DNS Over HTTPS (DoH): Auswirkungen auf die Filterung in öffentlichen WiFi-Netzwerken
This technical reference guide explains how DNS over HTTPS (DoH) bypasses traditional port 53 content filtering on public WiFi networks. It provides actionable, vendor-neutral mitigation strategies for network architects and IT managers to regain visibility, enforce compliance, and secure guest access in enterprise environments.
Diesen Leitfaden anhören
Podcast-Transkript ansehen
- Executive Summary
- Technical Deep-Dive: The DoH Bypass Mechanism
- Implementation Patterns: Application vs. OS-Level DoH
- Implementation Guide: A Defence-in-Depth Architecture
- Layer 1: Block Known DoH Resolver Endpoints
- Layer 2: Enforce Port 53 Interception and Redirect
- Layer 3: Block Port 853 (DNS over TLS)
- Best Practices and Compliance Considerations
- Troubleshooting & Risk Mitigation
- Incomplete Interception Rules
- IPv6 Oversights
- Application Breakage
- ROI & Business Impact
Executive Summary
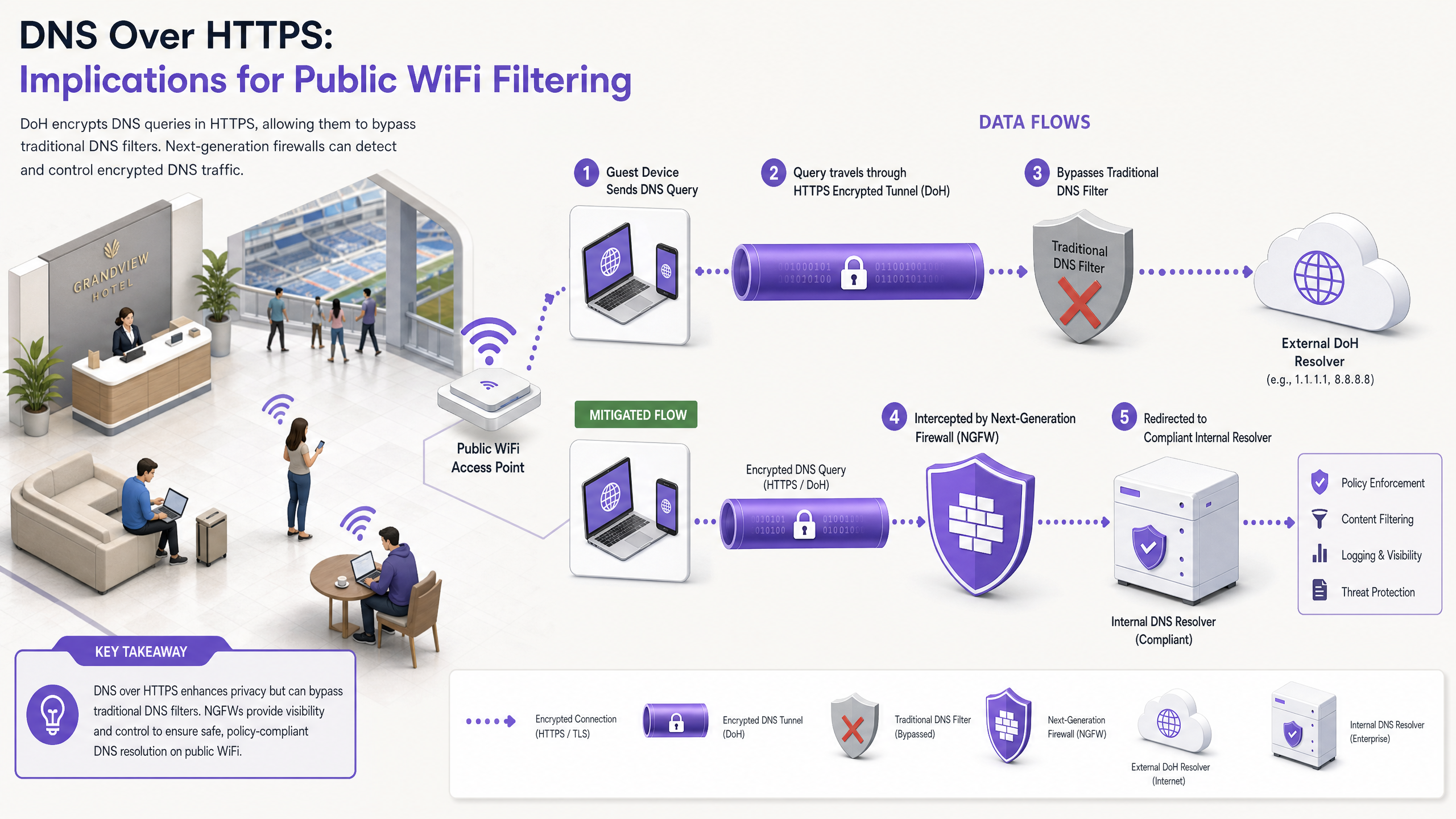
For nearly a decade, traditional DNS filtering on port 53 has served as the primary mechanism for enforcing content policies and mitigating malware threats on public WiFi networks. However, the widespread adoption of DNS over HTTPS (DoH) by mainstream browsers and operating systems fundamentally disrupts this model. By encapsulating DNS queries within standard HTTPS traffic on port 443, DoH renders these queries invisible to traditional network interception techniques.
For enterprise IT managers and network architects operating guest WiFi across Hospitality , Retail , stadiums, and public-sector venues, this represents a significant compliance and security gap. When guest devices silently bypass the venue's designated DNS resolvers, carefully constructed acceptable use policies fail, exposing the network to command-and-control (C2) malware traffic and inappropriate content. This guide details the mechanics of the DoH bypass vector and provides a layered, defence-in-depth architecture to regain network visibility, ensure regulatory compliance, and maintain robust Guest WiFi security.
Technical Deep-Dive: The DoH Bypass Mechanism
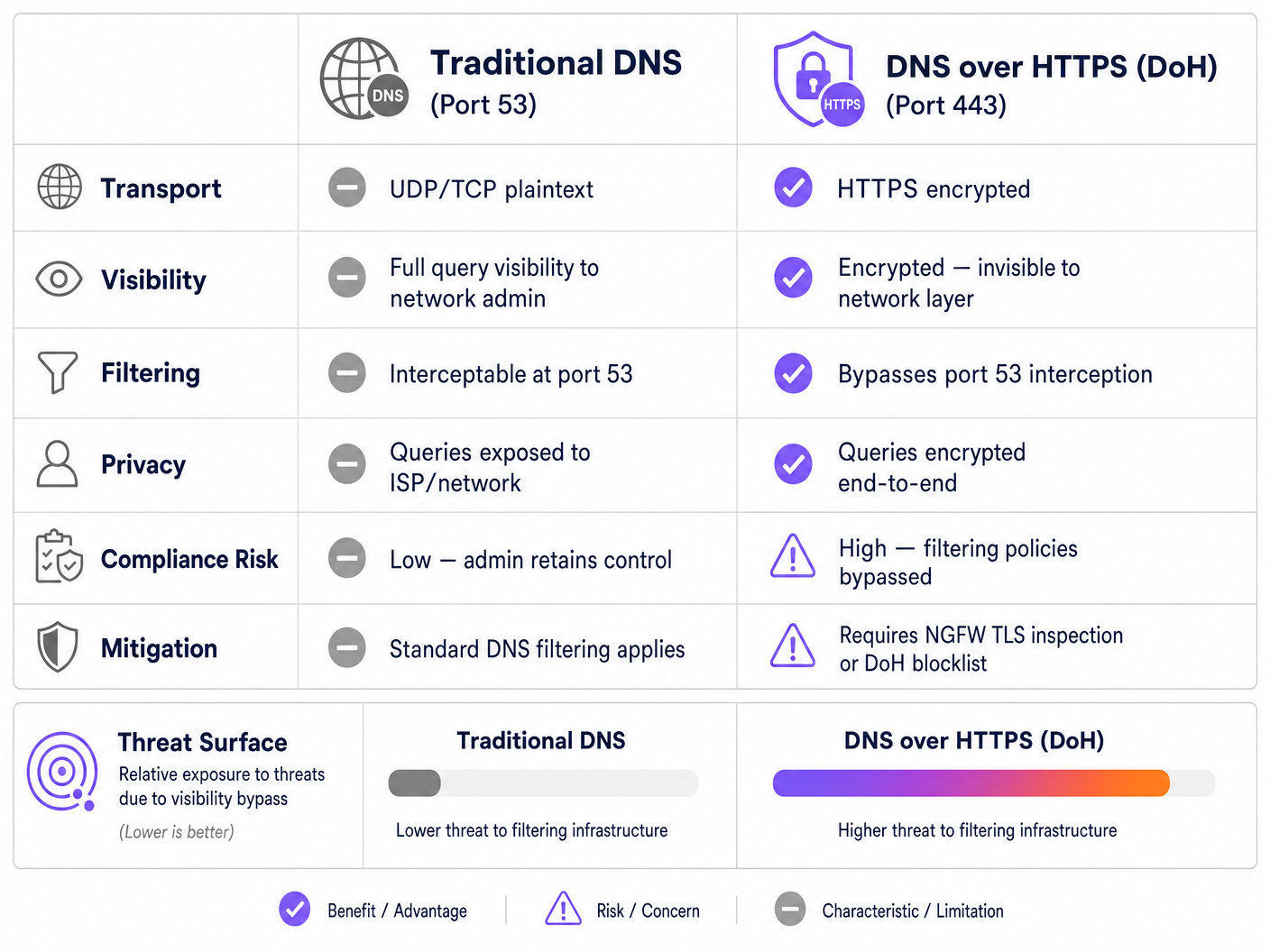
To understand the DoH threat vector, one must first examine the baseline architecture of traditional DNS filtering. Historically, when a guest device connected to a public network and requested a domain, the query was transmitted in plaintext over UDP or TCP port 53. Network administrators could easily intercept this traffic at the firewall or wireless controller, redirecting it to a compliant DNS resolver that checked the requested domain against threat intelligence feeds and content categorisation policies.
DNS over HTTPS circumvents this entire control plane. By design, DoH encrypts the DNS query and transmits it to an external resolver (such as Cloudflare's 1.1.1.1 or Google's 8.8.8.8) using standard TLS encryption over port 443. From the perspective of the venue's network infrastructure, a DoH query is indistinguishable from a user browsing a secure website or streaming a video.
Implementation Patterns: Application vs. OS-Level DoH
The challenge for network administrators is compounded by how DoH is implemented across different platforms. There are two primary deployment patterns:
- Application-Level DoH: In this model, the application maintains its own DoH configuration independently of the host operating system. Mozilla Firefox is the canonical example; when DoH is enabled, Firefox ignores the DHCP-assigned DNS servers and routes all queries to its preferred DoH provider. The venue's port 53 interception rules are entirely bypassed.
- OS-Level (Opportunistic) DoH: Modern operating systems, including Windows 11 and Android, employ opportunistic DoH. The OS checks if the DHCP-assigned DNS resolver has a known DoH endpoint. If a match is found, the OS automatically upgrades the connection to DoH. While this preserves the administrator's choice of resolver, it still shifts the traffic to port 443, which may bypass legacy monitoring tools expecting traffic on port 53.
Furthermore, administrators must account for DNS over TLS (DoT), which operates on port 853. While DoT is easier to block due to its dedicated port, it is the default standard for Android's "Private DNS" feature and represents an identical bypass risk if port 853 is left open on the guest VLAN.
Implementation Guide: A Defence-in-Depth Architecture
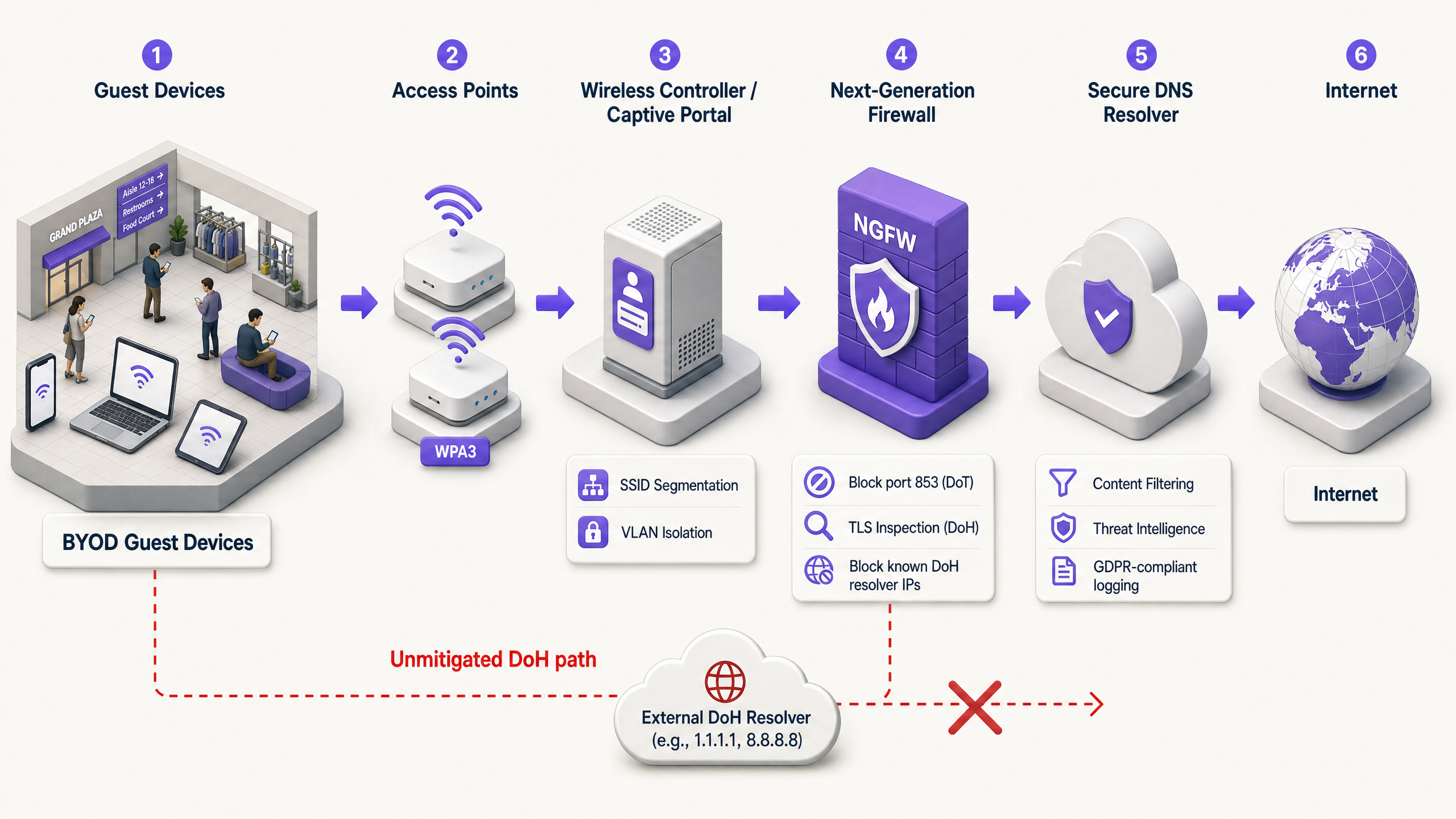
Regaining control over DNS resolution requires a multi-layered mitigation strategy. Relying on a single control point is insufficient against modern, encrypted protocols. Network architects should implement the following architecture to secure guest access and ensure compliance with frameworks like PCI DSS and GDPR.
Layer 1: Block Known DoH Resolver Endpoints
The most immediate and effective mitigation is to block outbound HTTPS traffic to known public DoH resolvers at the network edge. While DoH traffic blends in with standard HTTPS, the destination IP addresses and domains of major DoH providers are well-documented.
By configuring the Next-Generation Firewall (NGFW) to drop connections to these specific endpoints (e.g., dns.google, cloudflare-dns.com), administrators force the client device's DoH resolution to fail. In most implementations, when DoH fails, the client will gracefully fall back to traditional, unencrypted DNS on port 53, which can then be intercepted and filtered.
Implementation Note: This approach requires maintaining an updated blocklist. Enterprise firewall vendors often provide dynamic threat feeds that automatically update known DoH endpoints, significantly reducing operational overhead.
Layer 2: Enforce Port 53 Interception and Redirect
Blocking DoH is only effective if the fallback traffic is properly managed. The network must be configured to intercept all outbound UDP and TCP traffic on port 53 originating from the guest VLAN. This traffic must be forcibly redirected (via NAT/port forwarding rules) to the venue's approved, compliant DNS resolver.
This step is critical because many devices or malicious applications hardcode public DNS servers (e.g., 8.8.8.8) into their network stack, ignoring the DHCP-provided settings. Without forced interception, these devices will successfully bypass the venue's filtering policies even if DoH is blocked.
Layer 3: Block Port 853 (DNS over TLS)
To address the DoT bypass vector, administrators must explicitly block outbound traffic on TCP port 853 from the guest network. Similar to the DoH mitigation, blocking DoT forces Android devices and other DoT-capable clients to fall back to standard port 53 DNS.
Best Practices and Compliance Considerations
Implementing DoH mitigation is not merely a technical exercise; it is a fundamental requirement for maintaining regulatory compliance and enforcing acceptable use policies.
- Policy Documentation: Ensure that the venue's captive portal terms and conditions explicitly state that DNS filtering is in place for security and compliance purposes. This provides legal defensibility under GDPR and the UK's Online Safety Act when blocking encrypted DNS protocols.
- Network Segmentation: Guest WiFi must be strictly isolated from corporate and payment networks using VLANs and firewall rules. This is a core requirement of PCI DSS v4.0, which also mandates robust monitoring of network traffic—monitoring that is impossible if DoH is permitted to bypass security controls.
- Continuous Monitoring: Leverage the reporting capabilities of your enterprise DNS filtering service to monitor query volumes and identify anomalous patterns. A sudden drop in port 53 traffic from a specific subnet often indicates a new, unblocked DoH resolver is being utilized by client devices.
- Integration with Analytics: When implementing secure guest access, consider how the authentication flow integrates with broader business objectives. Utilizing a wi fi assistant for secure, profile-based authentication ensures users connect safely while allowing the venue to leverage WiFi Analytics to understand footfall and dwell times, similar to how Offline Maps Mode enhances the visitor experience.
Troubleshooting & Risk Mitigation
When deploying DoH mitigation, network teams often encounter specific failure modes. Anticipating these issues reduces downtime and guest friction.
Incomplete Interception Rules
The most common deployment failure is incomplete port 53 interception. Administrators may configure the DHCP server to hand out the correct DNS IPs but fail to implement the firewall NAT rules required to catch hardcoded DNS requests. Mitigation: Always test the deployment by configuring a client device with a static, external DNS server (e.g., 9.9.9.9) and verifying that requests are still successfully routed to the venue's filtering service.
IPv6 Oversights
As networks transition to dual-stack configurations, firewall rules are frequently written exclusively for IPv4. If DoH blocklists and port 53 interception rules do not cover IPv6, modern devices will seamlessly bypass the IPv4 controls using their IPv6 stack. Mitigation: Ensure all DoH blocklists, port 53 redirect rules, and port 853 drop rules are applied symmetrically across both IPv4 and IPv6 routing tables.
Application Breakage
Aggressive DoH blocking can occasionally break specific mobile applications that rely exclusively on their own DoH implementation and refuse to fall back to standard DNS. Mitigation: Maintain a documented exception process. If a business-critical application breaks, utilize TLS inspection (if available on the NGFW) to selectively permit DoH traffic to that specific application's resolver, rather than opening DoH globally.
ROI & Business Impact
The business case for robust DoH mitigation is rooted in risk avoidance and compliance assurance. A single incident—such as a guest accessing illegal content resulting in a regulatory inquiry, or a compromised IoT device establishing a C2 connection via DoH—can incur costs that far exceed the engineering time required to implement proper controls.
For an enterprise operating across multiple venues, standardising the DoH mitigation architecture ensures consistent policy enforcement. This standardisation reduces the operational burden on the IT service desk, as abuse notices from ISPs drop to zero and network performance is preserved by blocking high-bandwidth inappropriate content. Ultimately, securing the DNS layer ensures that the venue's investment in Guest WiFi remains a safe, compliant asset rather than a liability.
Schlüsseldefinitionen
DNS over HTTPS (DoH)
A protocol for performing remote Domain Name System (DNS) resolution via the HTTPS protocol, encrypting the data between the DoH client and the DoH-based DNS resolver.
When IT teams deploy content filtering, DoH acts as a bypass mechanism, hiding DNS queries within standard encrypted web traffic.
DNS over TLS (DoT)
A security protocol for encrypting and wrapping DNS queries and answers via the Transport Layer Security (TLS) protocol, operating on a dedicated port (853).
Often enabled by default on modern Android devices (Private DNS), DoT must be blocked at the firewall to ensure queries fall back to the venue's filtered DNS.
Opportunistic DoH
A behavior where an operating system or browser automatically upgrades standard DNS queries to DoH if it detects that the configured DNS resolver supports the encrypted protocol.
This feature, common in Windows 11 and Chrome, means that even if a venue assigns a standard DNS IP, the traffic may still shift to encrypted port 443, bypassing legacy monitoring.
Port 53 Interception
A network firewall configuration that captures all outbound traffic on UDP/TCP port 53 and forcibly redirects it to a designated DNS resolver, regardless of the destination IP requested by the client.
Essential for capturing DNS queries from devices with hardcoded DNS settings or those that have fallen back from a failed DoH connection.
Next-Generation Firewall (NGFW)
A network security device that provides capabilities beyond a traditional, stateful firewall, including deep packet inspection, application awareness, and TLS/SSL decryption.
NGFWs are critical for DoH mitigation as they can identify and block DoH traffic based on application signatures rather than just IP addresses.
Fallback Behavior
The programmed response of a client device when its preferred encrypted DNS protocol (DoH or DoT) fails to connect, typically resulting in the device reverting to standard, unencrypted DNS.
Network architects rely on this behavior; by intentionally breaking DoH/DoT connections, they force the device to use the interceptable port 53.
Command-and-Control (C2)
The infrastructure used by attackers to communicate with compromised devices (malware/botnets) within a target network.
Modern malware increasingly uses DoH to hide C2 communications from enterprise network monitors, making DoH mitigation a critical security requirement.
Captive Portal
A web page that the user of a public-access network is obliged to view and interact with before access is granted.
The captive portal is the legally appropriate location to inform users that their DNS traffic is being filtered and that encrypted DNS protocols are blocked.
Ausgearbeitete Beispiele
A 400-room hotel recently deployed a cloud-based DNS filtering service to comply with brand standards regarding family-friendly content. However, the IT manager notices that a significant portion of guest traffic is still reaching adult content sites, and the DNS filtering dashboard shows lower-than-expected query volumes. How should the network architect remediate this bypass?
- Audit Firewall Rules: The architect must first verify that outbound TCP/UDP port 53 is being intercepted and NAT-redirected to the cloud DNS service.
- Block DoH Resolvers: Implement an NGFW blocklist to drop outbound HTTPS (port 443) traffic destined for known DoH providers (e.g., Cloudflare, Google, Quad9).
- Block DoT: Add a firewall rule to drop all outbound TCP port 853 traffic to prevent Android Private DNS bypass.
- Verify IPv6: Ensure all the above rules are applied to both IPv4 and IPv6 traffic.
A retail chain with 150 locations needs to implement DNS filtering to block malware and phishing on their guest WiFi. They use basic branch firewalls without advanced TLS inspection capabilities. How can they effectively mitigate DoH without upgrading their hardware?
Without TLS inspection, the chain must rely on robust routing and blocklists.
- Deploy a dynamic DoH IP/Domain blocklist on the branch firewalls, configured to update automatically via an external threat feed.
- Implement strict port 53 NAT redirection to the enterprise DNS filter.
- Block port 853 entirely.
- Update the captive portal Terms of Service to explicitly state that encrypted DNS protocols are blocked to enforce network security policies.
Übungsfragen
Q1. A stadium network engineer configures the DHCP server to provide the IP address of their secure, filtered DNS service to all guest devices. However, testing reveals that devices with manually configured DNS settings (e.g., 8.8.8.8) are successfully bypassing the filter. What is the most appropriate architectural fix?
Hinweis: Consider the difference between suggesting a route and enforcing a route at the network edge.
Musterlösung anzeigen
The engineer must implement a NAT port forwarding rule on the stadium's firewall. This rule should intercept all outbound UDP and TCP traffic on port 53 originating from the guest VLAN and forcibly translate the destination IP to the secure DNS service's IP address. This ensures that regardless of the client's local configuration, the traffic is routed through the filtering policy.
Q2. Following the implementation of a strict DoH blocklist, the IT helpdesk at a conference centre receives reports that a specific, bespoke event management app is failing to load for attendees. Packet capture shows the app is attempting to use its own hardcoded DoH resolver, which is being blocked, and the app refuses to fall back to standard DNS. How should this be resolved?
Hinweis: Balance security policy with business continuity. Can the firewall distinguish between general DoH traffic and traffic to a specific, approved endpoint?
Musterlösung anzeigen
The administrator should create an exception in the NGFW policy. Rather than disabling the DoH blocklist globally, they should identify the specific IP address or domain of the DoH resolver used by the event management app and whitelist it. If the firewall supports application-layer (Layer 7) inspection, a more robust solution is to create a policy that permits DoH traffic only if the destination matches the approved application's infrastructure, ensuring general DoH bypass attempts remain blocked.
Q3. A public sector organisation is auditing its guest WiFi compliance. They have successfully blocked port 853 (DoT) and implemented port 53 interception. However, they lack the budget for an NGFW with advanced TLS inspection or dynamic DoH blocklists. What is the most effective remaining strategy to mitigate DoH?
Hinweis: If dynamic lists aren't available, how can you address the vast majority of opportunistic DoH traffic?
Musterlösung anzeigen
The organisation should implement a static blocklist on their existing firewall, targeting the IP addresses and domains of the most common public DoH providers (e.g., Cloudflare, Google, Quad9). While this requires manual maintenance and won't catch obscure DoH resolvers, research shows that the vast majority of DoH traffic defaults to a handful of major providers. This provides a highly effective '80/20' solution within their budget constraints.