Como Configurar WiFi Empresarial em Dispositivos Android com EAP-TLS
Este guia de referência técnica fornece aos líderes de TI seniores um plano abrangente para implementar a autenticação 802.1X EAP-TLS em dispositivos Android. Abrange a mecânica arquitetónica, estratégias de implementação manual e impulsionadas por MDM, e metodologias de resolução de problemas necessárias para proteger redes sem fios empresariais.
Listen to this guide
View podcast transcript
- Resumo Executivo
- Ouça o Briefing
- Análise Técnica Detalhada
- A Arquitetura 802.1X e a Mecânica EAP-TLS
- Requisitos de Certificado Específicos para Android
- Integração com o Ecossistema da Purple
- Guia de Implementação
- Método 1: Configuração Manual (BYOD / Pequena Escala)
- Método 2: Perfil Distribuído por MDM (Escala Empresarial)
- Melhores Práticas
- Resolução de Problemas e Mitigação de Riscos
- ROI e Impacto nos Negócios

Resumo Executivo
Proteger redes sem fios empresariais contra roubo de credenciais e acesso não autorizado exige ir além das palavras-passe partilhadas. Para frotas de dispositivos Android em ambientes corporativos, 802.1X EAP-TLS (Extensible Authentication Protocol with Transport Layer Security) representa o padrão de segurança definitivo. Ao aproveitar a autenticação mútua baseada em certificados, o EAP-TLS elimina os riscos associados à fadiga de palavras-passe, phishing e credenciais fracas.
Este guia de referência técnica fornece a arquitetos de rede, gestores de TI e CTOs estratégias acionáveis para implementar EAP-TLS em dispositivos Android. Seja a gerir terminais de ponto de venda em Retalho , dispositivos clínicos em Saúde , ou operações de bastidores em Hotelaria , dominar esta implementação garante uma conformidade de segurança robusta (PCI DSS, GDPR, ISO 27001) enquanto proporciona uma experiência de conexão perfeita para os utilizadores finais. Abrangemos tanto a configuração manual para ambientes BYOD como o aprovisionamento MDM zero-touch para frotas propriedade da empresa.
Ouça o Briefing
Análise Técnica Detalhada
A Arquitetura 802.1X e a Mecânica EAP-TLS
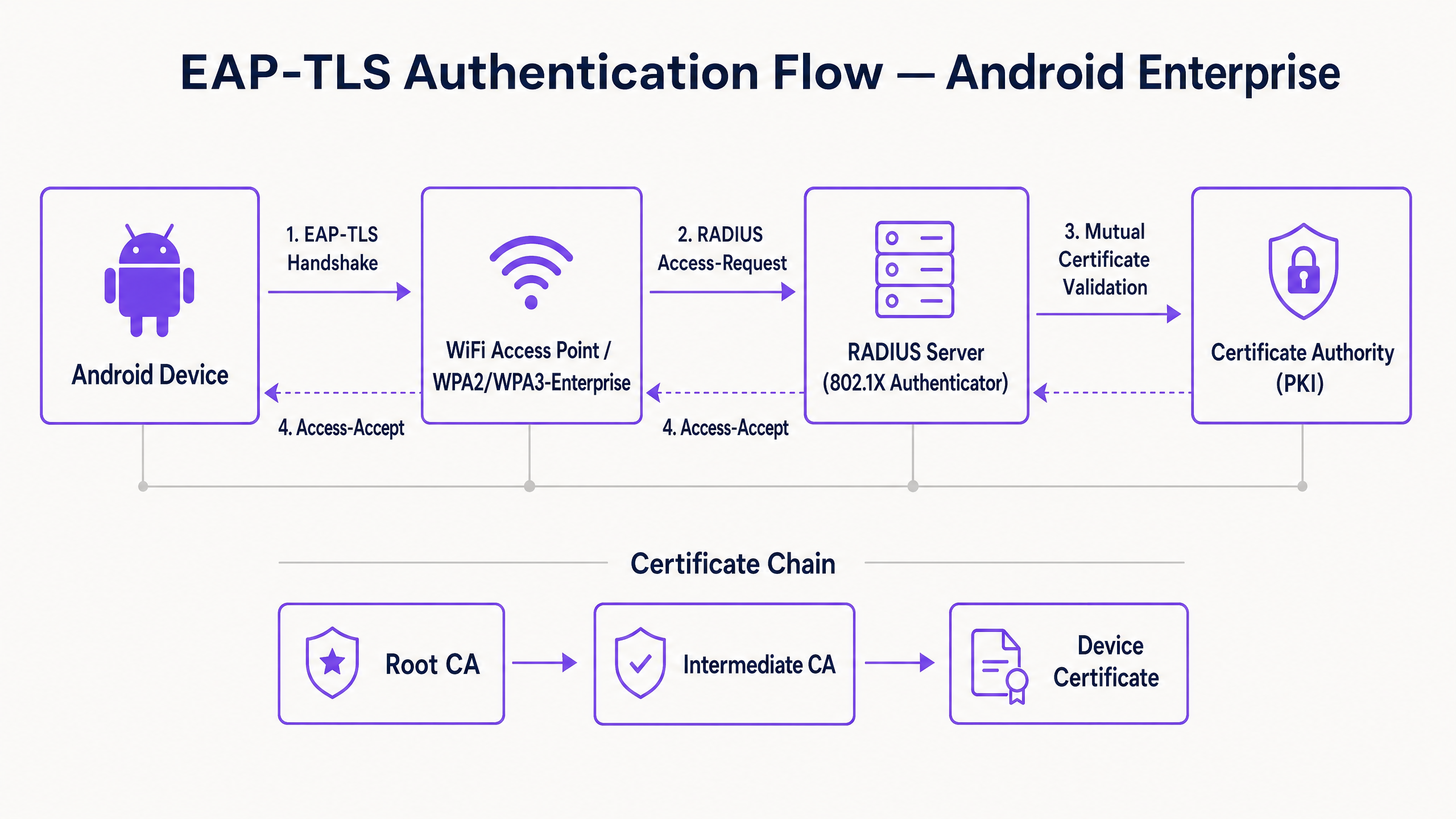
Na sua essência, 802.1X é um padrão IEEE para controlo de acesso à rede baseado em portas. Num contexto sem fios, o ponto de acesso atua como o Autenticador, facilitando a comunicação entre o dispositivo Android (o Suplicante) e o servidor RADIUS (o Servidor de Autenticação).
Ao contrário de PEAP ou TTLS, que encapsulam a autenticação de palavra-passe legada dentro de TLS, o EAP-TLS depende inteiramente de certificados X.509. Isto cria um paradigma de autenticação mútua:
- O servidor RADIUS apresenta o seu certificado ao dispositivo Android para provar que a rede é legítima.
- O dispositivo Android apresenta o seu certificado de cliente único ao servidor RADIUS para provar que é um endpoint autorizado.
Requisitos de Certificado Específicos para Android
A implementação em Android introduz restrições específicas, particularmente a partir do Android 11. A Google descontinuou a opção "Não validar" para certificados de servidor para mitigar ataques man-in-the-middle (MitM). Consequentemente, o dispositivo Android deve possuir o certificado Root CA que assinou o certificado do servidor RADIUS.
Além disso, o certificado do servidor RADIUS deve conter os atributos corretos de Extended Key Usage (EKU) — especificamente Server Authentication (OID 1.3.6.1.5.5.7.3.1). Sem isto, o suplicante Android irá silenciosamente abandonar o handshake TLS.
Para o lado do cliente, o Android requer que a chave privada e o certificado sejam agrupados, tipicamente num formato PKCS#12 (.p12 ou .pfx).
Integração com o Ecossistema da Purple
Embora o EAP-TLS proteja os seus dispositivos corporativos e infraestrutura operacional, os operadores de espaços também devem gerir o acesso de visitantes. É aqui que uma estratégia de dual-SSID se torna crítica. O seu SSID corporativo utiliza 802.1X EAP-TLS, enquanto o seu SSID público aproveita a plataforma Guest WiFi da Purple. Esta separação garante a segurança operacional, permitindo que a equipa de marketing aproveite o WiFi Analytics na rede de convidados. Para uma visão mais ampla sobre a segurança da infraestrutura física, consulte Access Point Security: Your 2026 Enterprise Guide .
Guia de Implementação
A implementação de EAP-TLS em Android pode ser abordada manualmente para pequenas implementações BYOD ou via Mobile Device Management (MDM) para escala empresarial.
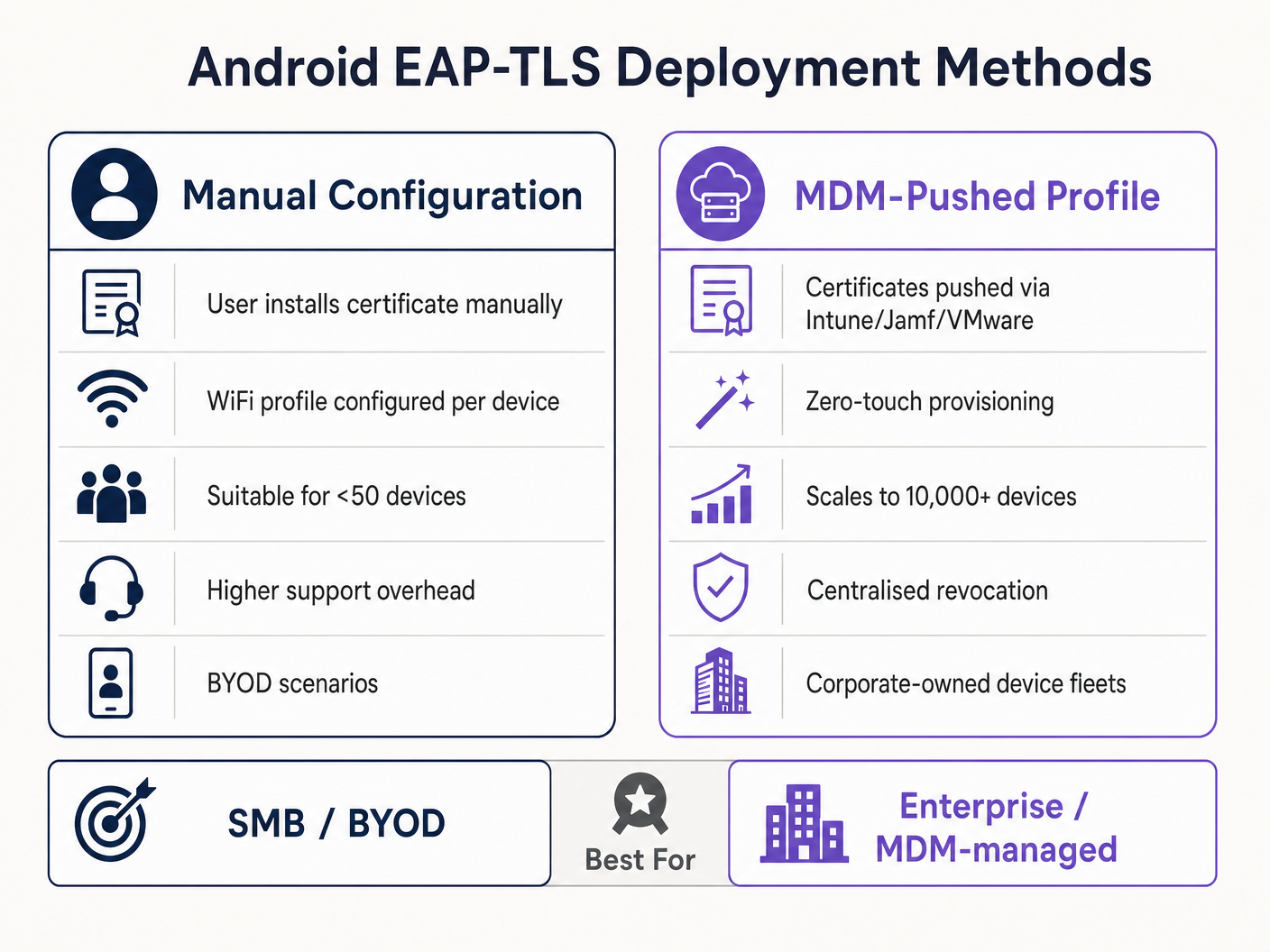
Método 1: Configuração Manual (BYOD / Pequena Escala)
Este método exige muito suporte e é recomendado apenas para implementações limitadas ou testes.
- Entrega de Certificados: Entregue de forma segura o certificado de cliente
.p12e o ficheiro.cerda Root CA ao dispositivo Android (por exemplo, via portal seguro ou e-mail encriptado). - Instalação:
- Navegue para Definições > Segurança > Encriptação e credenciais > Instalar um certificado.
- Instale a Root CA como um "certificado Wi-Fi".
- Instale o ficheiro
.p12, fornecendo a palavra-passe de extração quando solicitado.
- Configuração de Rede:
- Vá a Definições > Rede e internet > Wi-Fi e selecione "Adicionar rede".
- Introduza o SSID.
- Defina a Segurança para WPA/WPA2/WPA3-Enterprise.
- Defina o método EAP para TLS.
- Defina o certificado CA para a Root CA instalada.
- Defina o Estado do Certificado Online para Solicitar estado do certificado.
- Defina o Domínio para corresponder ao Subject Alternative Name (SAN) do certificado do servidor RADIUS.
- Selecione o Certificado de Cliente instalado.
- Introduza a Identidade (geralmente o UPN do utilizador ou o MAC do dispositivo).
Método 2: Perfil Distribuído por MDM (Escala Empresarial)
Para grandes infraestruturas, como um campus universitário ou um centro logístico em Transporte , o MDM é obrigatório. Isto proporciona aprovisionamento zero-touch e gestão do ciclo de vida.
- Integração PKI: Conecte o seu MDM (Intune, Workspace ONE, Jamf) à sua Autoridade de Certificação usando SCEP ou NDES.
- Perfil de Certificado: Crie um perfil de configuração para enviar a Root CA para o armazenamento de confiança do dispositivo. Crie um segundo perfil (SCEP) para solicitar e instalar automaticamente o certificado de cliente único.
- Perfil WiFi: Crie um perfil de configuração Wi-Fi que ligue o certificado implementadotes.
- Tipo de Segurança: WPA2/WPA3 Enterprise
- Tipo de EAP: EAP-TLS
- Método de Autenticação: Certificado
- Confiança do Servidor: Especifique a CA Raiz e o nome de domínio exato do servidor.
Para instruções detalhadas específicas da Microsoft, consulte o nosso guia: Como Usar o Microsoft Intune para Enviar Certificados WiFi para Dispositivos .
Melhores Práticas
- Imponha WPA3-Enterprise: Onde o hardware o suporta, imponha WPA3-Enterprise. O conjunto de segurança de 192 bits exige explicitamente EAP-TLS, garantindo os mais altos padrões criptográficos.
- Automatize o Ciclo de Vida dos Certificados: Os certificados de cliente expiram. Se depender de renovações manuais, enfrentará interrupções massivas. Implemente SCEP/NDES para renovar automaticamente os certificados 30 dias antes da expiração.
- Implemente um DNS Robusto: As verificações da Lista de Revogação de Certificados (CRL) e OCSP exigem uma resolução DNS fiável a partir da extremidade. Leia mais em Proteja a Sua Rede com DNS e Segurança Robustos .
- Segmentação de VLAN: Mapeie as sessões autenticadas por EAP-TLS para VLANs específicas com base nos atributos do certificado (por exemplo, separando terminais POS de tablets de gestores) usando atributos RADIUS como
Tunnel-Private-Group-Id.
Resolução de Problemas e Mitigação de Riscos
Quando os dispositivos Android não conseguem ligar via EAP-TLS, o problema reside quase sempre na cadeia de certificados ou na configuração RADIUS.
- Sintoma: Dispositivos Android 11+ desligam-se imediatamente ou mostram "Erro de autenticação" sem solicitar ao utilizador.
- Causa Raiz: O dispositivo não confia no certificado do servidor RADIUS. O campo "Domínio" no perfil WiFi deve corresponder exatamente ao SAN do certificado do servidor, e a CA Raiz deve estar instalada.
- Sintoma: A ligação expira durante o handshake TLS.
- Causa Raiz: O servidor RADIUS não consegue aceder ao ponto de distribuição CRL para verificar o estado de revogação do certificado do cliente. Certifique-se de que o seu servidor RADIUS tem acesso HTTP de saída aos pontos finais CRL da sua PKI.
- Sintoma: Dispositivos Windows ligam-se, mas dispositivos Android falham.
- Causa Raiz: Falta de EKU
Server Authenticationno certificado RADIUS, ou o suplicante Android está a tentar usar um conjunto de cifras não suportado. Verifique os registos RADIUS para falhas de negociação TLS.
- Causa Raiz: Falta de EKU
ROI e Impacto nos Negócios
A transição para EAP-TLS exige um investimento inicial em infraestrutura PKI e MDM, mas o retorno do investimento é substancial para líderes de TI seniores.
- Redução de Custos do Helpdesk: As redefinições de palavra-passe representam 20-30% dos tickets do helpdesk de TI. A autenticação baseada em certificados elimina as políticas de rotação de palavra-passe para acesso à rede, reduzindo drasticamente os custos de suporte.
- Mitigação de Riscos: EAP-TLS oferece imunidade contra a recolha de credenciais e ataques de dicionário offline. O custo de uma única violação numa indústria regulamentada como Saúde excede em muito o custo de implementação de uma PKI.
- Continuidade Operacional: O provisionamento automatizado de certificados garante que dispositivos operacionais críticos — desde scanners de armazém a sistemas POS de retalho — nunca saiam da rede devido a credenciais expiradas. À medida que a Purple continua a expandir o seu alcance, destacada por movimentos estratégicos recentes como Purple Sinaliza Ambições no Ensino Superior com a Nomeação do VP de Educação Tim Peers , a conectividade fundamental robusta torna-se o facilitador para análises avançadas e envolvimento.
Key Definitions
802.1X
An IEEE standard for port-based Network Access Control (PNAC) that provides an authentication mechanism to devices wishing to attach to a LAN or WLAN.
The foundational framework that prevents unauthorised devices from accessing the corporate network at the edge.
EAP-TLS
Extensible Authentication Protocol with Transport Layer Security. An authentication framework that uses X.509 certificates for mutual authentication between the client and the server.
Considered the most secure EAP type, it eliminates password reliance, making it essential for high-security environments.
RADIUS
Remote Authentication Dial-In User Service. A networking protocol that provides centralised Authentication, Authorization, and Accounting (AAA) management.
The server component (e.g., Cisco ISE, Microsoft NPS) that validates the Android device's certificate against the PKI.
Supplicant
The client device (in this case, the Android smartphone or tablet) that is requesting access to the network.
Understanding the supplicant's specific OS constraints (like Android 11's strict validation) is key to a successful deployment.
Authenticator
The network device (the WiFi Access Point) that facilitates the authentication process between the Supplicant and the RADIUS server.
The AP does not make the decision; it merely enforces the port control based on the RADIUS server's response.
PKI
Public Key Infrastructure. A set of roles, policies, hardware, software, and procedures needed to create, manage, distribute, use, store, and revoke digital certificates.
The backbone of EAP-TLS. Without a robust PKI, certificate-based authentication is impossible.
SCEP
Simple Certificate Enrollment Protocol. A protocol designed to make the issuing and revocation of digital certificates as scalable as possible.
Used by MDM platforms to automatically provision client certificates to Android devices without user intervention.
SAN
Subject Alternative Name. An extension to X.509 that allows various values to be associated with a security certificate.
Android 11+ requires the 'Domain' field in the WiFi profile to match the SAN of the RADIUS server's certificate.
Worked Examples
A national retail chain needs to deploy 5,000 Android-based point-of-sale (POS) tablets. The security team mandates that these devices must not use shared passwords and must be immune to credential phishing. How should the infrastructure team approach this deployment?
The team must deploy a Mobile Device Management (MDM) solution integrated with their internal Public Key Infrastructure (PKI) via SCEP. The MDM will push a configuration profile containing the Root CA certificate, automatically request a unique client certificate for each POS tablet, and configure the WPA3-Enterprise WiFi profile to use EAP-TLS. The RADIUS server will be configured to assign these devices to an isolated POS VLAN based on successful certificate validation.
A hospital IT manager is upgrading the wireless network. Following the upgrade, older Android 9 devices connect successfully to the EAP-TLS network, but newly procured Android 12 devices fail to authenticate, citing a trust error.
The IT manager must update the WiFi configuration profile pushed to the devices. Android 11+ enforces strict server certificate validation. The profile must be updated to explicitly define the Root CA certificate to trust and specify the exact 'Domain' (matching the RADIUS server's SAN) to prevent MitM attacks.
Practice Questions
Q1. Your organisation is migrating from PEAP-MSCHAPv2 to EAP-TLS. During the pilot phase, several Android 13 devices fail to connect. The RADIUS logs show that the TLS handshake is initiated but dropped by the client before the client certificate is sent. What is the most likely configuration error?
Hint: Consider the strict validation requirements introduced in recent Android versions regarding the server's identity.
View model answer
The most likely error is that the WiFi profile pushed to the Android 13 devices does not correctly specify the 'Domain' suffix match, or the Root CA is not properly linked in the profile. Android drops the connection to prevent a Man-in-the-Middle attack because it cannot validate the RADIUS server's certificate.
Q2. You are designing the architecture for a large stadium deployment. The client wants to use EAP-TLS for all staff devices. What specific infrastructure component must be scaled up compared to a standard WPA2-PSK network, and why?
Hint: EAP-TLS involves complex cryptographic operations during the connection phase.
View model answer
The RADIUS server infrastructure must be significantly scaled up. EAP-TLS requires full mutual certificate validation (asymmetric cryptography), which is computationally expensive. In a stadium environment with thousands of devices potentially roaming or authenticating simultaneously, an undersized RADIUS deployment will cause authentication timeouts and connection failures.
Q3. A client certificate is compromised on a lost Android tablet. What is the exact mechanism by which the network prevents this device from connecting via EAP-TLS?
Hint: How does the RADIUS server know the certificate is no longer valid before its expiration date?
View model answer
The IT administrator revokes the client certificate in the PKI. The PKI updates its Certificate Revocation List (CRL) or OCSP responder. When the lost tablet attempts to connect, the RADIUS server checks the client certificate against the CRL/OCSP. Seeing it is revoked, the RADIUS server rejects the authentication request.



