WiFi para Passageiros: Como os Operadores de Transportes Usam Dados de WiFi para Compreender Viagens
Este guia técnico explica como os operadores de transportes aproveitam a infraestrutura de WiFi para passageiros para capturar análises operacionais. Abrange a arquitetura técnica, as melhores práticas de implementação e as aplicações no mundo real para medir o fluxo de pessoas, o tempo de permanência e os padrões de viagem.
🎧 Ouça este Guia
Ver Transcrição
- Resumo Executivo
- Análise Técnica Detalhada: Arquitetura e Fluxo de Dados
- Superando a Aleatorização de MAC
- Guia de Implementação: Da Infraestrutura aos Insights
- Melhores Práticas e Casos de Uso Operacionais
- Estudo de Caso Real: Rede Ferroviária Interurbana
- Estudo de Caso Real: Operações de Terminal de Ferry
- Resolução de Problemas e Mitigação de Riscos
- ROI e Impacto no Negócio

Resumo Executivo
Para os operadores de transportes — quer gerenciem redes ferroviárias interurbanas, frotas de autocarros urbanos ou serviços de ferry marítimos — o WiFi para passageiros é frequentemente visto estritamente como um custo operacional ou uma comodidade para o passageiro. No entanto, quando integrada com uma camada de análise de nível empresarial, esta infraestrutura existente transforma-se numa poderosa ferramenta de inteligência operacional. Ao capturar metadados de conexão de dispositivos, os operadores podem mapear o fluxo de passageiros, medir os tempos de permanência em zonas de estações e rastrear padrões de viagem sem depender exclusivamente de dados de bilhética.
Este guia fornece a gestores de TI, arquitetos de rede e diretores de operações um quadro prático para implementar e aproveitar a análise de WiFi para passageiros. Exploramos a arquitetura técnica subjacente necessária para capturar sinais de dispositivos de forma segura, os casos de uso operacionais que proporcionam um ROI mensurável e os requisitos de conformidade necessários para processar estes dados dentro dos frameworks de GDPR e proteção de dados.
Ouça o nosso briefing do consultor sénior sobre este tópico:
Análise Técnica Detalhada: Arquitetura e Fluxo de Dados
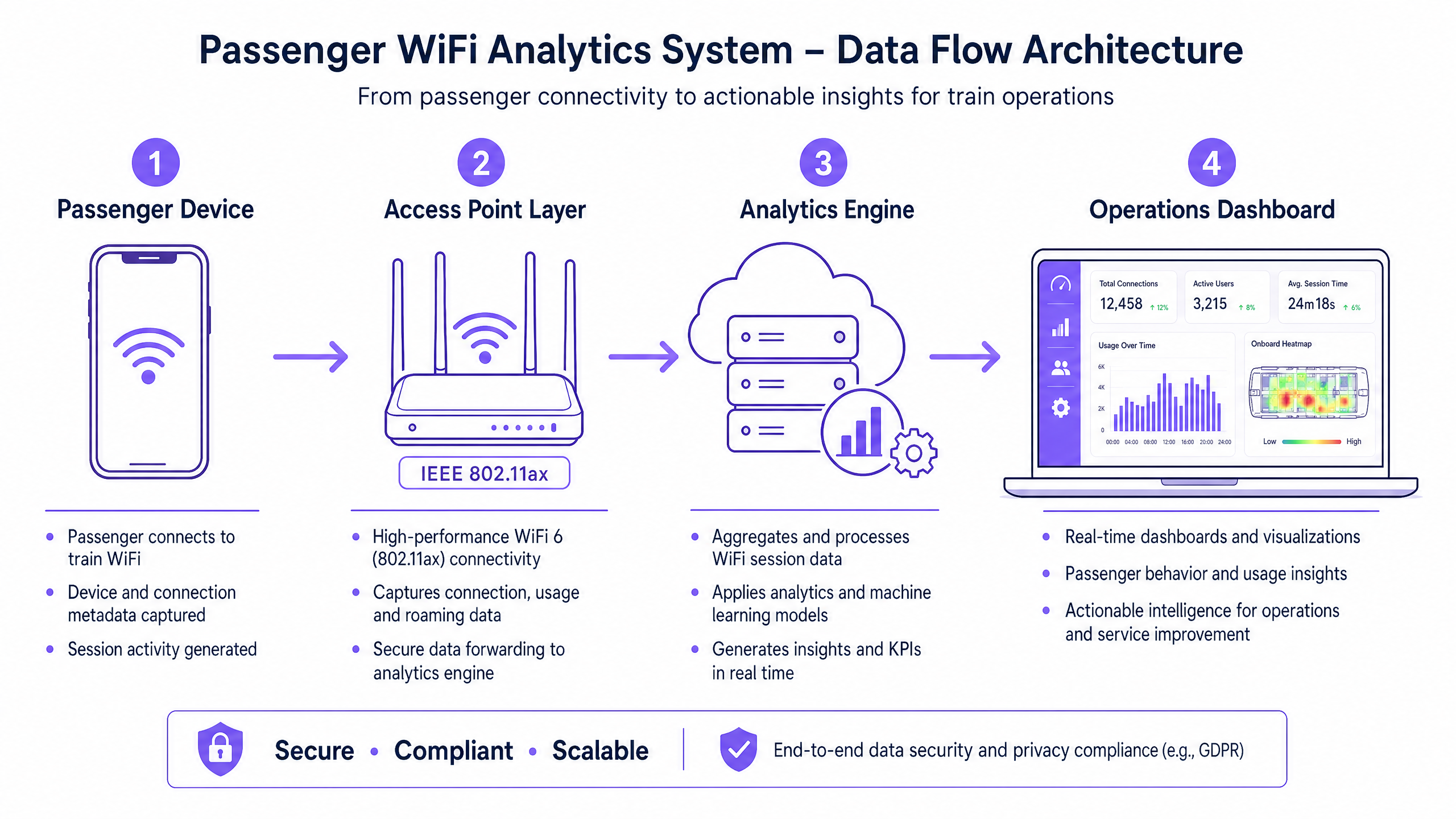
A base de qualquer capacidade de análise de WiFi para passageiros é a capacidade da rede de capturar e processar metadados de dispositivos de forma segura. A arquitetura consiste tipicamente em quatro camadas principais:
- Camada de Ponto de Acesso (Edge): Hardware físico implementado em estações e material circulante. Implementações modernas que utilizam IEEE 802.11ax (WiFi 6) fornecem suporte a clientes de alta densidade e capturam metadados essenciais, incluindo endereços MAC, intensidade do sinal (RSSI) e carimbos de data/hora de conexão.
- Camada de Recolha de Dados (Controlador): Um controlador centralizado gerido na cloud agrega registos de sessão brutos e transferências de roaming da camada de ponto de acesso.
- Motor de Análise: Plataformas como a camada WiFi Analytics da Purple processam os registos brutos, aplicando modelos de machine learning para filtrar dispositivos de funcionários e sinais transitórios, transformando dados brutos em métricas significativas (por exemplo, tempo de permanência, fluxo de pessoas).
- Dashboard de Operações: A camada de visualização onde os planeadores de rede e os gestores de estações consomem insights através de dashboards e mapas de calor em tempo real.
Superando a Aleatorização de MAC
Um desafio técnico crítico na análise moderna de WiFi é a aleatorização de endereços MAC. Desde o iOS 14 e Android 10, os dispositivos aleatorizam os seus endereços MAC por rede para melhorar a privacidade. Embora isto não afete as métricas agregadas de fluxo de pessoas ou tempo de permanência (uma vez que a sessão permanece consistente durante uma única visita), limita a capacidade de rastrear visitantes repetidos anonimamente ao longo do tempo.
A solução arquitetónica é o Guest WiFi autenticado. Ao encaminhar os utilizadores através de um captive portal que requer autenticação (por exemplo, e-mail ou login social), o sistema cria um perfil de utilizador persistente e consentido. Este perfil ancora os dados da sessão a um utilizador conhecido, contornando as limitações da aleatorização de MAC, mantendo uma estrita conformidade com os regulamentos de proteção de dados.
Guia de Implementação: Da Infraestrutura aos Insights
A implementação de análises de WiFi para passageiros requer uma abordagem estruturada para garantir a precisão dos dados e a segurança da rede.
- Realizar Auditorias RF Abrangentes: A precisão da análise depende inteiramente da cobertura da rede. Zonas mortas em átrios de estações ou plataformas resultam em sessões perdidas e dados de viagem fragmentados. Realize levantamentos de RF detalhados para garantir cobertura contígua em todas as zonas de passageiros.
- Padronizar a Integração de Dados: As redes de transportes frequentemente apresentam hardware heterogéneo (por exemplo, Cisco Meraki em estações, diferentes fornecedores em material circulante). Implemente uma camada de API agnóstica ao fornecedor para normalizar os registos de sessão antes que cheguem ao motor de análise.
- Implementar Controlos de Segurança Robustos: As redes voltadas para passageiros são superfícies de ataque de alto risco. Imponha WPA3 onde a compatibilidade do cliente o permita, implemente isolamento rigoroso do cliente (isolamento de Camada 2) para prevenir movimento lateral entre dispositivos de passageiros e implemente filtragem de DNS para bloquear domínios maliciosos. Para mais informações sobre como proteger estes ambientes, consulte o nosso guia Proteja a Sua Rede com DNS e Segurança Fortes .
- Definir Arquitetura Zonal: Segmente as suas localizações físicas em zonas lógicas (por exemplo, átrio, área de retalho, plataforma). Isto permite uma análise granular do tempo de permanência, permitindo que os operadores diferenciem entre um passageiro a navegar numa zona de retalho e um passageiro à espera numa plataforma durante um atraso no serviço.
Melhores Práticas e Casos de Uso Operacionais
Os operadores de transportes estão a aproveitar a análise de WiFi para impulsionar a eficiência em múltiplos domínios operacionais. Semelhante à forma como os locais em Retalho e Hotelaria usam dados de fluxo de pessoas para otimizar o pessoal, os operadores de transportes usam estes insights para gerir a procura de pico.
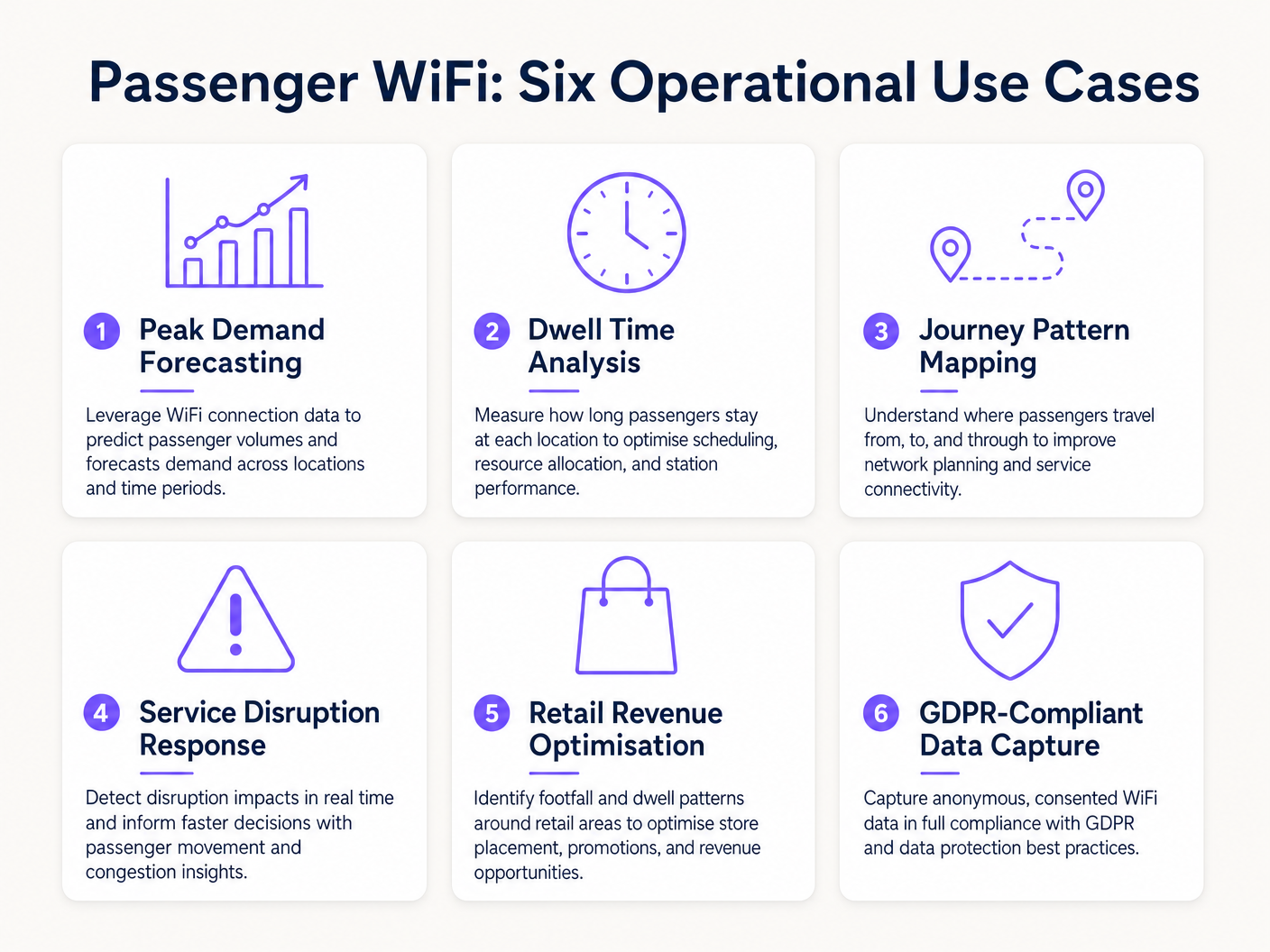
Estudo de Caso Real: Rede Ferroviária Interurbana
Um grande operador ferroviário interurbano do Reino Unido implementou a análise de WiFi em doze estações terminais para resolver o congestionamento das plataformas. Ao correlacionar picos de conexão WiFi com os horários de partida dos comboios, a equipa de operações identificou que plataformas específicas experimentavam um congestionamento perigoso 40 minutos antes da partidare. Os dados revelaram que os passageiros estavam a chegar mais cedo do que o previsto devido à sinalização digital pouco clara no átrio principal. Ao ajustar o horário dos anúncios de plataforma nos painéis de partidas, o operador suavizou o fluxo de passageiros, reduzindo a densidade máxima da plataforma em 22% e melhorando a segurança geral.
Estudo de Caso Real: Operações de Terminal de Ferry
Um operador regional de ferry, que gere tráfego de alto volume no verão, utilizou a análise de tempo de permanência WiFi para otimizar a sua estratégia de retalho no terminal. O painel de controlo de análise destacou que os passageiros à espera de travessias atrasadas tinham um tempo médio de permanência de 45 minutos no terminal, mas apenas 12% entravam na zona de retalho secundária. Ao reposicionar a sinalização digital e acionar notificações push automáticas através do captive portal, oferecendo um desconto de café durante os atrasos, o operador aumentou a conversão de retalho em 18% durante eventos de interrupção.
Resolução de Problemas e Mitigação de Riscos
Ao implementar a análise de WiFi para passageiros, as equipas de TI devem mitigar vários modos de falha comuns:
- Diluição de Dados de Dispositivos de Funcionários: A falha em filtrar dispositivos de funcionários (por exemplo, equipas de limpeza, pessoal de retalho) distorce significativamente as métricas de tempo de permanência. Implemente filtragem rigorosa de endereços MAC ou SSIDs dedicados para funcionários para garantir que os dados dos passageiros permaneçam limpos.
- Falhas de Conformidade: A recolha de dados de dispositivos sem consentimento explícito ou uma base legal documentada viola o GDPR. Garanta que o seu captive portal articula claramente a política de processamento de dados e recolhe o consentimento explícito quando necessário.
- Estrangulamentos de Backhaul: Os sistemas a bordo que dependem de backhaul celular (LTE/5G) frequentemente sofrem de restrições de largura de banda. Garanta que a sua arquitetura armazena dados de análise localmente durante quedas de conectividade e sincroniza assincronamente para evitar a perda de dados sem afetar as velocidades de navegação dos passageiros.
ROI e Impacto no Negócio
O retorno do investimento para a análise de WiFi para passageiros estende-se muito além do departamento de TI. Ao tratar a rede como um ativo de inteligência, os operadores podem:
- Otimizar a Alocação de Recursos: Alinhar o pessoal da estação, horários de limpeza e patrulhas de segurança com dados empíricos de fluxo de pessoas, em vez de horários estáticos.
- Aumentar a Receita de Retalho: Fornecer aos inquilinos de retalho métricas precisas de fluxo de pessoas e conversão, justificando taxas de aluguer premium em zonas de alto tráfego.
- Melhorar a Experiência do Passageiro: Identificar pontos de atrito na jornada da estação e gerir proativamente o congestionamento, tal como o setor de Saúde utiliza tecnologia semelhante para entender o fluxo de pacientes. Para contexto sobre aplicações intersetoriais, consulte Como o WiFi Pode Melhorar a Experiência do Paciente em Hospitais .
Ao integrar a análise de WiFi na estratégia operacional central, os operadores de transporte no setor de Transporte podem fazer a transição de uma gestão reativa para uma prestação de serviços proativa e orientada por dados.
Termos-Chave e Definições
MAC Address Randomisation
A privacy feature in modern operating systems (iOS, Android) that generates a temporary, random MAC address for each WiFi network the device connects to.
IT teams must account for this as it prevents the tracking of repeat visitors using only hardware identifiers, necessitating captive portal authentication.
Dwell Time
The total duration a device remains connected or visible to the WiFi network within a specific physical zone.
Used by operations directors to measure how long passengers wait on platforms or spend in retail areas, directly impacting commercial and safety planning.
Captive Portal
A web page that users must view and interact with before being granted access to a public WiFi network.
The primary mechanism for capturing user consent, enforcing terms of service, and collecting first-party marketing data.
IEEE 802.11ax (WiFi 6)
The current standard for wireless networks, designed to improve performance in high-density environments.
Essential for transport hubs like stadiums and train stations where thousands of devices attempt to connect simultaneously.
RSSI (Received Signal Strength Indicator)
A measurement of the power present in a received radio signal.
Analytics engines use RSSI values from multiple access points to triangulate a device's physical location within a venue.
Client Isolation
A security feature that prevents devices connected to the same WiFi network from communicating directly with each other.
Critical for public passenger WiFi to prevent malicious actors from scanning or attacking other users' devices on the network.
Footfall
The total number of unique devices detected by the WiFi network within a specific timeframe.
Provides station managers with an accurate proxy for total passenger volume, independent of ticket sales.
Cellular Backhaul
The use of cellular networks (LTE/5G) to connect a local WiFi network (like on a bus or train) back to the internet.
The primary ongoing operational cost (OPEX) for onboard WiFi deployments, requiring careful bandwidth management.
Estudos de Caso
A major train station operator is experiencing severe congestion on Platform 4 during the evening peak. They need to understand where these passengers are originating from within the station (e.g., main concourse vs. retail zone) to improve flow.
- Deploy high-density IEEE 802.11ax access points across the concourse, retail zones, and Platform 4 to ensure contiguous coverage.
- Configure the analytics platform to define logical 'Zones' for each area.
- Analyse the 'Zone-to-Zone Transition' reports in the analytics dashboard during the 16:00-19:00 window.
- Identify the primary origin zones for devices arriving at Platform 4.
- If the data shows a bottleneck originating from the retail zone corridor, operations can deploy staff to redirect flow or update digital signage to route passengers through a secondary concourse entrance.
A regional bus operator wants to offer free onboard WiFi but needs to justify the cellular backhaul costs to the commercial director by capturing marketing data.
- Implement a cloud-managed captive portal for the onboard WiFi network.
- Configure the portal to require authentication via email or social login (e.g., Facebook, Google).
- Ensure the portal includes a clear, GDPR-compliant privacy notice and opt-in checkboxes for marketing communications.
- Integrate the captive portal data capture directly with the operator's CRM or email marketing platform via API.
- Track the volume of new marketing opt-ins generated per route and calculate the equivalent cost-per-acquisition (CPA) to justify the backhaul OPEX.
Análise de Cenários
Q1. Your ferry terminal has deployed WiFi analytics, but the average dwell time in the main waiting lounge is reporting as 8.5 hours, which is impossible given your sailing schedule. What is the most likely cause and how do you fix it?
💡 Dica:Consider what other devices might be permanently located in or near the waiting lounge.
Mostrar Abordagem Recomendada
The analytics engine is likely capturing static devices (e.g., smart TVs, digital signage, point-of-sale systems) or staff devices that remain in the lounge all day. The solution is to identify the MAC addresses of these known devices and configure the analytics platform to filter them out of the dataset.
Q2. A bus operator wants to track how many passengers travel the full length of a specific route versus hopping off early. They are relying purely on anonymous MAC address tracking from the onboard access point. Why might this data be inaccurate?
💡 Dica:Think about how modern smartphones handle network connections to protect privacy.
Mostrar Abordagem Recomendada
Modern smartphones use MAC address randomisation. While connected to the bus WiFi, the session is tracked accurately. However, if a device disconnects (e.g., goes to sleep) and reconnects later on the route, it may present a new MAC address, making it appear as a new passenger rather than a continuing journey. Implementing a captive portal for authentication is required to track persistent journeys accurately.
Q3. You are deploying WiFi across a large train station with a high-density concourse. To ensure secure data capture and protect passengers, what two critical network security configurations must be enabled on the public SSID?
💡 Dica:One prevents devices from talking to each other; the other prevents access to malicious sites.
Mostrar Abordagem Recomendada
- Client Isolation (Layer 2 isolation) must be enabled to prevent passenger devices from communicating with or attacking each other on the local network. 2. DNS Filtering should be deployed to block access to known malicious domains, phishing sites, and inappropriate content.



