Airport WiFi Security: How to Protect Passengers on Public Networks
This technical reference guide details the specific threat landscape of airport WiFi, covering Evil Twin access points, rogue hardware, and Man-in-the-Middle attacks. It provides IT managers, network architects, and venue operations directors with actionable architectural strategies — including WPA3 implementation, VLAN segmentation, WIPS deployment, and GDPR-compliant captive portal design — to protect passengers and enterprise infrastructure at scale. Purple's guest WiFi and analytics platform is mapped concretely to each problem domain throughout.
🎧 Listen to this Guide
View Transcript
- Executive Summary
- Technical Deep-Dive: The Airport WiFi Threat Landscape
- Evil Twin Access Points
- Rogue Access Points
- Man-in-the-Middle Attacks
- Implementation Guide: Secure Architecture
- Layer 1: Encryption and Authentication Standards
- Layer 2: Network Segmentation and Client Isolation
- Layer 3: Wireless Intrusion Detection and Prevention (WIDS/WIPS)
- Layer 4: DNS Filtering and Secure Captive Portal Design
- Layer 5: Analytics, Monitoring, and Continuous Improvement
- Best Practices and Risk Mitigation
- ROI and Business Impact
Executive Summary
For CTOs and IT directors managing high-density public environments, the question "is airport wifi safe" is not a consumer query — it is a compliance and infrastructure challenge with direct liability implications. Airport networks present a uniquely volatile attack surface: thousands of transient connections per hour, diverse device types spanning consumer mobiles to enterprise laptops, and the commingling of guest, staff, retail tenant, and operational technology traffic on infrastructure that is often years behind the current security standard.
The primary threats — Evil Twin Access Points (APs) and rogue hardware installations — are low-cost, high-impact attacks that require minimal technical sophistication to execute. Left unaddressed, they expose passengers to credential theft and financial fraud, and expose the airport operator to GDPR enforcement action and reputational damage. By implementing WPA3 with Opportunistic Wireless Encryption, enforcing strict VLAN segmentation, deploying Wireless Intrusion Prevention Systems (WIPS), and integrating a secure, GDPR-compliant Guest WiFi platform, venue operators can secure passenger data while maintaining seamless connectivity. Purple's WiFi Analytics layer adds operational intelligence on top of this security foundation, converting secure onboarding into measurable commercial ROI.
Technical Deep-Dive: The Airport WiFi Threat Landscape
Airport environments are among the most targeted public spaces for wireless attacks. The combination of high passenger volumes, a transient user base that is unlikely to report issues, and the presence of corporate travellers transmitting sensitive data creates an ideal environment for malicious actors. Understanding the specific threat vectors is the prerequisite to designing an effective countermeasure architecture.

Evil Twin Access Points
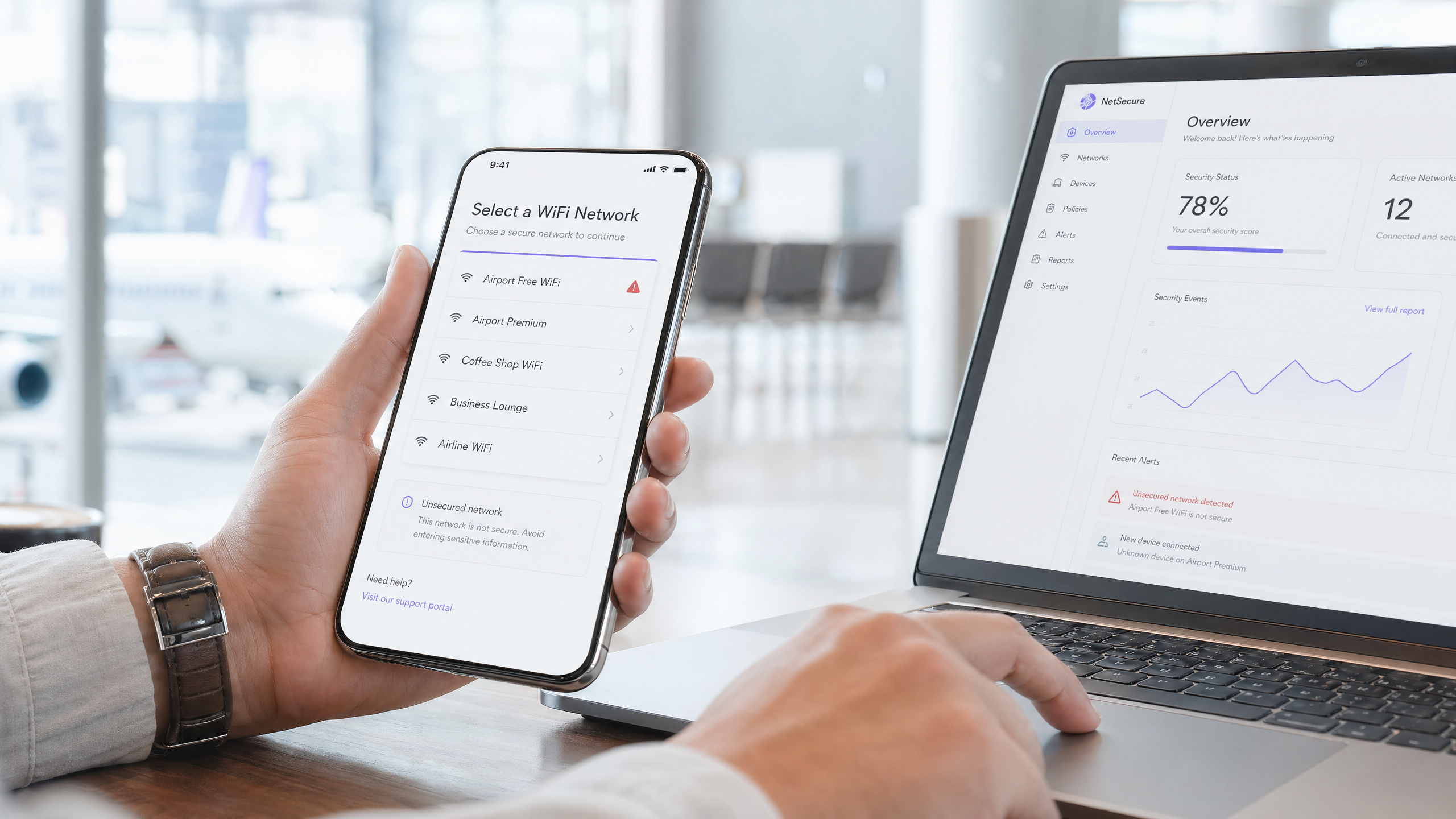
An Evil Twin is a malicious AP configured to broadcast the exact Service Set Identifier (SSID) of the legitimate airport network — for example, "Airport Free WiFi" or "LHR_Passenger_WiFi". Because standard client devices implement automatic network selection based on SSID matching and signal strength, a passenger's device will preferentially connect to the Evil Twin if it presents a stronger signal than the legitimate infrastructure. This is trivially achievable: a portable router broadcasting at maximum power from a nearby seat will outcompete a ceiling-mounted enterprise AP operating at regulated power levels.
Once a client connects to the Evil Twin, the attacker can execute several attack classes. Passive interception captures unencrypted HTTP traffic, DNS queries, and session cookies. SSL stripping downgrades HTTPS connections to HTTP in real time, exposing credentials on sites that do not enforce HTTP Strict Transport Security (HSTS). DNS spoofing redirects users to phishing pages that mimic banking portals or airline booking systems. The passenger sees a normal-looking connection with no warning indicators, because the Evil Twin is providing genuine internet access via its own upstream connection — the attack is entirely transparent to the end user.
The operational cost to an attacker is minimal: a consumer-grade travel router, a laptop running open-source tools, and a seat in the departure lounge. The attack requires no physical access to the airport's infrastructure.
Rogue Access Points
Rogue APs are unauthorised devices physically connected to the airport's wired network infrastructure. Unlike Evil Twins, which operate entirely over the air, rogue APs represent an insider threat vector — they require physical access to a network port. However, in a large airport environment with hundreds of retail concessions, service contractors, and cleaning staff, physical access to network ports is not difficult to obtain.
The most common source of rogue APs is not malicious actors but well-intentioned staff. A retail concessionaire in Terminal 3 experiencing poor WiFi coverage purchases a consumer-grade router and plugs it into the ethernet port behind their counter. The router broadcasts its own SSID, bypasses the enterprise firewall, Network Access Control (NAC) policies, and WPA3 enterprise configurations, and creates a direct, unmanaged pathway from the public internet into the airport's internal network. From that point, any device connected to the rogue AP — whether the concessionaire's POS terminal or a passenger who happens to connect — has potential network-level access to systems that should be entirely isolated.
For Transport operators and airport IT teams, the rogue AP problem is compounded by the scale of the environment. A major international airport may have hundreds of network ports distributed across terminals, retail units, lounges, and back-of-house areas. Manual auditing is impractical without automated detection tooling.
Man-in-the-Middle Attacks
Both Evil Twin and rogue AP scenarios enable Man-in-the-Middle (MitM) attacks, where the attacker positions themselves between the client device and the legitimate network. In a MitM scenario, the attacker can intercept, read, and modify traffic in both directions. Modern TLS encryption significantly reduces the impact of MitM attacks on HTTPS traffic, but the attack surface remains significant: unencrypted protocols, misconfigured TLS implementations, and the use of legacy applications that do not enforce certificate validation all create exploitable gaps.
For corporate travellers — a significant proportion of airport WiFi users — MitM attacks targeting VPN credential capture or corporate email session hijacking represent a high-value attack vector that extends the blast radius well beyond the individual passenger.
Implementation Guide: Secure Architecture
Addressing the airport WiFi threat landscape requires a layered, defence-in-depth architecture. No single control is sufficient; the goal is to make each successive layer of attack progressively more difficult and detectable.
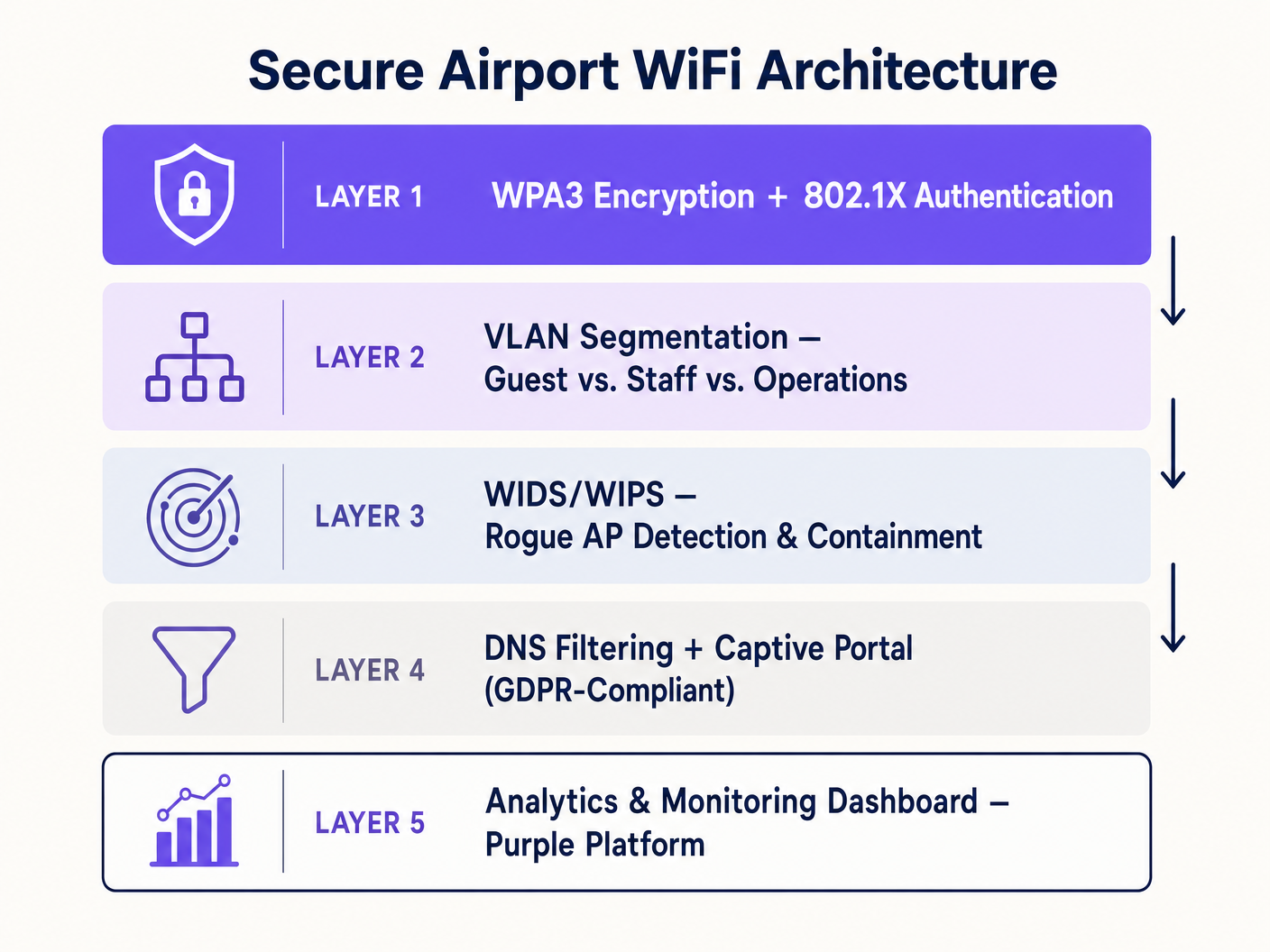
Layer 1: Encryption and Authentication Standards
The transition to WPA3 is the foundational requirement. For open public networks, WPA3 introduces Opportunistic Wireless Encryption (OWE), defined in IEEE 802.11-2020. OWE provides individualised encryption for each client session without requiring a shared password or pre-shared key. Each client-AP association negotiates a unique Diffie-Hellman key exchange, meaning that even if an attacker captures the raw radio frequency traffic for the entire terminal, they cannot decrypt any individual session. This directly mitigates passive eavesdropping and eliminates the primary attack vector of open network interception.
For authenticated network segments — staff, operations, retail tenants — IEEE 802.1X with RADIUS authentication is the correct standard. 802.1X enforces per-device authentication before network access is granted, with each authentication event logged for compliance and audit purposes. Combined with certificate-based Extensible Authentication Protocol (EAP-TLS), this eliminates credential-based attacks against the staff network entirely.
For venues exploring seamless passenger onboarding, OpenRoaming — the Wireless Broadband Alliance's federated identity standard — provides profile-based authentication that connects passengers automatically to verified networks without manual SSID selection. Purple operates as a free identity provider within the OpenRoaming ecosystem under its Connect licence, enabling airports to offer seamless, secure connectivity that removes the human error element of network selection. This is directly relevant to the Evil Twin threat: if a passenger's device connects automatically via a verified profile, it will not connect to an Evil Twin broadcasting the same SSID.
Layer 2: Network Segmentation and Client Isolation
Guest traffic must be completely isolated from operational technology (OT), staff networks, and retail point-of-sale (POS) systems using strict VLAN tagging at the AP level. A minimum segmentation model for an airport environment should include: a Public Guest VLAN (internet access only, no internal routing), a Staff VLAN (authenticated via 802.1X, access to internal systems), a Retail Tenant VLAN (isolated from both guest and staff, internet access for POS systems), and an Operations VLAN (air-gapped or strictly firewalled, for digital signage, building management, and airside systems).
Client isolation — Layer 2 isolation between devices on the same VLAN — must be enabled on the Guest VLAN. Without client isolation, two passengers connected to the same guest network can communicate directly at the IP layer, enabling device-to-device attacks. This is a configuration setting on the wireless controller that is frequently overlooked in legacy deployments.
For Hospitality and Retail environments operating within airport terminals, the same segmentation principles apply. A hotel airside lounge or a retail concession must be treated as an untrusted network segment, regardless of the commercial relationship with the airport operator.
Layer 3: Wireless Intrusion Detection and Prevention (WIDS/WIPS)
A Wireless Intrusion Prevention System is the primary automated defence against both Evil Twin and rogue AP threats. The WIPS must be configured to continuously scan the radio frequency environment across all channels and bands (2.4 GHz, 5 GHz, and 6 GHz for Wi-Fi 6E deployments) for unauthorised SSIDs, MAC address spoofing, and deauthentication flood attacks.
Upon detecting an Evil Twin — identified by an SSID match combined with a BSSID that does not correspond to any authorised AP in the managed infrastructure — the WIPS should automatically deploy containment. Containment involves transmitting targeted IEEE 802.11 de-authentication frames to clients attempting to associate with the malicious AP, preventing successful connection. This is automated response at machine speed, far faster than any human operator could intervene.
For rogue AP detection, the WIPS correlates over-the-air observations with the wired network topology. An AP detected broadcasting over the air that also appears as a connected device on the wired network — but is not in the authorised AP inventory — is flagged as a rogue. The system can then trigger automated port shutdown on the managed switch to physically disconnect the device.
Layer 4: DNS Filtering and Secure Captive Portal Design
DNS-level filtering provides a critical control for protecting users from malicious domains, regardless of the device's own security posture. By routing all DNS queries through a filtering resolver, the network can block resolution of known phishing domains, command-and-control infrastructure, and malware distribution sites. This is particularly valuable in an airport context where passengers may be connecting compromised devices that were infected prior to arrival.
As detailed in our guide on Protect Your Network with Strong DNS and Security , implementing DNS over HTTPS (DoH) or DNS over TLS (DoT) for the resolver connection prevents DNS queries from being intercepted or spoofed in transit — a relevant consideration when WIPS containment may not catch every Evil Twin immediately.
The captive portal is the passenger's primary onboarding touchpoint and must be designed with security as a first-order requirement, not an afterthought. The portal must be served over HTTPS with a valid certificate from a trusted Certificate Authority. The onboarding form must collect only the data required for the stated purpose (GDPR Article 5 data minimisation principle), with explicit, granular consent mechanisms for any marketing use. Purple's captive portal platform is purpose-built for this compliance requirement, providing GDPR-compliant data capture, consent management, and seamless integration with the analytics layer. For context on how this scales across multi-terminal airport environments, see Airport WiFi: How Operators Deliver Connectivity Across Terminals and the Italian-language equivalent at WiFi Aeroportuale .
Layer 5: Analytics, Monitoring, and Continuous Improvement
Security is not a one-time deployment; it requires continuous monitoring and iterative improvement. Purple's WiFi Analytics platform provides the operational visibility layer that transforms raw connection data into actionable intelligence. By monitoring device connection patterns, dwell times, and session anomalies, network operations teams can identify indicators of compromise — unusual connection spikes, devices connecting from unexpected physical locations, or authentication failure patterns that suggest a scanning attack.
The analytics layer also provides the commercial justification for the security investment. Higher passenger opt-in rates — driven by a trusted, secure onboarding experience — generate richer first-party data sets. This data enables targeted marketing, retail footfall analysis, and terminal layout optimisation, delivering measurable ROI on the infrastructure investment. For Healthcare environments operating WiFi in airport medical facilities, the same analytics framework applies with additional GDPR special category data controls.
Best Practices and Risk Mitigation
Enforce Retail Tenant Network Policies at the Technical Level. Policy documents are insufficient. Retail concessions must be provided with managed, segmented network access — a dedicated VLAN with internet access and no internal routing — and the physical network ports in their units must be configured to reject unauthorised hardware via 802.1X port authentication or MAC address allowlisting. Remove the incentive for rogue AP deployment by providing adequate, managed connectivity.
Conduct Regular RF Site Surveys. Quarterly physical and RF site surveys identify unauthorised hardware that WIPS may have missed due to signal attenuation, physical obstruction, or deliberate RF shielding. A survey should cover all terminals, lounges, retail units, and back-of-house areas. Document the authorised AP inventory and compare against survey findings.
Implement a Leased Line or Dedicated Business Internet Connection for Critical Infrastructure. As discussed in our guide on What Is a Leased Line? Dedicated Business Internet , separating critical operational traffic onto a dedicated, uncontended connection ensures that a DDoS attack or bandwidth exhaustion event on the guest network cannot impact airside operations systems.
Test Incident Response Procedures. Conduct tabletop exercises simulating an Evil Twin detection event. Verify that WIPS containment is functioning, that the NOC team knows the escalation procedure, and that passenger-facing communications are prepared for a scenario where the guest network must be temporarily suspended.
ROI and Business Impact
Securing the network is the foundation for commercial value, not a cost centre in isolation. A secure, reliable, and trusted guest WiFi network directly increases passenger opt-in rates at the captive portal. Higher opt-in rates generate larger, higher-quality first-party data sets. This data enables the airport operator to deliver personalised retail promotions, optimise terminal layouts based on real footfall data, and build loyalty programmes that drive repeat engagement.
The cost of a security incident — GDPR enforcement action, reputational damage, and the operational cost of incident response — far exceeds the cost of deploying the security controls described in this guide. The UK Information Commissioner's Office has issued fines of up to £17.5 million under UK GDPR for data protection failures. For a major international airport processing millions of passenger connections annually, the risk exposure is significant.
Purple's platform is designed to align the security investment with commercial outcomes. The secure captive portal, GDPR-compliant data capture, and analytics layer are a single integrated deployment — not three separate procurement exercises. This reduces total cost of ownership and accelerates time-to-value for the IT and marketing teams simultaneously.
Key Terms & Definitions
Evil Twin Access Point
A malicious wireless access point that masquerades as a legitimate network by broadcasting the same SSID, designed to intercept user data via Man-in-the-Middle attacks.
Common in airport terminals where attackers exploit devices auto-connecting to known SSIDs based on signal strength. Mitigated by OWE encryption and WIPS containment.
Rogue Access Point
An unauthorized wireless access point physically connected to the enterprise wired network, bypassing security controls including firewalls, NAC policies, and enterprise WiFi configurations.
Often installed by retail tenants or staff seeking better coverage. Addressed by 802.1X port authentication on all ethernet ports and automated WIPS detection.
Opportunistic Wireless Encryption (OWE)
A WPA3 feature defined in IEEE 802.11-2020 that provides individualized, session-unique encryption for open networks without requiring a shared password, using Diffie-Hellman key exchange.
The correct encryption standard for public airport guest networks. Eliminates passive eavesdropping without adding authentication friction for passengers.
Wireless Intrusion Prevention System (WIPS)
Network infrastructure that continuously monitors the radio frequency spectrum for unauthorized access points, Evil Twins, and attack signatures, and automatically deploys countermeasures including de-authentication frames.
The primary automated defense against Evil Twin and rogue AP threats in high-density environments. Must be configured to cover all frequency bands including 6 GHz for Wi-Fi 6E deployments.
Client Isolation
A wireless network configuration that prevents devices connected to the same SSID from communicating directly with each other at Layer 2, restricting all traffic to the gateway.
Mandatory on Guest VLANs to prevent device-to-device attacks. A simple configuration setting that is frequently absent in legacy deployments.
VLAN Segmentation
The practice of dividing a physical network into multiple logical networks using IEEE 802.1Q VLAN tags to isolate traffic types and enforce access control boundaries.
Used to separate untrusted guest traffic from secure airport operations, staff systems, and retail POS infrastructure. Eliminates lateral movement risk from compromised guest devices.
IEEE 802.1X
An IEEE standard for port-based Network Access Control that requires devices to authenticate before being granted network access, typically via a RADIUS server.
The authentication standard for staff and operations VLANs, and for port-level enforcement on retail ethernet ports to prevent rogue AP deployment.
OpenRoaming
A Wireless Broadband Alliance federation standard that enables automatic, seamless WiFi authentication across participating networks using pre-provisioned device profiles, without manual SSID selection.
Directly mitigates Evil Twin attacks by removing the manual network selection step. Purple operates as a free identity provider within the OpenRoaming ecosystem under its Connect licence.
Man-in-the-Middle (MitM) Attack
An attack where the perpetrator secretly intercepts, relays, and potentially modifies communications between two parties who believe they are communicating directly.
The primary goal of Evil Twin deployments. Mitigated by OWE encryption at the radio layer and HSTS enforcement at the application layer.
Captive Portal
A web page presented to new users of a public network before they are granted internet access, used for authentication, terms acceptance, and data collection.
The primary passenger onboarding touchpoint. Must be served over HTTPS with a valid certificate and designed for GDPR compliance including explicit consent mechanisms.
Case Studies
A major international airport is upgrading Terminal 3. The current network is flat — all devices, including retail POS systems, digital signage, and passenger devices, share the same broadcast domain. Retail vendors frequently complain about poor connectivity, leading them to install their own consumer-grade routers. The IT director needs a redesign that addresses security without disrupting commercial operations during a phased rollout.
Phase 1 — VLAN Architecture: Design four VLANs: Public Guest (internet-only, client isolation enabled), Staff (802.1X authenticated, internal access), Retail Tenant (internet-only, isolated from guest and staff, 802.1X port authentication on all retail ethernet ports), and Operations (air-gapped, for signage and building management). Phase 2 — Rogue AP Elimination: Enable 802.1X port authentication on all retail ethernet ports. Any device without a valid certificate is denied network access, eliminating the ability to plug in unauthorized routers. Simultaneously, provide retail tenants with a managed Retail Tenant SSID with adequate signal coverage, removing the incentive for rogue hardware. Phase 3 — WIPS Deployment: Configure the wireless controller to scan for unauthorized SSIDs and automatically contain Evil Twins. Set up alerting to the NOC for any rogue AP detection events. Phase 4 — Captive Portal and Analytics: Deploy Purple's captive portal on the Guest VLAN with GDPR-compliant onboarding, OWE encryption, and analytics integration.
Passengers at a regional airport are receiving browser warnings when connecting to the guest WiFi captive portal, and the marketing team reports that opt-in rates have dropped by 40% over the past six months. The IT team suspects the SSL certificate on the captive portal has expired. How should this be resolved, and what broader improvements should be made to the onboarding architecture?
Immediate remediation: Renew the SSL certificate on the captive portal server and implement automated certificate renewal (e.g., via Let's Encrypt with auto-renewal scripting) to prevent recurrence. Broader improvements: 1) Upgrade the guest SSID to WPA3 with OWE to provide encryption at the radio layer, which modern mobile operating systems surface as a positive trust signal. 2) Implement HSTS on the captive portal domain to prevent SSL stripping attacks. 3) Integrate Purple's captive portal platform, which manages certificate lifecycle, GDPR consent flows, and analytics as a managed service, removing the operational burden from the in-house team. 4) Consider OpenRoaming profile-based authentication for returning passengers, eliminating the portal interaction entirely for opted-in users.
Scenario Analysis
Q1. Your WIPS dashboard alerts you to a new AP broadcasting the airport's official guest SSID from within a retail coffee shop in Terminal 2. The AP's BSSID does not appear in your authorized AP inventory, and it is not connected to your wired network. What type of threat is this, what is the automated WIPS response, and what follow-up action should the NOC team take?
💡 Hint:Consider whether the device is physically attached to your wired infrastructure or operating entirely over the air. The distinction determines both the threat classification and the remediation pathway.
Show Recommended Approach
This is an Evil Twin AP. Because it is not connected to the wired network, it is attempting to hijack client connections over the air by mimicking the legitimate SSID. The automated WIPS response should be to transmit de-authentication frames to clients attempting to associate with that specific BSSID, preventing successful connection. The NOC team should dispatch physical security to the coffee shop location to identify and remove the device, document the incident for the security log, and review whether any clients successfully connected to the Evil Twin before containment was activated — those sessions should be treated as potentially compromised.
Q2. A new terminal is opening in six months. The operations director wants a completely open network with no captive portal to maximise passenger convenience. The marketing director wants maximum opt-in data collection. The CISO wants GDPR compliance and encryption. How do you satisfy all three stakeholders in a single architecture?
💡 Hint:Consider WPA3 OWE for the encryption requirement, OpenRoaming for the seamless authentication requirement, and Purple's platform for the data collection and compliance requirement. These are not mutually exclusive.
Show Recommended Approach
Deploy WPA3 with OWE on the public SSID — this provides encryption without requiring a password, satisfying the CISO's encryption requirement while maintaining the open, frictionless experience the operations director wants. Implement OpenRoaming via Purple's identity provider capability, so returning passengers with existing profiles connect automatically and securely without any manual interaction. For new passengers, present a lightweight, GDPR-compliant captive portal that collects consent and profile data — this satisfies the marketing director's requirement. The net result is a network that is encrypted by default, seamless for returning users, and data-capturing for new users, with full GDPR compliance.
Q3. During a quarterly RF site survey, your team discovers an AP in a back-of-house service corridor that is connected to the wired network but does not appear in the authorized AP inventory. It is broadcasting a hidden SSID and has been active for approximately three months based on switch port logs. What is the threat classification, what is the immediate containment action, and what does the three-month window imply for your incident response process?
💡 Hint:This device has wired network access, making it a different threat class from an Evil Twin. The three-month window has specific implications for data breach notification obligations under GDPR.
Show Recommended Approach
This is a Rogue AP with wired network access — a high-severity incident. Immediate containment: shut down the switch port to which the device is connected, physically remove the device, and preserve it as evidence. The three-month active window implies that an unknown actor has had persistent network access for approximately 90 days. Under UK GDPR Article 33, a personal data breach must be reported to the ICO within 72 hours of becoming aware of it, if it is likely to result in a risk to individuals' rights and freedoms. The incident response team must immediately assess what data was accessible from that network segment, whether any exfiltration occurred (review NetFlow/IPFIX logs for the switch port), and prepare a breach notification if the assessment indicates risk. This incident also indicates a gap in the WIPS configuration — the system should have detected the rogue AP's wired presence and over-the-air broadcast within hours of installation, not three months later.



