eduroam e 802.1X: Autenticação WiFi Segura para o Ensino Superior
Este guia de referência técnica e autoritário explica a arquitetura, implementação e segurança da autenticação eduroam e 802.1X. Concebido para gestores de TI e arquitetos de rede, abrange passos práticos de implementação, seleção de métodos EAP e como os operadores de espaços podem suportar com segurança o roaming académico.
GuidesSlugPage.podcastTitle
GuidesSlugPage.podcastTranscript
- Resumo Executivo
- Análise Técnica Aprofundada: 802.1X e a Arquitetura eduroam
- O Triângulo 802.1X
- A Hierarquia de Proxy RADIUS do eduroam
- Métodos EAP: Segurança vs. Implementabilidade
- Guia de Implementação
- 1. Preparação da Infraestrutura
- 2. Gestão de Certificados
- 3. Configuração do Cliente (A Ferramenta CAT)
- 4. Atribuição e Segmentação de VLAN
- Melhores Práticas e Recomendações Neutras em Relação ao Fornecedor
- Resolução de Problemas e Mitigação de Riscos
- ROI e Impacto no Negócio

Resumo Executivo
Para as instituições de ensino superior e os espaços que acolhem os seus estudantes e funcionários, fornecer conectividade sem fios segura e contínua já não é um luxo — é um mandato operacional. O padrão para esta conectividade é o eduroam, um serviço de roaming global construído sobre a estrutura IEEE 802.1X.
Este guia fornece a gestores de TI, arquitetos de rede e diretores de operações de espaços uma referência abrangente e neutra em relação a fornecedores para compreender, implementar e resolver problemas com 802.1X e eduroam. Vamos além dos modelos teóricos básicos para abordar as realidades práticas do WiFi empresarial, incluindo gestão de certificados, arquitetura de proxy RADIUS e integração com estratégias mais amplas de rede de convidados.
Quer esteja a atualizar uma rede universitária antiga ou a configurar um centro de conferências para suportar visitantes académicos, implementar 802.1X corretamente mitiga riscos de segurança significativos — particularmente o roubo de credenciais — ao mesmo tempo que reduz drasticamente os custos de suporte. Para espaços fora do ensino superior tradicional, compreender estes padrões é crítico para avaliar federações de roaming comerciais como o OpenRoaming, que partilham a mesma arquitetura subjacente.
Análise Técnica Aprofundada: 802.1X e a Arquitetura eduroam
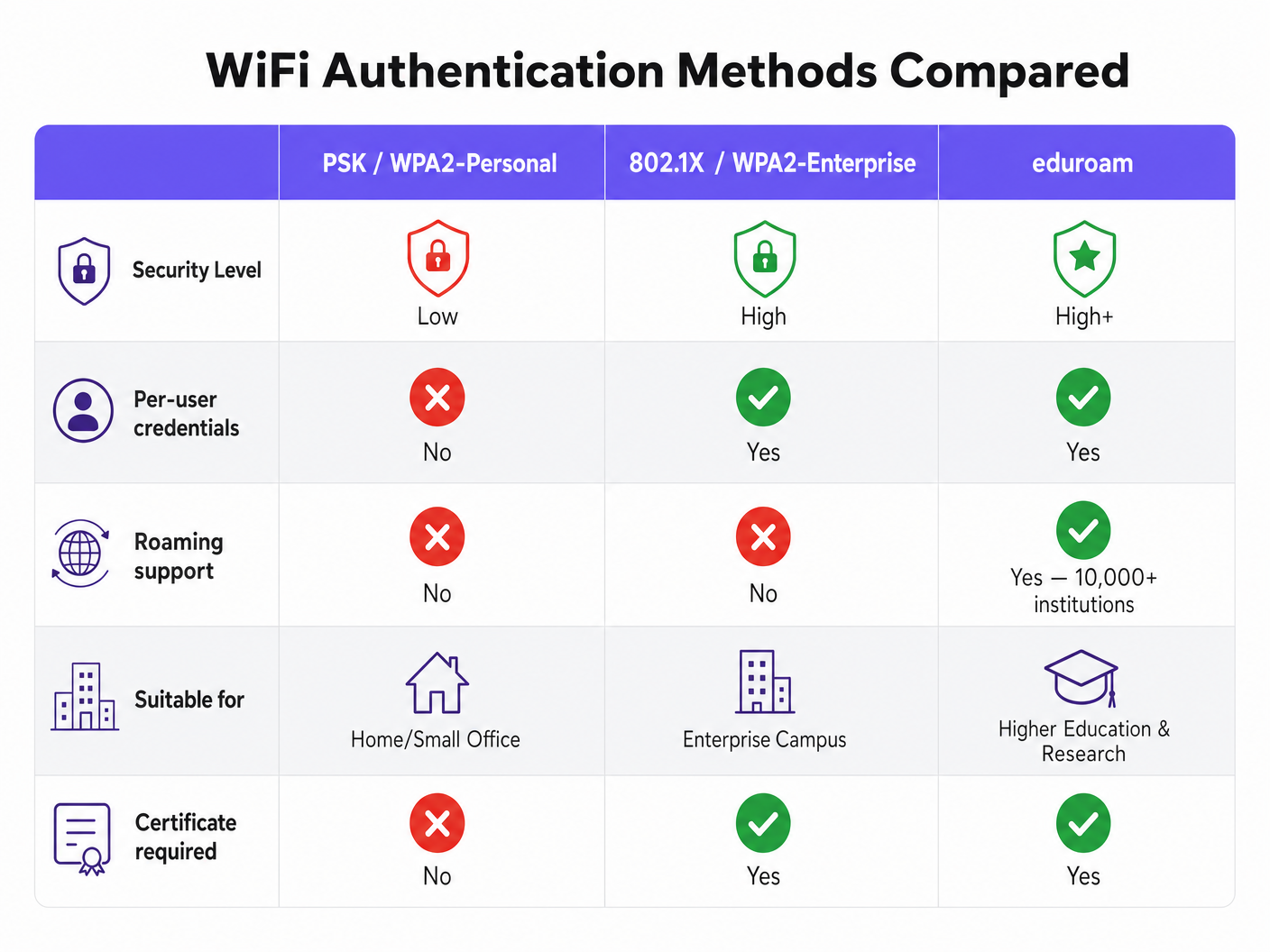
No seu cerne, o eduroam é uma implementação do IEEE 802.1X, o padrão para controlo de acesso à rede baseado em porta. Embora originalmente concebido para redes com fios, o 802.1X forma a base da segurança WPA2-Enterprise e WPA3-Enterprise.
O Triângulo 802.1X
A estrutura 802.1X baseia-se em três componentes distintos que interagem para autorizar o acesso:
- Suplicante: O dispositivo cliente (por exemplo, o portátil ou smartphone de um estudante) que solicita acesso à rede.
- Autenticador: O dispositivo de acesso à rede (por exemplo, um ponto de acesso sem fios ou um switch gerido). Atua como um porteiro, bloqueando todo o tráfego, exceto as mensagens de autenticação, até que o dispositivo seja autorizado.
- Servidor de Autenticação: O sistema de backend que valida as credenciais, quase universalmente um servidor RADIUS (Remote Authentication Dial-In User Service).
Quando um dispositivo se conecta, o Autenticador estabelece uma porta controlada. Ele passa mensagens do Extensible Authentication Protocol (EAP) entre o Suplicante e o Servidor de Autenticação. Se as credenciais forem válidas, o servidor retorna uma mensagem RADIUS Access-Accept, e o Autenticador abre a porta para o tráfego IP padrão.
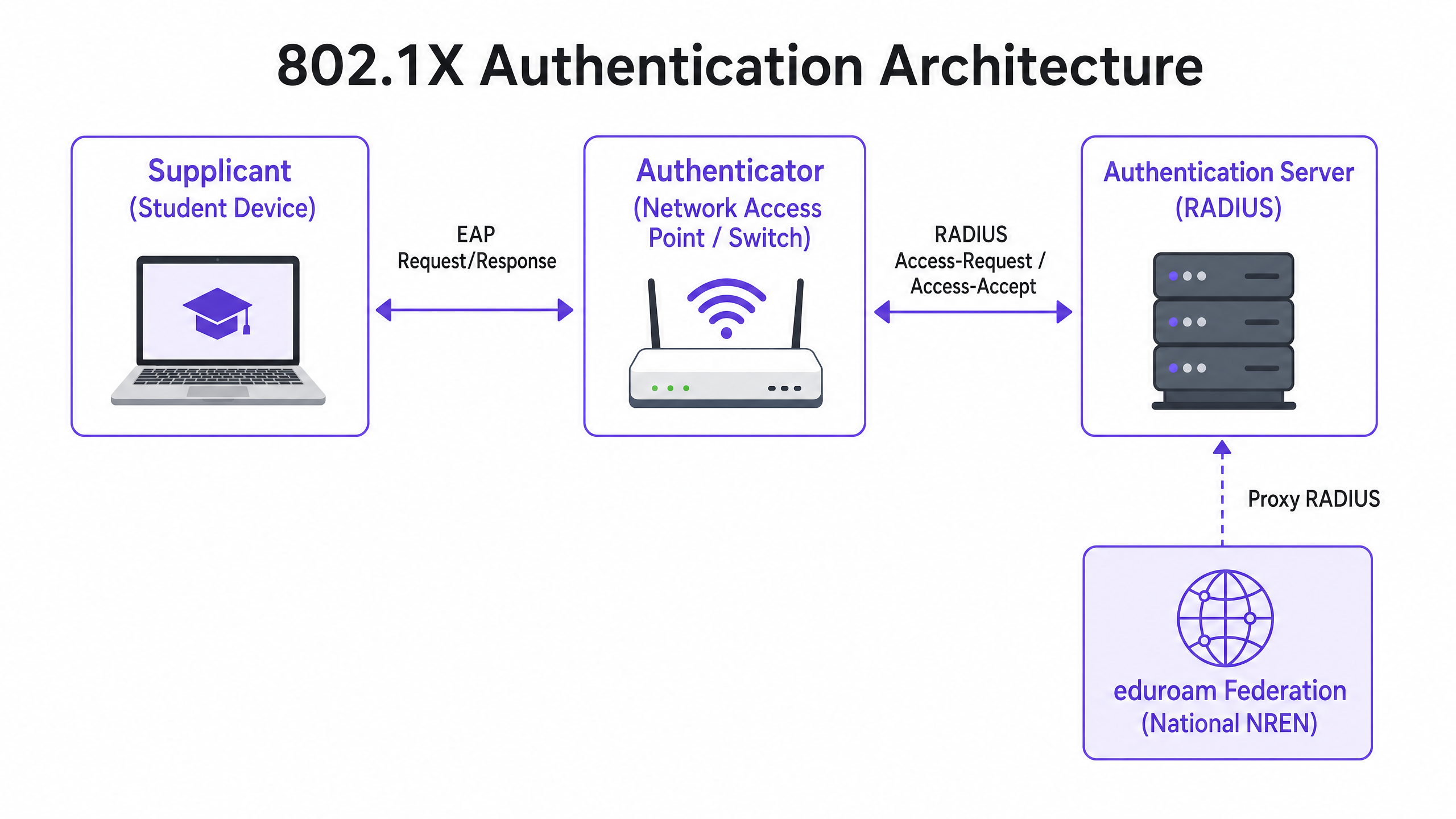
A Hierarquia de Proxy RADIUS do eduroam
O que torna o eduroam único é a sua arquitetura federada. Permite que os utilizadores se autentiquem em qualquer instituição participante usando as suas credenciais de origem, sem que a instituição anfitriã precise de uma cópia dessas credenciais.
Isto é conseguido através de uma cadeia hierárquica de proxy RADIUS. Quando um utilizador de username@university.ac.uk se conecta ao SSID eduroam num local anfitrião:
- O dispositivo do utilizador envia um pedido de autenticação no formato
username@university.ac.uk. - O servidor RADIUS do local anfitrião examina o realm (a parte após o
@). Reconhecendo-o como um domínio externo, ele encaminha o pedido para o servidor RADIUS nacional de nível superior (operado pela National Research and Education Network, ou NREN). - O servidor nacional encaminha o pedido para o servidor RADIUS da instituição de origem (
university.ac.uk). - A instituição de origem valida as credenciais e retorna uma mensagem
Access-AcceptouAccess-Rejectpela cadeia.
Todo este processo geralmente é concluído em menos de dois segundos. Crucialmente, a palavra-passe do utilizador nunca é exposta à instituição anfitriã ou aos proxies intermédios; é protegida dentro de um túnel EAP encriptado estabelecido diretamente entre o suplicante e o servidor RADIUS de origem.
Métodos EAP: Segurança vs. Implementabilidade
A escolha do método EAP dita como o túnel encriptado é formado e como as credenciais são trocadas. A Definição de Serviço de Política eduroam restringe fortemente os métodos permitidos para garantir a segurança.
- PEAP (Protected EAP): A implementação mais comum. Estabelece um túnel TLS usando um certificado do lado do servidor no servidor RADIUS. O cliente autentica-se então dentro deste túnel, tipicamente usando MSCHAPv2 (nome de utilizador e palavra-passe). É relativamente fácil de implementar, mas vulnerável a ataques de pontos de acesso maliciosos se os clientes não estiverem configurados para validar estritamente o certificado do servidor.
- EAP-TLS: O padrão ouro para segurança. Requer autenticação mútua, o que significa que tanto o servidor RADIUS quanto o dispositivo cliente devem apresentar certificados válidos. Embora imune a phishing de credenciais, requer uma robusta Public Key Infrastructure (PKI) para emitir e gerir certificados de cliente, tornando-o mais complexo de implementar em escala.
Guia de Implementação
A implementação de 802.1X e eduroam requer uma coordenação cuidadosa entre a infraestrutura de rede, a gestão de identidades e a configuração do cliente.
1. Preparação da Infraestrutura
Certifique-se de que os seus pontos de acesso sem fios e controladores suportam WPA2-Enterprise/WPA3-Enterprise e 802.1X. Qualquer hardware moderno de nível empresarial (Cisco, Aruba, Juniper, etc.) cumprirá este requisito. Deve também implementar uma infraestrutura RADIUS robusta (por exemplo, FreeRADIUS, Cisco ISE, Aruba ClearPass) capaz de lidar com a carga de autenticação esperada e de encaminhar pedidos.
2. Gestão de Certificados
Para implementações PEAP, o seu servidor RADIUS requer um certificado TLS emitido por uma Certificate Authority (CA) confiável pelos seus clientes. Não utilize certificados autoassinados para implementações eduroam de produção. O certificado deve ser renovado regularmente para evitar interrupções na autenticação.
3. Configuração do Cliente (A Ferramenta CAT)
O ponto de falha mais comum nas implementações eduroam é a má configuração do cliente. Os utilizadores que se conectam manualmente muitas vezes não conseguem configurar a validação do certificado, deixando-os vulneráveis à recolha de credenciais.
Para mitigar isto, as instituições devem usar a eduroam Configuration Assistant Tool (CAT) ou uma solução MDM para distribuir perfis pré-configurados. Estes perfis configuram automaticamente o método EAP correto, fixam o certificado do servidor RADIUS esperado e definem os protocolos de autenticação internos apropriados.
4. Atribuição e Segmentação de VLAN
Uma implementação madura utiliza atributos RADIUS para atribuir VLANs dinamicamente com base na identidade do utilizador.
- Utilizadores Domésticos: Atribuídos a VLANs internas com acesso apropriado aos recursos do campus.
- Utilizadores Visitantes: Atribuídos a uma VLAN de convidado restrita com acesso apenas à internet.
Esta segmentação é vital para a segurança e conformidade, garantindo que os dispositivos visitantes não possam aceder a redes internas sensíveis.
Melhores Práticas e Recomendações Neutras em Relação ao Fornecedor
- Priorizar WPA3: Para novas implementações, ative o WPA3-Enterprise para beneficiar da encriptação obrigatória de 192 bits e de uma proteção melhorada contra ataques de dicionário offline.
- Impor a Validação de Certificados: Obrigue o uso de perfis de configuração (via CAT ou MDM) para garantir que os suplicantes validam estritamente o certificado do servidor RADIUS antes de transmitir credenciais.
- Usar RadSec: Ao configurar ligações de proxy RADIUS para a federação nacional, use RadSec (RADIUS over TLS) em vez de UDP simples. Isto encripta o tráfego do proxy e melhora a fiabilidade em ligações WAN.
- Integrar com Soluções de Convidados: eduroam serve apenas utilizadores com credenciais académicas. Deve manter uma solução Guest WiFi separada e segura para contratados, visitantes públicos e participantes em eventos.
- Rever Infraestrutura Relacionada: Garanta que a sua rede subjacente é segura. Leia o nosso guia Proteja a Sua Rede com DNS e Segurança Fortes para mais detalhes. Se estiver a implementar infraestrutura temporária para eventos universitários, consulte Event WiFi: Planning and Deploying Temporary Wireless Networks ou a versão portuguesa Event WiFi: Planeamento e Implementação de Redes Sem Fios Temporárias .
Resolução de Problemas e Mitigação de Riscos
Quando a autenticação falha, a resolução sistemática de problemas é essencial.
- Isolar o Domínio da Falha: Determine se a falha é local (afetando os seus próprios utilizadores na sua própria rede), remota (afetando os seus utilizadores noutros locais) ou de entrada (afetando visitantes na sua rede).
- Verificar os Registos RADIUS: Os registos do servidor RADIUS são a fonte definitiva da verdade. Procure mensagens de
Access-Reject(indicando credenciais incorretas ou violações de política) ou timeouts (indicando problemas de conectividade do proxy). - Verificar a Validade do Certificado: Garanta que o certificado do servidor RADIUS não expirou e que a cadeia de certificados completa está a ser apresentada ao cliente.
- Monitorizar a Latência a Montante: A alta latência na ligação ao proxy RADIUS nacional pode causar timeouts no cliente, resultando em ligações falhadas mesmo com credenciais corretas.
ROI e Impacto no Negócio
Para instituições de ensino superior, o ROI de uma implementação eduroam adequada é medido na redução drástica de tickets de suporte. Ao eliminar captive portals e a introdução manual de palavras-passe, os helpdesks de TI observam uma queda significativa nas chamadas relacionadas com a conectividade. (O compromisso da Purple com este setor é evidente; veja Purple Signals Higher Education Ambitions with Appointment of VP Education Tim Peers ).
Para locais comerciais — como os de Hotelaria , Retalho , Saúde ou Transportes — o suporte ao eduroam Visitor Access (eVA) ou federações semelhantes como OpenRoaming proporciona uma experiência sem atritos para demografias de alto valor. Garante que os visitantes académicos podem conectar-se automaticamente e de forma segura, melhorando a satisfação e permitindo que o local mantenha uma segmentação de rede rigorosa. Se o seu local requer largura de banda dedicada para suportar isto, considere ler O Que É Uma Linha Alugada? Internet Empresarial Dedicada .
Ao planear atualizações de rede, a integração de capacidades 802.1X garante que a infraestrutura está pronta para redes modernas baseadas em identidade, estabelecendo as bases para WiFi Analytics avançados e serviços baseados em localização.
GuidesSlugPage.keyDefinitionsTitle
802.1X
An IEEE standard for port-based Network Access Control (PNAC). It provides an authentication mechanism to devices wishing to attach to a LAN or WLAN.
The foundational protocol for enterprise-grade WiFi security, replacing shared passwords (PSKs) with individualised authentication.
RADIUS (Remote Authentication Dial-In User Service)
A networking protocol that provides centralised Authentication, Authorization, and Accounting (AAA) management for users who connect and use a network service.
The backend server in an 802.1X deployment that actually checks the user's credentials against a directory (like Active Directory).
EAP (Extensible Authentication Protocol)
An authentication framework frequently used in wireless networks and point-to-point connections. It provides for the transport and usage of various authentication mechanisms.
The language spoken between the client device and the RADIUS server during the 802.1X handshake.
Supplicant
The client device (e.g., laptop, smartphone) or the software on that device attempting to authenticate to a network using 802.1X.
The entity requesting access. Its configuration (especially regarding certificate validation) is critical for security.
Authenticator
The network device (e.g., wireless access point, Ethernet switch) that facilitates the 802.1X authentication process by passing messages between the Supplicant and the Authentication Server.
The gatekeeper that blocks network traffic until the RADIUS server gives the green light.
PEAP (Protected Extensible Authentication Protocol)
An EAP method that encapsulates the EAP transaction within a TLS tunnel established using a server-side certificate, protecting the inner authentication (usually a password).
The most common authentication method for eduroam, balancing security with ease of deployment.
RadSec
A protocol for transmitting RADIUS data over TCP and TLS, rather than the traditional UDP.
Recommended for securing the proxy connections between institutions and the national eduroam federation, preventing interception of authentication traffic.
Realm
The portion of a user's identity following the '@' symbol (e.g., 'university.ac.uk' in 'user@university.ac.uk').
Used by RADIUS proxy servers to determine where to route the authentication request in a federated environment like eduroam.
GuidesSlugPage.workedExamplesTitle
A 400-room conference hotel adjacent to a major university frequently hosts academic symposiums. The IT Director wants to allow visiting academics to connect automatically without using the hotel's standard captive portal, but must ensure these visitors cannot access the hotel's corporate network or the standard guest network VLAN.
The hotel should implement eduroam Visitor Access (eVA) or join a commercial federation like OpenRoaming.
- The hotel configures a new SSID ('eduroam' or 'OpenRoaming') on their enterprise access points.
- The APs are configured to use WPA2-Enterprise/802.1X.
- The hotel deploys a local RADIUS server configured to proxy authentication requests for external realms to the national federation (for eduroam) or the OpenRoaming hub.
- Crucially, the local RADIUS server is configured to return a specific VLAN ID attribute in the
Access-Acceptmessage for all proxied authentications. - The access points place these authenticated users onto an isolated, internet-only VLAN, completely segmented from the hotel's corporate and standard guest traffic.
A university IT team notices a spike in compromised student accounts. Investigation reveals that students are connecting to a rogue access point broadcasting the 'eduroam' SSID at a local coffee shop. The rogue AP is using a self-signed certificate to harvest credentials via PEAP.
The IT team must immediately enforce strict certificate validation on all client devices.
- They must stop advising students to manually connect to the SSID and 'accept the certificate warning'.
- They deploy the eduroam Configuration Assistant Tool (CAT) for BYOD devices and update MDM profiles for managed devices.
- These profiles configure the supplicant to only trust the specific Certificate Authority (CA) that issued the university's RADIUS server certificate, and to verify the server's Common Name (CN).
- Once configured, if a student's device encounters the rogue AP, the EAP tunnel establishment will fail because the rogue certificate does not match the pinned CA/CN, preventing the transmission of credentials.
A retail chain wants to offer OpenRoaming across 50 locations using their existing guest WiFi infrastructure, which currently relies on an open SSID with a captive portal.
The retail chain must upgrade their network to support 802.1X and RADIUS proxying.
- The network team enables a new SSID broadcasting the OpenRoaming Consortium OI (Organization Identifier).
- They configure the access points to authenticate via 802.1X.
- They configure their central RADIUS server to proxy requests to the OpenRoaming federation hub.
- They ensure their internet backhaul can support the expected increase in automated connections, potentially upgrading to dedicated leased lines if necessary.
GuidesSlugPage.practiceQuestionsTitle
Q1. Your university is deploying a new wireless network. The CISO mandates that credential phishing via rogue access points must be mathematically impossible. Which EAP method must you select?
GuidesSlugPage.hintPrefixConsider which method relies on passwords versus which relies entirely on cryptographic keys.
GuidesSlugPage.viewModelAnswer
You must select EAP-TLS. Unlike PEAP, which relies on a password inside a TLS tunnel, EAP-TLS requires mutual certificate authentication. Because the client device authenticates using a cryptographic certificate rather than a password, there are no credentials for a rogue access point to phish.
Q2. A visiting researcher from another university complains they cannot connect to your eduroam network. Your local users are connecting fine. You check your local RADIUS server logs and see the request arriving, but it times out before an Access-Accept is received. What is the most likely cause?
GuidesSlugPage.hintPrefixThink about the path the authentication request takes for a visiting user versus a local user.
GuidesSlugPage.viewModelAnswer
The most likely cause is a connectivity or latency issue between your local RADIUS server and the national NREN RADIUS proxy. Because local users authenticate directly against your server, they are unaffected. The visiting user's request must be proxied upstream, and a timeout indicates the response from the home institution is not returning in time.
Q3. You are a network architect for a retail chain located near a large university. You want to offer seamless WiFi to students using eduroam Visitor Access (eVA), but you must comply with PCI DSS for your point-of-sale terminals. How do you securely integrate eVA?
GuidesSlugPage.hintPrefixHow does 802.1X allow the network access point to differentiate traffic after authentication?
GuidesSlugPage.viewModelAnswer
You integrate eVA by configuring your RADIUS server to assign all successful eVA authentications to a dedicated, internet-only guest VLAN. The Access-Accept message from the RADIUS server must include the specific VLAN ID. This ensures student devices are completely segmented from the PCI-compliant VLAN used by the point-of-sale terminals, satisfying compliance requirements.



