Conformité à la PIPEDA pour le WiFi invité au Canada
Ce guide fournit une référence technique et opérationnelle définitive pour les opérateurs de sites canadiens déployant le WiFi invité conformément à la PIPEDA. Il couvre le cadre de consentement significatif de l'OPC, le principe de responsabilité, les précédents d'application issus des enquêtes Tim Hortons et Google WiFi, et les changements architecturaux requis pour se conformer à la future Loi sur la protection de la vie privée des consommateurs (CPPA) en vertu du projet de loi C-27. Les responsables informatiques et de la conformité y trouveront des spécifications concrètes pour la conception de captive portals, les exigences de minimisation des données, et une feuille de route claire pour se prémunir contre les pénalités de l'ampleur du GDPR.
🎧 Écouter ce guide
Voir la transcription
- Résumé Exécutif
- Plongée Technique : La PIPEDA et le Captive Portal
- Le Mandat de Consentement Significatif
- Le Précédent Tim Hortons : Un Avertissement pour l'Analyse de Localisation
- Guide d'Implémentation : Construire un Parcours d'Intégration Conforme
- Étape 1 : Minimisation des Données en Périphérie
- Étape 2 : Architecture de l'interface utilisateur du Captive Portal en couches
- Étape 3 : Intégration API et Résidence des Données
- Étape 4 : Conformité Bilingue
- Étape 5 : Programme de Gestion de la Confidentialité
- Bonnes Pratiques et Préparation à l'avenir pour le Projet de Loi C-27 (CPPA)
- Dépannage et Atténuation des Risques
- ROI et impact commercial
- Références

Résumé Exécutif
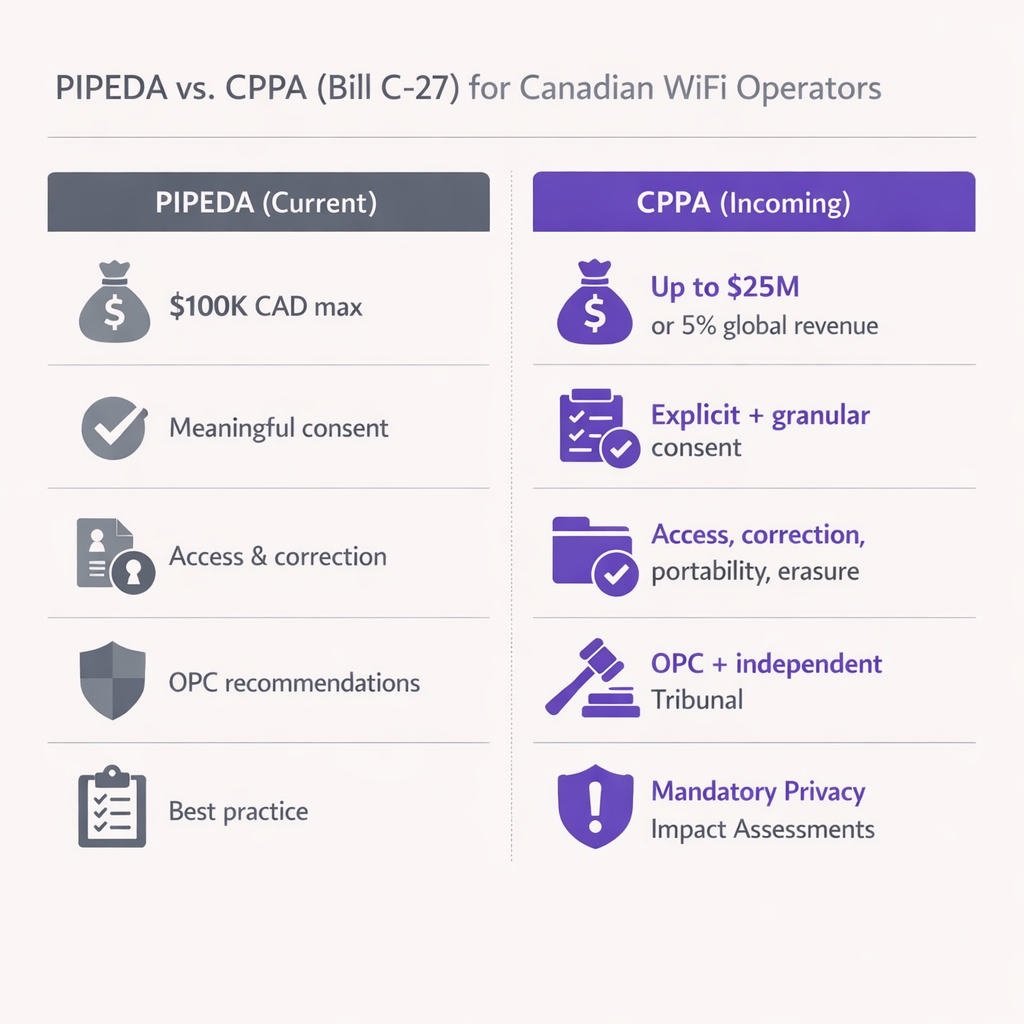
Pour les opérateurs de sites canadiens et les leaders informatiques, offrir le WiFi invité n'est plus seulement une question de connectivité — c'est un canal d'acquisition de données essentiel. Cependant, le cadre réglementaire régissant la collecte et l'utilisation de ces données se durcit. La Loi sur la protection des renseignements personnels et les documents électroniques (PIPEDA) impose des exigences strictes pour l'obtention d'un "consentement significatif" avant de collecter les données des utilisateurs sur les captive portals. De plus, avec la future Loi sur la protection de la vie privée des consommateurs (CPPA) qui s'apprête à introduire des pénalités de type GDPR (jusqu'à 25 millions de dollars canadiens ou 5 % du chiffre d'affaires mondial), la conformité est désormais une priorité de gestion des risques au niveau du conseil d'administration.
Ce guide fournit une feuille de route technique et opérationnelle pour les architectes et les responsables informatiques déployant des solutions de WiFi invité au Canada. Nous détaillons la position d'application du Commissariat à la protection de la vie privée (OPC), les exigences techniques pour le consentement échelonné, et les étapes concrètes pour pérenniser votre architecture réseau face aux changements législatifs à venir. Que vous opériez dans le Commerce de détail , l' Hôtellerie , ou le Transport , ce document traduit les obligations légales en spécifications techniques concrètes.
Plongée Technique : La PIPEDA et le Captive Portal
La PIPEDA s'applique à la collecte, à l'utilisation et à la divulgation de renseignements personnels dans le cadre d'activités commerciales au Canada. Pour un captive portal WiFi, les "renseignements personnels" vont au-delà des noms et adresses e-mail ; ils incluent les adresses MAC des appareils, les analyses de localisation et le comportement de navigation. La Loi est structurée autour de dix principes d'équité en matière d'information énoncés à l'annexe 1, dont le Principe 3 (Consentement), le Principe 2 (Détermination des fins), le Principe 4 (Limitation de la collecte) et le Principe 1 (Responsabilité) sont les plus directement pertinents pour les déploiements de WiFi invité.
Le Mandat de Consentement Significatif
Les Lignes directrices de l'OPC pour l'obtention d'un consentement significatif, publiées conjointement avec les commissaires provinciaux de l'Alberta et de la Colombie-Britannique en 2018, ont fondamentalement modifié la manière dont les sites doivent concevoir leurs parcours d'intégration. Dissimuler les pratiques de collecte de données dans un document de 5 000 mots de Termes et Conditions est explicitement non conforme. Les lignes directrices établissent sept principes, dont trois sont architecturalement critiques pour la conception des captive portals.
Premièrement, l'accent sur les éléments clés : la page d'accueil doit afficher de manière proéminente quelles données sont collectées, avec qui elles sont partagées, les finalités de la collecte et tout risque résiduel significatif de préjudice. Un langage vague tel que "amélioration du service" est insuffisant — les finalités doivent être spécifiques et distinguables entre celles qui sont intégrales à la prestation de service et celles qui sont optionnelles.
Deuxièmement, choix granulaire : les utilisateurs doivent pouvoir accepter ou refuser les utilisations secondaires (marketing, profilage comportemental, analytics) indépendamment du service principal (accès WiFi). Lier le consentement marketing à la condition d'accès au réseau viole directement le Principe 3 de la PIPEDA, car cela exige un consentement au-delà de ce qui est nécessaire pour fournir le service.
Troisièmement, transparence dynamique : le consentement n'est pas un événement unique. Si vous mettez à jour votre moteur de WiFi Analytics pour suivre de nouvelles métriques ou partager des données avec un nouveau tiers, vous devez en informer les utilisateurs existants et obtenir un nouveau consentement pour la nouvelle finalité avant que le changement ne prenne effet.
Le Précédent Tim Hortons : Un Avertissement pour l'Analyse de Localisation
En 2022, l'enquête conjointe de l'OPC sur l'application mobile Tim Hortons (Conclusions PIPEDA #2022-001) a établi un précédent marquant pour le suivi de localisation que chaque équipe informatique de site doit comprendre. L'enquête a révélé que l'application collectait des données GPS granulaires même lorsque l'application était fermée — plus de 2 700 fois en moins de cinq mois pour un utilisateur — prétendument pour de la publicité ciblée, une finalité qu'elle n'a jamais réellement remplie. L'OPC a jugé que cette collecte manquait de "besoin légitime" et que le consentement obtenu était trompeur, car les utilisateurs avaient été informés que les données n'étaient collectées que lorsque l'application était ouverte.
Pour les équipes informatiques de sites déployant un Système de Positionnement Intérieur : Guide UWB, BLE, & WiFi , la leçon est claire : vous ne pouvez pas sur-collecter des données de localisation "juste au cas où". Si vos points d'accès sondent les adresses MAC non associées pour générer des cartes thermiques de fréquentation, vous devez anonymiser ces données en périphérie en utilisant des hachages cryptographiques rotatifs, ou obtenir un consentement explicite avant même que l'utilisateur ne s'associe au SSID. L'OPC évaluera si votre finalité déclarée correspond à votre utilisation réelle, et si le volume de données collectées est proportionné au bénéfice obtenu.
Guide d'Implémentation : Construire un Parcours d'Intégration Conforme
Le déploiement d'un captive portal conforme à la PIPEDA nécessite une coordination entre l'ingénierie réseau, le service juridique et le marketing. Le plan suivant s'applique à tout site déployant du WiFi invité au Canada.
Étape 1 : Minimisation des Données en Périphérie
Configurez vos contrôleurs WLAN pour qu'ils suppriment les données de charge utile inutiles. Comme établi dans l'enquête Google Street View de 2011 (Conclusions PIPEDA #2011-001), la capture de données de charge utile provenant de réseaux non chiffrés viole la PIPEDA. Assurez-vous que vos serveurs RADIUS et vos passerelles de captive portal n'enregistrent que les attributs requis pour la gestion de session et les analytics explicitement consentis. Pour les analytics de présence basés sur les adresses MAC, implémentez une fonction de hachage rotativen au niveau du point d'accès ou du contrôleur afin que l'adresse MAC brute ne soit jamais écrite dans un stockage persistant.
Étape 2 : Architecture de l'interface utilisateur du Captive Portal en couches
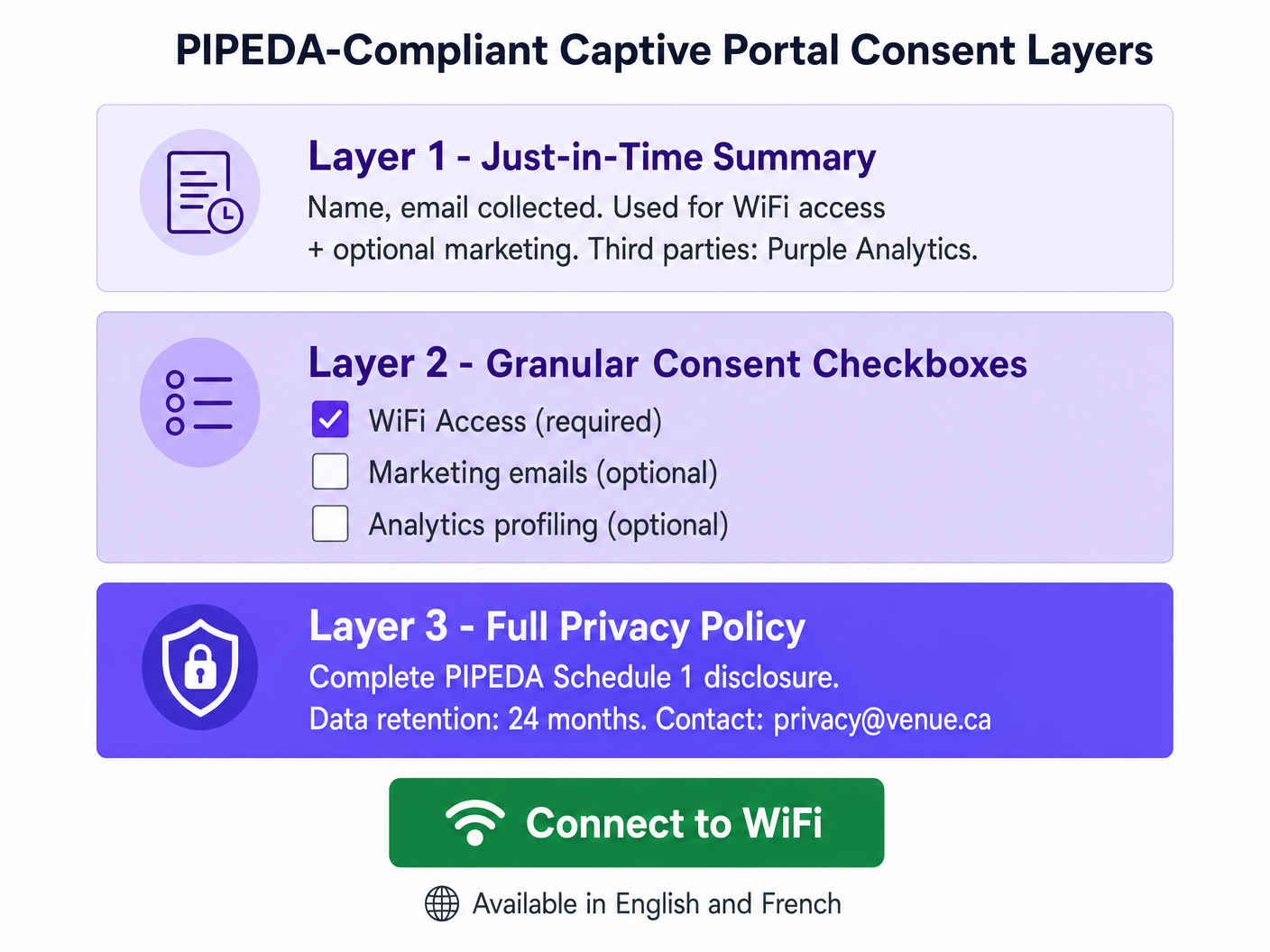
Concevez la page d'accueil en utilisant une approche à trois couches alignée sur les directives de l'OPC en matière d'avis en couches. La couche 1 (l'écran d'accueil) présente un résumé clair et en langage simple : quelles données sont collectées, qui les traite et à quelles fins. La couche 2 présente des cases à cocher de consentement granulaire — décochées par défaut pour toutes les finalités facultatives — couvrant les communications marketing, l'analyse comportementale et tout partage de données avec des tiers au-delà de ce qui est requis pour la prestation de services. La couche 3 fournit un hyperlien vers la politique de confidentialité complète, hébergée sur une page sécurisée et réactive, accessible depuis n'importe quel appareil. Si votre équipe marketing a besoin d'aide pour rédiger des résumés concis et juridiquement solides, envisagez d'utiliser Generative AI for Captive Portal Copy and Creative ou, pour les déploiements en français, IA générative pour le texte et les créatifs de Captive Portal .
Étape 3 : Intégration API et Résidence des Données
Lors de l'intégration de votre captive portal avec un CRM ou une plateforme d'automatisation marketing, assurez-vous que les données transitent via des API sécurisées et chiffrées (TLS 1.2 minimum, TLS 1.3 préféré). Pour les déploiements canadiens, privilégiez les fournisseurs qui offrent une résidence des données locale (par exemple, AWS Canada Central, ca-central-1) afin d'atténuer les risques de transfert transfrontalier. Ceci est particulièrement critique pour les établissements opérant au Québec en vertu de la Loi 25, qui exige une évaluation des facteurs relatifs à la vie privée (EFVP) avant de transférer des renseignements personnels à l'extérieur du Québec et impose que la juridiction de réception offre une protection équivalente.
Étape 4 : Conformité Bilingue
Tous les avis de consentement, les politiques de confidentialité et les informations sur les droits des personnes concernées doivent être disponibles en anglais et en français pour les établissements opérant au Québec. Il s'agit d'une exigence en vertu de la Loi 25 et de la Charte de la langue française du Québec. Pour les établissements fédéraux (aéroports, gares ferroviaires, bâtiments fédéraux), la prestation bilingue est une attente de base en vertu de la Loi sur les langues officielles.
Étape 5 : Programme de Gestion de la Confidentialité
Le Principe de Responsabilité de la LPRPDE (Principe 1) exige que votre organisation désigne un responsable de la protection de la vie privée, maintienne des politiques et procédures documentées, et soit en mesure de démontrer sa conformité à l'OPC sur demande. Pour les opérateurs multisites — tels qu'une chaîne de magasins nationale avec plus de 50 emplacements, chacun gérant un captive portal — cela signifie un Programme de Gestion de la Confidentialité (PGC) centralisé qui couvre tous les sites de manière cohérente, avec des pistes d'audit pour les événements de consentement, les demandes des personnes concernées et les calendriers de conservation.
Bonnes Pratiques et Préparation à l'avenir pour le Projet de Loi C-27 (CPPA)
Bien que le projet de loi C-27 — la Loi sur la protection des renseignements personnels des consommateurs — ait été bloqué en raison de la prorogation du Parlement en janvier 2025, ses principes fondamentaux représentent l'avenir inévitable du droit canadien de la protection de la vie privée. Début 2026, un nouveau projet de loi fédéral sur la protection de la vie privée intégrant de nombreuses dispositions de la CPPA devrait être présenté au Parlement. L'approche prudente consiste à considérer les contrôles de niveau CPPA comme votre objectif de mise en œuvre dès aujourd'hui.
Les changements les plus importants à préparer sont les suivants. L'escalade des pénalités est la préoccupation la plus immédiate : la CPPA introduirait des amendes pouvant atteindre 25 millions de dollars canadiens ou 5 % du chiffre d'affaires annuel mondial, un changement radical par rapport au maximum actuel de 100 000 dollars de la LPRPDE. Des évaluations obligatoires des facteurs relatifs à la vie privée seront requises pour les activités de traitement à haut risque, y compris l'analyse de localisation, le profilage comportemental et tout traitement impliquant des renseignements personnels sensibles. Des droits explicites à la portabilité et à l'effacement des données nécessiteront des flux de travail automatisés capables de purger l'enregistrement d'un utilisateur de tous les systèmes — base de données locale, contrôleur cloud, CRM en aval — dans un délai de réponse défini. Les normes de désidentification deviendront plus prescriptives ; assurez-vous que votre plateforme d'analyse hache les adresses MAC à l'aide de sels rotatifs et que la réidentification est techniquement infaisable.
Pour les opérateurs d'établissements de santé, l'intersection de l'analyse WiFi et des données des patients crée des obligations supplémentaires en vertu de la LPRPDE et de la législation provinciale sur la protection de la vie privée en matière de santé. Consultez nos directives sectorielles Santé pour les considérations de déploiement spécifiques au secteur.
Dépannage et Atténuation des Risques
Mode de défaillance : Le portail tout-ou-rien. De nombreux déploiements de captive portal hérités présentent un seul "J'accepte" bouton qui regroupe l'accès WiFi, le consentement marketing et le profilage analytique en un seul clic. Il s'agit d'une violation directe de la LPRPDE et du mode de défaillance le plus courant que l'OPC rencontre dans les plaintes. L'atténuation est simple : dissociez l'authentification réseau des opt-ins marketing à l'aide de cases à cocher séparées et clairement étiquetées. L'accès au réseau doit être accordable sans aucun consentement secondaire.
Mode de défaillance : Suivi MAC silencieux. Certains déploiements enregistrent les adresses MAC des appareils qui passent devant l'établissement mais ne se connectent jamais au SSID, utilisant ces données pour générer des analyses de fréquentation. En vertu de la LPRPDE, cela constitue une collecte de renseignements personnels sans connaissance ni consentement. L'atténuation consiste à mettre en œuvre la prise en charge de la randomisation MAC au niveau du point d'accès et à s'assurer que tous les tableaux de bord d'analyse de présence agrègent et anonymisent les données avant le stockage. Les adresses MAC brutes des appareils non associés ne doivent jamais être écrites dans un stockage persistant.
Mode de défaillance : Consentement obsolète. Un établissement déploie un captive portal conforme, puis six mois plus tard, ajoute une nouvelle intégration d'analyse qui envoie des données de session à une plateforme publicitaire tierce. Les utilisateurs existants qui ont consenti aux conditions initiales n'ont pas consenti à cette nouvelle divulgation. Cela viole l'exigence de la LPRPDE d'obtenir le consentement avant toute nouvelle finalité. L'atténuation consiste à mettre en œuvre un système de versioning du consentement qui déclencheune demande de re-consentement pour les utilisateurs existants lorsque des modifications importantes sont apportées aux activités de traitement des données.
Mode de défaillance : Contrats tiers inadéquats. Comme souligné dans l'enquête Tim Hortons, un langage contractuel vague avec les fournisseurs de services tiers — leur permettant d'utiliser les données à leurs propres fins — ne constitue pas une protection adéquate. Assurez-vous que tous les accords de traitement des données avec les fournisseurs d'analyse, les fournisseurs de CRM et les plateformes de marketing incluent des restrictions explicites sur l'utilisation secondaire, les limites de conservation des données et les contrôles des sous-traitants.
ROI et impact commercial
La conformité n'est pas un centre de coûts — c'est un multiplicateur de confiance avec des résultats commerciaux mesurables. Les établissements qui mettent en œuvre des flux de consentement transparents et centrés sur l'utilisateur signalent constamment des taux d'adhésion plus élevés pour les programmes de marketing, car les utilisateurs se sentent maîtres de leurs données. Un Captive Portal bien conçu et conforme à la LPRPDE, qui explique clairement l'échange de valeur — WiFi gratuit en échange d'une adresse e-mail et d'un consentement marketing facultatif — convertit à des taux significativement plus élevés qu'un portail qui noie le consentement dans le jargon juridique.
Du point de vue de l'atténuation des risques, le calcul financier est simple. Une seule action d'application de la loi de l'OPC, même sous le plafond actuel de 100 000 $ de la LPRPDE, génère des dommages réputationnels et des coûts juridiques importants qui dépassent de loin l'investissement dans un déploiement conforme. Sous le régime de la LCAP à venir, l'exposition financière atteint des niveaux menaçant l'entreprise. L'adoption d'une plateforme de niveau entreprise comme Purple, qui offre une gestion centralisée du consentement, des pistes d'audit et des flux de travail automatisés pour les demandes des personnes concernées, réduit les frais généraux opérationnels de la gestion de la conformité en matière de confidentialité sur un parc multi-sites et fournit la piste de preuves documentée que l'OPC s'attend à voir.
Pour les opérateurs de transport qui envisagent des déploiements de véhicules connectés et de WiFi en transit, les mêmes principes de la LPRPDE s'appliquent. Consultez notre guide sur Votre guide des solutions Wi-Fi embarquées pour entreprises pour les considérations spécifiques au déploiement.
Références
[1] Commissariat à la protection de la vie privée du Canada. « Loi sur la protection des renseignements personnels et les documents électroniques (LPRPDE). » priv.gc.ca.
[2] Commissariat à la protection de la vie privée du Canada. « Lignes directrices pour l’obtention d’un consentement valable. » priv.gc.ca, mai 2018.
[3] Commissariat à la protection de la vie privée du Canada. « Principes d’équité en matière d’information de la LPRPDE — Annexe 1. » priv.gc.ca.
[4] Commissariat à la protection de la vie privée du Canada. « Enquête conjointe sur le suivi de la localisation par l’application Tim Hortons (Conclusions LPRPDE n° 2022-001). » priv.gc.ca, juin 2022.
[5] Commissariat à la protection de la vie privée du Canada. « Rapport de conclusions : Collecte de données WiFi par Google Inc. (Conclusions LPRPDE n° 2011-001). » priv.gc.ca, 2011.
[6] Commission d'accès à l'information du Québec. « Loi 25 : Loi modernisant des dispositions législatives en matière de protection des renseignements personnels. » cai.gouv.qc.ca.
[7] IAPP. « Ce que 2026 pourrait apporter aux efforts de réforme de la confidentialité au Canada. » iapp.org, février 2026.
Termes clés et définitions
PIPEDA (Personal Information Protection and Electronic Documents Act)
Canada's federal private-sector privacy law governing the collection, use, and disclosure of personal information in commercial activities. Structured around ten Fair Information Principles in Schedule 1. Applies to all provinces except Alberta, British Columbia, and Quebec, which have substantially similar provincial legislation.
The primary compliance framework for any Canadian venue offering guest WiFi. IT teams encounter PIPEDA when designing captive portals, configuring analytics platforms, and responding to data subject requests.
Meaningful Consent
The OPC's standard for valid consent under PIPEDA, requiring that individuals genuinely understand what they are consenting to — specifically: what data is collected, who receives it, the purposes of collection, and any meaningful risks of harm. Consent buried in lengthy T&Cs, or obtained through a single bundled 'I Accept' button, does not meet this standard.
The central compliance requirement for captive portal design. Every element of the splash page UI must be evaluated against this standard.
Captive Portal
A network gateway that intercepts HTTP/HTTPS traffic from newly associated WiFi clients and redirects them to a web page for authentication, consent collection, and/or payment before granting internet access. Technically implemented via WLAN controller redirect rules, DNS spoofing, or a dedicated gateway appliance.
The primary point of consent collection for guest WiFi deployments. The design of the captive portal UI directly determines PIPEDA compliance status.
MAC Address (Media Access Control Address)
A 48-bit hardware identifier assigned to a network interface controller, used to uniquely identify a device at the data link layer (Layer 2). Under PIPEDA, MAC addresses are personal information because they can be used to identify an individual's device and, by extension, their movements and behaviour.
Encountered in WiFi analytics deployments, probe-based footfall counting, and session logging. Must be anonymised or handled with explicit consent.
OPC (Office of the Privacy Commissioner of Canada)
The independent federal authority responsible for overseeing compliance with PIPEDA and the Privacy Act. The OPC investigates complaints, conducts audits, publishes guidance, and can apply to the Federal Court to enforce its recommendations. Current maximum fine under PIPEDA is $100,000 CAD per violation.
The primary regulatory body IT teams must satisfy. OPC findings are publicly published and serve as binding precedents for compliance interpretation.
CPPA (Consumer Privacy Protection Act)
The proposed replacement for PIPEDA, introduced as part of Bill C-27 in 2022. Would introduce GDPR-scale penalties (up to $25M CAD or 5% of global revenue), mandatory Privacy Impact Assessments, explicit data portability and erasure rights, and a new independent enforcement tribunal. Bill C-27 stalled due to parliamentary prorogation in January 2025; a successor bill is anticipated in 2026.
The future compliance target for Canadian venue operators. IT teams should begin implementing CPPA-level controls now to avoid costly remediation when the legislation passes.
Law 25 (Quebec Act to Modernize Legislative Provisions as Regards the Protection of Personal Information)
Quebec's provincial privacy legislation, which imposes requirements that exceed PIPEDA. Key provisions include mandatory Privacy Impact Assessments before new projects involving personal information, explicit consent for cross-border data transfers, French-language consent notices, and fines up to $25M CAD or 10% of worldwide turnover. Fully in force as of September 2023.
Applies to all venues operating in Quebec. IT teams must implement enhanced consent flows, bilingual notices, and PIAs for any Quebec deployment.
Privacy Impact Assessment (PIA)
A structured risk assessment process that evaluates the privacy implications of a new project, system, or data processing activity before deployment. Identifies data flows, assesses risks to individuals, and documents mitigation measures. Currently a best practice under PIPEDA; mandatory under Quebec's Law 25 for new projects involving personal information; expected to become mandatory federally under the CPPA.
Required before deploying new analytics features, location tracking systems, or third-party data integrations. Provides the documented evidence trail the OPC expects to see in an enforcement scenario.
Layered Notice
A consent architecture that presents privacy information at multiple levels of detail: a brief, prominent summary for the average user; granular options for those who want more control; and a full privacy policy for those who want complete information. Recommended by the OPC as the preferred method for obtaining meaningful consent in digital environments.
The architectural pattern that all PIPEDA-compliant captive portals should implement. Directly addresses the OPC's concern that information buried in lengthy T&Cs is functionally invisible to users.
Accountability Principle (PIPEDA Schedule 1, Principle 1)
The requirement that an organisation is responsible for personal information under its control and must designate an individual (a Privacy Officer) accountable for compliance. Includes implementing policies and practices, training staff, and being able to demonstrate compliance to the OPC on request.
The organisational governance requirement that underpins all other PIPEDA compliance activities. Multi-site venue operators must have a documented Privacy Management Programme covering all locations.
Études de cas
A 300-room hotel in Toronto wants to offer free guest WiFi and use sign-up data to drive repeat bookings and promotional email campaigns. The hotel's current captive portal uses a single 'I Accept' button that links to a 4,000-word Terms and Conditions document. The IT director has been asked to assess compliance risk and redesign the flow before the next OPC audit cycle.
The existing single-button flow is non-compliant and must be replaced with a three-layer architecture. On the WLAN controller (e.g., Cisco Catalyst Centre or Aruba Central), configure the captive portal redirect to the new splash page hosted over HTTPS. Layer 1 of the splash page presents a plain-language summary panel: 'We collect your name, email address, and device identifier to provide WiFi access. We share this data with Purple (our WiFi analytics provider). You can optionally receive promotional emails from us.' Layer 2 presents two checkboxes: Checkbox A (pre-checked, mandatory): 'I agree to the WiFi Terms of Use and Privacy Policy.' Checkbox B (unchecked, optional): 'I would like to receive promotional offers and news from [Hotel Name].' Layer 3 provides a hyperlink 'Full Privacy Policy' opening the complete PIPEDA-compliant policy in a new tab. The policy must specify: data categories collected (name, email, MAC address, session timestamps), purposes (WiFi access delivery; marketing if opted-in), third parties (Purple, email marketing platform), retention period (12 months for marketing, 90 days for session logs), and a privacy contact email. The hotel must also configure its CRM integration to tag records with consent status, so that only users who checked Checkbox B receive marketing communications. Implement a consent versioning system so that if the hotel adds a new analytics partner in future, existing users are prompted to re-consent.
A large shopping centre operator in Montreal wants to deploy a WiFi analytics system to generate zone-level footfall heatmaps across 120,000 square feet of retail space. The proposed system uses WiFi probe requests from unassociated devices (i.e., phones that have not connected to the network) to estimate visitor counts and dwell times. The CTO wants to understand the PIPEDA and Law 25 compliance requirements before procurement.
This deployment involves processing personal information (MAC addresses are personal information under PIPEDA) without the knowledge or consent of the individuals whose devices are being probed. Under both PIPEDA and Quebec's Law 25, this requires careful architectural controls. The compliant approach is as follows: First, conduct a Privacy Impact Assessment (PIA) before procurement, as required by Law 25 for any new project involving personal information. The PIA must assess the necessity and proportionality of the data collection. Second, implement MAC address anonymisation at the access point or controller level using a rotating cryptographic hash (e.g., HMAC-SHA256 with a key that rotates every 24 hours). This ensures that the same device cannot be tracked across days, and that the raw MAC address is never written to persistent storage. Third, configure the analytics platform to store and display only aggregate, zone-level counts — not individual device trajectories. The dashboard should show 'Zone A: 450 visitors, avg dwell 8 minutes' rather than individual movement paths. Fourth, post clear, visible signage at all venue entrances disclosing that WiFi-based analytics are in use for footfall measurement, with a QR code linking to the full privacy notice. This satisfies the 'openness' principle and provides constructive notice. Fifth, for the connected WiFi network (the SSID guests can join), implement a standard three-layer captive portal as described in the hotel scenario above. The Law 25 requirement for French-language consent notices applies to all captive portal text.
A national retail chain with 85 stores across Canada is preparing for the incoming CPPA regime. Their current PIPEDA compliance is adequate, but the CTO wants to understand what architectural changes are needed to meet CPPA-level requirements, particularly around data subject rights, de-identification, and the increased penalty exposure.
The transition from PIPEDA to CPPA compliance requires three primary architectural investments. First, implement automated data subject rights workflows. The CPPA introduces explicit rights to data portability and erasure. The chain's WiFi platform must expose an API endpoint that, when triggered by a verified data subject request, can: (a) export all personal data associated with a given email address or device identifier in a machine-readable format (JSON or CSV); and (b) purge that record from the local captive portal database, the cloud analytics platform, and all downstream CRM and marketing automation systems simultaneously. This must be achievable within a defined SLA — 30 days is the CPPA's proposed response window. Second, upgrade de-identification protocols. Current PIPEDA guidance on de-identified data is relatively permissive. The CPPA will introduce a higher bar: de-identified data must be processed in a manner that makes re-identification 'not reasonably foreseeable.' For MAC-based analytics, this means implementing rotating hash keys (as described above) and ensuring that the analytics platform cannot be used to re-identify individuals even by the operator. Third, conduct mandatory Privacy Impact Assessments for all high-risk processing activities. For a retail chain, this includes any deployment involving location analytics, behavioural profiling for targeted advertising, or data sharing with advertising technology platforms. PIAs should be documented and retained as evidence of accountability. The chain should also review all third-party data processing agreements and update them to include CPPA-compliant clauses covering data retention, sub-processor restrictions, and breach notification timelines.
Analyse de scénario
Q1. Your venue's current captive portal collects name, email, and device MAC address. The splash page has a single 'Connect to WiFi' button that, when clicked, is deemed acceptance of the Terms and Conditions (which include consent to receive marketing emails). A user complains to the OPC. What specific PIPEDA violations has your venue committed, and what is the minimum remediation required?
💡 Astuce :Consider PIPEDA Principles 1, 2, 3, and 4. Focus on the bundling of consent and the adequacy of the notice provided.
Afficher l'approche recommandée
The venue has committed at least three violations. First, under Principle 3 (Consent), the bundling of marketing consent with WiFi access is non-compliant — users cannot be required to consent to marketing as a condition of receiving the service. Second, under Principle 2 (Identifying Purposes), the purposes are not clearly identified at the point of collection; the user must read the full T&Cs to discover the marketing purpose. Third, the consent is not 'meaningful' under the OPC's 2018 guidelines because key elements (what data, why, who gets it) are not prominently displayed. Minimum remediation: redesign the portal with a three-layer architecture, decouple marketing consent into a separate unchecked checkbox, and add a plain-language summary to the splash page. The venue must also implement a consent versioning system and update its Privacy Management Programme documentation.
Q2. You are the IT director of a conference centre in Vancouver. A vendor proposes deploying a WiFi analytics system that tracks the MAC addresses of all devices in the venue — including those that never connect to the WiFi network — to generate session-level movement analytics for exhibitors. The vendor says the data is 'de-identified' because they hash the MAC addresses. Is this deployment compliant with PIPEDA? What additional controls, if any, are required?
💡 Astuce :Consider whether hashing alone constitutes de-identification under PIPEDA. Think about the difference between a static hash and a rotating hash, and the concept of re-identification risk.
Afficher l'approche recommandée
The deployment is potentially compliant but requires additional controls. A static hash of a MAC address is not true de-identification under PIPEDA because the same device will always produce the same hash, allowing cross-session tracking and, potentially, re-identification if the hash table is compromised or if the MAC address is known. To achieve genuine de-identification, the hash key must rotate at regular intervals (e.g., every 24 hours), ensuring that the same device cannot be tracked across sessions. Additionally, the venue must post clear, visible signage at all entrances disclosing that WiFi-based analytics are in use, satisfying the Openness principle. The analytics platform must store and display only aggregate, zone-level data — not individual device trajectories. If the vendor intends to share session-level data with exhibitors (third parties), this constitutes a disclosure of personal information and requires explicit consent from users who have connected to the network, or robust anonymisation that makes re-identification 'not reasonably foreseeable.' A Privacy Impact Assessment is strongly recommended before deployment.
Q3. A hotel chain with properties in Ontario, Alberta, and Quebec is standardising its guest WiFi platform. The CTO wants a single consent flow that works across all provinces. The legal team has flagged that Quebec's Law 25 imposes additional requirements. Design the minimum viable consent architecture that satisfies PIPEDA in Ontario and Alberta, Law 25 in Quebec, and is forward-compatible with the incoming CPPA.
💡 Astuce :Identify the highest common denominator across all three regimes. Consider language, PIA requirements, consent granularity, and data subject rights.
Afficher l'approche recommandée
The minimum viable architecture should be designed to the highest standard across all applicable regimes, which means treating Law 25 as the baseline. The consent flow must: (1) Present a bilingual (English and French) splash page with a plain-language just-in-time summary; (2) Provide separate, unchecked-by-default checkboxes for WiFi access terms, marketing consent, and analytics profiling; (3) Link to a full privacy policy available in both languages, specifying data categories, purposes, third parties, retention periods, and data subject rights contact; (4) Support data subject rights for access, correction, and deletion — with automated workflows capable of purging records across all systems within 30 days; (5) Implement rotating-hash MAC anonymisation at the edge. Before deploying the system in Quebec, conduct a Privacy Impact Assessment as required by Law 25. For CPPA forward-compatibility, ensure the platform supports data portability export in machine-readable format and can generate audit trails of all consent events. This single architecture satisfies PIPEDA in Ontario and Alberta, Law 25 in Quebec, and is well-positioned for CPPA compliance when the legislation passes.
Q4. Six months after deploying a compliant captive portal, your marketing team wants to add a new integration that sends guest session data (email, visit frequency, dwell time) to a third-party programmatic advertising platform for retargeting campaigns. Existing users consented to the original terms, which did not mention this platform. What are your obligations under PIPEDA before activating this integration?
💡 Astuce :Focus on the 'new purpose' requirement under PIPEDA and the OPC's guidance on dynamic consent. Consider what constitutes a 'significant change' to privacy practices.
Afficher l'approche recommandée
Under PIPEDA, sharing personal information with a third-party advertising platform for retargeting constitutes a new purpose that was not anticipated in the original consent. Before activating the integration, you must: (1) Update your privacy policy to disclose the new third party and the retargeting purpose; (2) Notify all existing users of the material change to your privacy practices — this can be done via email to those who provided their address during WiFi sign-up; (3) Obtain fresh consent from existing users for the new purpose before their data is shared with the advertising platform — this means presenting them with a new opt-in opportunity, not assuming their original consent covers the new use; (4) Ensure that users who do not consent to the new purpose continue to receive WiFi access without interruption; (5) Review the data processing agreement with the advertising platform to ensure it includes adequate protections against secondary use by the platform. Failing to obtain fresh consent before activating the integration would constitute a disclosure of personal information for a purpose beyond what was originally consented to — a direct violation of PIPEDA Principle 3.



