest WiFi is no longer just a connectivity play — it is a critical data acquisition channel. However, the regulatory landscape governing how that data is collected and used is tightening. The Personal Information Protection and Electronic Documents Act (PIPEDA) mandates strict requirements for obtaining "meaningful consent" before collecting user data at captive portals. Furthermore, with the incoming Consumer Privacy Protection Act (CPPA) poised to introduce GDPR-style penalties (up to $25M CAD or 5% of global revenue), compliance is now a board-level risk management priority.
This guide provides a technical and operational roadmap for architects and IT managers deploying Guest WiFi solutions in Canada. We break down the Office of the Privacy Commissioner's (OPC) enforcement posture, technical requirements for layered consent, and actionable steps to future-proof your network architecture against upcoming legislative changes. Whether you operate in Retail , Hospitality , or Transport , this document translates legal obligations into concrete technical specifications.
Technical Deep-Dive: PIPEDA and the Captive Portal
PIPEDA applies to the collection, use, and disclosure of personal information in the course of commercial activities in Canada. For a WiFi captive portal, "personal information" extends beyond names and email addresses; it includes device MAC addresses, location analytics, and browsing behaviour. The Act is structured around ten Fair Information Principles enshrined in Schedule 1, of which Principle 3 (Consent), Principle 2 (Identifying Purposes), Principle 4 (Limiting Collection), and Principle 1 (Accountability) are most directly relevant to guest WiFi deployments.
The Meaningful Consent Mandate
The OPC's Guidelines for Obtaining Meaningful Consent, issued jointly with the provincial commissioners of Alberta and British Columbia in 2018, fundamentally changed how venues must design their onboarding flows. Burying data collection practices in a 5,000-word Terms and Conditions document is explicitly non-compliant. The guidelines establish seven principles, of which three are architecturally critical for captive portal design.
First, emphasis on key elements: the splash page must prominently display what data is being collected, with whom it is shared, the purposes of collection, and any meaningful residual risks of harm. Vague language such as "service improvement" is insufficient — purposes must be specific and distinguishable between those integral to service delivery and those that are optional.
Second, granular choice: users must be able to opt-in or opt-out of secondary uses (marketing, behavioural profiling, analytics) independently of the primary service (WiFi access). Bundling marketing consent as a condition of network access violates PIPEDA Principle 3 directly, as it requires consent beyond what is necessary to provide the service.
Third, dynamic transparency: consent is not a one-time event. If you update your WiFi Analytics engine to track new metrics or share data with a new third party, you must notify existing users and obtain fresh consent for the new purpose before the change takes effect.
The Tim Hortons Precedent: A Warning for Location Analytics
In 2022, the OPC's joint investigation into the Tim Hortons mobile app (PIPEDA Findings #2022-001) established a landmark precedent for location tracking that every venue IT team must understand. The investigation found that the app collected granular GPS data even when the application was closed — more than 2,700 times in under five months for one user — purportedly for targeted advertising, a purpose it never actually fulfilled. The OPC ruled this collection lacked a "legitimate need" and that the consent obtained was misleading, as users were told data was only collected while the app was open.
For venue IT teams deploying an Indoor Positioning System: UWB, BLE, & WiFi Guide , the lesson is clear: you cannot over-collect location data "just in case." If your access points probe for unassociated MAC addresses to generate footfall heatmaps, you must anonymise this data at the edge using rotating cryptographic hashes, or obtain explicit consent before the user even associates with the SSID. The OPC will assess whether your stated purpose matches your actual use, and whether the volume of data collected is proportionate to the benefit gained.
Implementation Guide: Building a Compliant Onboarding Flow
Deploying a PIPEDA-compliant captive portal requires coordination between network engineering, legal, and marketing. The following blueprint applies to any venue deploying Guest WiFi in Canada.
Step 1: Data Minimisation at the Edge
Configure your WLAN controllers to drop unnecessary payload data. As established in the 2011 Google Street View investigation (PIPEDA Findings #2011-001), capturing payload data from unencrypted networks violates PIPEDA. Ensure your RADIUS servers and captive portal gateways only log the attributes required for session management and explicitly consented analytics. For MAC address-based presence analytics, implement a rotating hash function at the AP or controller level so that the raw MAC address is never written to persistent storage.
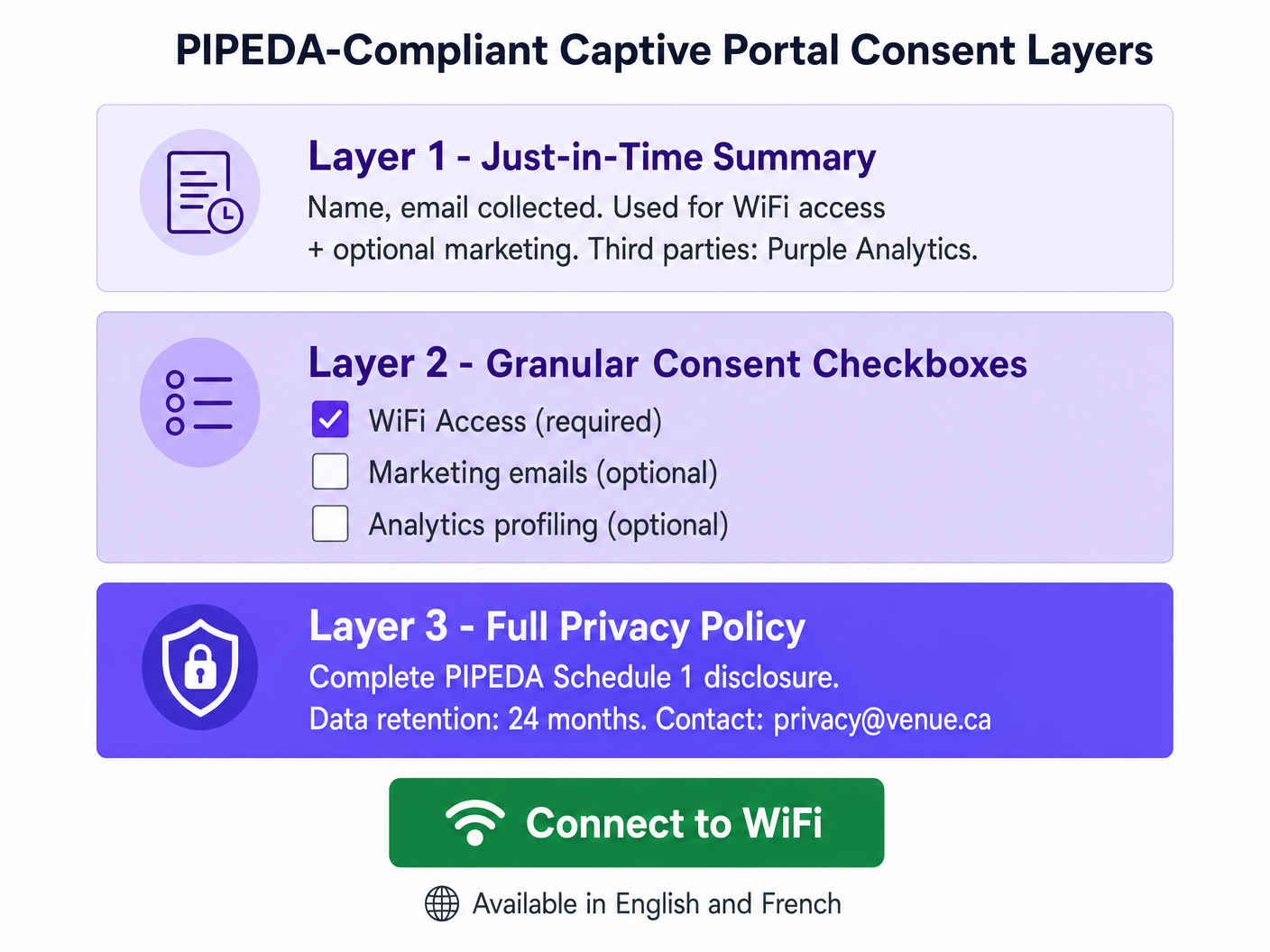
Step 2: Layered Captive Portal UI Architecture
Design the splash page using a three-layer approach aligned with the OPC's layered notice guidance. Layer 1 (the splash screen) presents a clear, plain-language summary: what data is collected, who processes it, and for what purposes. Layer 2 presents granular consent checkboxes — unchecked by default for all optional purposes — covering marketing communications, behavioural analytics, and any third-party data sharing beyond what is required for service delivery. Layer 3 provides a hyperlink to the full privacy policy, hosted on a secure, responsive page accessible from any device. If your marketing team needs help writing concise, legally sound summaries, consider using Generative AI for Captive Portal Copy and Creative or, for French-language deployments, IA générative pour le texte et les créatifs de Captive Portal .
Step 3: API Integration and Data Residency
When integrating your captive portal with a CRM or marketing automation platform, ensure data flows via secure, encrypted APIs (TLS 1.2 minimum, TLS 1.3 preferred). For Canadian deployments, prioritise vendors that offer local data residency (e.g., AWS Canada Central, ca-central-1) to mitigate cross-border transfer risks. This is especially critical for venues operating in Quebec under Law 25, which requires a Privacy Impact Assessment (PIA) before transferring personal information outside Quebec and mandates that the receiving jurisdiction offers equivalent protection.
Step 4: Bilingual Compliance
All consent notices, privacy policies, and data subject rights information must be available in both English and French for venues operating in Quebec. This is a requirement under both Law 25 and Quebec's Charter of the French Language. For federal venues (airports, rail stations, federal buildings), bilingual delivery is a baseline expectation under the Official Languages Act.
Step 5: Privacy Management Programme
PIPEDA's Accountability Principle (Principle 1) requires that your organisation designate a Privacy Officer, maintain documented policies and procedures, and be able to demonstrate compliance to the OPC on request. For multi-site operators — such as a national retail chain with 50+ locations each running a captive portal — this means a centralised Privacy Management Programme (PMP) that covers all sites consistently, with audit trails for consent events, data subject requests, and retention schedules.
Best Practices and Future-Proofing for Bill C-27 (CPPA)
While Bill C-27 — the Consumer Privacy Protection Act — stalled due to the prorogation of Parliament in January 2025, its core principles represent the inevitable future of Canadian privacy law. As of early 2026, a new federal privacy bill incorporating many CPPA provisions is expected to be introduced in Parliament. The prudent approach is to treat CPPA-level controls as your implementation target today.
The most significant changes to prepare for are as follows. Penalty escalation is the most immediate concern: the CPPA would introduce fines of up to $25M CAD or 5% of global annual revenue, a step-change from PIPEDA's current $100K maximum. Mandatory Privacy Impact Assessments will be required for high-risk processing activities, including location analytics, behavioural profiling, and any processing involving sensitive personal information. Explicit data portability and erasure rights will require automated workflows capable of purging a user's record from all systems — local database, cloud controller, downstream CRMs — within a defined response window. De-identification standards will become more prescriptive; ensure your analytics platform hashes MAC addresses using rotating salts and that re-identification is technically infeasible.
For healthcare venue operators, the intersection of WiFi analytics and patient data creates additional obligations under PIPEDA and provincial health privacy legislation. See our Healthcare industry guidance for sector-specific deployment considerations.
Troubleshooting and Risk Mitigation
Failure Mode: The All-or-Nothing Portal. Many legacy captive portal deployments present a single "I Accept" button that bundles WiFi access, marketing consent, and analytics profiling into one click. This is a direct PIPEDA violation and the most common failure mode the OPC encounters in complaints. The mitigation is straightforward: decouple network authentication from marketing opt-ins using separate, clearly labelled checkboxes. Network access should be grantable without any secondary consent.
Failure Mode: Silent MAC Tracking. Some deployments log the MAC addresses of devices that walk past the venue but never connect to the SSID, using this data to generate footfall analytics. Under PIPEDA, this constitutes collecting personal information without knowledge or consent. The mitigation is to implement MAC randomisation support at the AP level and ensure all presence analytics dashboards aggregate and anonymise data before storage. Raw MAC addresses of unassociated devices must never be written to persistent storage.
Failure Mode: Stale Consent. A venue deploys a compliant captive portal, then six months later adds a new analytics integration that sends session data to a third-party advertising platform. Existing users who consented to the original terms have not consented to this new disclosure. This violates PIPEDA's requirement to obtain consent before any new purpose. The mitigation is to implement a consent versioning system that triggers a re-consent prompt for existing users when material changes are made to data processing activities.
Failure Mode: Inadequate Third-Party Contracts. As highlighted in the Tim Hortons investigation, vague contractual language with third-party service providers — permitting them to use data for their own purposes — does not constitute adequate protection. Ensure all data processing agreements with analytics vendors, CRM providers, and marketing platforms include explicit restrictions on secondary use, data retention limits, and sub-processor controls.
ROI and Business Impact
Compliance is not a cost centre — it is a trust multiplier with measurable commercial outcomes. Venues that implement transparent, user-centric consent flows consistently report higher opt-in rates for marketing programmes because users feel in control of their data. A well-designed, PIPEDA-compliant captive portal that clearly explains the value exchange — free WiFi in return for an email address and optional marketing consent — converts at significantly higher rates than a portal that buries consent in legalese.
From a risk mitigation standpoint, the financial calculus is straightforward. A single OPC enforcement action, even under PIPEDA's current $100K maximum, generates significant reputational damage and legal costs that far exceed the investment in a compliant deployment. Under the incoming CPPA regime, the financial exposure scales to enterprise-threatening levels. Standardising on an enterprise-grade platform like Purple, which provides centralised consent management, audit trails, and automated data subject request workflows, reduces the operational overhead of managing privacy compliance across a multi-site estate and provides the documented evidence trail the OPC expects to see.
For transport operators considering connected vehicle and in-transit WiFi deployments, the same PIPEDA principles apply. See our guide on Your Guide to Enterprise In Car Wi Fi Solutions for deployment-specific considerations.
References
[1] Office of the Privacy Commissioner of Canada. "The Personal Information Protection and Electronic Documents Act (PIPEDA)." priv.gc.ca.
[2] Office of the Privacy Commissioner of Canada. "Guidelines for obtaining meaningful consent." priv.gc.ca, May 2018.
[3] Office of the Privacy Commissioner of Canada. "PIPEDA Fair Information Principles — Schedule 1." priv.gc.ca.
[4] Office of the Privacy Commissioner of Canada. "Joint investigation into location tracking by the Tim Hortons App (PIPEDA Findings #2022-001)." priv.gc.ca, June 2022.
[5] Office of the Privacy Commissioner of Canada. "Report of Findings: Google Inc. WiFi Data Collection (PIPEDA Findings #2011-001)." priv.gc.ca, 2011.
[6] Commission d'accès à l'information du Québec. "Law 25: Act to modernise legislative provisions as regards the protection of personal information." cai.gouv.qc.ca.
[7] IAPP. "What 2026 may bring for Canada's privacy reform efforts." iapp.org, February 2026.
Key Terms & Definitions
PIPEDA (Personal Information Protection and Electronic Documents Act)
Canada's federal private-sector privacy law governing the collection, use, and disclosure of personal information in commercial activities. Structured around ten Fair Information Principles in Schedule 1. Applies to all provinces except Alberta, British Columbia, and Quebec, which have substantially similar provincial legislation.
The primary compliance framework for any Canadian venue offering guest WiFi. IT teams encounter PIPEDA when designing captive portals, configuring analytics platforms, and responding to data subject requests.
Meaningful Consent
The OPC's standard for valid consent under PIPEDA, requiring that individuals genuinely understand what they are consenting to — specifically: what data is collected, who receives it, the purposes of collection, and any meaningful risks of harm. Consent buried in lengthy T&Cs, or obtained through a single bundled 'I Accept' button, does not meet this standard.
The central compliance requirement for captive portal design. Every element of the splash page UI must be evaluated against this standard.
Captive Portal
A network gateway that intercepts HTTP/HTTPS traffic from newly associated WiFi clients and redirects them to a web page for authentication, consent collection, and/or payment before granting internet access. Technically implemented via WLAN controller redirect rules, DNS spoofing, or a dedicated gateway appliance.
The primary point of consent collection for guest WiFi deployments. The design of the captive portal UI directly determines PIPEDA compliance status.
MAC Address (Media Access Control Address)
A 48-bit hardware identifier assigned to a network interface controller, used to uniquely identify a device at the data link layer (Layer 2). Under PIPEDA, MAC addresses are personal information because they can be used to identify an individual's device and, by extension, their movements and behaviour.
Encountered in WiFi analytics deployments, probe-based footfall counting, and session logging. Must be anonymised or handled with explicit consent.
OPC (Office of the Privacy Commissioner of Canada)
The independent federal authority responsible for overseeing compliance with PIPEDA and the Privacy Act. The OPC investigates complaints, conducts audits, publishes guidance, and can apply to the Federal Court to enforce its recommendations. Current maximum fine under PIPEDA is $100,000 CAD per violation.
The primary regulatory body IT teams must satisfy. OPC findings are publicly published and serve as binding precedents for compliance interpretation.
CPPA (Consumer Privacy Protection Act)
The proposed replacement for PIPEDA, introduced as part of Bill C-27 in 2022. Would introduce GDPR-scale penalties (up to $25M CAD or 5% of global revenue), mandatory Privacy Impact Assessments, explicit data portability and erasure rights, and a new independent enforcement tribunal. Bill C-27 stalled due to parliamentary prorogation in January 2025; a successor bill is anticipated in 2026.
The future compliance target for Canadian venue operators. IT teams should begin implementing CPPA-level controls now to avoid costly remediation when the legislation passes.
Law 25 (Quebec Act to Modernize Legislative Provisions as Regards the Protection of Personal Information)
Quebec's provincial privacy legislation, which imposes requirements that exceed PIPEDA. Key provisions include mandatory Privacy Impact Assessments before new projects involving personal information, explicit consent for cross-border data transfers, French-language consent notices, and fines up to $25M CAD or 10% of worldwide turnover. Fully in force as of September 2023.
Applies to all venues operating in Quebec. IT teams must implement enhanced consent flows, bilingual notices, and PIAs for any Quebec deployment.
Privacy Impact Assessment (PIA)
A structured risk assessment process that evaluates the privacy implications of a new project, system, or data processing activity before deployment. Identifies data flows, assesses risks to individuals, and documents mitigation measures. Currently a best practice under PIPEDA; mandatory under Quebec's Law 25 for new projects involving personal information; expected to become mandatory federally under the CPPA.
Required before deploying new analytics features, location tracking systems, or third-party data integrations. Provides the documented evidence trail the OPC expects to see in an enforcement scenario.
Layered Notice
A consent architecture that presents privacy information at multiple levels of detail: a brief, prominent summary for the average user; granular options for those who want more control; and a full privacy policy for those who want complete information. Recommended by the OPC as the preferred method for obtaining meaningful consent in digital environments.
The architectural pattern that all PIPEDA-compliant captive portals should implement. Directly addresses the OPC's concern that information buried in lengthy T&Cs is functionally invisible to users.
Accountability Principle (PIPEDA Schedule 1, Principle 1)
The requirement that an organisation is responsible for personal information under its control and must designate an individual (a Privacy Officer) accountable for compliance. Includes implementing policies and practices, training staff, and being able to demonstrate compliance to the OPC on request.
The organisational governance requirement that underpins all other PIPEDA compliance activities. Multi-site venue operators must have a documented Privacy Management Programme covering all locations.
Case Studies
A 300-room hotel in Toronto wants to offer free guest WiFi and use sign-up data to drive repeat bookings and promotional email campaigns. The hotel's current captive portal uses a single 'I Accept' button that links to a 4,000-word Terms and Conditions document. The IT director has been asked to assess compliance risk and redesign the flow before the next OPC audit cycle.
The existing single-button flow is non-compliant and must be replaced with a three-layer architecture. On the WLAN controller (e.g., Cisco Catalyst Centre or Aruba Central), configure the captive portal redirect to the new splash page hosted over HTTPS. Layer 1 of the splash page presents a plain-language summary panel: 'We collect your name, email address, and device identifier to provide WiFi access. We share this data with Purple (our WiFi analytics provider). You can optionally receive promotional emails from us.' Layer 2 presents two checkboxes: Checkbox A (pre-checked, mandatory): 'I agree to the WiFi Terms of Use and Privacy Policy.' Checkbox B (unchecked, optional): 'I would like to receive promotional offers and news from [Hotel Name].' Layer 3 provides a hyperlink 'Full Privacy Policy' opening the complete PIPEDA-compliant policy in a new tab. The policy must specify: data categories collected (name, email, MAC address, session timestamps), purposes (WiFi access delivery; marketing if opted-in), third parties (Purple, email marketing platform), retention period (12 months for marketing, 90 days for session logs), and a privacy contact email. The hotel must also configure its CRM integration to tag records with consent status, so that only users who checked Checkbox B receive marketing communications. Implement a consent versioning system so that if the hotel adds a new analytics partner in future, existing users are prompted to re-consent.
A large shopping centre operator in Montreal wants to deploy a WiFi analytics system to generate zone-level footfall heatmaps across 120,000 square feet of retail space. The proposed system uses WiFi probe requests from unassociated devices (i.e., phones that have not connected to the network) to estimate visitor counts and dwell times. The CTO wants to understand the PIPEDA and Law 25 compliance requirements before procurement.
This deployment involves processing personal information (MAC addresses are personal information under PIPEDA) without the knowledge or consent of the individuals whose devices are being probed. Under both PIPEDA and Quebec's Law 25, this requires careful architectural controls. The compliant approach is as follows: First, conduct a Privacy Impact Assessment (PIA) before procurement, as required by Law 25 for any new project involving personal information. The PIA must assess the necessity and proportionality of the data collection. Second, implement MAC address anonymisation at the access point or controller level using a rotating cryptographic hash (e.g., HMAC-SHA256 with a key that rotates every 24 hours). This ensures that the same device cannot be tracked across days, and that the raw MAC address is never written to persistent storage. Third, configure the analytics platform to store and display only aggregate, zone-level counts — not individual device trajectories. The dashboard should show 'Zone A: 450 visitors, avg dwell 8 minutes' rather than individual movement paths. Fourth, post clear, visible signage at all venue entrances disclosing that WiFi-based analytics are in use for footfall measurement, with a QR code linking to the full privacy notice. This satisfies the 'openness' principle and provides constructive notice. Fifth, for the connected WiFi network (the SSID guests can join), implement a standard three-layer captive portal as described in the hotel scenario above. The Law 25 requirement for French-language consent notices applies to all captive portal text.
A national retail chain with 85 stores across Canada is preparing for the incoming CPPA regime. Their current PIPEDA compliance is adequate, but the CTO wants to understand what architectural changes are needed to meet CPPA-level requirements, particularly around data subject rights, de-identification, and the increased penalty exposure.
The transition from PIPEDA to CPPA compliance requires three primary architectural investments. First, implement automated data subject rights workflows. The CPPA introduces explicit rights to data portability and erasure. The chain's WiFi platform must expose an API endpoint that, when triggered by a verified data subject request, can: (a) export all personal data associated with a given email address or device identifier in a machine-readable format (JSON or CSV); and (b) purge that record from the local captive portal database, the cloud analytics platform, and all downstream CRM and marketing automation systems simultaneously. This must be achievable within a defined SLA — 30 days is the CPPA's proposed response window. Second, upgrade de-identification protocols. Current PIPEDA guidance on de-identified data is relatively permissive. The CPPA will introduce a higher bar: de-identified data must be processed in a manner that makes re-identification 'not reasonably foreseeable.' For MAC-based analytics, this means implementing rotating hash keys (as described above) and ensuring that the analytics platform cannot be used to re-identify individuals even by the operator. Third, conduct mandatory Privacy Impact Assessments for all high-risk processing activities. For a retail chain, this includes any deployment involving location analytics, behavioural profiling for targeted advertising, or data sharing with advertising technology platforms. PIAs should be documented and retained as evidence of accountability. The chain should also review all third-party data processing agreements and update them to include CPPA-compliant clauses covering data retention, sub-processor restrictions, and breach notification timelines.
Scenario Analysis
Q1. Your venue's current captive portal collects name, email, and device MAC address. The splash page has a single 'Connect to WiFi' button that, when clicked, is deemed acceptance of the Terms and Conditions (which include consent to receive marketing emails). A user complains to the OPC. What specific PIPEDA violations has your venue committed, and what is the minimum remediation required?
💡 Hint:Consider PIPEDA Principles 1, 2, 3, and 4. Focus on the bundling of consent and the adequacy of the notice provided.
Show Recommended Approach
The venue has committed at least three violations. First, under Principle 3 (Consent), the bundling of marketing consent with WiFi access is non-compliant — users cannot be required to consent to marketing as a condition of receiving the service. Second, under Principle 2 (Identifying Purposes), the purposes are not clearly identified at the point of collection; the user must read the full T&Cs to discover the marketing purpose. Third, the consent is not 'meaningful' under the OPC's 2018 guidelines because key elements (what data, why, who gets it) are not prominently displayed. Minimum remediation: redesign the portal with a three-layer architecture, decouple marketing consent into a separate unchecked checkbox, and add a plain-language summary to the splash page. The venue must also implement a consent versioning system and update its Privacy Management Programme documentation.
Q2. You are the IT director of a conference centre in Vancouver. A vendor proposes deploying a WiFi analytics system that tracks the MAC addresses of all devices in the venue — including those that never connect to the WiFi network — to generate session-level movement analytics for exhibitors. The vendor says the data is 'de-identified' because they hash the MAC addresses. Is this deployment compliant with PIPEDA? What additional controls, if any, are required?
💡 Hint:Consider whether hashing alone constitutes de-identification under PIPEDA. Think about the difference between a static hash and a rotating hash, and the concept of re-identification risk.
Show Recommended Approach
The deployment is potentially compliant but requires additional controls. A static hash of a MAC address is not true de-identification under PIPEDA because the same device will always produce the same hash, allowing cross-session tracking and, potentially, re-identification if the hash table is compromised or if the MAC address is known. To achieve genuine de-identification, the hash key must rotate at regular intervals (e.g., every 24 hours), ensuring that the same device cannot be tracked across sessions. Additionally, the venue must post clear, visible signage at all entrances disclosing that WiFi-based analytics are in use, satisfying the Openness principle. The analytics platform must store and display only aggregate, zone-level data — not individual device trajectories. If the vendor intends to share session-level data with exhibitors (third parties), this constitutes a disclosure of personal information and requires explicit consent from users who have connected to the network, or robust anonymisation that makes re-identification 'not reasonably foreseeable.' A Privacy Impact Assessment is strongly recommended before deployment.
Q3. A hotel chain with properties in Ontario, Alberta, and Quebec is standardising its guest WiFi platform. The CTO wants a single consent flow that works across all provinces. The legal team has flagged that Quebec's Law 25 imposes additional requirements. Design the minimum viable consent architecture that satisfies PIPEDA in Ontario and Alberta, Law 25 in Quebec, and is forward-compatible with the incoming CPPA.
💡 Hint:Identify the highest common denominator across all three regimes. Consider language, PIA requirements, consent granularity, and data subject rights.
Show Recommended Approach
The minimum viable architecture should be designed to the highest standard across all applicable regimes, which means treating Law 25 as the baseline. The consent flow must: (1) Present a bilingual (English and French) splash page with a plain-language just-in-time summary; (2) Provide separate, unchecked-by-default checkboxes for WiFi access terms, marketing consent, and analytics profiling; (3) Link to a full privacy policy available in both languages, specifying data categories, purposes, third parties, retention periods, and data subject rights contact; (4) Support data subject rights for access, correction, and deletion — with automated workflows capable of purging records across all systems within 30 days; (5) Implement rotating-hash MAC anonymisation at the edge. Before deploying the system in Quebec, conduct a Privacy Impact Assessment as required by Law 25. For CPPA forward-compatibility, ensure the platform supports data portability export in machine-readable format and can generate audit trails of all consent events. This single architecture satisfies PIPEDA in Ontario and Alberta, Law 25 in Quebec, and is well-positioned for CPPA compliance when the legislation passes.
Q4. Six months after deploying a compliant captive portal, your marketing team wants to add a new integration that sends guest session data (email, visit frequency, dwell time) to a third-party programmatic advertising platform for retargeting campaigns. Existing users consented to the original terms, which did not mention this platform. What are your obligations under PIPEDA before activating this integration?
💡 Hint:Focus on the 'new purpose' requirement under PIPEDA and the OPC's guidance on dynamic consent. Consider what constitutes a 'significant change' to privacy practices.
Show Recommended Approach
Under PIPEDA, sharing personal information with a third-party advertising platform for retargeting constitutes a new purpose that was not anticipated in the original consent. Before activating the integration, you must: (1) Update your privacy policy to disclose the new third party and the retargeting purpose; (2) Notify all existing users of the material change to your privacy practices — this can be done via email to those who provided their address during WiFi sign-up; (3) Obtain fresh consent from existing users for the new purpose before their data is shared with the advertising platform — this means presenting them with a new opt-in opportunity, not assuming their original consent covers the new use; (4) Ensure that users who do not consent to the new purpose continue to receive WiFi access without interruption; (5) Review the data processing agreement with the advertising platform to ensure it includes adequate protections against secondary use by the platform. Failing to obtain fresh consent before activating the integration would constitute a disclosure of personal information for a purpose beyond what was originally consented to — a direct violation of PIPEDA Principle 3.



