Conformidade com a PIPEDA para WiFi de Convidados no Canadá
Este guia fornece uma referência técnica e operacional definitiva para operadores de estabelecimentos canadenses que implementam WiFi de convidados sob a PIPEDA. Ele aborda a estrutura de consentimento significativo do OPC, o princípio da responsabilidade, precedentes de aplicação das investigações do Tim Hortons e do Google WiFi, e as mudanças arquitetônicas necessárias para atender à Lei de Proteção à Privacidade do Consumidor (CPPA) que está por vir, sob o Projeto de Lei C-27. Gerentes de TI e líderes de conformidade encontrarão especificações acionáveis de design de Captive Portal, requisitos de minimização de dados e um roteiro claro para se proteger contra penalidades em escala GDPR.
🎧 Ouça este Guia
Ver Transcrição
- Resumo Executivo
- Análise Técnica Aprofundada: PIPEDA e o Captive Portal
- O Mandato de Consentimento Significativo
- O Precedente Tim Hortons: Um Alerta para Análises de Localização
- Guia de Implementação: Construindo um Fluxo de Integração em Conformidade
- Passo 1: Minimização de Dados na Borda
- Etapa 2: Arquitetura de UI do Captive Portal em Camadas
- Etapa 3: Integração de API e Residência de Dados
- Etapa 4: Conformidade Bilíngue
- Etapa 5: Programa de Gestão de Privacidade
- Melhores Práticas e Preparação para o Futuro para o Projeto de Lei C-27 (CPPA)
- Solução de Problemas e Mitigação de Riscos
- ROI e Impacto nos Negócios
- Referências

Resumo Executivo
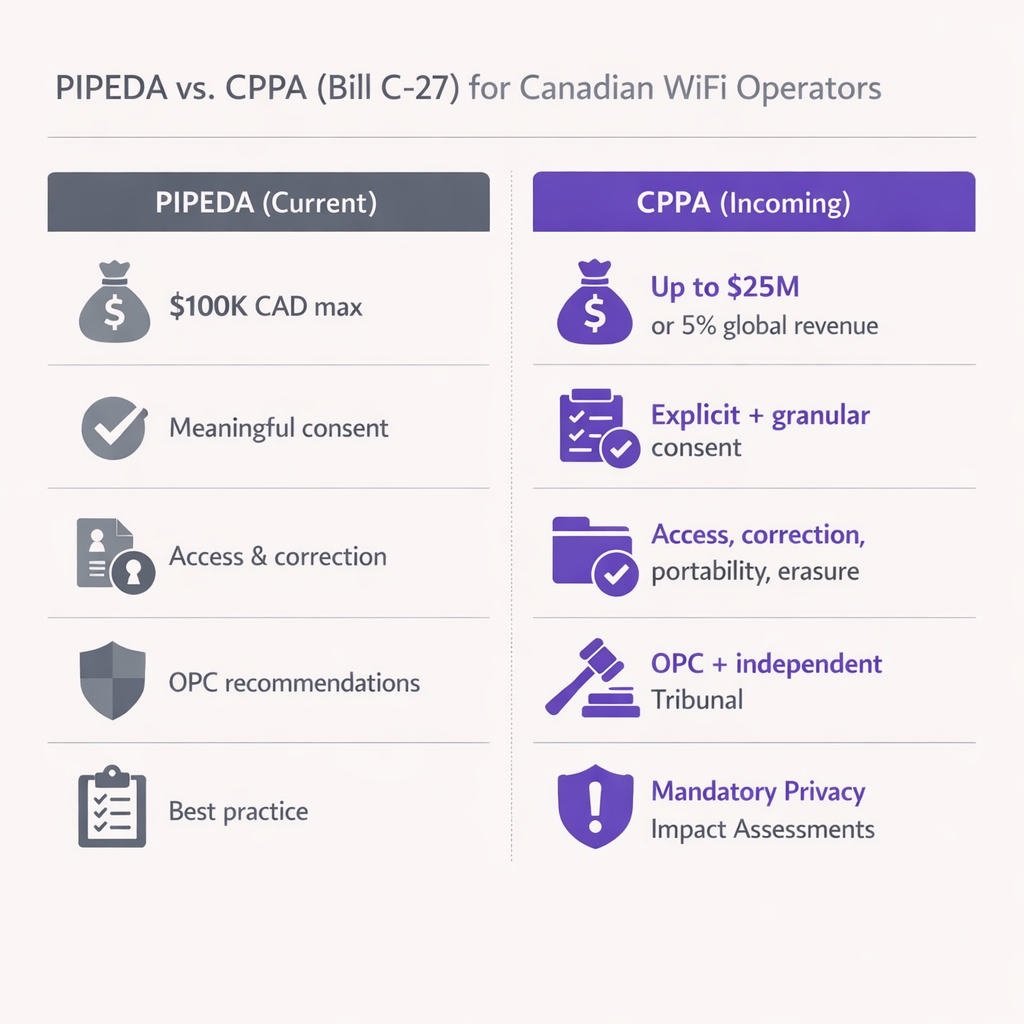
Para operadores de estabelecimentos canadenses e líderes de TI, oferecer WiFi de convidados não é mais apenas uma questão de conectividade — é um canal crítico de aquisição de dados. No entanto, o cenário regulatório que rege como esses dados são coletados e usados está se tornando mais rigoroso. A Lei de Proteção de Informações Pessoais e Documentos Eletrônicos (PIPEDA) impõe requisitos rigorosos para a obtenção de "consentimento significativo" antes de coletar dados do usuário em Captive Portals. Além disso, com a Lei de Proteção à Privacidade do Consumidor (CPPA) que está por vir, pronta para introduzir penalidades no estilo GDPR (até $25M CAD ou 5% da receita global), a conformidade é agora uma prioridade de gerenciamento de risco em nível de diretoria.
Este guia fornece um roteiro técnico e operacional para arquitetos e gerentes de TI que implementam soluções de WiFi de Convidados no Canadá. Detalhamos a postura de fiscalização do Gabinete do Comissário de Privacidade (OPC), os requisitos técnicos para consentimento em camadas e as etapas acionáveis para proteger sua arquitetura de rede contra futuras mudanças legislativas. Seja você opera em Varejo , Hotelaria ou Transporte , este documento traduz obrigações legais em especificações técnicas concretas.
Análise Técnica Aprofundada: PIPEDA e o Captive Portal
A PIPEDA se aplica à coleta, uso e divulgação de informações pessoais no curso de atividades comerciais no Canadá. Para um Captive Portal WiFi, "informações pessoais" se estendem além de nomes e endereços de e-mail; inclui endereços MAC de dispositivos, análises de localização e comportamento de navegação. A Lei é estruturada em torno de dez Princípios de Informação Justa consagrados no Anexo 1, dos quais o Princípio 3 (Consentimento), o Princípio 2 (Identificação de Propósitos), o Princípio 4 (Limitação da Coleta) e o Princípio 1 (Responsabilidade) são os mais diretamente relevantes para implementações de WiFi de convidados.
O Mandato de Consentimento Significativo
As Diretrizes do OPC para Obtenção de Consentimento Significativo, emitidas em conjunto com os comissários provinciais de Alberta e British Columbia em 2018, mudaram fundamentalmente como os estabelecimentos devem projetar seus fluxos de integração. Enterrar as práticas de coleta de dados em um documento de Termos e Condições de 5.000 palavras é explicitamente não-conforme. As diretrizes estabelecem sete princípios, dos quais três são arquitetonicamente críticos para o design de Captive Portal.
Primeiro, ênfase nos elementos-chave: a página de splash deve exibir de forma proeminente quais dados estão sendo coletados, com quem são compartilhados, os propósitos da coleta e quaisquer riscos residuais significativos de dano. Linguagem vaga como "melhoria do serviço" é insuficiente — os propósitos devem ser específicos e distinguíveis entre aqueles integrais à prestação do serviço e aqueles que são opcionais.
Segundo, escolha granular: os usuários devem ser capazes de optar por participar ou não de usos secundários (marketing, perfil comportamental, análises) independentemente do serviço primário (acesso WiFi). Agrupar o consentimento de marketing como condição de acesso à rede viola diretamente o Princípio 3 da PIPEDA, pois exige consentimento além do que é necessário para fornecer o serviço.
Terceiro, transparência dinâmica: o consentimento não é um evento único. Se você atualizar seu motor de Análise de WiFi para rastrear novas métricas ou compartilhar dados com um novo terceiro, você deve notificar os usuários existentes e obter novo consentimento para o novo propósito antes que a mudança entre em vigor.
O Precedente Tim Hortons: Um Alerta para Análises de Localização
Em 2022, a investigação conjunta do OPC sobre o aplicativo móvel Tim Hortons (PIPEDA Findings #2022-001) estabeleceu um precedente marcante para o rastreamento de localização que toda equipe de TI de um estabelecimento deve entender. A investigação descobriu que o aplicativo coletava dados GPS granulares mesmo quando o aplicativo estava fechado — mais de 2.700 vezes em menos de cinco meses para um usuário — supostamente para publicidade direcionada, um propósito que nunca foi realmente cumprido. O OPC decidiu que essa coleta carecia de uma "necessidade legítima" e que o consentimento obtido era enganoso, pois os usuários foram informados de que os dados eram coletados apenas enquanto o aplicativo estava aberto.
Para equipes de TI de estabelecimentos que implementam um Sistema de Posicionamento Interno: UWB, BLE e WiFi , a lição é clara: você não pode coletar dados de localização em excesso "apenas por precaução". Se seus pontos de acesso sondam endereços MAC não associados para gerar mapas de calor de fluxo de pessoas, você deve anonimizar esses dados na borda usando hashes criptográficos rotativos, ou obter consentimento explícito antes mesmo que o usuário se associe ao SSID. O OPC avaliará se seu propósito declarado corresponde ao seu uso real e se o volume de dados coletados é proporcional ao benefício obtido.
Guia de Implementação: Construindo um Fluxo de Integração em Conformidade
A implementação de um Captive Portal em conformidade com a PIPEDA requer coordenação entre engenharia de rede, jurídico e marketing. O seguinte plano se aplica a qualquer estabelecimento que implemente WiFi de Convidados no Canadá.
Passo 1: Minimização de Dados na Borda
Configure seus controladores WLAN para descartar dados de payload desnecessários. Conforme estabelecido na investigação do Google Street View de 2011 (PIPEDA Findings #2011-001), a captura de dados de payload de redes não criptografadas viola a PIPEDA. Garanta que seus servidores RADIUS e gateways de Captive Portal registrem apenas os atributos necessários para o gerenciamento de sessão e análises explicitamente consentidas. Para análises de presença baseadas em endereço MAC, implemente uma função de hash rotativano nível do AP ou do controlador, para que o endereço MAC bruto nunca seja gravado no armazenamento persistente.
Etapa 2: Arquitetura de UI do Captive Portal em Camadas
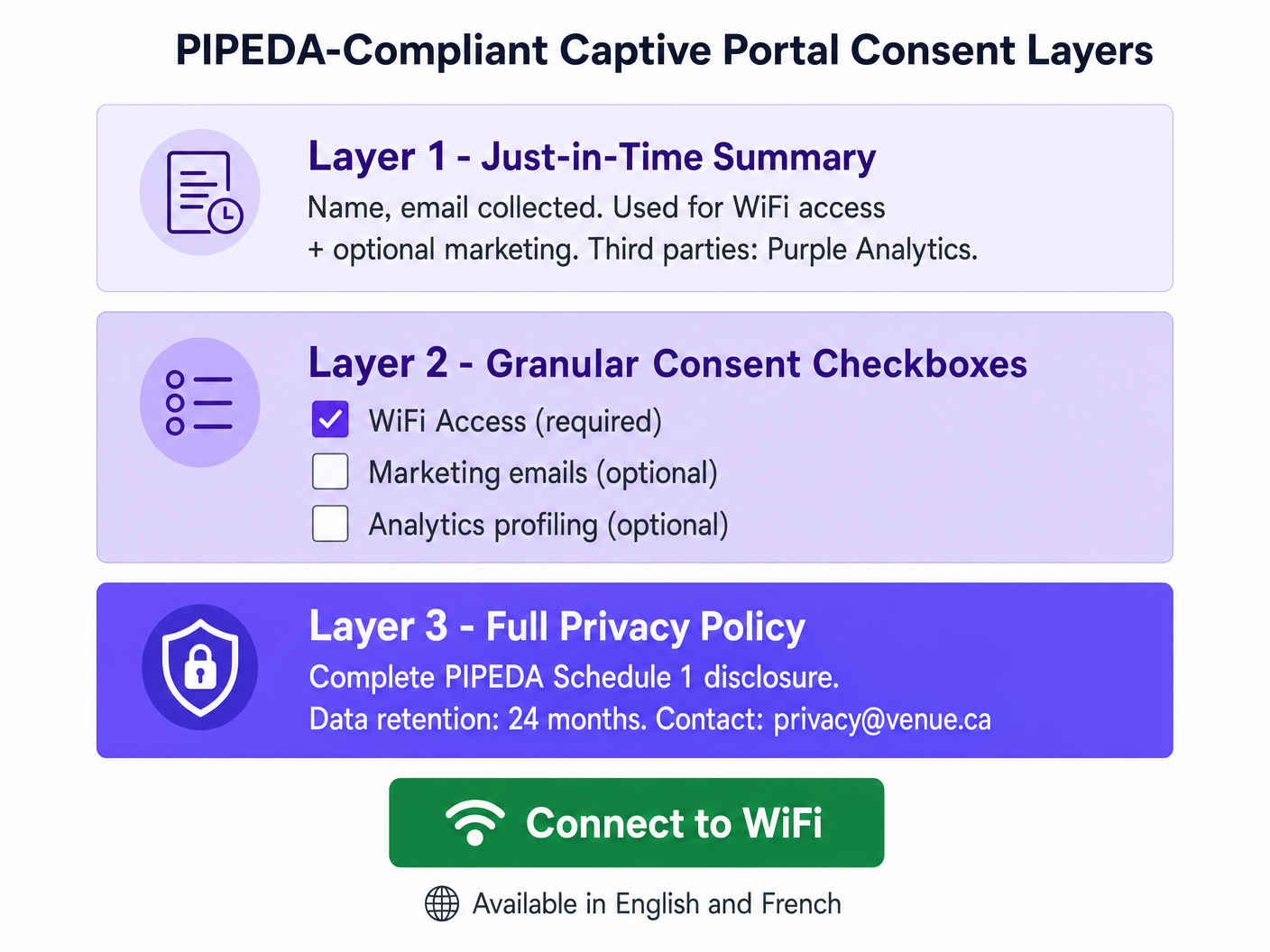
Projete a página inicial usando uma abordagem de três camadas alinhada com a orientação de aviso em camadas da OPC. A Camada 1 (a tela inicial) apresenta um resumo claro e em linguagem simples: quais dados são coletados, quem os processa e para quais finalidades. A Camada 2 apresenta caixas de seleção de consentimento granulares — desmarcadas por padrão para todas as finalidades opcionais — cobrindo comunicações de marketing, análises comportamentais e qualquer compartilhamento de dados com terceiros além do que é exigido para a prestação de serviços. A Camada 3 fornece um hiperlink para a política de privacidade completa, hospedada em uma página segura e responsiva acessível de qualquer dispositivo. Se sua equipe de marketing precisar de ajuda para escrever resumos concisos e juridicamente sólidos, considere usar IA Generativa para Conteúdo e Criativos de Captive Portal ou, para implantações em francês, IA générative pour le texte et les créatifs de Captive Portal .
Etapa 3: Integração de API e Residência de Dados
Ao integrar seu captive portal com um CRM ou plataforma de automação de marketing, garanta que os dados fluam via APIs seguras e criptografadas (TLS 1.2 mínimo, TLS 1.3 preferencial). Para implantações canadenses, priorize fornecedores que ofereçam residência de dados local (por exemplo, AWS Canada Central, ca-central-1) para mitigar riscos de transferência transfronteiriça. Isso é especialmente crítico para locais que operam em Quebec sob a Lei 25, que exige uma Avaliação de Impacto à Privacidade (PIA) antes de transferir informações pessoais para fora de Quebec e exige que a jurisdição receptora ofereça proteção equivalente.
Etapa 4: Conformidade Bilíngue
Todos os avisos de consentimento, políticas de privacidade e informações sobre os direitos dos titulares de dados devem estar disponíveis em inglês e francês para locais que operam em Quebec. Este é um requisito tanto da Lei 25 quanto da Carta da Língua Francesa de Quebec. Para locais federais (aeroportos, estações ferroviárias, edifícios federais), a entrega bilíngue é uma expectativa básica sob a Lei de Línguas Oficiais.
Etapa 5: Programa de Gestão de Privacidade
O Princípio de Responsabilidade da PIPEDA (Princípio 1) exige que sua organização designe um Encarregado de Proteção de Dados (Privacy Officer), mantenha políticas e procedimentos documentados e seja capaz de demonstrar conformidade à OPC mediante solicitação. Para operadores multi-site — como uma rede de varejo nacional com mais de 50 locais, cada um executando um captive portal — isso significa um Programa de Gestão de Privacidade (PMP) centralizado que abrange todos os locais de forma consistente, com trilhas de auditoria para eventos de consentimento, solicitações de titulares de dados e cronogramas de retenção.
Melhores Práticas e Preparação para o Futuro para o Projeto de Lei C-27 (CPPA)
Embora o Projeto de Lei C-27 — a Lei de Proteção da Privacidade do Consumidor — tenha sido paralisado devido à prorrogação do Parlamento em janeiro de 2025, seus princípios centrais representam o futuro inevitável da lei de privacidade canadense. A partir do início de 2026, espera-se que um novo projeto de lei federal de privacidade, incorporando muitas disposições da CPPA, seja introduzido no Parlamento. A abordagem prudente é tratar os controles de nível CPPA como seu objetivo de implementação hoje.
As mudanças mais significativas a serem preparadas são as seguintes. A escalada de penalidades é a preocupação mais imediata: a CPPA introduziria multas de até $25M CAD ou 5% da receita anual global, uma mudança significativa em relação ao máximo atual de $100K da PIPEDA. Avaliações de Impacto à Privacidade obrigatórias serão exigidas para atividades de processamento de alto risco, incluindo análises de localização, criação de perfis comportamentais e qualquer processamento envolvendo informações pessoais sensíveis. Direitos explícitos de portabilidade e exclusão de dados exigirão fluxos de trabalho automatizados capazes de purgar o registro de um usuário de todos os sistemas — banco de dados local, controlador de nuvem, CRMs a jusante — dentro de uma janela de resposta definida. Os padrões de desidentificação se tornarão mais prescritivos; garanta que sua plataforma de análise faça hash de endereços MAC usando salts rotativos e que a reidentificação seja tecnicamente inviável.
Para operadores de locais de saúde, a interseção de análises de WiFi e dados de pacientes cria obrigações adicionais sob a PIPEDA e a legislação provincial de privacidade de saúde. Consulte nossa orientação da indústria de Saúde para considerações de implantação específicas do setor.
Solução de Problemas e Mitigação de Riscos
Modo de Falha: O Portal Tudo ou Nada. Muitas implantações legadas de captive portal apresentam um único "Eu Aceito" que agrupa o acesso ao WiFi, o consentimento de marketing e a criação de perfis de análise em um único clique. Esta é uma violação direta da PIPEDA e o modo de falha mais comum que a OPC encontra em reclamações. A mitigação é simples: desvincule a autenticação de rede das opções de marketing usando caixas de seleção separadas e claramente identificadas. O acesso à rede deve ser concedido sem qualquer consentimento secundário.
Modo de Falha: Rastreamento Silencioso de MAC. Algumas implantações registram os endereços MAC de dispositivos que passam pelo local, mas nunca se conectam ao SSID, usando esses dados para gerar análises de fluxo de pessoas. Sob a PIPEDA, isso constitui coleta de informações pessoais sem conhecimento ou consentimento. A mitigação é implementar suporte à randomização de MAC no nível do AP e garantir que todos os painéis de análise de presença agreguem e anonimizem os dados antes do armazenamento. Endereços MAC brutos de dispositivos não associados nunca devem ser gravados no armazenamento persistente.
Modo de Falha: Consentimento Obsoleto. Um local implanta um captive portal compatível e, seis meses depois, adiciona uma nova integração de análise que envia dados de sessão para uma plataforma de publicidade de terceiros. Usuários existentes que consentiram com os termos originais não consentiram com esta nova divulgação. Isso viola o requisito da PIPEDA de obter consentimento antes de qualquer nova finalidade. A mitigação é implementar um sistema de versionamento de consentimento que acione um aviso de novo consentimento para usuários existentes quando alterações materiais são feitas nas atividades de processamento de dados.
Modo de Falha: Contratos Inadequados com Terceiros. Conforme destacado na investigação do Tim Hortons, a linguagem contratual vaga com provedores de serviços terceirizados — permitindo-lhes usar dados para seus próprios fins — não constitui proteção adequada. Garanta que todos os acordos de processamento de dados com fornecedores de análise, provedores de CRM e plataformas de marketing incluam restrições explícitas sobre uso secundário, limites de retenção de dados e controles de sub-processadores.
ROI e Impacto nos Negócios
A conformidade não é um centro de custo — é um multiplicador de confiança com resultados comerciais mensuráveis. Locais que implementam fluxos de consentimento transparentes e centrados no usuário relatam consistentemente taxas de adesão mais altas para programas de marketing porque os usuários se sentem no controle de seus dados. Um Captive Portal bem projetado e em conformidade com a PIPEDA, que explica claramente a troca de valor — WiFi gratuito em troca de um endereço de e-mail e consentimento de marketing opcional — converte em taxas significativamente mais altas do que um portal que esconde o consentimento em termos jurídicos.
Do ponto de vista da mitigação de riscos, o cálculo financeiro é direto. Uma única ação de fiscalização da OPC, mesmo sob o máximo atual de US$ 100 mil da PIPEDA, gera danos reputacionais significativos e custos legais que excedem em muito o investimento em uma implantação em conformidade. Sob o regime CPPA que se aproxima, a exposição financeira escala para níveis que ameaçam a empresa. Padronizar em uma plataforma de nível empresarial como a Purple, que oferece gerenciamento de consentimento centralizado, trilhas de auditoria e fluxos de trabalho automatizados para solicitações de titulares de dados, reduz a sobrecarga operacional de gerenciar a conformidade de privacidade em um ambiente multi-site e fornece o rastro de evidências documentado que a OPC espera ver.
Para operadores de transporte que consideram implantações de veículos conectados e WiFi em trânsito, os mesmos princípios da PIPEDA se aplicam. Consulte nosso guia sobre Seu Guia para Soluções Wi-Fi Empresariais em Carros para considerações específicas de implantação.
Referências
[1] Office of the Privacy Commissioner of Canada. "The Personal Information Protection and Electronic Documents Act (PIPEDA)." priv.gc.ca.
[2] Office of the Privacy Commissioner of Canada. "Guidelines for obtaining meaningful consent." priv.gc.ca, May 2018.
[3] Office of the Privacy Commissioner of Canada. "PIPEDA Fair Information Principles — Schedule 1." priv.gc.ca.
[4] Office of the Privacy Commissioner of Canada. "Joint investigation into location tracking by the Tim Hortons App (PIPEDA Findings #2022-001)." priv.gc.ca, June 2022.
[5] Office of the Privacy Commissioner of Canada. "Report of Findings: Google Inc. WiFi Data Collection (PIPEDA Findings #2011-001)." priv.gc.ca, 2011.
[6] Commission d'accès à l'information du Québec. "Law 25: Act to modernize legislative provisions as regards the protection of personal information." cai.gouv.qc.ca.
[7] IAPP. "What 2026 may bring for Canada's privacy reform efforts." iapp.org, February 2026.
Termos-Chave e Definições
PIPEDA (Personal Information Protection and Electronic Documents Act)
Canada's federal private-sector privacy law governing the collection, use, and disclosure of personal information in commercial activities. Structured around ten Fair Information Principles in Schedule 1. Applies to all provinces except Alberta, British Columbia, and Quebec, which have substantially similar provincial legislation.
The primary compliance framework for any Canadian venue offering guest WiFi. IT teams encounter PIPEDA when designing captive portals, configuring analytics platforms, and responding to data subject requests.
Meaningful Consent
The OPC's standard for valid consent under PIPEDA, requiring that individuals genuinely understand what they are consenting to — specifically: what data is collected, who receives it, the purposes of collection, and any meaningful risks of harm. Consent buried in lengthy T&Cs, or obtained through a single bundled 'I Accept' button, does not meet this standard.
The central compliance requirement for captive portal design. Every element of the splash page UI must be evaluated against this standard.
Captive Portal
A network gateway that intercepts HTTP/HTTPS traffic from newly associated WiFi clients and redirects them to a web page for authentication, consent collection, and/or payment before granting internet access. Technically implemented via WLAN controller redirect rules, DNS spoofing, or a dedicated gateway appliance.
The primary point of consent collection for guest WiFi deployments. The design of the captive portal UI directly determines PIPEDA compliance status.
MAC Address (Media Access Control Address)
A 48-bit hardware identifier assigned to a network interface controller, used to uniquely identify a device at the data link layer (Layer 2). Under PIPEDA, MAC addresses are personal information because they can be used to identify an individual's device and, by extension, their movements and behaviour.
Encountered in WiFi analytics deployments, probe-based footfall counting, and session logging. Must be anonymised or handled with explicit consent.
OPC (Office of the Privacy Commissioner of Canada)
The independent federal authority responsible for overseeing compliance with PIPEDA and the Privacy Act. The OPC investigates complaints, conducts audits, publishes guidance, and can apply to the Federal Court to enforce its recommendations. Current maximum fine under PIPEDA is $100,000 CAD per violation.
The primary regulatory body IT teams must satisfy. OPC findings are publicly published and serve as binding precedents for compliance interpretation.
CPPA (Consumer Privacy Protection Act)
The proposed replacement for PIPEDA, introduced as part of Bill C-27 in 2022. Would introduce GDPR-scale penalties (up to $25M CAD or 5% of global revenue), mandatory Privacy Impact Assessments, explicit data portability and erasure rights, and a new independent enforcement tribunal. Bill C-27 stalled due to parliamentary prorogation in January 2025; a successor bill is anticipated in 2026.
The future compliance target for Canadian venue operators. IT teams should begin implementing CPPA-level controls now to avoid costly remediation when the legislation passes.
Law 25 (Quebec Act to Modernize Legislative Provisions as Regards the Protection of Personal Information)
Quebec's provincial privacy legislation, which imposes requirements that exceed PIPEDA. Key provisions include mandatory Privacy Impact Assessments before new projects involving personal information, explicit consent for cross-border data transfers, French-language consent notices, and fines up to $25M CAD or 10% of worldwide turnover. Fully in force as of September 2023.
Applies to all venues operating in Quebec. IT teams must implement enhanced consent flows, bilingual notices, and PIAs for any Quebec deployment.
Privacy Impact Assessment (PIA)
A structured risk assessment process that evaluates the privacy implications of a new project, system, or data processing activity before deployment. Identifies data flows, assesses risks to individuals, and documents mitigation measures. Currently a best practice under PIPEDA; mandatory under Quebec's Law 25 for new projects involving personal information; expected to become mandatory federally under the CPPA.
Required before deploying new analytics features, location tracking systems, or third-party data integrations. Provides the documented evidence trail the OPC expects to see in an enforcement scenario.
Layered Notice
A consent architecture that presents privacy information at multiple levels of detail: a brief, prominent summary for the average user; granular options for those who want more control; and a full privacy policy for those who want complete information. Recommended by the OPC as the preferred method for obtaining meaningful consent in digital environments.
The architectural pattern that all PIPEDA-compliant captive portals should implement. Directly addresses the OPC's concern that information buried in lengthy T&Cs is functionally invisible to users.
Accountability Principle (PIPEDA Schedule 1, Principle 1)
The requirement that an organisation is responsible for personal information under its control and must designate an individual (a Privacy Officer) accountable for compliance. Includes implementing policies and practices, training staff, and being able to demonstrate compliance to the OPC on request.
The organisational governance requirement that underpins all other PIPEDA compliance activities. Multi-site venue operators must have a documented Privacy Management Programme covering all locations.
Estudos de Caso
A 300-room hotel in Toronto wants to offer free guest WiFi and use sign-up data to drive repeat bookings and promotional email campaigns. The hotel's current captive portal uses a single 'I Accept' button that links to a 4,000-word Terms and Conditions document. The IT director has been asked to assess compliance risk and redesign the flow before the next OPC audit cycle.
The existing single-button flow is non-compliant and must be replaced with a three-layer architecture. On the WLAN controller (e.g., Cisco Catalyst Centre or Aruba Central), configure the captive portal redirect to the new splash page hosted over HTTPS. Layer 1 of the splash page presents a plain-language summary panel: 'We collect your name, email address, and device identifier to provide WiFi access. We share this data with Purple (our WiFi analytics provider). You can optionally receive promotional emails from us.' Layer 2 presents two checkboxes: Checkbox A (pre-checked, mandatory): 'I agree to the WiFi Terms of Use and Privacy Policy.' Checkbox B (unchecked, optional): 'I would like to receive promotional offers and news from [Hotel Name].' Layer 3 provides a hyperlink 'Full Privacy Policy' opening the complete PIPEDA-compliant policy in a new tab. The policy must specify: data categories collected (name, email, MAC address, session timestamps), purposes (WiFi access delivery; marketing if opted-in), third parties (Purple, email marketing platform), retention period (12 months for marketing, 90 days for session logs), and a privacy contact email. The hotel must also configure its CRM integration to tag records with consent status, so that only users who checked Checkbox B receive marketing communications. Implement a consent versioning system so that if the hotel adds a new analytics partner in future, existing users are prompted to re-consent.
A large shopping centre operator in Montreal wants to deploy a WiFi analytics system to generate zone-level footfall heatmaps across 120,000 square feet of retail space. The proposed system uses WiFi probe requests from unassociated devices (i.e., phones that have not connected to the network) to estimate visitor counts and dwell times. The CTO wants to understand the PIPEDA and Law 25 compliance requirements before procurement.
This deployment involves processing personal information (MAC addresses are personal information under PIPEDA) without the knowledge or consent of the individuals whose devices are being probed. Under both PIPEDA and Quebec's Law 25, this requires careful architectural controls. The compliant approach is as follows: First, conduct a Privacy Impact Assessment (PIA) before procurement, as required by Law 25 for any new project involving personal information. The PIA must assess the necessity and proportionality of the data collection. Second, implement MAC address anonymisation at the access point or controller level using a rotating cryptographic hash (e.g., HMAC-SHA256 with a key that rotates every 24 hours). This ensures that the same device cannot be tracked across days, and that the raw MAC address is never written to persistent storage. Third, configure the analytics platform to store and display only aggregate, zone-level counts — not individual device trajectories. The dashboard should show 'Zone A: 450 visitors, avg dwell 8 minutes' rather than individual movement paths. Fourth, post clear, visible signage at all venue entrances disclosing that WiFi-based analytics are in use for footfall measurement, with a QR code linking to the full privacy notice. This satisfies the 'openness' principle and provides constructive notice. Fifth, for the connected WiFi network (the SSID guests can join), implement a standard three-layer captive portal as described in the hotel scenario above. The Law 25 requirement for French-language consent notices applies to all captive portal text.
A national retail chain with 85 stores across Canada is preparing for the incoming CPPA regime. Their current PIPEDA compliance is adequate, but the CTO wants to understand what architectural changes are needed to meet CPPA-level requirements, particularly around data subject rights, de-identification, and the increased penalty exposure.
The transition from PIPEDA to CPPA compliance requires three primary architectural investments. First, implement automated data subject rights workflows. The CPPA introduces explicit rights to data portability and erasure. The chain's WiFi platform must expose an API endpoint that, when triggered by a verified data subject request, can: (a) export all personal data associated with a given email address or device identifier in a machine-readable format (JSON or CSV); and (b) purge that record from the local captive portal database, the cloud analytics platform, and all downstream CRM and marketing automation systems simultaneously. This must be achievable within a defined SLA — 30 days is the CPPA's proposed response window. Second, upgrade de-identification protocols. Current PIPEDA guidance on de-identified data is relatively permissive. The CPPA will introduce a higher bar: de-identified data must be processed in a manner that makes re-identification 'not reasonably foreseeable.' For MAC-based analytics, this means implementing rotating hash keys (as described above) and ensuring that the analytics platform cannot be used to re-identify individuals even by the operator. Third, conduct mandatory Privacy Impact Assessments for all high-risk processing activities. For a retail chain, this includes any deployment involving location analytics, behavioural profiling for targeted advertising, or data sharing with advertising technology platforms. PIAs should be documented and retained as evidence of accountability. The chain should also review all third-party data processing agreements and update them to include CPPA-compliant clauses covering data retention, sub-processor restrictions, and breach notification timelines.
Análise de Cenário
Q1. Your venue's current captive portal collects name, email, and device MAC address. The splash page has a single 'Connect to WiFi' button that, when clicked, is deemed acceptance of the Terms and Conditions (which include consent to receive marketing emails). A user complains to the OPC. What specific PIPEDA violations has your venue committed, and what is the minimum remediation required?
💡 Dica:Consider PIPEDA Principles 1, 2, 3, and 4. Focus on the bundling of consent and the adequacy of the notice provided.
Mostrar Abordagem Recomendada
The venue has committed at least three violations. First, under Principle 3 (Consent), the bundling of marketing consent with WiFi access is non-compliant — users cannot be required to consent to marketing as a condition of receiving the service. Second, under Principle 2 (Identifying Purposes), the purposes are not clearly identified at the point of collection; the user must read the full T&Cs to discover the marketing purpose. Third, the consent is not 'meaningful' under the OPC's 2018 guidelines because key elements (what data, why, who gets it) are not prominently displayed. Minimum remediation: redesign the portal with a three-layer architecture, decouple marketing consent into a separate unchecked checkbox, and add a plain-language summary to the splash page. The venue must also implement a consent versioning system and update its Privacy Management Programme documentation.
Q2. You are the IT director of a conference centre in Vancouver. A vendor proposes deploying a WiFi analytics system that tracks the MAC addresses of all devices in the venue — including those that never connect to the WiFi network — to generate session-level movement analytics for exhibitors. The vendor says the data is 'de-identified' because they hash the MAC addresses. Is this deployment compliant with PIPEDA? What additional controls, if any, are required?
💡 Dica:Consider whether hashing alone constitutes de-identification under PIPEDA. Think about the difference between a static hash and a rotating hash, and the concept of re-identification risk.
Mostrar Abordagem Recomendada
The deployment is potentially compliant but requires additional controls. A static hash of a MAC address is not true de-identification under PIPEDA because the same device will always produce the same hash, allowing cross-session tracking and, potentially, re-identification if the hash table is compromised or if the MAC address is known. To achieve genuine de-identification, the hash key must rotate at regular intervals (e.g., every 24 hours), ensuring that the same device cannot be tracked across sessions. Additionally, the venue must post clear, visible signage at all entrances disclosing that WiFi-based analytics are in use, satisfying the Openness principle. The analytics platform must store and display only aggregate, zone-level data — not individual device trajectories. If the vendor intends to share session-level data with exhibitors (third parties), this constitutes a disclosure of personal information and requires explicit consent from users who have connected to the network, or robust anonymisation that makes re-identification 'not reasonably foreseeable.' A Privacy Impact Assessment is strongly recommended before deployment.
Q3. A hotel chain with properties in Ontario, Alberta, and Quebec is standardising its guest WiFi platform. The CTO wants a single consent flow that works across all provinces. The legal team has flagged that Quebec's Law 25 imposes additional requirements. Design the minimum viable consent architecture that satisfies PIPEDA in Ontario and Alberta, Law 25 in Quebec, and is forward-compatible with the incoming CPPA.
💡 Dica:Identify the highest common denominator across all three regimes. Consider language, PIA requirements, consent granularity, and data subject rights.
Mostrar Abordagem Recomendada
The minimum viable architecture should be designed to the highest standard across all applicable regimes, which means treating Law 25 as the baseline. The consent flow must: (1) Present a bilingual (English and French) splash page with a plain-language just-in-time summary; (2) Provide separate, unchecked-by-default checkboxes for WiFi access terms, marketing consent, and analytics profiling; (3) Link to a full privacy policy available in both languages, specifying data categories, purposes, third parties, retention periods, and data subject rights contact; (4) Support data subject rights for access, correction, and deletion — with automated workflows capable of purging records across all systems within 30 days; (5) Implement rotating-hash MAC anonymisation at the edge. Before deploying the system in Quebec, conduct a Privacy Impact Assessment as required by Law 25. For CPPA forward-compatibility, ensure the platform supports data portability export in machine-readable format and can generate audit trails of all consent events. This single architecture satisfies PIPEDA in Ontario and Alberta, Law 25 in Quebec, and is well-positioned for CPPA compliance when the legislation passes.
Q4. Six months after deploying a compliant captive portal, your marketing team wants to add a new integration that sends guest session data (email, visit frequency, dwell time) to a third-party programmatic advertising platform for retargeting campaigns. Existing users consented to the original terms, which did not mention this platform. What are your obligations under PIPEDA before activating this integration?
💡 Dica:Focus on the 'new purpose' requirement under PIPEDA and the OPC's guidance on dynamic consent. Consider what constitutes a 'significant change' to privacy practices.
Mostrar Abordagem Recomendada
Under PIPEDA, sharing personal information with a third-party advertising platform for retargeting constitutes a new purpose that was not anticipated in the original consent. Before activating the integration, you must: (1) Update your privacy policy to disclose the new third party and the retargeting purpose; (2) Notify all existing users of the material change to your privacy practices — this can be done via email to those who provided their address during WiFi sign-up; (3) Obtain fresh consent from existing users for the new purpose before their data is shared with the advertising platform — this means presenting them with a new opt-in opportunity, not assuming their original consent covers the new use; (4) Ensure that users who do not consent to the new purpose continue to receive WiFi access without interruption; (5) Review the data processing agreement with the advertising platform to ensure it includes adequate protections against secondary use by the platform. Failing to obtain fresh consent before activating the integration would constitute a disclosure of personal information for a purpose beyond what was originally consented to — a direct violation of PIPEDA Principle 3.



