Conformità PIPEDA per il WiFi Ospiti in Canada
Questa guida fornisce un riferimento tecnico e operativo definitivo per gli operatori di locali canadesi che implementano il WiFi ospiti ai sensi del PIPEDA. Copre il quadro del consenso significativo dell'OPC, il principio di responsabilità, i precedenti di applicazione delle indagini su Tim Hortons e Google WiFi e le modifiche architettoniche necessarie per soddisfare il prossimo Consumer Privacy Protection Act (CPPA) ai sensi del Bill C-27. I responsabili IT e i responsabili della conformità troveranno specifiche di progettazione del Captive Portal attuabili, requisiti di minimizzazione dei dati e una chiara roadmap per la protezione futura contro sanzioni su scala GDPR.
🎧 Ascolta questa guida
Visualizza trascrizione
- Riepilogo Esecutivo
- Approfondimento Tecnico: PIPEDA e il Captive Portal
- Il Mandato del Consenso Significativo
- Il Precedente Tim Hortons: Un Avvertimento per l'Analisi della Posizione
- Guida all'Implementazione: Costruire un Flusso di Onboarding Conforme
- Fase 1: Minimizzazione dei Dati al Limite
- Fase 2: Architettura dell'interfaccia utente del Captive Portal a strati
- Fase 3: Integrazione API e residenza dei dati
- Fase 4: Conformità bilingue
- Fase 5: Programma di gestione della privacy
- Best practice e preparazione per il futuro per il disegno di legge C-27 (CPPA)
- Risoluzione dei problemi e mitigazione del rischio
- ROI e impatto sul business
- Riferimenti

Riepilogo Esecutivo
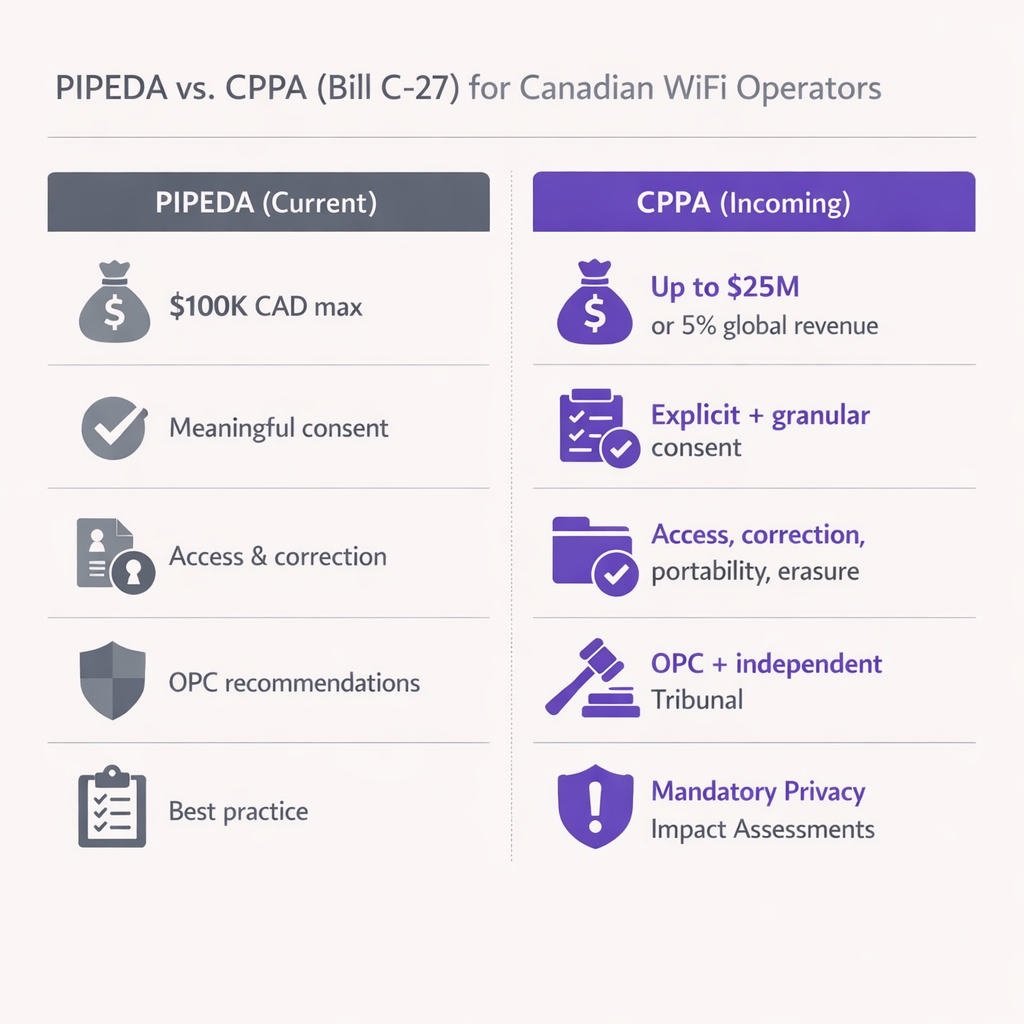
Per gli operatori di locali canadesi e i leader IT, offrire il WiFi ospiti non è più solo una questione di connettività, ma un canale critico per l'acquisizione di dati. Tuttavia, il panorama normativo che disciplina la raccolta e l'utilizzo di tali dati si sta inasprendo. Il Personal Information Protection and Electronic Documents Act (PIPEDA) impone requisiti rigorosi per ottenere il "consenso significativo" prima di raccogliere i dati degli utenti nei Captive Portal. Inoltre, con l'imminente Consumer Privacy Protection Act (CPPA) pronto a introdurre sanzioni in stile GDPR (fino a 25 milioni di CAD o il 5% del fatturato globale), la conformità è ora una priorità di gestione del rischio a livello di consiglio di amministrazione.
Questa guida fornisce una roadmap tecnica e operativa per architetti e responsabili IT che implementano soluzioni Guest WiFi in Canada. Analizziamo la posizione di applicazione dell'Office of the Privacy Commissioner (OPC), i requisiti tecnici per il consenso a più livelli e i passaggi attuabili per rendere la tua architettura di rete a prova di futuro contro i prossimi cambiamenti legislativi. Sia che operiate nel Retail , nell' Hospitality o nel Transport , questo documento traduce gli obblighi legali in specifiche tecniche concrete.
Approfondimento Tecnico: PIPEDA e il Captive Portal
Il PIPEDA si applica alla raccolta, all'uso e alla divulgazione di informazioni personali nel corso di attività commerciali in Canada. Per un Captive Portal WiFi, le "informazioni personali" vanno oltre nomi e indirizzi email; includono indirizzi MAC dei dispositivi, analisi della posizione e comportamento di navigazione. La Legge è strutturata attorno a dieci Principi di Informazione Equa sanciti nell'Allegato 1, di cui il Principio 3 (Consenso), il Principio 2 (Identificazione degli Scopi), il Principio 4 (Limitazione della Raccolta) e il Principio 1 (Responsabilità) sono i più direttamente rilevanti per le implementazioni di WiFi ospiti.
Il Mandato del Consenso Significativo
Le Linee Guida dell'OPC per l'ottenimento del Consenso Significativo, pubblicate congiuntamente con i commissari provinciali di Alberta e British Columbia nel 2018, hanno cambiato radicalmente il modo in cui i locali devono progettare i loro flussi di onboarding. Nascondere le pratiche di raccolta dati in un documento di Termini e Condizioni di 5.000 parole è esplicitamente non conforme. Le linee guida stabiliscono sette principi, di cui tre sono architetturalmente critici per la progettazione del Captive Portal.
Primo, enfasi sugli elementi chiave: la splash page deve mostrare in modo prominente quali dati vengono raccolti, con chi vengono condivisi, gli scopi della raccolta e qualsiasi rischio residuo significativo di danno. Un linguaggio vago come "miglioramento del servizio" è insufficiente — gli scopi devono essere specifici e distinguibili tra quelli integrali alla fornitura del servizio e quelli opzionali.
Secondo, scelta granulare: gli utenti devono essere in grado di acconsentire o rifiutare usi secondari (marketing, profilazione comportamentale, analisi) indipendentemente dal servizio primario (accesso WiFi). Raggruppare il consenso al marketing come condizione per l'accesso alla rete viola direttamente il Principio 3 del PIPEDA, poiché richiede un consenso che va oltre quanto necessario per fornire il servizio.
Terzo, trasparenza dinamica: il consenso non è un evento una tantum. Se aggiorni il tuo motore di WiFi Analytics per tracciare nuove metriche o condividere dati con una nuova terza parte, devi notificare gli utenti esistenti e ottenere un nuovo consenso per il nuovo scopo prima che la modifica abbia effetto.
Il Precedente Tim Hortons: Un Avvertimento per l'Analisi della Posizione
Nel 2022, l'indagine congiunta dell'OPC sull'app mobile di Tim Hortons (PIPEDA Findings #2022-001) ha stabilito un precedente storico per il tracciamento della posizione che ogni team IT di un locale deve comprendere. L'indagine ha rilevato che l'app raccoglieva dati GPS granulari anche quando l'applicazione era chiusa — più di 2.700 volte in meno di cinque mesi per un utente — presumibilmente per pubblicità mirata, uno scopo che non ha mai effettivamente raggiunto. L'OPC ha stabilito che questa raccolta mancava di una "necessità legittima" e che il consenso ottenuto era fuorviante, poiché agli utenti era stato detto che i dati venivano raccolti solo quando l'app era aperta.
Per i team IT dei locali che implementano un Indoor Positioning System: UWB, BLE, & WiFi Guide , la lezione è chiara: non si possono raccogliere troppi dati sulla posizione "per ogni evenienza". Se i tuoi access point sondano indirizzi MAC non associati per generare mappe di calore del traffico pedonale, devi anonimizzare questi dati al limite utilizzando hash crittografici rotanti, o ottenere il consenso esplicito prima che l'utente si associ all'SSID. L'OPC valuterà se lo scopo dichiarato corrisponde all'uso effettivo e se il volume di dati raccolti è proporzionato al beneficio ottenuto.
Guida all'Implementazione: Costruire un Flusso di Onboarding Conforme
L'implementazione di un Captive Portal conforme al PIPEDA richiede il coordinamento tra ingegneria di rete, legale e marketing. Il seguente modello si applica a qualsiasi locale che implementa Guest WiFi in Canada.
Fase 1: Minimizzazione dei Dati al Limite
Configura i tuoi controller WLAN per eliminare i dati di payload non necessari. Come stabilito nell'indagine Google Street View del 2011 (PIPEDA Findings #2011-001), l'acquisizione di dati di payload da reti non crittografate viola il PIPEDA. Assicurati che i tuoi server RADIUS e i gateway Captive Portal registrino solo gli attributi richiesti per la gestione della sessione e le analisi esplicitamente acconsentite. Per l'analisi della presenza basata su indirizzi MAC, implementa una funzione hash rotantea livello di AP o controller in modo che l'indirizzo MAC grezzo non venga mai scritto su memoria persistente.
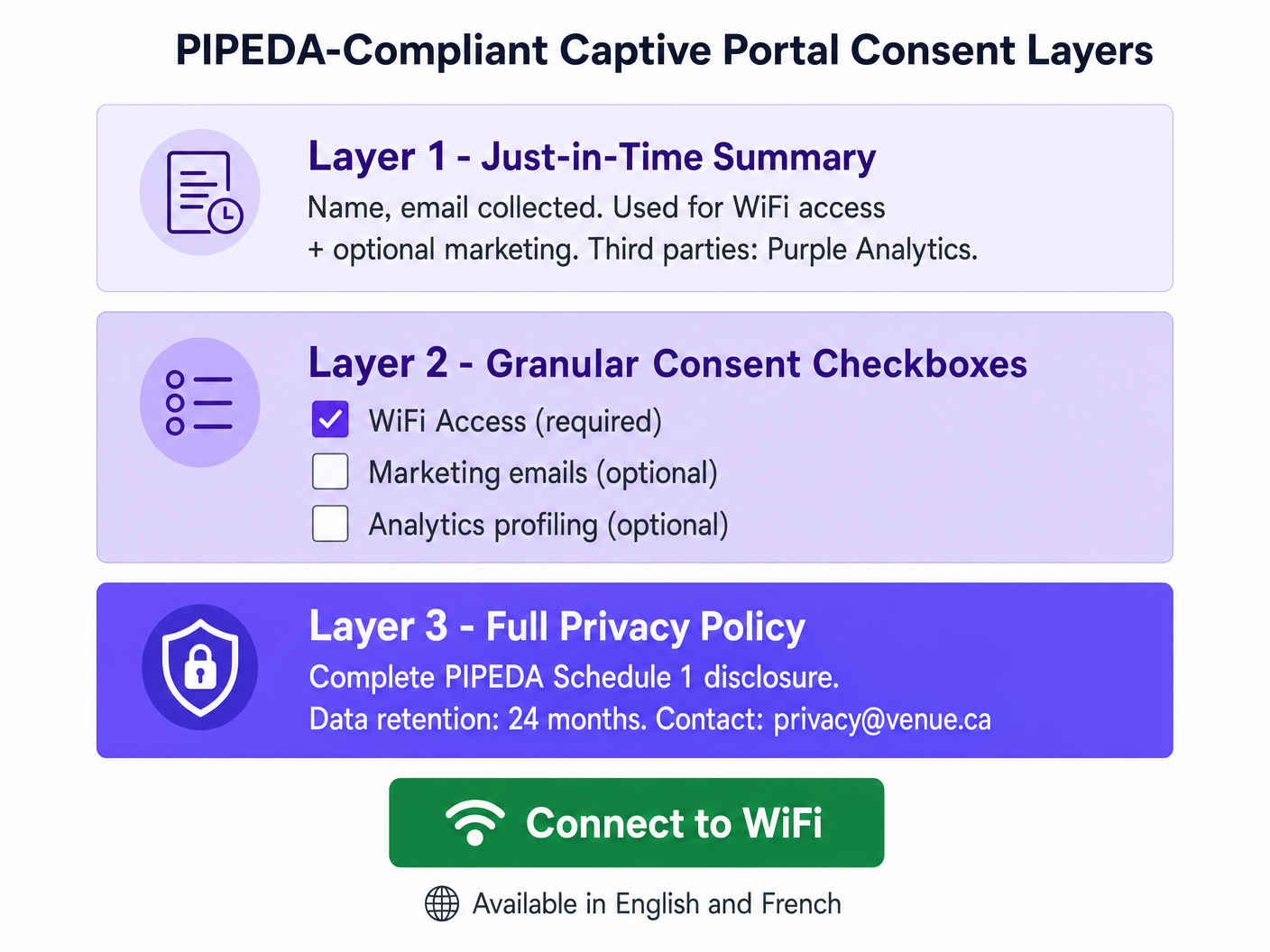
Fase 2: Architettura dell'interfaccia utente del Captive Portal a strati
Progetta la splash page utilizzando un approccio a tre strati allineato con le linee guida sull'informativa a strati dell'OPC. Il Livello 1 (la schermata iniziale) presenta un riepilogo chiaro e in linguaggio semplice: quali dati vengono raccolti, chi li elabora e per quali scopi. Il Livello 2 presenta caselle di controllo per il consenso granulare — deselezionate per impostazione predefinita per tutti gli scopi opzionali — che coprono le comunicazioni di marketing, l'analisi comportamentale e qualsiasi condivisione di dati con terze parti oltre a quanto richiesto per la fornitura del servizio. Il Livello 3 fornisce un collegamento ipertestuale all'informativa sulla privacy completa, ospitata su una pagina sicura e reattiva accessibile da qualsiasi dispositivo. Se il tuo team di marketing ha bisogno di aiuto per scrivere riepiloghi concisi e legalmente validi, considera l'utilizzo di Generative AI for Captive Portal Copy and Creative o, per le implementazioni in lingua francese, IA générative pour le texte et les créatifs de Captive Portal .
Fase 3: Integrazione API e residenza dei dati
Quando integri il tuo captive portal con un CRM o una piattaforma di automazione del marketing, assicurati che i dati fluiscano tramite API sicure e crittografate (TLS 1.2 minimo, TLS 1.3 preferito). Per le implementazioni canadesi, dai priorità ai fornitori che offrono la residenza dei dati locale (ad esempio, AWS Canada Central, ca-central-1) per mitigare i rischi di trasferimento transfrontaliero. Questo è particolarmente critico per le sedi che operano in Quebec ai sensi della Legge 25, che richiede una Valutazione d'Impatto sulla Privacy (PIA) prima di trasferire informazioni personali al di fuori del Quebec e impone che la giurisdizione ricevente offra una protezione equivalente.
Fase 4: Conformità bilingue
Tutte le informative sul consenso, le politiche sulla privacy e le informazioni sui diritti degli interessati devono essere disponibili sia in inglese che in francese per le sedi che operano in Quebec. Questo è un requisito sia della Legge 25 che della Carta della lingua francese del Quebec. Per le sedi federali (aeroporti, stazioni ferroviarie, edifici federali), la fornitura bilingue è un'aspettativa di base ai sensi dell'Official Languages Act.
Fase 5: Programma di gestione della privacy
Il Principio di Responsabilità di PIPEDA (Principio 1) richiede che la tua organizzazione designi un Responsabile della Privacy, mantenga politiche e procedure documentate e sia in grado di dimostrare la conformità all'OPC su richiesta. Per gli operatori multi-sito — come una catena di vendita al dettaglio nazionale con oltre 50 sedi, ognuna delle quali gestisce un captive portal — ciò significa un Programma di Gestione della Privacy (PMP) centralizzato che copra tutti i siti in modo coerente, con registri di audit per gli eventi di consenso, le richieste degli interessati e i programmi di conservazione.
Best practice e preparazione per il futuro per il disegno di legge C-27 (CPPA)
Mentre il disegno di legge C-27 — il Consumer Privacy Protection Act — si è bloccato a causa della proroga del Parlamento nel gennaio 2025, i suoi principi fondamentali rappresentano l'inevitabile futuro della legge canadese sulla privacy. All'inizio del 2026, si prevede che un nuovo disegno di legge federale sulla privacy, che incorpora molte disposizioni del CPPA, sarà introdotto in Parlamento. L'approccio prudente è trattare i controlli a livello di CPPA come il tuo obiettivo di implementazione oggi.
I cambiamenti più significativi a cui prepararsi sono i seguenti. L'escalation delle sanzioni è la preoccupazione più immediata: il CPPA introdurrebbe multe fino a 25 milioni di CAD o il 5% del fatturato annuo globale, un cambiamento significativo rispetto al massimo attuale di 100.000 CAD di PIPEDA. Le Valutazioni d'Impatto sulla Privacy obbligatorie saranno richieste per le attività di trattamento ad alto rischio, inclusi gli analytics di localizzazione, la profilazione comportamentale e qualsiasi trattamento che coinvolga informazioni personali sensibili. I diritti espliciti alla portabilità e alla cancellazione dei dati richiederanno flussi di lavoro automatizzati in grado di eliminare il record di un utente da tutti i sistemi — database locale, cloud controller, CRM a valle — entro una finestra di risposta definita. Gli standard di de-identificazione diventeranno più prescrittivi; assicurati che la tua piattaforma di analytics esegua l'hashing degli indirizzi MAC utilizzando salt rotanti e che la re-identificazione sia tecnicamente infattibile.
Per gli operatori di strutture sanitarie, l'intersezione tra gli analytics WiFi e i dati dei pazienti crea obblighi aggiuntivi ai sensi di PIPEDA e della legislazione provinciale sulla privacy sanitaria. Consulta le nostre linee guida del settore Healthcare per considerazioni specifiche sull'implementazione nel settore.
Risoluzione dei problemi e mitigazione del rischio
Modalità di errore: Il portale tutto o niente. Molte implementazioni legacy di captive portal presentano un unico pulsante "Accetto" che raggruppa l'accesso WiFi, il consenso al marketing e la profilazione analitica in un solo clic. Questa è una violazione diretta di PIPEDA e la modalità di errore più comune che l'OPC riscontra nelle denunce. La mitigazione è semplice: disaccoppiare l'autenticazione di rete dagli opt-in di marketing utilizzando caselle di controllo separate e chiaramente etichettate. L'accesso alla rete dovrebbe essere concedibile senza alcun consenso secondario.
Modalità di errore: Tracciamento MAC silenzioso. Alcune implementazioni registrano gli indirizzi MAC dei dispositivi che passano davanti alla sede ma non si connettono mai all'SSID, utilizzando questi dati per generare analytics sul traffico pedonale. Ai sensi di PIPEDA, ciò costituisce la raccolta di informazioni personali senza conoscenza o consenso. La mitigazione consiste nell'implementare il supporto alla randomizzazione MAC a livello di AP e garantire che tutti i dashboard di analytics di presenza aggreghino e anonimizzino i dati prima dell'archiviazione. Gli indirizzi MAC grezzi dei dispositivi non associati non devono mai essere scritti su memoria persistente.
Modalità di errore: Consenso obsoleto. Una sede implementa un captive portal conforme, poi sei mesi dopo aggiunge una nuova integrazione di analytics che invia i dati di sessione a una piattaforma pubblicitaria di terze parti. Gli utenti esistenti che hanno acconsentito ai termini originali non hanno acconsentito a questa nuova divulgazione. Ciò viola il requisito di PIPEDA di ottenere il consenso prima di qualsiasi nuovo scopo. La mitigazione consiste nell'implementare un sistema di versioning del consenso che attiviun prompt di nuovo consenso per gli utenti esistenti quando vengono apportate modifiche sostanziali alle attività di trattamento dei dati.
Modalità di fallimento: Contratti con terze parti inadeguati. Come evidenziato nell'indagine su Tim Hortons, un linguaggio contrattuale vago con fornitori di servizi terzi — che consente loro di utilizzare i dati per i propri scopi — non costituisce una protezione adeguata. Assicurarsi che tutti gli accordi sul trattamento dei dati con fornitori di analisi, provider CRM e piattaforme di marketing includano restrizioni esplicite sull'uso secondario, limiti di conservazione dei dati e controlli sui sub-processori.
ROI e impatto sul business
La conformità non è un centro di costo — è un moltiplicatore di fiducia con risultati commerciali misurabili. Le sedi che implementano flussi di consenso trasparenti e incentrati sull'utente riportano costantemente tassi di adesione più elevati per i programmi di marketing perché gli utenti si sentono in controllo dei propri dati. Un Captive Portal ben progettato e conforme a PIPEDA che spiega chiaramente lo scambio di valore — WiFi gratuito in cambio di un indirizzo email e consenso marketing opzionale — converte a tassi significativamente più alti rispetto a un portale che nasconde il consenso in un linguaggio legale.
Dal punto di vista della mitigazione del rischio, il calcolo finanziario è semplice. Una singola azione di applicazione dell'OPC, anche sotto il massimo attuale di $100K di PIPEDA, genera danni reputazionali significativi e costi legali che superano di gran lunga l'investimento in una distribuzione conforme. Sotto il regime CPPA in arrivo, l'esposizione finanziaria si estende a livelli che minacciano l'impresa. La standardizzazione su una piattaforma di livello enterprise come Purple, che fornisce gestione centralizzata del consenso, tracce di audit e flussi di lavoro automatizzati per le richieste degli interessati, riduce il sovraccarico operativo della gestione della conformità alla privacy in una proprietà multi-sito e fornisce la traccia di prove documentate che l'OPC si aspetta di vedere.
Per gli operatori di trasporto che considerano implementazioni di veicoli connessi e WiFi in transito, si applicano gli stessi principi PIPEDA. Consulta la nostra guida su La tua guida alle soluzioni Wi-Fi in auto per le aziende per considerazioni specifiche sull'implementazione.
Riferimenti
[1] Ufficio del Commissario per la Privacy del Canada. "Legge sulla protezione delle informazioni personali e dei documenti elettronici (PIPEDA)." priv.gc.ca.
[2] Ufficio del Commissario per la Privacy del Canada. "Linee guida per ottenere un consenso significativo." priv.gc.ca, maggio 2018.
[3] Ufficio del Commissario per la Privacy del Canada. "Principi di informazione equa PIPEDA — Allegato 1." priv.gc.ca.
[4] Ufficio del Commissario per la Privacy del Canada. "Indagine congiunta sul tracciamento della posizione tramite l'app Tim Hortons (Risultati PIPEDA #2022-001)." priv.gc.ca, giugno 2022.
[5] Ufficio del Commissario per la Privacy del Canada. "Rapporto sui risultati: Raccolta dati WiFi di Google Inc. (Risultati PIPEDA #2011-001)." priv.gc.ca, 2011.
[6] Commission d'accès à l'information du Québec. "Legge 25: Legge per modernizzare le disposizioni legislative in materia di protezione delle informazioni personali." cai.gouv.qc.ca.
[7] IAPP. "Cosa potrebbe portare il 2026 per gli sforzi di riforma della privacy in Canada." iapp.org, febbraio 2026.
Termini chiave e definizioni
PIPEDA (Personal Information Protection and Electronic Documents Act)
Canada's federal private-sector privacy law governing the collection, use, and disclosure of personal information in commercial activities. Structured around ten Fair Information Principles in Schedule 1. Applies to all provinces except Alberta, British Columbia, and Quebec, which have substantially similar provincial legislation.
The primary compliance framework for any Canadian venue offering guest WiFi. IT teams encounter PIPEDA when designing captive portals, configuring analytics platforms, and responding to data subject requests.
Meaningful Consent
The OPC's standard for valid consent under PIPEDA, requiring that individuals genuinely understand what they are consenting to — specifically: what data is collected, who receives it, the purposes of collection, and any meaningful risks of harm. Consent buried in lengthy T&Cs, or obtained through a single bundled 'I Accept' button, does not meet this standard.
The central compliance requirement for captive portal design. Every element of the splash page UI must be evaluated against this standard.
Captive Portal
A network gateway that intercepts HTTP/HTTPS traffic from newly associated WiFi clients and redirects them to a web page for authentication, consent collection, and/or payment before granting internet access. Technically implemented via WLAN controller redirect rules, DNS spoofing, or a dedicated gateway appliance.
The primary point of consent collection for guest WiFi deployments. The design of the captive portal UI directly determines PIPEDA compliance status.
MAC Address (Media Access Control Address)
A 48-bit hardware identifier assigned to a network interface controller, used to uniquely identify a device at the data link layer (Layer 2). Under PIPEDA, MAC addresses are personal information because they can be used to identify an individual's device and, by extension, their movements and behaviour.
Encountered in WiFi analytics deployments, probe-based footfall counting, and session logging. Must be anonymised or handled with explicit consent.
OPC (Office of the Privacy Commissioner of Canada)
The independent federal authority responsible for overseeing compliance with PIPEDA and the Privacy Act. The OPC investigates complaints, conducts audits, publishes guidance, and can apply to the Federal Court to enforce its recommendations. Current maximum fine under PIPEDA is $100,000 CAD per violation.
The primary regulatory body IT teams must satisfy. OPC findings are publicly published and serve as binding precedents for compliance interpretation.
CPPA (Consumer Privacy Protection Act)
The proposed replacement for PIPEDA, introduced as part of Bill C-27 in 2022. Would introduce GDPR-scale penalties (up to $25M CAD or 5% of global revenue), mandatory Privacy Impact Assessments, explicit data portability and erasure rights, and a new independent enforcement tribunal. Bill C-27 stalled due to parliamentary prorogation in January 2025; a successor bill is anticipated in 2026.
The future compliance target for Canadian venue operators. IT teams should begin implementing CPPA-level controls now to avoid costly remediation when the legislation passes.
Law 25 (Quebec Act to Modernize Legislative Provisions as Regards the Protection of Personal Information)
Quebec's provincial privacy legislation, which imposes requirements that exceed PIPEDA. Key provisions include mandatory Privacy Impact Assessments before new projects involving personal information, explicit consent for cross-border data transfers, French-language consent notices, and fines up to $25M CAD or 10% of worldwide turnover. Fully in force as of September 2023.
Applies to all venues operating in Quebec. IT teams must implement enhanced consent flows, bilingual notices, and PIAs for any Quebec deployment.
Privacy Impact Assessment (PIA)
A structured risk assessment process that evaluates the privacy implications of a new project, system, or data processing activity before deployment. Identifies data flows, assesses risks to individuals, and documents mitigation measures. Currently a best practice under PIPEDA; mandatory under Quebec's Law 25 for new projects involving personal information; expected to become mandatory federally under the CPPA.
Required before deploying new analytics features, location tracking systems, or third-party data integrations. Provides the documented evidence trail the OPC expects to see in an enforcement scenario.
Layered Notice
A consent architecture that presents privacy information at multiple levels of detail: a brief, prominent summary for the average user; granular options for those who want more control; and a full privacy policy for those who want complete information. Recommended by the OPC as the preferred method for obtaining meaningful consent in digital environments.
The architectural pattern that all PIPEDA-compliant captive portals should implement. Directly addresses the OPC's concern that information buried in lengthy T&Cs is functionally invisible to users.
Accountability Principle (PIPEDA Schedule 1, Principle 1)
The requirement that an organisation is responsible for personal information under its control and must designate an individual (a Privacy Officer) accountable for compliance. Includes implementing policies and practices, training staff, and being able to demonstrate compliance to the OPC on request.
The organisational governance requirement that underpins all other PIPEDA compliance activities. Multi-site venue operators must have a documented Privacy Management Programme covering all locations.
Casi di studio
A 300-room hotel in Toronto wants to offer free guest WiFi and use sign-up data to drive repeat bookings and promotional email campaigns. The hotel's current captive portal uses a single 'I Accept' button that links to a 4,000-word Terms and Conditions document. The IT director has been asked to assess compliance risk and redesign the flow before the next OPC audit cycle.
The existing single-button flow is non-compliant and must be replaced with a three-layer architecture. On the WLAN controller (e.g., Cisco Catalyst Centre or Aruba Central), configure the captive portal redirect to the new splash page hosted over HTTPS. Layer 1 of the splash page presents a plain-language summary panel: 'We collect your name, email address, and device identifier to provide WiFi access. We share this data with Purple (our WiFi analytics provider). You can optionally receive promotional emails from us.' Layer 2 presents two checkboxes: Checkbox A (pre-checked, mandatory): 'I agree to the WiFi Terms of Use and Privacy Policy.' Checkbox B (unchecked, optional): 'I would like to receive promotional offers and news from [Hotel Name].' Layer 3 provides a hyperlink 'Full Privacy Policy' opening the complete PIPEDA-compliant policy in a new tab. The policy must specify: data categories collected (name, email, MAC address, session timestamps), purposes (WiFi access delivery; marketing if opted-in), third parties (Purple, email marketing platform), retention period (12 months for marketing, 90 days for session logs), and a privacy contact email. The hotel must also configure its CRM integration to tag records with consent status, so that only users who checked Checkbox B receive marketing communications. Implement a consent versioning system so that if the hotel adds a new analytics partner in future, existing users are prompted to re-consent.
A large shopping centre operator in Montreal wants to deploy a WiFi analytics system to generate zone-level footfall heatmaps across 120,000 square feet of retail space. The proposed system uses WiFi probe requests from unassociated devices (i.e., phones that have not connected to the network) to estimate visitor counts and dwell times. The CTO wants to understand the PIPEDA and Law 25 compliance requirements before procurement.
This deployment involves processing personal information (MAC addresses are personal information under PIPEDA) without the knowledge or consent of the individuals whose devices are being probed. Under both PIPEDA and Quebec's Law 25, this requires careful architectural controls. The compliant approach is as follows: First, conduct a Privacy Impact Assessment (PIA) before procurement, as required by Law 25 for any new project involving personal information. The PIA must assess the necessity and proportionality of the data collection. Second, implement MAC address anonymisation at the access point or controller level using a rotating cryptographic hash (e.g., HMAC-SHA256 with a key that rotates every 24 hours). This ensures that the same device cannot be tracked across days, and that the raw MAC address is never written to persistent storage. Third, configure the analytics platform to store and display only aggregate, zone-level counts — not individual device trajectories. The dashboard should show 'Zone A: 450 visitors, avg dwell 8 minutes' rather than individual movement paths. Fourth, post clear, visible signage at all venue entrances disclosing that WiFi-based analytics are in use for footfall measurement, with a QR code linking to the full privacy notice. This satisfies the 'openness' principle and provides constructive notice. Fifth, for the connected WiFi network (the SSID guests can join), implement a standard three-layer captive portal as described in the hotel scenario above. The Law 25 requirement for French-language consent notices applies to all captive portal text.
A national retail chain with 85 stores across Canada is preparing for the incoming CPPA regime. Their current PIPEDA compliance is adequate, but the CTO wants to understand what architectural changes are needed to meet CPPA-level requirements, particularly around data subject rights, de-identification, and the increased penalty exposure.
The transition from PIPEDA to CPPA compliance requires three primary architectural investments. First, implement automated data subject rights workflows. The CPPA introduces explicit rights to data portability and erasure. The chain's WiFi platform must expose an API endpoint that, when triggered by a verified data subject request, can: (a) export all personal data associated with a given email address or device identifier in a machine-readable format (JSON or CSV); and (b) purge that record from the local captive portal database, the cloud analytics platform, and all downstream CRM and marketing automation systems simultaneously. This must be achievable within a defined SLA — 30 days is the CPPA's proposed response window. Second, upgrade de-identification protocols. Current PIPEDA guidance on de-identified data is relatively permissive. The CPPA will introduce a higher bar: de-identified data must be processed in a manner that makes re-identification 'not reasonably foreseeable.' For MAC-based analytics, this means implementing rotating hash keys (as described above) and ensuring that the analytics platform cannot be used to re-identify individuals even by the operator. Third, conduct mandatory Privacy Impact Assessments for all high-risk processing activities. For a retail chain, this includes any deployment involving location analytics, behavioural profiling for targeted advertising, or data sharing with advertising technology platforms. PIAs should be documented and retained as evidence of accountability. The chain should also review all third-party data processing agreements and update them to include CPPA-compliant clauses covering data retention, sub-processor restrictions, and breach notification timelines.
Analisi degli scenari
Q1. Your venue's current captive portal collects name, email, and device MAC address. The splash page has a single 'Connect to WiFi' button that, when clicked, is deemed acceptance of the Terms and Conditions (which include consent to receive marketing emails). A user complains to the OPC. What specific PIPEDA violations has your venue committed, and what is the minimum remediation required?
💡 Suggerimento:Consider PIPEDA Principles 1, 2, 3, and 4. Focus on the bundling of consent and the adequacy of the notice provided.
Mostra l'approccio consigliato
The venue has committed at least three violations. First, under Principle 3 (Consent), the bundling of marketing consent with WiFi access is non-compliant — users cannot be required to consent to marketing as a condition of receiving the service. Second, under Principle 2 (Identifying Purposes), the purposes are not clearly identified at the point of collection; the user must read the full T&Cs to discover the marketing purpose. Third, the consent is not 'meaningful' under the OPC's 2018 guidelines because key elements (what data, why, who gets it) are not prominently displayed. Minimum remediation: redesign the portal with a three-layer architecture, decouple marketing consent into a separate unchecked checkbox, and add a plain-language summary to the splash page. The venue must also implement a consent versioning system and update its Privacy Management Programme documentation.
Q2. You are the IT director of a conference centre in Vancouver. A vendor proposes deploying a WiFi analytics system that tracks the MAC addresses of all devices in the venue — including those that never connect to the WiFi network — to generate session-level movement analytics for exhibitors. The vendor says the data is 'de-identified' because they hash the MAC addresses. Is this deployment compliant with PIPEDA? What additional controls, if any, are required?
💡 Suggerimento:Consider whether hashing alone constitutes de-identification under PIPEDA. Think about the difference between a static hash and a rotating hash, and the concept of re-identification risk.
Mostra l'approccio consigliato
The deployment is potentially compliant but requires additional controls. A static hash of a MAC address is not true de-identification under PIPEDA because the same device will always produce the same hash, allowing cross-session tracking and, potentially, re-identification if the hash table is compromised or if the MAC address is known. To achieve genuine de-identification, the hash key must rotate at regular intervals (e.g., every 24 hours), ensuring that the same device cannot be tracked across sessions. Additionally, the venue must post clear, visible signage at all entrances disclosing that WiFi-based analytics are in use, satisfying the Openness principle. The analytics platform must store and display only aggregate, zone-level data — not individual device trajectories. If the vendor intends to share session-level data with exhibitors (third parties), this constitutes a disclosure of personal information and requires explicit consent from users who have connected to the network, or robust anonymisation that makes re-identification 'not reasonably foreseeable.' A Privacy Impact Assessment is strongly recommended before deployment.
Q3. A hotel chain with properties in Ontario, Alberta, and Quebec is standardising its guest WiFi platform. The CTO wants a single consent flow that works across all provinces. The legal team has flagged that Quebec's Law 25 imposes additional requirements. Design the minimum viable consent architecture that satisfies PIPEDA in Ontario and Alberta, Law 25 in Quebec, and is forward-compatible with the incoming CPPA.
💡 Suggerimento:Identify the highest common denominator across all three regimes. Consider language, PIA requirements, consent granularity, and data subject rights.
Mostra l'approccio consigliato
The minimum viable architecture should be designed to the highest standard across all applicable regimes, which means treating Law 25 as the baseline. The consent flow must: (1) Present a bilingual (English and French) splash page with a plain-language just-in-time summary; (2) Provide separate, unchecked-by-default checkboxes for WiFi access terms, marketing consent, and analytics profiling; (3) Link to a full privacy policy available in both languages, specifying data categories, purposes, third parties, retention periods, and data subject rights contact; (4) Support data subject rights for access, correction, and deletion — with automated workflows capable of purging records across all systems within 30 days; (5) Implement rotating-hash MAC anonymisation at the edge. Before deploying the system in Quebec, conduct a Privacy Impact Assessment as required by Law 25. For CPPA forward-compatibility, ensure the platform supports data portability export in machine-readable format and can generate audit trails of all consent events. This single architecture satisfies PIPEDA in Ontario and Alberta, Law 25 in Quebec, and is well-positioned for CPPA compliance when the legislation passes.
Q4. Six months after deploying a compliant captive portal, your marketing team wants to add a new integration that sends guest session data (email, visit frequency, dwell time) to a third-party programmatic advertising platform for retargeting campaigns. Existing users consented to the original terms, which did not mention this platform. What are your obligations under PIPEDA before activating this integration?
💡 Suggerimento:Focus on the 'new purpose' requirement under PIPEDA and the OPC's guidance on dynamic consent. Consider what constitutes a 'significant change' to privacy practices.
Mostra l'approccio consigliato
Under PIPEDA, sharing personal information with a third-party advertising platform for retargeting constitutes a new purpose that was not anticipated in the original consent. Before activating the integration, you must: (1) Update your privacy policy to disclose the new third party and the retargeting purpose; (2) Notify all existing users of the material change to your privacy practices — this can be done via email to those who provided their address during WiFi sign-up; (3) Obtain fresh consent from existing users for the new purpose before their data is shared with the advertising platform — this means presenting them with a new opt-in opportunity, not assuming their original consent covers the new use; (4) Ensure that users who do not consent to the new purpose continue to receive WiFi access without interruption; (5) Review the data processing agreement with the advertising platform to ensure it includes adequate protections against secondary use by the platform. Failing to obtain fresh consent before activating the integration would constitute a disclosure of personal information for a purpose beyond what was originally consented to — a direct violation of PIPEDA Principle 3.



