WiFi em Comboios: O Guia Completo para Operadores Ferroviários e Passageiros
Este guia abrangente detalha a arquitetura, os desafios de implementação e as oportunidades comerciais do WiFi para passageiros em comboios. Concebido para líderes seniores de TI e operações, abrange a agregação de backhaul, a segmentação de rede e como transformar uma responsabilidade de conformidade em análises acionáveis dos passageiros.
🎧 Ouça este Guia
Ver Transcrição
- Resumo Executivo
- Análise Técnica Detalhada: A Arquitetura de Três Camadas
- Camada 1: Backhaul WAN e Agregação
- Camada 2: A Rede a Bordo e a Segmentação
- Camada 3: Acesso de Passageiros e Hardware de Cabine
- Guia de Implementação: Implementação e Conformidade
- ROI e Impacto no Negócio: Transformar Dados em Inteligência
- Ouça o Briefing
Resumo Executivo
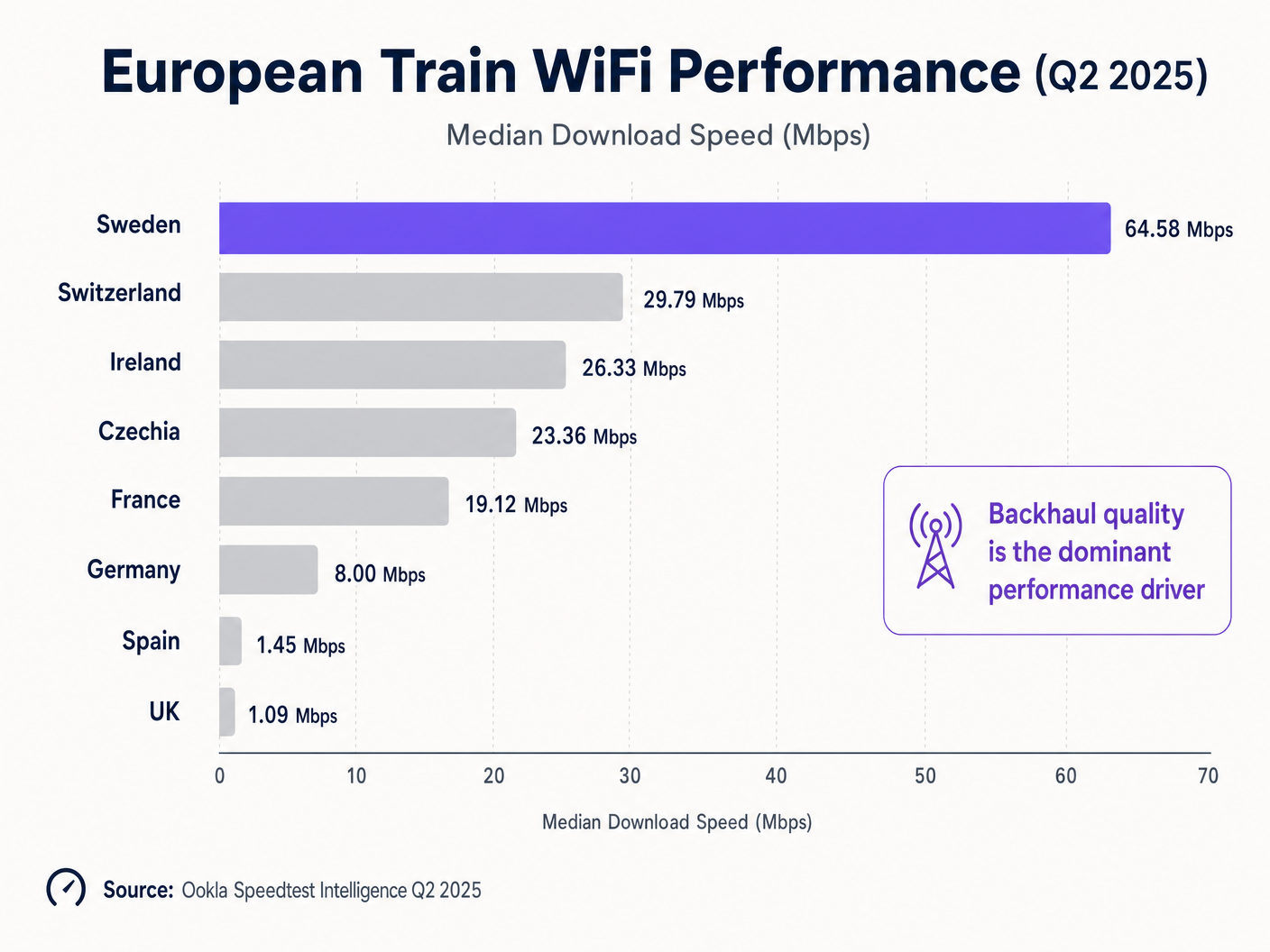
Para os operadores ferroviários, o WiFi de alta qualidade em comboios passou de um benefício para os passageiros a uma infraestrutura operacional essencial. A diferença entre as implementações de topo e as legadas é notória: os dados do Q2 de 2025 da Ookla mostram a Suécia a fornecer velocidades médias de download de 64.58 Mbps, enquanto o Reino Unido se arrasta com 1.09 Mbps [1]. Esta diferença de 59 vezes não é principalmente um problema tecnológico; é uma falha de arquitetura e estratégia de investimento.
Este guia fornece um plano de arquitetura neutro em relação a fornecedores para diretores de TI, arquitetos de rede e líderes de operações de espaços. Dissecamos a arquitetura de três camadas necessária para uma conectividade a bordo resiliente, exploramos o requisito crítico de segurança da segmentação de rede e demonstramos como plataformas como Guest WiFi transformam dados de conexão brutos em inteligência comercial acionável. Quer esteja a gerir uma rota interurbana de alta velocidade ou um serviço regional de passageiros, os princípios de agregação de backhaul e de captura de dados em conformidade com o GDPR permanecem idênticos.
Análise Técnica Detalhada: A Arquitetura de Três Camadas
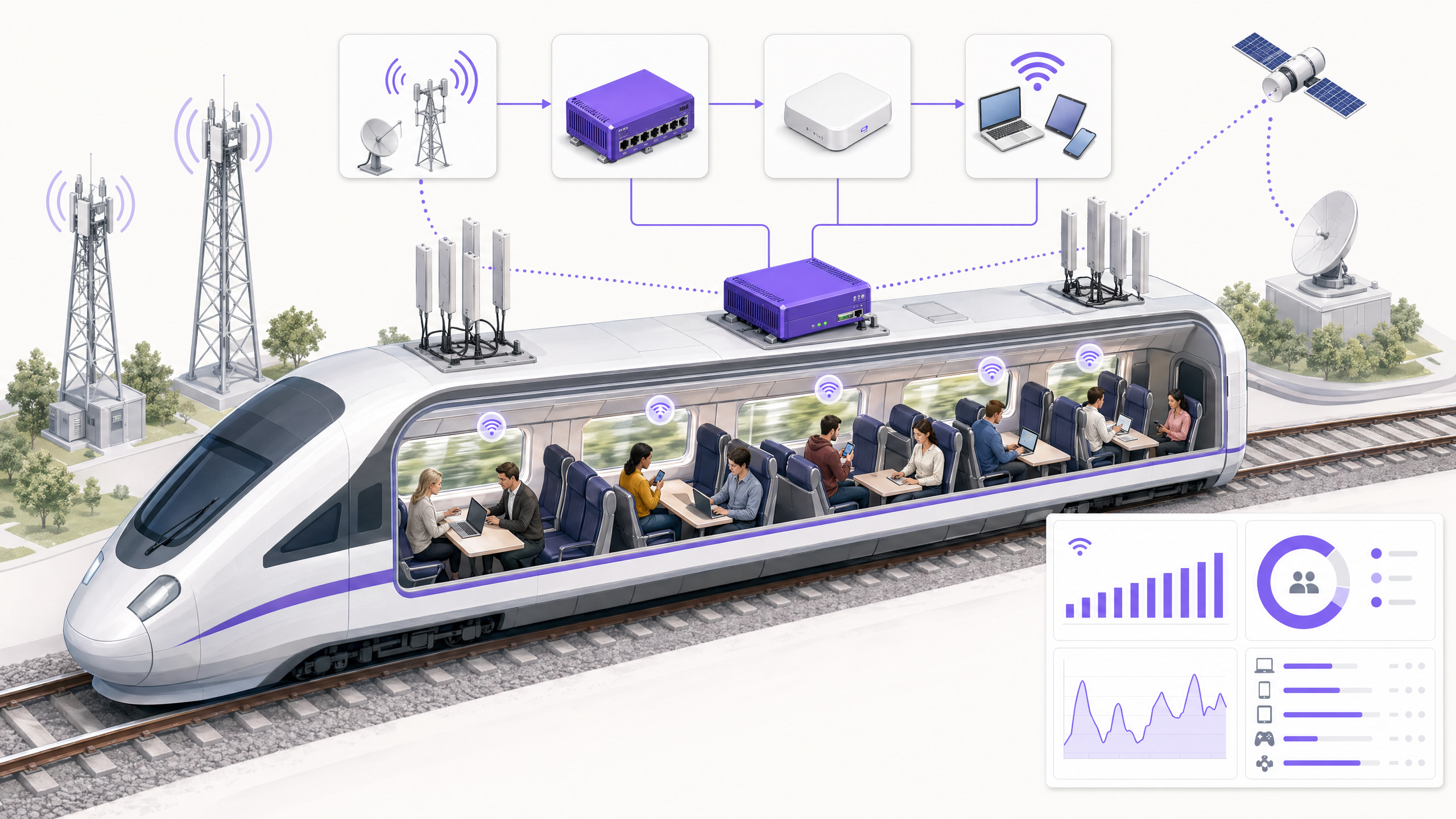
Uma implementação moderna de WiFi em comboios é fundamentalmente diferente das implementações estáticas encontradas em Retalho ou Hotelaria . A rede deve manter a persistência da sessão enquanto se move a 300 km/h, alternando entre células ao longo da via e penetrando em material circulante fortemente isolado.
Camada 1: Backhaul WAN e Agregação
O limite da sua experiência de passageiro é ditado inteiramente pela sua capacidade de backhaul. Um único modem LTE com uma antena montada no tejadilho já não é viável. As arquiteturas modernas utilizam um WAN Gateway para agregar múltiplos uplinks:
- Cellular Bonding: Combinação de conexões 4G/5G de múltiplos Operadores de Rede Móvel (MNOs) para mitigar pontos cegos de cobertura de rede única.
- Infraestrutura ao Longo da Via: Redes sem fios dedicadas de 5 GHz ou 60 GHz implementadas ao longo do corredor ferroviário.
- LEO Satellite: Constelações de órbita terrestre baixa (por exemplo, Starlink) que fornecem um débito de 100-200 Mbps em secções rurais ou transfronteiriças onde o serviço celular terrestre falha [2].
Camada 2: A Rede a Bordo e a Segmentação
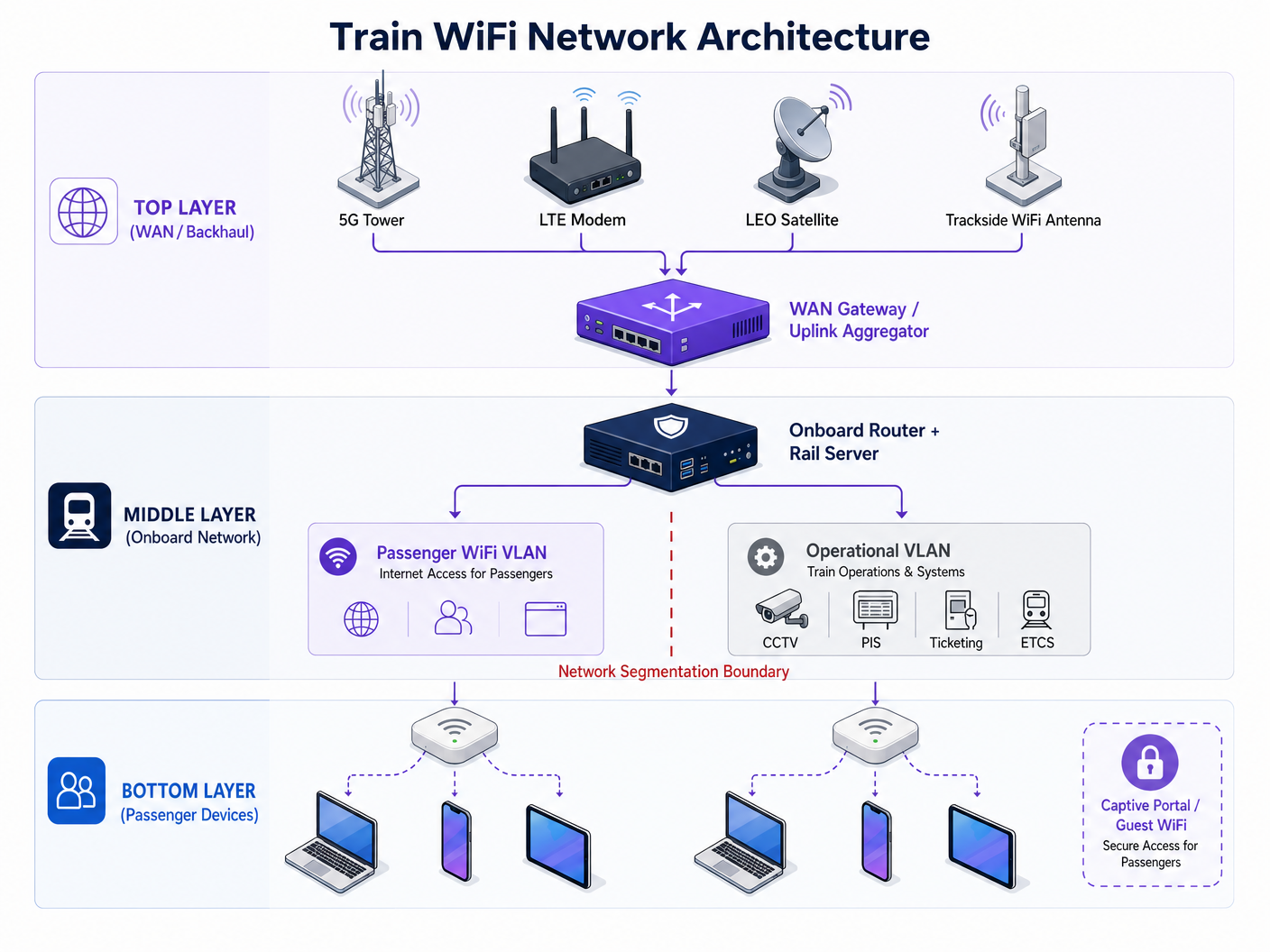
O WAN Gateway alimenta um router a bordo e um servidor ferroviário. Esta camada gere a tarefa crítica de Segmentação de Rede.
> "O WiFi para passageiros deve funcionar numa VLAN completamente isolada, sem caminho de encaminhamento para a rede operacional que transporta feeds de CCTV, Sistemas de Informação de Passageiros (PIS) ou dados de sinalização do European Train Control System (ETCS)."
Um ciberataque em 2024 a uma rede WiFi de passageiros no Reino Unido demonstrou os graves riscos de uma segmentação inadequada, onde vulnerabilidades viradas para o público comprometeram uma infraestrutura terminal mais ampla [3]. A implementação de autenticação baseada em porta IEEE 802.1X e regras rigorosas de firewall inter-VLAN é um requisito de segurança inegociável. Além disso, o servidor ferroviário oferece alojamento de aplicações em contentores, permitindo que o cache de conteúdo local e os serviços de captive portal funcionem mesmo quando a conectividade de backhaul falha.
Camada 3: Acesso de Passageiros e Hardware de Cabine
A camada final consiste nos pontos de acesso (APs) distribuídos por todas as carruagens. O hardware legado é um entrave significativo ao desempenho. Na Alemanha, a atualização de WiFi 4 (802.11n) para WiFi 5 (802.11ac) resultou numa melhoria de velocidade de 241%, enquanto a mudança de tráfego da banda de 2.4 GHz para 5 GHz proporcionou um aumento de 328% [1]. No entanto, quase 40% das conexões ferroviárias europeias ainda dependem de WiFi 4.
Guia de Implementação: Implementação e Conformidade
A implementação de WiFi em comboios é um projeto complexo de integração de sistemas. Os seguintes passos descrevem uma estratégia de implementação robusta:
- Realize uma Auditoria de Backhaul: Antes de especificar os APs de cabine, audite a sua rota para identificar lacunas de cobertura celular. Desenhe a sua estratégia de agregação de uplink em torno destes pontos cegos.
- Especifique Janelas Permeáveis a RF: As janelas modernas dos comboios utilizam revestimentos metálicos para eficiência térmica, o que pode atenuar os sinais celulares em 20-30 dB. Antenas montadas no tejadilho que alimentam APs internos são obrigatórias para superar este problema.
- Implemente um Captive Portal Robusto: O captive portal é a interface principal entre o passageiro e o operador. Deve capturar credenciais verificadas de forma segura (e-mail ou login social) enquanto apresenta os termos de serviço.
- Garanta a Conformidade com o GDPR: Os operadores devem estabelecer uma base legal para o tratamento de dados dos passageiros. O consentimento deve ser dado livremente e registado de forma inequívoca. Proteja a Sua Rede com DNS e Segurança Fortes é uma consideração crítica aqui.
ROI e Impacto no Negócio: Transformar Dados em Inteligência
Fornecer WiFi gratuito representa uma despesa operacional significativa. Para gerar ROI, os operadores devem aproveitar a camada de conexão para recolher dados primários.
Quando os passageiros se autenticam através de um captive portal compatível, os operadores podem construir perfis ricos de comportamento de viagem. É aqui que o WiFi Analytics se torna transformador. Ao analisar as frequências de conexão, os tempos de permanência em estações específicas e os padrões de ocupação das carruagens, os operadores obtêm inteligência operacional que rivaliza com os insights recolhidos em centros de Transport e aeroportos.
Por exemplo, compreender que um grupo específico de viajantes de negócios se conecta consistentemente no serviço das 07:30 permite comunicações de marketing direcionadas e de alto valor ou a integração em programas de fidelidade. Esta abordagem baseada em dados transforma a rede WiFi fde um centro de custos para um ativo gerador de receita.
Ouça o Briefing
Para uma análise mais aprofundada da arquitetura e estratégia comercial, ouça o nosso briefing técnico completo:
Referências: [1] Ookla Speedtest Intelligence, "Comboios Rápidos, Wi-Fi Lento: A Realidade da Conectividade a Bordo na Europa e Ásia", Q2 2025. [2] Testes da Indústria, Integração de Satélites LEO para Mobilidade, 2024-2025. [3] Railway Technology, "Rede WiFi de passageiros do Reino Unido hackeada", Setembro 2024.
Termos-Chave e Definições
WAN Aggregation
The process of combining multiple Wide Area Network connections (e.g., two 5G connections and a satellite link) into a single logical connection to increase throughput and resilience.
Critical for trains moving through varying cellular coverage areas to prevent dropped connections.
Network Segmentation (VLAN)
Dividing a computer network into smaller, isolated sub-networks. Virtual Local Area Networks (VLANs) keep traffic separated logically even if it shares the same physical switches.
Essential for preventing a compromised passenger device from accessing critical train control systems.
Captive Portal
A web page that a user of a public-access network is obliged to view and interact with before access is granted.
Used to enforce terms of service, collect user data, and secure GDPR consent.
RF Attenuation
The reduction in signal strength as radio waves pass through a medium.
Modern train windows with metallic thermal coatings cause massive RF attenuation, requiring roof-mounted antennas.
LEO Satellite
Low Earth Orbit satellites that operate much closer to Earth than traditional geostationary satellites, offering lower latency and higher bandwidth.
Increasingly used as a backhaul solution for trains in rural or cross-border areas.
IEEE 802.1X
An IEEE Standard for port-based Network Access Control (PNAC), providing an authentication mechanism to devices wishing to attach to a LAN or WLAN.
Used to secure the operational network interfaces on the train from unauthorized access.
Rail Server
A ruggedized onboard computer designed to host containerized applications locally on the train.
Used to host local entertainment, caching, and captive portal services to reduce reliance on the WAN link.
First-Party Data
Information a company collects directly from its customers and owns.
The primary commercial output of a properly configured Guest WiFi network.
Estudos de Caso
A regional rail operator running 4-carriage commuter trains through a mix of dense urban areas and deep rural valleys is experiencing severe passenger complaints regarding WiFi dropouts. Their current setup uses a single 4G LTE modem per train. How should they redesign their architecture?
- Upgrade the WAN Backhaul: Replace the single LTE modem with a WAN Gateway capable of uplink aggregation. Install dual-SIM routers using two different Mobile Network Operators (MNOs) to provide failover in urban areas.
- Address Rural Gaps: For the deep valleys where cellular coverage is non-existent, integrate a LEO satellite terminal (e.g., Starlink Mobility) into the WAN Gateway as a secondary aggregated link.
- Local Caching: Deploy an onboard rail server to cache the captive portal and key journey information locally, ensuring the passenger UI remains responsive even during brief total connection losses in tunnels.
An intercity rail franchise is upgrading its fleet and wants to use the new onboard WiFi to gather passenger analytics for marketing, similar to how [Retail](/industries/retail) venues operate. What compliance and technical steps must they take?
- Captive Portal Deployment: Implement a robust captive portal that requires users to authenticate via email or social login before accessing the internet.
- GDPR Compliance: Ensure the portal explicitly asks for opt-in consent for marketing communications. Pre-ticked boxes must not be used. The system must log the timestamp and version of the privacy policy consented to.
- Analytics Integration: Route the authenticated session data into a centralized WiFi Analytics platform to track journey frequency, dwell time, and cross-reference with ticketing data where permissible.
Análise de Cenários
Q1. Your CTO wants to upgrade all carriage access points to WiFi 6 to solve passenger complaints about slow internet speeds. Your current backhaul is a single 4G connection. What is the correct architectural response?
💡 Dica:Consider where the actual bottleneck in the data flow is occurring.
Mostrar Abordagem Recomendada
Advise the CTO to halt the AP upgrade and invest the budget in a WAN Gateway capable of uplink aggregation. Upgrading to WiFi 6 will improve local device-to-AP speeds within the carriage, but the total throughput to the internet remains choked by the single 4G connection. Fix the backhaul bottleneck first.
Q2. During a network design review, an engineer suggests routing the train's CCTV data through the same router interfaces as the passenger WiFi to save on cabling costs. How do you respond?
💡 Dica:Consider the security implications of mixing public and operational traffic.
Mostrar Abordagem Recomendada
Reject the proposal immediately. Passenger WiFi and operational systems like CCTV must be strictly segmented into isolated VLANs with deny-all firewall rules between them. Mixing this traffic creates a critical security vulnerability, potentially allowing a malicious actor on the public WiFi to access or disrupt train operations.
Q3. The marketing team wants to automatically subscribe all passengers who use the free WiFi to a weekly newsletter to boost engagement. What must you configure on the captive portal to ensure this is legal?
💡 Dica:Review the requirements for lawful data processing under GDPR.
Mostrar Abordagem Recomendada
You must configure the captive portal to include an explicit, unticked opt-in checkbox for marketing communications. Automatic subscription or pre-ticked boxes violate GDPR requirements for freely given, unambiguous consent. The system must also log the timestamp of this consent for audit purposes.



