Cisco Meraki vs. Aruba: A Technical Comparison for Guest WiFi
An authoritative technical comparison of Cisco Meraki and HPE Aruba for enterprise guest WiFi deployments. This guide provides actionable insights for IT managers and architects on architecture, authentication, network segmentation, and hardware-agnostic analytics integration.
Listen to this guide
View podcast transcript
- Executive Summary
- Technical Deep-Dive: Architecture and Authentication
- Management Plane Architecture
- Guest Authentication and Network Access Control
- Implementation Guide: Best Practices for Enterprise Deployment
- 1. Network Segmentation and VLAN Design
- 2. High-Density RF Design
- Troubleshooting & Risk Mitigation
- Common Failure Modes
- ROI & Business Impact
- Listen to the Technical Briefing

Executive Summary
For CTOs and network architects in hospitality, retail, and public-sector environments, selecting the right enterprise wireless infrastructure is a critical decision that dictates operational overhead and guest experience for the next refresh cycle. This technical guide compares the two market leaders: Cisco Meraki and HPE Aruba.
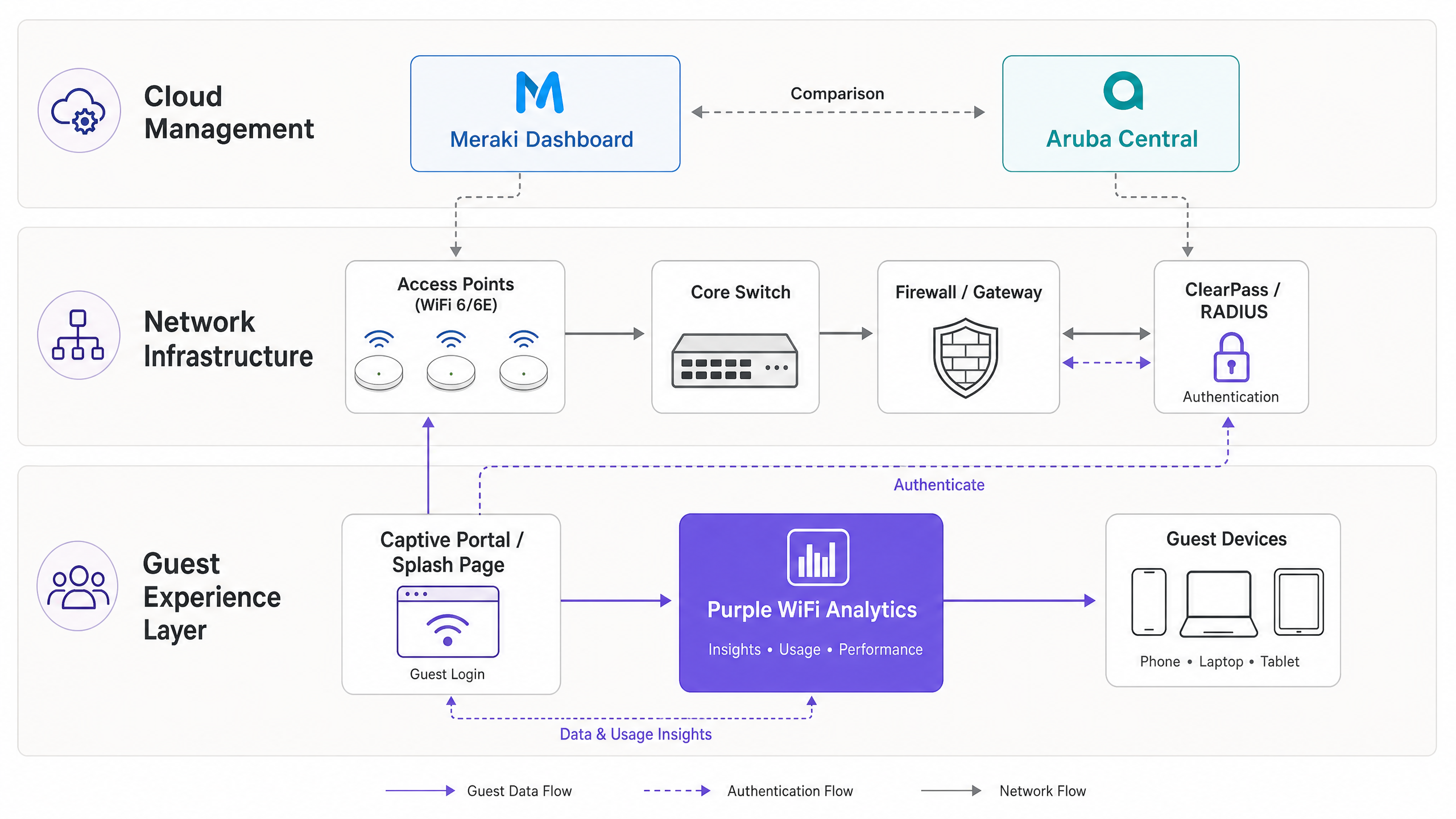
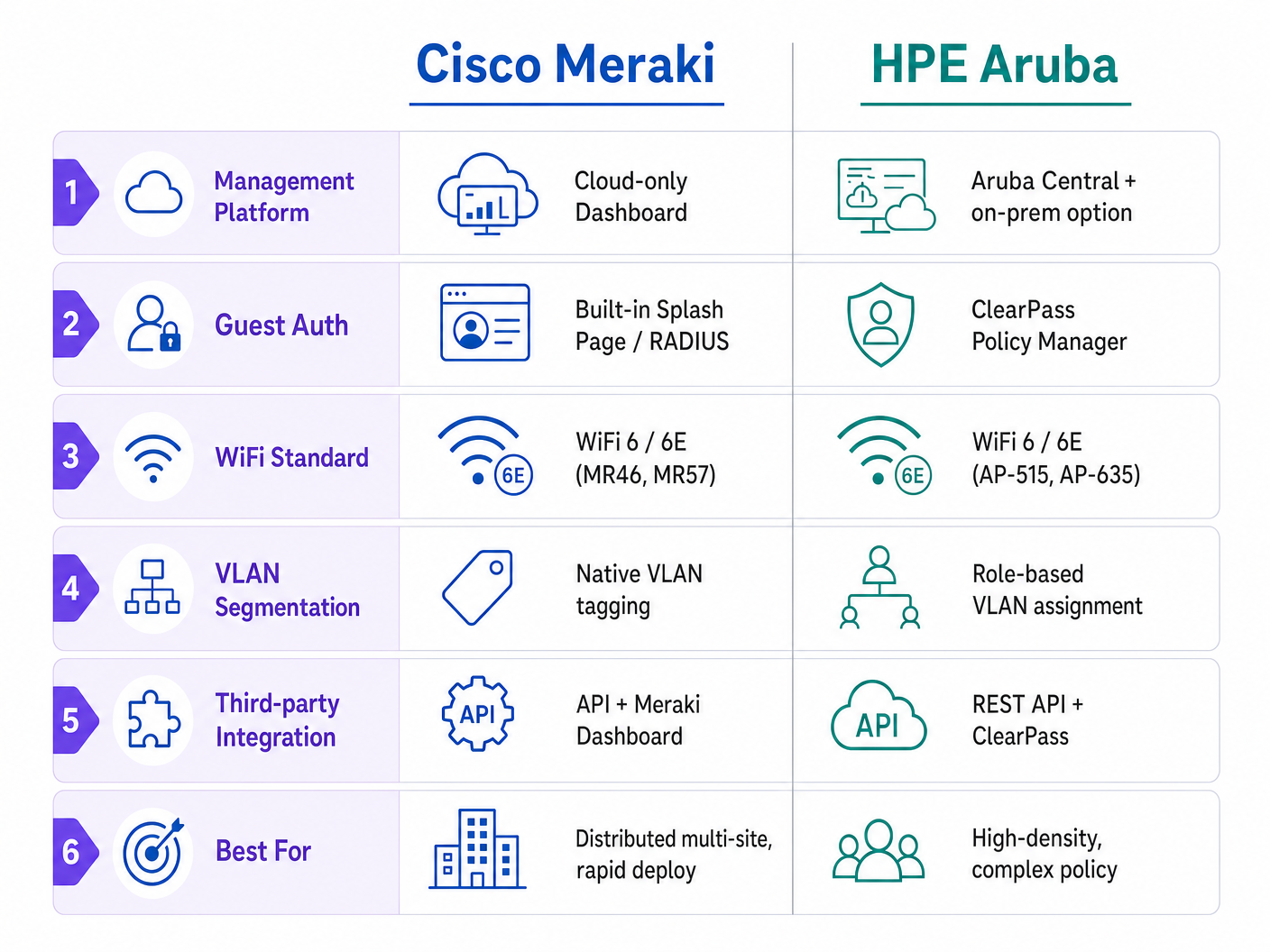
While both platforms deliver robust WiFi 6/6E performance, they diverge fundamentally in their management architecture and approach to network access control. Cisco Meraki relies on a cloud-first, zero-touch provisioning model that excels in distributed multi-site deployments. HPE Aruba offers hybrid deployment flexibility and sophisticated role-based policy enforcement via ClearPass, making it the standard for high-density, complex RF environments.
Regardless of the underlying hardware chosen, enterprise operators must abstract their guest intelligence layer. By integrating a hardware-agnostic platform like Purple , organisations ensure compliance, preserve their WiFi Analytics continuity, and enable advanced identity provisioning across any hardware refresh cycle.
Technical Deep-Dive: Architecture and Authentication
Management Plane Architecture
The most significant architectural divergence between the two vendors lies in their management planes.
Cisco Meraki employs a strictly cloud-managed architecture. The Meraki Dashboard serves as the single pane of glass for all configuration, monitoring, and firmware management. Access points (APs) are "headless" and require connectivity to the Meraki cloud to receive policy updates. This model enables true zero-touch provisioning: APs can be shipped to remote Retail branches, plugged into PoE switches, and they will automatically pull their configuration templates.
HPE Aruba provides a hybrid approach. While Aruba Central offers cloud management comparable to Meraki, Aruba also supports on-premises controllers (Mobility Controllers). This is a mandatory requirement for many Healthcare and public-sector deployments where data sovereignty or strict NHS governance prevents routing management traffic through a public cloud.
Guest Authentication and Network Access Control
Guest onboarding is where network policy meets user experience.
Meraki handles guest access through built-in splash pages or external RADIUS integration. The native captive portal is functional but lacks the sophisticated data capture and consent management required for modern GDPR compliance. For enterprise deployments, the standard architecture involves configuring the Meraki SSID with a "Sign-on with" requirement, pointing to an external captive portal URL (such as Purple), and authenticating via RADIUS.
Aruba approaches this through ClearPass Policy Manager, a dedicated Network Access Control (NAC) appliance. ClearPass Guest provides extensive capabilities for self-registration, sponsor approval, and granular role-based access control (RBAC). However, ClearPass is a complex, separate product requiring specific licensing and expertise to manage effectively.
Implementation Guide: Best Practices for Enterprise Deployment
1. Network Segmentation and VLAN Design
Proper network segmentation is non-negotiable for security and PCI DSS compliance. Guest traffic must be isolated from corporate, IoT, and point-of-sale (PoS) networks.
- Meraki Implementation: Create a dedicated Guest SSID and assign it to a specific VLAN (e.g., VLAN 100). Use Meraki's Layer 3/7 firewall rules to explicitly deny traffic to local LAN subnets, ensuring guests only have internet egress.
- Aruba Implementation: Utilise Aruba's role-based firewall. Assign the 'Guest' role to the SSID, and define policies that drop any traffic destined for RFC 1918 private IP space before permitting HTTP/HTTPS traffic to the WAN.
For a deeper dive into segmentation strategies, see our guide on Comparing Controller-Based vs. Cloud-Managed Access Points .
2. High-Density RF Design
In Hospitality environments (conference centres) or Transport hubs, AP placement and channel planning are critical.
- Deploy WiFi 6E (6 GHz) APs like the Meraki MR57 or Aruba AP-635 to alleviate congestion in the 5 GHz band.
- Limit 2.4 GHz radios to provide basic coverage for legacy IoT devices, while steering guest devices to 5 GHz and 6 GHz bands.
- Aruba's ClientMatch technology historically provides excellent client steering in extremely dense environments, while Meraki's Auto RF handles dynamic channel and power assignment effectively for distributed sites.
Troubleshooting & Risk Mitigation
Common Failure Modes
- Captive Portal Redirect Failures: Often caused by aggressive HTTPS interception (HSTS) or DNS resolution issues before authentication. Ensure your Walled Garden includes the necessary domains for the captive portal platform, identity providers (Apple, Google, Facebook), and certificate revocation lists (CRLs).
- VLAN Leaking: Misconfigured switch trunk ports can allow guest traffic to bridge into corporate networks. Always use explicit tagged VLANs for AP uplinks and avoid using the native VLAN for guest traffic.
- Asymmetric Routing in Hybrid Environments: When migrating or mixing vendors, ensure the default gateway for the guest subnet is consistent and handles NAT correctly to avoid dropped stateful connections.
ROI & Business Impact
Deploying enterprise WiFi is a significant CapEx and OpEx investment. To generate ROI, the network must do more than provide basic connectivity.
By layering Purple's hardware-agnostic platform over either Meraki or Aruba, venues transform a cost centre into a revenue-generating asset. Purple's Profile-based authentication (with over 440M global users) reduces friction, while capturing first-party data. This enables retail media monetisation, targeted marketing, and deep footfall analytics.
As noted in our recent playbook on How To Improve Guest Satisfaction: The Ultimate Playbook , seamless connectivity is the baseline; intelligent engagement is the differentiator.
Listen to the Technical Briefing
For a 10-minute deep dive into this comparison, listen to our senior architect briefing podcast:
Key Definitions
Zero-Touch Provisioning (ZTP)
The ability to configure network hardware via the cloud before it arrives on site, allowing it to download its configuration automatically upon connecting to the internet.
Critical for IT teams deploying WiFi across hundreds of retail branches without sending engineers to each site.
Network Access Control (NAC)
A security solution that enforces policy on devices and users attempting to access the network, ensuring only authorized entities gain entry.
Aruba ClearPass is a dedicated NAC; it determines what a user can access based on their role, device type, and location.
Walled Garden
A limited list of IP addresses or domains that a user can access before they have fully authenticated on the captive portal.
Essential for allowing devices to reach the Purple splash page, identity providers (like Google/Facebook for social login), and certificate validation servers before granting full internet access.
RADIUS (Remote Authentication Dial-In User Service)
A networking protocol that provides centralized Authentication, Authorization, and Accounting (AAA) management for users connecting to a network service.
The standard protocol used by Meraki and Aruba to communicate with Purple or ClearPass to verify if a guest should be allowed on the WiFi.
VLAN (Virtual Local Area Network)
A logical subnetwork that groups a collection of devices from different physical LANs, isolating their broadcast traffic.
The primary method for keeping guest WiFi traffic completely separate from sensitive back-office or Point of Sale (PoS) systems.
WiFi 6E (802.11ax in 6 GHz)
An extension of the WiFi 6 standard that utilizes the newly available 6 GHz spectrum, providing wider channels and less interference.
Crucial for future-proofing high-density venues like stadiums, ensuring the network can handle thousands of concurrent connections without legacy device congestion.
Captive Portal
A web page that the user of a public-access network is obliged to view and interact with before access is granted.
The primary guest touchpoint where terms are accepted, marketing consent is gathered, and brand engagement occurs.
Profile-Based Authentication
A method where users authenticate once and are subsequently recognized seamlessly across a network of venues without repeatedly entering credentials.
Purple's approach to creating a frictionless guest experience, leveraging a global network of over 440 million users.
Worked Examples
A 400-room resort hotel needs to deploy guest WiFi across accommodation blocks, a high-density conference centre, and outdoor pool areas. They have a lean IT team of two engineers and require GDPR-compliant marketing data capture.
Deploy Cisco Meraki MR46 APs in the accommodation blocks and MR57 (WiFi 6E) APs in the conference centre for high-density support. Use Meraki Dashboard for zero-touch provisioning and unified management, reducing the burden on the lean IT team. For the marketing requirement, configure the Meraki Guest SSID to use a custom splash URL pointing to Purple WiFi. Purple will handle the captive portal, GDPR consent, and data capture, integrating with Meraki via RADIUS for authentication.
A large public-sector hospital trust requires guest WiFi for patients and visitors. Strict NHS data governance mandates that no network management traffic can traverse a public cloud. They also need to integrate with existing Active Directory for staff BYOD access on a separate SSID.
Deploy HPE Aruba AP-515 access points managed by on-premises Aruba Mobility Controllers. This ensures all management and control plane traffic remains within the hospital's data centre. Deploy ClearPass Policy Manager to handle the complex NAC requirements: integrating with AD for staff BYOD, and providing a secure, segmented guest portal for patients. Purple can still be integrated via ClearPass to provide advanced analytics and seamless roaming (like OpenRoaming) without violating the on-prem management constraint.
Practice Questions
Q1. A retail chain with 150 small branches needs to deploy guest WiFi. They have no dedicated IT staff at the branch level and rely on a small central team. Which platform architecture is more suitable?
Hint: Consider the operational overhead of deploying hardware to 150 locations without on-site technical expertise.
View model answer
Cisco Meraki is the recommended approach. Its cloud-only architecture and zero-touch provisioning allow the central IT team to configure templates in the Dashboard. Hardware can be shipped directly to branches, plugged in by store staff, and it will automatically download its configuration, significantly reducing deployment complexity and costs.
Q2. You are configuring a guest WiFi network in a hotel. You need to ensure that guests cannot access the hotel's reservation system servers located on the same physical network infrastructure. What is the standard approach?
Hint: Think about Layer 2 isolation and Layer 3 boundary control.
View model answer
The standard approach is strict network segmentation. The Guest SSID must be mapped to a dedicated VLAN (e.g., VLAN 200), completely separate from the corporate VLAN (e.g., VLAN 10). Additionally, Layer 3/7 firewall rules must be applied at the AP or gateway level to explicitly deny any traffic from the Guest VLAN destined for RFC 1918 private IP addresses (the internal network), allowing only traffic destined for the public internet.
Q3. A venue wants to capture guest data for marketing purposes and ensure GDPR compliance. Why is relying solely on the native splash pages provided by hardware vendors often insufficient for enterprise requirements?
Hint: Consider the difference between network access control and data privacy/consent management.
View model answer
Native vendor splash pages are designed primarily for basic network access control (accepting terms and conditions). They generally lack the sophisticated features required for modern marketing and compliance, such as granular consent management, data retention policies, right-to-erasure workflows, social login integrations, and seamless CRM synchronization. An overlay platform like Purple is required to handle the complex compliance burden and abstract the guest intelligence layer from the underlying hardware.