Captive Portal Baseado na Nuvem vs. On-Premise: Qual é o Certo para o Seu Negócio?
Uma comparação técnica abrangente das arquiteturas de captive portal baseado na nuvem versus on-premise. Este guia avalia a velocidade de implementação, estruturas de custos, escalabilidade e implicações de conformidade para ajudar os líderes de TI a tomar decisões informadas sobre a infraestrutura.
🎧 Ouça este Guia
Ver Transcrição
- Resumo Executivo
- Análise Técnica Aprofundada: Arquitetura e Fluxos de Autenticação
- A Arquitetura de Captive Portal Baseado na Nuvem
- A Arquitetura de Servidor Captive Portal On-Premise
- Guia de Implementação: Recomendações Neutras em Relação ao Fornecedor
- Quando Escolher um Captive Portal Baseado na Nuvem
- Quando Escolher um Captive Portal On-Premise
- Melhores Práticas para a Implementação de Captive Portal
- Resolução de Problemas e Mitigação de Riscos
- Riscos Baseados na Cloud
- Riscos no Local
- ROI e Impacto no Negócio

Resumo Executivo
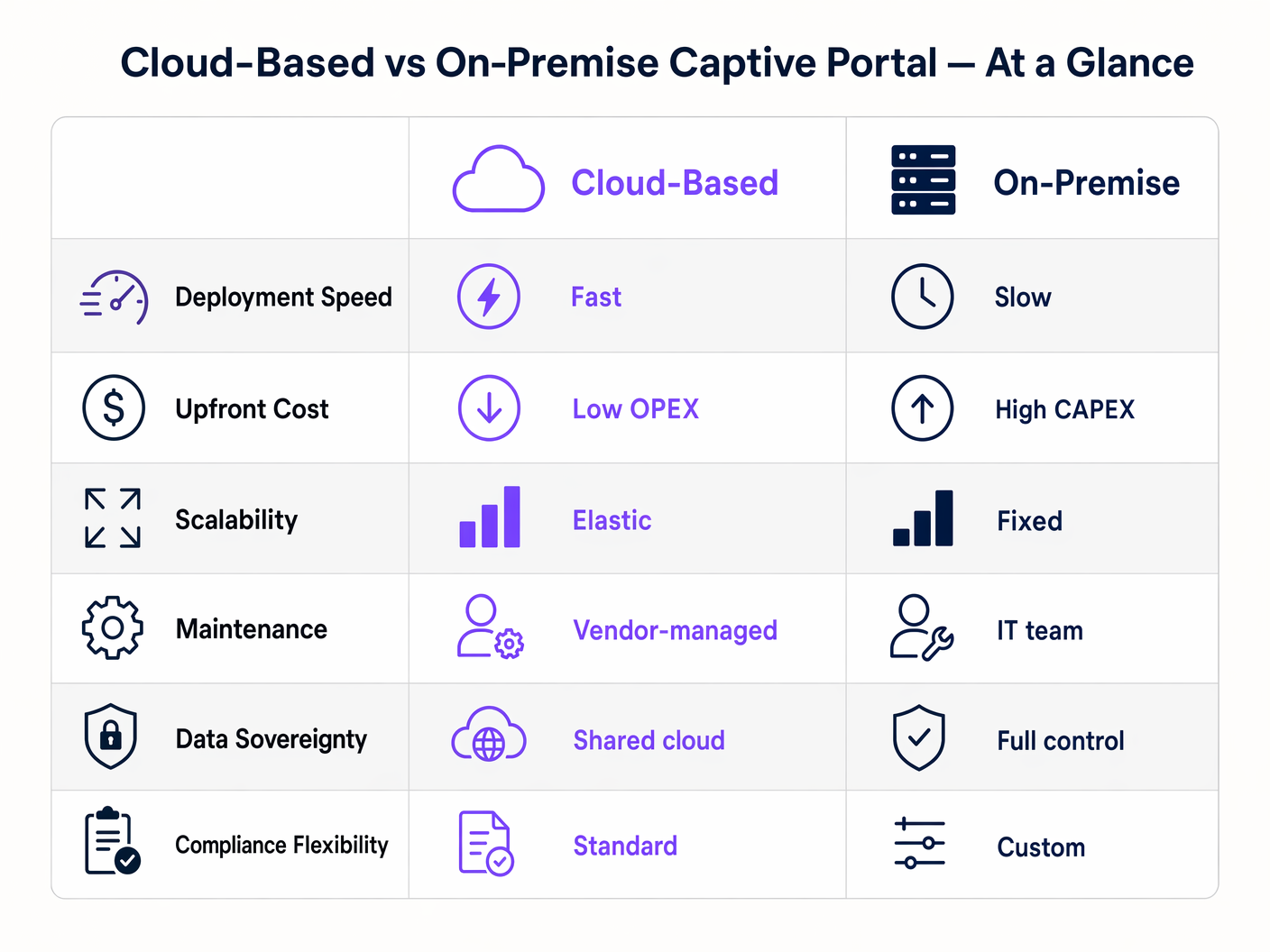
Ao projetar uma arquitetura de WiFi para convidados, a escolha entre um captive portal baseado na nuvem e um servidor captive portal on-premise dita os seus custos de infraestrutura, sobrecarga operacional e postura de conformidade para o ciclo de vida da implementação. Para IT managers, network architects e CTOs, esta não é meramente uma preferência de software; é uma decisão arquitetónica fundamental.
Um captive portal baseado na nuvem transfere as cargas de trabalho de autenticação e renderização do portal para um ambiente gerido por um fornecedor, oferecendo escalabilidade elástica e manutenção significativamente reduzida. Por outro lado, um sistema captive portal on-premise retém todos os dados e lógica de autenticação dentro do perímetro da sua rede local, proporcionando controlo absoluto à custa de maiores despesas de capital e encargos operacionais.
Este guia fornece uma comparação técnica rigorosa de ambos os modelos de implementação. Iremos examinar a arquitetura, avaliar o custo total de propriedade e delinear cenários de implementação específicos para o ajudar a determinar qual software de captive portal se alinha com os seus objetivos de negócio e requisitos regulamentares.
Análise Técnica Aprofundada: Arquitetura e Fluxos de Autenticação
Compreender a distinção entre um captive portal alojado e uma solução on-premise requer examinar o fluxo de autenticação e onde os processos subjacentes são executados.
A Arquitetura de Captive Portal Baseado na Nuvem
Num modelo baseado na nuvem, a lógica do captive portal, a autenticação RADIUS e as bases de dados de captura de dados residem em infraestruturas de terceiros (por exemplo, AWS, Azure, GCP) geridas por um fornecedor como a Purple.
Quando um dispositivo cliente se associa ao SSID de convidado, o access point (AP) local ou o wireless LAN controller (WLC) interceta o pedido HTTP/HTTPS inicial. Como o dispositivo não está autenticado, o controlador redireciona o navegador para um URL alojado na nuvem. O utilizador interage com o portal — aceitando termos, autenticando-se via social login ou preenchendo um formulário. Após autenticação bem-sucedida, a plataforma na nuvem comunica de volta ao controlador local (frequentemente via RADIUS ou uma API específica do fornecedor) para autorizar o MAC address do cliente, concedendo acesso à internet.
Esta arquitetura é altamente elástica. Durante picos de carga — como o intervalo num estádio ou uma grande promoção em Retail — a infraestrutura na nuvem escala automaticamente para lidar com milhares de pedidos de autenticação concorrentes sem exigir atualizações de hardware local. Além disso, plataformas como a Purple fornecem análises de Guest WiFi e atuam como um provedor de identidade gratuito para serviços como o OpenRoaming sob a licença Connect, adicionando valor significativo além do controlo de acesso básico.
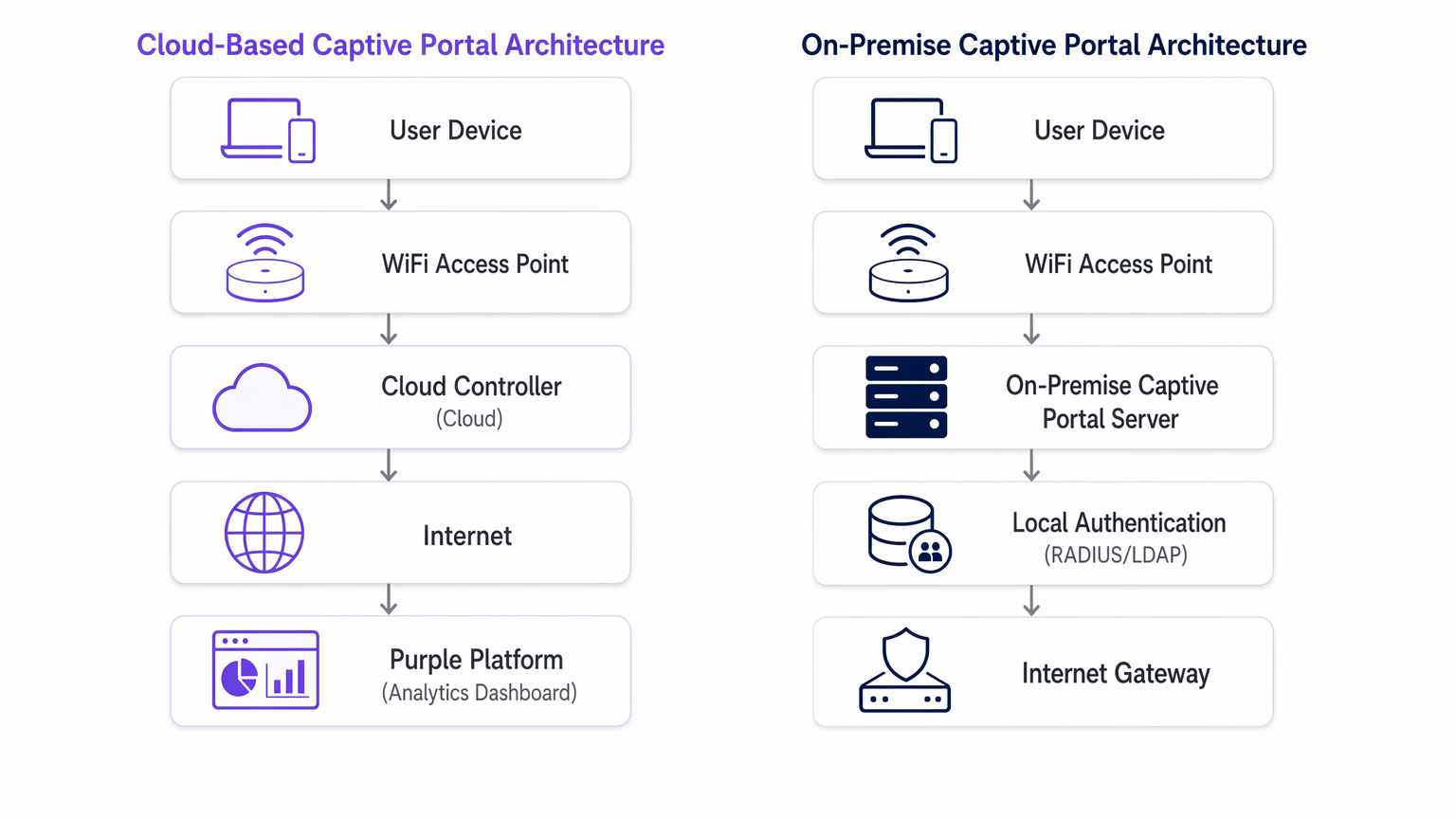
A Arquitetura de Servidor Captive Portal On-Premise
Um servidor captive portal on-premise requer a implementação de hardware dedicado ou máquinas virtuais (VMs) dentro da sua infraestrutura de rede local. O servidor web do portal, o servidor RADIUS (por exemplo, FreeRADIUS, Microsoft NPS) e a base de dados de utilizadores são todos mantidos localmente pela sua equipa de IT.
O processo de redirecionamento é semelhante, mas o cliente é direcionado para um IP address interno em vez de um URL público. A transação de autenticação ocorre inteiramente dentro da local area network (LAN). Este modelo garante que nenhum dado de convidado atravessa a internet pública durante a fase de autenticação, o que é frequentemente um requisito rigoroso para instalações de Healthcare ou governamentais regidas por políticas rigorosas de soberania de dados.
No entanto, a capacidade de um sistema on-premise é estritamente limitada pelo hardware provisionado. O planeamento da capacidade deve ter em conta as sessões concorrentes de pico, resultando frequentemente num significativo sobre-provisionamento. Além disso, a equipa de IT assume total responsabilidade pela aplicação de patches do OS, renovação de SSL certificate, manutenção da base de dados e configuração de pares de failover de alta disponibilidade.
Guia de Implementação: Recomendações Neutras em Relação ao Fornecedor
Selecionar a arquitetura apropriada depende das suas restrições operacionais específicas.
Quando Escolher um Captive Portal Baseado na Nuvem
- Implementações Multi-Site: Se gere um portefólio distribuído, como uma cadeia de Hospitality ou uma rede de centros de Transport , um captive portal baseado na nuvem oferece gestão centralizada. Pode enviar atualizações de portal, alterações de marca e modificações de políticas para centenas de sites simultaneamente.
- Operações de IT Reduzidas: Quando a sua equipa de rede está focada na infraestrutura principal em vez da manutenção de aplicações, delegar o sistema captive portal a um provedor de SaaS reduz a sobrecarga operacional.
- Integração de Marketing e Análises: As plataformas na nuvem facilitam inerentemente a agregação de dados. Se o seu objetivo é alavancar WiFi Analytics para impulsionar o envolvimento do cliente, um captive portal alojado fornece as integrações necessárias de imediato.
Quando Escolher um Captive Portal On-Premise
- Soberania de Dados Rigorosa: Se os quadros regulamentares proíbem que os dados de convidados saiam das suas instalações físicas ou fronteiras nacionais, uma implementação on-premise é obrigatória.
- Ambientes Air-Gapped ou de Alta Latência: Locais com uplinks de internet não fiáveis não podem depender de um gateway de autenticação na nuvem. Se o link WAN falhar, um portal na nuvem falha; um portal on-premise ainda pode autenticar utilizadores para acesso à rede local.
- Deep Integração Personalizada: Quando o portal deve interagir diretamente com sistemas de gestão de propriedades (PMS) legados, alojados localmente, através de APIs proprietárias que não podem ser expostas à internet.
Melhores Práticas para a Implementação de Captive Portal
Independentemente do modelo de implementação, a adesão aos padrões da indústria é crítica para a segurança e a experiência do utilizador.
- Segmentação de VLAN: Isole sempre a rede WiFi de convidados numa VLAN dedicada, totalmente separada dos recursos corporativos.
- Gestão de Certificados SSL/TLS: Um captive portal deve servir as suas páginas via HTTPS. Certificados expirados irão desencadear avisos graves no navegador, interrompendo o fluxo de autenticação. Para implementações no local, automatize a renovação de certificados usando protocolos como ACME (por exemplo, Let's Encrypt). Os fornecedores de cloud gerem isto automaticamente.
- Considerações sobre WPA3 e 802.1X: Embora o WPA3-Enterprise com 802.1X seja o padrão ouro para dispositivos corporativos, é impraticável para redes de convidados onde não é possível distribuir certificados para dispositivos não geridos. Portanto, uma rede aberta com um captive portal, ou WPA3-Personal (Opportunistic Wireless Encryption - OWE), permanece o padrão para acesso público.
- Acordos de Processamento de Dados (DPA): Ao utilizar um captive portal alojado, reveja rigorosamente o DPA do fornecedor. Garanta que cumprem o GDPR, PCI DSS e definem claramente os seus sub-processadores e locais de residência dos dados.
Resolução de Problemas e Mitigação de Riscos
Os modos de falha comuns diferem significativamente entre as duas arquiteturas.
Riscos Baseados na Cloud
- Interrupções de WAN: O risco principal é a perda de conectividade à internet. Sem um uplink, o controlador da cloud não pode ser alcançado e a autenticação falha. Mitigue isto com links WAN redundantes (por exemplo, fibra primária, 5G/LTE secundário) ou considere Os Principais Benefícios do SD WAN para Empresas Modernas para garantir alta disponibilidade.
- Falhas na Resolução de DNS: Se o DNS local falhar ao resolver o URL do portal da cloud, o redirecionamento é interrompido. Garanta uma infraestrutura DNS local robusta.
Riscos no Local
- Falha de Hardware: Um único servidor de captive portal é um único ponto de falha. Deve implementar num cluster ativo-passivo ou ativo-ativo para garantir alta disponibilidade.
- Esgotamento da Capacidade: Picos inesperados na densidade de utilizadores podem sobrecarregar o servidor RADIUS local ou o servidor web, causando timeouts. Monitorize rigorosamente as métricas de CPU, memória e sessões concorrentes.
- Gestão de Patches: Servidores de portal não atualizados são alvos principais para exploração. Implemente uma gestão rigorosa de vulnerabilidades e cronogramas de implementação de patches.
Para cenários onde o portal está a causar mais atrito do que valor, consulte Como Remover um Login de Captive Portal (E Quando Deve Fazê-lo) .
ROI e Impacto no Negócio
Os modelos financeiros para estas arquiteturas são fundamentalmente diferentes.
Uma implementação de software de captive portal no local é um modelo de Despesa de Capital (CAPEX). Incorre em custos iniciais significativos para hardware, licenciamento de hypervisor e infraestrutura redundante. Os custos contínuos estão ocultos na despesa operacional (OPEX) do tempo da sua equipa de TI gasto em manutenção e resolução de problemas.
Um captive portal baseado na cloud opera num modelo OPEX. Os custos iniciais são mínimos, limitados aos pontos de acesso e à configuração inicial. Paga uma taxa de subscrição previsível e recorrente. O ROI de uma plataforma cloud é frequentemente realizado através da redução da carga de trabalho de TI e da monetização dos dados capturados via análises avançadas e integrações de marketing, transformando o WiFi de convidados de um centro de custos num ativo gerador de receita.
Termos-Chave e Definições
Captive Portal
A web page that a user of a public access network is obliged to view and interact with before access is granted.
The primary mechanism for authenticating guests and capturing marketing consent on public WiFi networks.
RADIUS (Remote Authentication Dial-In User Service)
A networking protocol that provides centralized Authentication, Authorization, and Accounting (AAA) management for users who connect and use a network service.
The backend protocol used by both cloud and on-premise portals to signal the access point that a user is authorized.
Data Sovereignty
The concept that data is subject to the laws and governance structures within the nation it is collected.
A critical deciding factor for government and healthcare venues evaluating cloud vs. on-premise architectures.
MAC Address Authorization
The process of using a device's Media Access Control address to identify it and grant network access after initial authentication.
How the network controller remembers a device so the user doesn't have to log in every time they roam between access points.
WPA3-Enterprise
The latest Wi-Fi security standard requiring 802.1X authentication and a RADIUS server, providing individualized encryption.
The standard for corporate networks, which operates separately from the open/OWE guest network where the captive portal resides.
VLAN Segmentation
The practice of dividing a physical network into multiple logical networks.
Essential for security, ensuring guest WiFi traffic (and the captive portal) is isolated from internal corporate data.
Data Processing Agreement (DPA)
A legally binding contract that states the rights and obligations of each party concerning the protection of personal data.
Mandatory documentation when utilizing a hosted captive portal to ensure GDPR compliance.
OpenRoaming
A federation of Wi-Fi networks that allows users to automatically and securely connect to participating networks without manual login.
An advanced authentication method supported by platforms like Purple, offering a frictionless alternative to traditional captive portals.
Estudos de Caso
A national retail chain with 400 locations needs to deploy a standardized guest WiFi experience. Their IT team consists of 5 network engineers based at headquarters. They require detailed analytics on customer dwell time and visit frequency to integrate with their CRM.
Deploy a cloud-based captive portal system. The lean IT team cannot manage 400 on-premise portal servers or complex VPN routing back to a centralized on-premise data center. A hosted captive portal allows centralized policy management, immediate scalability, and native API integration for CRM data syncing.
A large NHS hospital trust requires guest WiFi across its campus. Strict patient data confidentiality policies dictate that no MAC addresses, device identifiers, or user information can be stored on servers outside the UK, and all authentication traffic must remain within the hospital's private network.
Deploy an on-premise captive portal server. The hospital must provision a high-availability cluster of portal servers within their local data center, integrated with their local Active Directory or a dedicated FreeRADIUS instance for guest accounts.
Análise de Cenários
Q1. A hotel chain is experiencing frequent authentication timeouts during large conferences because their local captive portal server reaches maximum CPU utilization. What is the most operationally efficient architectural solution?
💡 Dica:Consider which deployment model handles elastic scaling automatically.
Mostrar Abordagem Recomendada
Migrate to a cloud-based captive portal system. Cloud architectures provide elastic scalability, automatically absorbing authentication spikes without requiring the local IT team to provision, configure, or maintain additional hardware.
Q2. A government facility must deploy guest WiFi but has a strict policy that no external DNS resolution or outbound internet traffic is permitted from the management VLAN. Which captive portal architecture must be deployed?
💡 Dica:Evaluate how a cloud portal redirects clients.
Mostrar Abordagem Recomendada
An on-premise captive portal server must be deployed. A cloud-based portal requires the client to resolve and reach an external URL for authentication. Without outbound internet access from the management/guest VLAN, the redirection will fail. The authentication process must be handled entirely locally.
Q3. You are calculating the total cost of ownership (TCO) for an on-premise captive portal deployment. Beyond the initial server hardware and software licensing, what critical infrastructure component must be included to ensure network resilience?
💡 Dica:Consider the impact of a single server failure.
Mostrar Abordagem Recomendada
You must include the cost of a secondary server configured for high availability (active-passive or active-active failover). Relying on a single on-premise server creates a single point of failure; if it goes offline, the entire guest network becomes inaccessible.



