Hospitality WiFi Solutions: What to Look for in a Provider
This authoritative guide details the critical technical and commercial considerations for selecting a hospitality WiFi provider. It covers network architecture, security standards, Captive Portal design, and GDPR-compliant data analytics to help IT leaders deploy solutions that drive revenue and operational efficiency.
🎧 Listen to this Guide
View Transcript

Executive Summary
For modern venue operators, guest WiFi is no longer a cost centre; it is a critical data asset and a revenue driver. As IT managers, network architects, and CTOs evaluate hospitality WiFi solutions, the focus must shift from basic connectivity to enterprise-grade analytics, compliance, and integration. This guide provides a vendor-neutral framework for evaluating guest WiFi providers, detailing the essential network architecture, Captive Portal requirements, and data analytics capabilities necessary for a successful deployment in hospitality, retail, and public-sector environments.
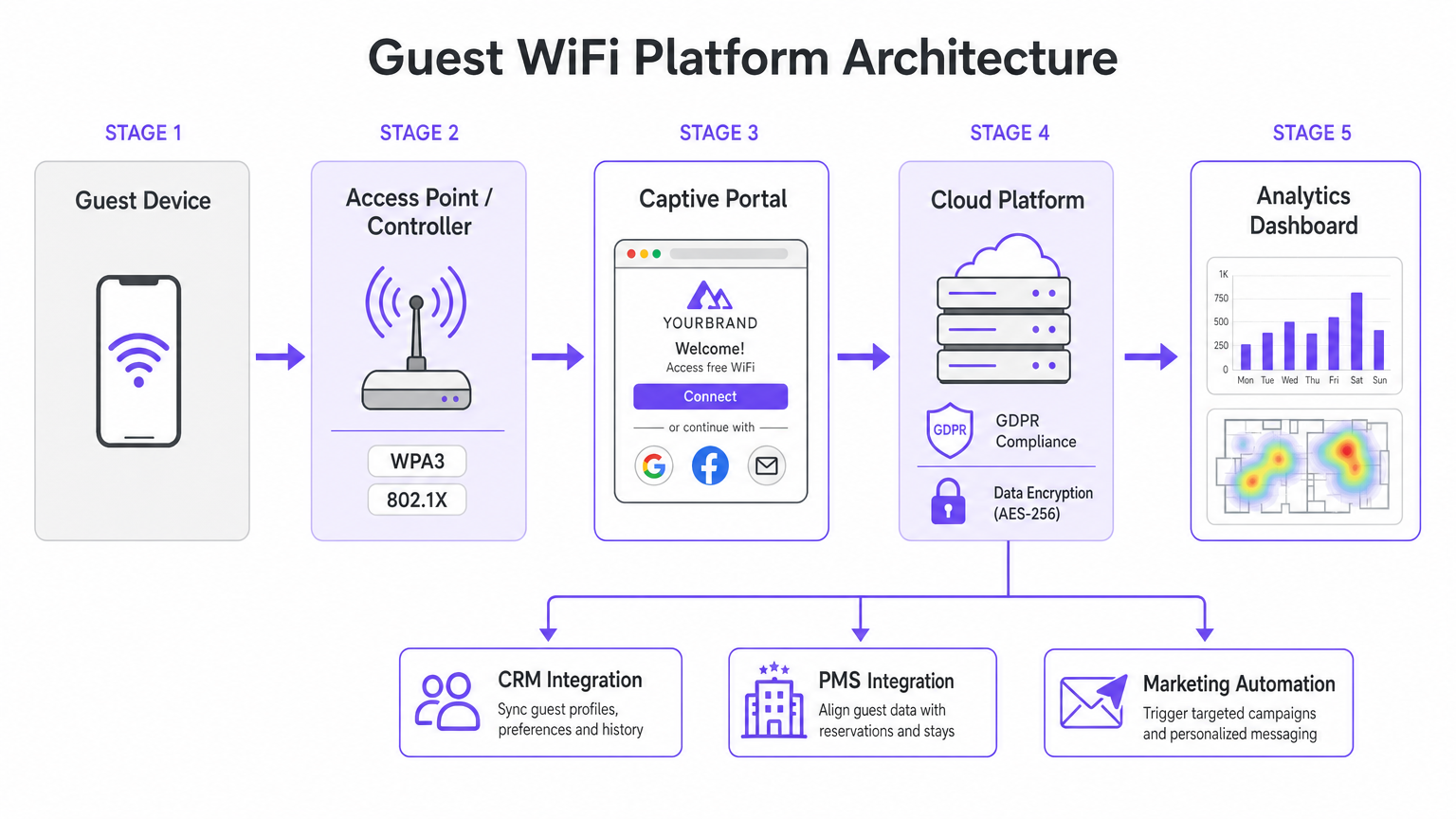
Deploying a robust Guest WiFi solution requires balancing high-density performance with stringent security standards like WPA3 and PCI DSS. Furthermore, the ability to capture first-party data via a WiFi Analytics platform transforms the network into a marketing engine. This reference guide outlines the technical specifications and business impact considerations required to select a provider capable of delivering both secure connectivity and actionable intelligence.
Technical Deep-Dive
Network Architecture and Radio Standards
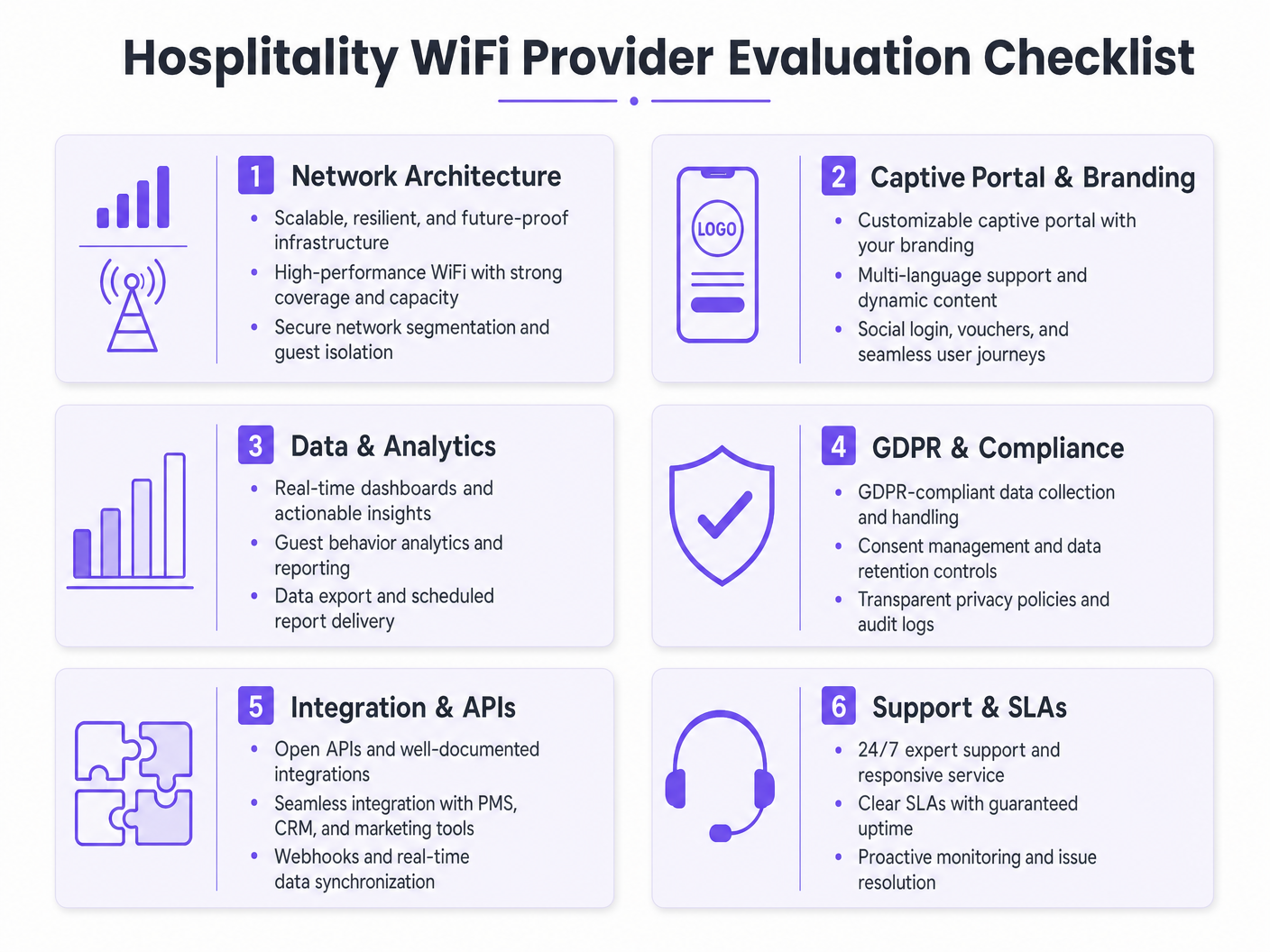
The foundation of any enterprise WiFi deployment is the underlying network architecture. For multi-site operators, a cloud-managed architecture is vastly superior to traditional on-premise controllers. Cloud management enables zero-touch provisioning, centralised policy enforcement, and seamless firmware updates across hundreds of locations without requiring local IT resources.
When evaluating access point (AP) specifications, Wi-Fi 6 (802.11ax) must be the baseline standard. Wi-Fi 6 introduces Orthogonal Frequency Division Multiple Access (OFDMA), which allows a single AP to communicate with multiple clients simultaneously across different sub-channels. In high-density environments—such as conference centres or stadium concourses—this dramatically reduces latency and improves throughput compared to the older Wi-Fi 5 (802.11ac) standard. For venues anticipating extreme device density, Wi-Fi 6E extends these capabilities into the uncongested 6 GHz spectrum.
Security and Network Segmentation
Security architecture in hospitality WiFi must address both guest safety and corporate compliance. Network segmentation is a non-negotiable requirement; guest traffic must be logically isolated from corporate and point-of-sale (POS) networks. This is typically achieved using VLAN tagging at the AP level, enforced by strict firewall rules at the gateway. This isolation is a core requirement for PCI DSS compliance if payment terminals share the physical network infrastructure.
Authentication standards are equally critical. WPA3 should be the default for all new guest networks, mitigating the vulnerabilities inherent in WPA2 (such as KRACK attacks). For internal staff networks operating on the same hardware, IEEE 802.1X authentication backed by a RADIUS server provides robust, certificate-based security that far exceeds the protection of pre-shared keys.
Implementation Guide
The Captive Portal and Data Capture
The Captive Portal serves as the gateway between the access point and the internet, acting as the primary interface for guest interaction and data capture. A basic static HTML page is insufficient for enterprise deployments. Operators require a dynamic, fully branded portal supporting multiple authentication methods, including social login (Google, Facebook), email registration, and SMS verification.
Each authentication method yields different data assets. Social login provides verified demographic data, while email registration is crucial for building a marketing database. However, this data capture must be strictly governed by consent management protocols. Under GDPR, marketing consent must be explicit, informed, and freely given. Providers must support separate, un-ticked checkboxes for network access and marketing communications, alongside transparent mechanisms for data subject access requests (DSARs).
Integration and Analytics
The true value of a modern hospitality WiFi solution lies in its analytics capabilities. Basic connection counts are inadequate; IT and marketing teams need actionable insights derived from dwell time analysis, repeat visitor identification, and footfall heatmaps.
To maximise ROI, the WiFi platform must integrate seamlessly with the venue's existing technology stack. Look for providers offering robust APIs and webhook support for real-time data synchronisation with CRM systems, marketing automation platforms, and Property Management Systems (PMS). This integration enables automated, targeted campaigns based on real-time guest behaviour.
Best Practices
- Conduct Rigorous RF Site Surveys: Never estimate AP placement based solely on floor plans. Conduct comprehensive RF site surveys to account for attenuation from walls, structural steel, and high-density user clusters. A common rule of thumb for high-density areas is one AP per 25-30 concurrent users.
- Ensure Adequate Backhaul: The fastest Wi-Fi 6 network will fail if the internet uplink is a bottleneck. For venues supporting over 100 concurrent users, invest in dedicated leased lines to guarantee uncontended bandwidth. For more on this, see our guide: What Is a Leased Line? Dedicated Business Internet .
- Continuously Optimise the Portal: Treat the captive portal as a dynamic marketing channel. Update branding, promotions, and loyalty messaging seasonally to maximise engagement and data capture rates.
Troubleshooting & Risk Mitigation
Common Failure Modes
- Inadequate Network Segmentation: Failing to isolate guest traffic from POS systems exposes the venue to significant PCI DSS compliance risks and potential data breaches. Always verify VLAN configurations and firewall rules during deployment.
- Non-Compliant Data Capture: Bundling Terms of Service acceptance with marketing consent violates GDPR. Ensure the captive portal uses explicit, separate opt-in mechanisms to avoid regulatory enforcement and reputational damage.
- Under-provisioned AP Density: Deploying too few access points in high-traffic areas leads to channel contention, dropped connections, and poor guest experience. Design for capacity, not just coverage.
ROI & Business Impact
The return on investment for an enterprise hospitality WiFi solution extends beyond basic connectivity. By leveraging a WiFi Analytics platform, venues can transform anonymous foot traffic into known customer profiles. This first-party data drives targeted marketing campaigns, increasing repeat visit rates and average spend per guest.
Furthermore, operational efficiencies are gained through centralised cloud management and automated CRM integrations, reducing the IT burden. Ultimately, a well-architected WiFi solution enhances the guest experience while providing measurable business intelligence to operations and marketing teams, particularly in core sectors like Hospitality and Retail .
Key Terms & Definitions
Wi-Fi 6 (802.11ax)
The current standard for wireless networking that significantly improves performance in high-density environments through technologies like OFDMA.
Essential for venues with large numbers of simultaneous users, such as conference centres and stadiums, to prevent network congestion.
OFDMA (Orthogonal Frequency Division Multiple Access)
A technology that allows a single wireless channel to be divided into smaller sub-channels, enabling an access point to communicate with multiple clients simultaneously.
Crucial for reducing latency and improving throughput when many guests are trying to access the network at the same time.
Network Segmentation
The practice of dividing a computer network into multiple logical subnets (VLANs) to improve performance and security.
Mandatory for isolating untrusted guest traffic from sensitive corporate data and payment processing systems.
Captive Portal
A web page that a user of a public-access network is obliged to view and interact with before access is granted.
The primary touchpoint for guest interaction, branding, and GDPR-compliant data capture.
WPA3
The latest Wi-Fi security certification program, providing stronger encryption and better protection against offline dictionary attacks compared to WPA2.
The baseline security standard that should be deployed on all new guest and corporate wireless networks.
PCI DSS (Payment Card Industry Data Security Standard)
An information security standard for organizations that handle branded credit cards from the major card schemes.
Relevant when a venue processes payments; requires strict isolation of the payment network from the guest WiFi network.
Webhook
A method of augmenting or altering the behaviour of a web page or web application with custom callbacks, allowing real-time data transfer between applications.
Used to instantly sync guest data captured on the WiFi portal with a venue's CRM or marketing automation platform.
Dwell Time
The length of time a visitor spends in a specific physical location, measured by tracking the presence of their mobile device's MAC address.
A key analytics metric used by operations teams to understand venue utilization and by marketing teams to gauge engagement.
Case Studies
A 200-room hotel needs to upgrade its legacy Wi-Fi 4 network to support high-density conference facilities and seamless guest roaming, while ensuring PCI DSS compliance for its new mobile point-of-sale terminals.
Deploy a cloud-managed Wi-Fi 6 architecture with access points configured for OFDMA to handle the high client density in the conference rooms. Implement strict network segmentation using VLANs to isolate guest traffic from the mobile POS devices, enforcing the separation at the gateway firewall. Configure the captive portal to require explicit GDPR-compliant consent for marketing data capture.
A national pub chain wants to use guest WiFi to build a marketing database and understand customer dwell times across its 50 locations.
Implement an enterprise guest WiFi platform featuring a branded captive portal with social login and email registration options. Ensure the portal includes separate, un-ticked checkboxes for marketing consent. Utilize the platform's analytics dashboard to track MAC addresses (hashed for privacy) to calculate dwell times and repeat visit frequencies. Set up webhook integrations to push verified email addresses directly to the chain's CRM system in real-time.
Scenario Analysis
Q1. Your marketing director wants to automatically add every guest who connects to the WiFi to the weekly promotional email blast to increase F&B revenue. How do you configure the captive portal to support this?
💡 Hint:Consider GDPR requirements regarding consent for marketing communications.
Show Recommended Approach
You cannot automatically add guests to a marketing list just because they connected to the WiFi. The captive portal must be configured with a clear privacy notice and a separate, un-ticked checkbox explicitly requesting consent for marketing communications. Only guests who actively check this box can be synced to the CRM via API or webhook for the email blast.
Q2. A stadium IT director is evaluating a vendor who proposes deploying 802.11ac (Wi-Fi 5) access points, arguing it will save 30% on hardware costs while providing sufficient coverage. How should the director respond?
💡 Hint:Consider the difference between coverage and capacity in a stadium environment.
Show Recommended Approach
The director should reject the proposal. While Wi-Fi 5 might provide adequate physical coverage, it lacks the capacity management features required for a stadium. Wi-Fi 6 (802.11ax) is essential in this environment because OFDMA allows the APs to handle many simultaneous connections efficiently, preventing the network from collapsing under high client density.
Q3. During a network upgrade at a retail chain, the deployment team suggests running the new guest WiFi and the staff inventory scanners on the same VLAN to simplify IP address management. What is the risk, and what is the correct approach?
💡 Hint:Think about security best practices and compliance requirements.
Show Recommended Approach
Running guest and corporate traffic on the same VLAN is a severe security risk and violates best practices (and potentially PCI DSS if payment data is involved). It exposes internal systems to untrusted guest devices. The correct approach is strict network segmentation: configure separate SSIDs mapped to separate VLANs, and use firewall rules to block all traffic between the guest VLAN and the corporate VLAN.



