Entwicklung einer Multi-Tenant WiFi-Architektur für MDU
Dieser maßgebliche Leitfaden bietet einen architektonischen Entwurf für die Bereitstellung skalierbarer, sicherer und isolierter WiFi-Netzwerke über mehrere Einheiten in einem MDU. Er behandelt kritische Überlegungen wie VLAN-Segmentierung, RF-Planung, 802.1X-Authentifizierung und wie die Mieterisolation mit zentralisiertem Management für einen verbesserten ROI in Einklang gebracht werden kann.
Diesen Leitfaden anhören
Podcast-Transkript ansehen
- Zusammenfassung für die Geschäftsleitung
- Technischer Deep-Dive
- Die Grundlage: Logische Segmentierung über VLANs
- Authentifizierungs- und Verschlüsselungsstandards
- Gast- und IoT-Isolation
- Implementierungsleitfaden
- Phase 1: Logisches Netzwerkdesign
- Phase 2: RF-Planung und Standortanalyse
- Phase 3: Infrastrukturkonfiguration
- Best Practices
- Fehlerbehebung & Risikominderung
- Häufige Fehlerursachen
- ROI & Geschäftsauswirkungen

Zusammenfassung für die Geschäftsleitung
Für CTOs und leitende Architekten, die Multi-Dwelling Units (MDUs) verwalten – seien es weitläufige Hotelkomplexe, gemischt genutzte Einzelhandelsumgebungen oder Wohnungen im öffentlichen Sektor – ist die Herausforderung konstant: die Bereitstellung sicherer, hochleistungsfähiger Konnektivität für unabhängige Mieter über eine gemeinsam genutzte physische Infrastruktur. Traditionelle Single-Tenant-Netzwerkdesigns brechen unter der Last der MDU-Anforderungen zusammen, was zu Sicherheitslücken, einer Sättigung der Broadcast-Domäne und einem unüberschaubaren Support-Aufwand führt.
Die Entwicklung einer Multi-Tenant WiFi-Architektur erfordert einen Wandel von der physischen Isolation zur logischen Segmentierung. Dieser Leitfaden skizziert den definitiven architektonischen Entwurf für MDU-Implementierungen. Wir werden die Implementierung von IEEE 802.1Q VLAN-Tagging für eine strikte Verkehrs-Isolation, die Notwendigkeit der 802.1X RADIUS-Authentifizierung für die Zugangskontrolle und die kritische Rolle zentralisierter Cloud-Controller bei der Aufrechterhaltung der operativen Sichtbarkeit untersuchen. Durch die Übernahme dieser herstellerneutralen Prinzipien können Betreiber Compliance-Risiken (wie PCI DSS und GDPR) mindern, Betriebskosten senken und die Konnektivität von einem Kostenfaktor in eine monetarisierbare Dienstleistungsebene umwandeln.
Technischer Deep-Dive
Die Grundlage: Logische Segmentierung über VLANs
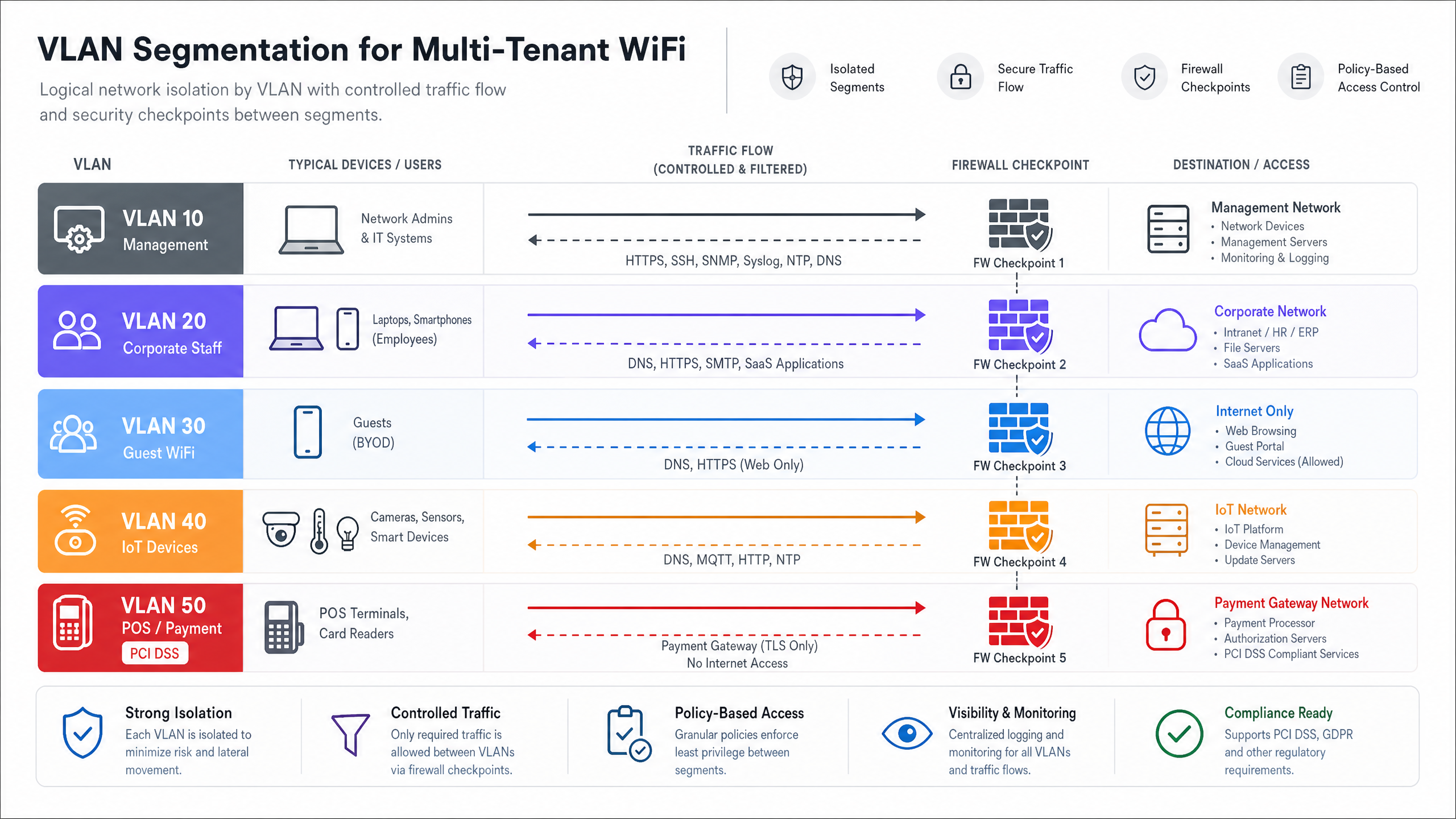
Der Eckpfeiler jeder Multi-Tenant-Architektur ist eine rigorose Netzwerksegmentierung. In einer gemeinsam genutzten physischen Umgebung ist die Bereitstellung separater Switches und Verkabelungen für jeden Mieter kommerziell nicht rentabel. Stattdessen wird die Isolation auf Schicht 2 mithilfe von IEEE 802.1Q Virtual Local Area Networks (VLANs) erreicht.
In diesem Modell sendet ein einzelner Access Point (AP) mehrere Service Set Identifiers (SSIDs) aus oder nutzt die dynamische VLAN-Zuweisung über RADIUS, um verschiedene Mieterprofile zu bedienen. Wenn sich ein Client mit dem Netzwerk verbindet, wird sein Datenverkehr am AP-Rand mit einer spezifischen VLAN-ID versehen. Dieses Tag bleibt erhalten, wenn der Frame Trunk-Links über das gemeinsam genutzte Switch-Fabric durchläuft, wodurch sichergestellt wird, dass Mieter A (z. B. VLAN 10) auf der Datenverbindungsschicht vollständig von Mieter B (z. B. VLAN 20) isoliert bleibt.
VLANs bieten jedoch Isolation, keine inhärente Sicherheit. Um eine laterale Bewegung zwischen Mieter-Netzwerken zu verhindern, muss das Inter-VLAN-Routing über Firewall-Richtlinien auf der Verteilungs- oder Kernschicht streng kontrolliert werden. Ein Zero-Trust-Ansatz schreibt vor, dass der Datenverkehr zwischen Mieter-VLANs implizit verweigert wird, es sei denn, er ist explizit für bestimmte, erforderliche Dienste zugelassen.
Authentifizierungs- und Verschlüsselungsstandards
Für Multi-Tenant-Umgebungen auf Unternehmensebene sind Pre-Shared Keys (PSKs) unzureichend. Sie sind leicht teilbar, schwer zu rotieren, ohne alle Benutzer zu beeinträchtigen, und bieten keine individuelle Verantwortlichkeit. Der architektonische Standard ist IEEE 802.1X mit RADIUS-Authentifizierung.
Unter 802.1X authentifiziert sich jeder Benutzer oder jedes Gerät individuell mithilfe einzigartiger Anmeldeinformationen oder digitaler Zertifikate. Der RADIUS-Server validiert nicht nur die Identität, sondern kann auch herstellerspezifische Attribute (VSAs) an den Authentifikator (den AP oder Switch) zurückgeben, wodurch der Benutzer dynamisch seinem zugewiesenen VLAN zugeordnet wird, unabhängig davon, mit welcher SSID er verbunden war. Dies reduziert die SSID-Proliferation erheblich, was für die Aufrechterhaltung der Airtime-Effizienz entscheidend ist.
Für die Verschlüsselung ist WPA3-Enterprise der aktuelle Standard. Es bietet robuste 192-Bit-Sicherheitssuiten für hochsensible Umgebungen und mindert die Offline-Wörterbuchangriffe, die WPA2 plagten.
Gast- und IoT-Isolation
Über den Unternehmens- oder Mieterdatenverkehr hinaus müssen MDU-Architekturen zwei unterschiedliche Verkehrsprofile berücksichtigen: Gäste und Internet of Things (IoT)-Geräte.
- Gastnetzwerke: Gäste benötigen reibungslosen Internetzugang, müssen aber vollständig von Mieterdaten getrennt sein. Dies wird typischerweise über ein Captive Portal gehandhabt. Für detaillierte Einblicke in die Verwaltung dieser Ebene und deren Nutzung für Business Intelligence, siehe unsere umfassende Übersicht über Guest WiFi und die zugehörigen WiFi Analytics -Funktionen.
- IoT-Geräte: Moderne MDUs sind stark mit intelligenten Thermostaten, IP-Kameras und Gebäudemanagementsystemen ausgestattet. Diese Geräte sind oft headless, schwer zu patchen und stellen eine erhebliche Angriffsfläche dar. Sie müssen auf dedizierten IoT VLANs mit strenger Ausgangsfilterung isoliert werden, die nur die Kommunikation mit spezifischen Management-Servern erlaubt.
Implementierungsleitfaden
Die Bereitstellung dieser Architektur erfordert einen methodischen Ansatz, der vom logischen Design zur physischen Validierung übergeht.
Phase 1: Logisches Netzwerkdesign
Beginnen Sie mit der Definition des IP-Adressierungsschemas und der VLAN-Zuordnung. Ein strukturierter Ansatz verhindert überlappende Subnetze und vereinfacht das Routing.
- Management VLAN (z. B. VLAN 1): Ausschließlich für die Netzwerkinfrastruktur (APs, Switches). Kein Benutzerzugriff.
- Mieter-VLANs (z. B. VLANs 100-199): Dedizierte Subnetze für einzelne Mieter oder Geschäftseinheiten.
- Gast-VLAN (z. B. VLAN 200): Nur Internetzugang, stark eingeschränkt.
- IoT/Gebäude-VLAN (z. B. VLAN 300): Für Gebäudemanagementsysteme.
Phase 2: RF-Planung und Standortanalyse
In Umgebungen mit hoher Dichte wie Hospitality oder Retail ist Co-Channel Interference (CCI) die Hauptursache für schlechte Leistung. Eine prädiktive Untersuchung ist unzureichend; eine aktive, Vor-Ort-RF-Untersuchung ist zwingend erforderlich, um Wanddämpfung und benachbarte Interferenzen zu berücksichtigen.
- 5 GHz / 6 GHz Präferenz: Clients auf das 5 GHz-Band oder 6 GHz, falls Wi-Fi 6E verwendet wird, drängen, um mehr nicht überlappende Kanäle zu nutzen. Für ein tieferes Verständnis des Spektrummanagements lesen Sie unseren Leitfaden zu Wi Fi Frequencies: A Guide to Wi-Fi Frequenzen im Jahr 2026 .
- Kanalbreiten: In dichten MDUs beschränken Sie die Kanalbreiten auf 20 MHz im 2,4-GHz-Band und 40 MHz im 5-GHz-Band, um die Kanalwiederverwendung zu maximieren.
- Wenn Sie Leistungsprobleme in einer bestehenden Bereitstellung haben, konsultieren Sie How to Analyze and Change Your WiFi Channel for Maximum Speed (oder die italienische Version: Come analizzare e modificare il canale WiFi per la massima velocità ).
Phase 3: Infrastrukturkonfiguration
- Switch Fabric: Konfigurieren Sie Trunk-Ports sorgfältig. Stellen Sie sicher, dass nur die erforderlichen VLANs auf Uplinks zwischen Access Switches und dem Core zugelassen sind.
- Access Points: Setzen Sie APs ein, die mehrere BSSIDs unterstützen und sich in einen Cloud-Controller integrieren lassen. Begrenzen Sie die Anzahl der ausgestrahlten SSIDs auf maximal 3-4 pro Funkmodul, um die Airtime zu erhalten.
- Controller-Richtlinien: Definieren Sie Bandbreitenbegrenzungen pro Mieter oder pro Benutzer, um zu verhindern, dass ein einzelner aggressiver Client den gemeinsam genutzten WAN-Uplink überlastet.
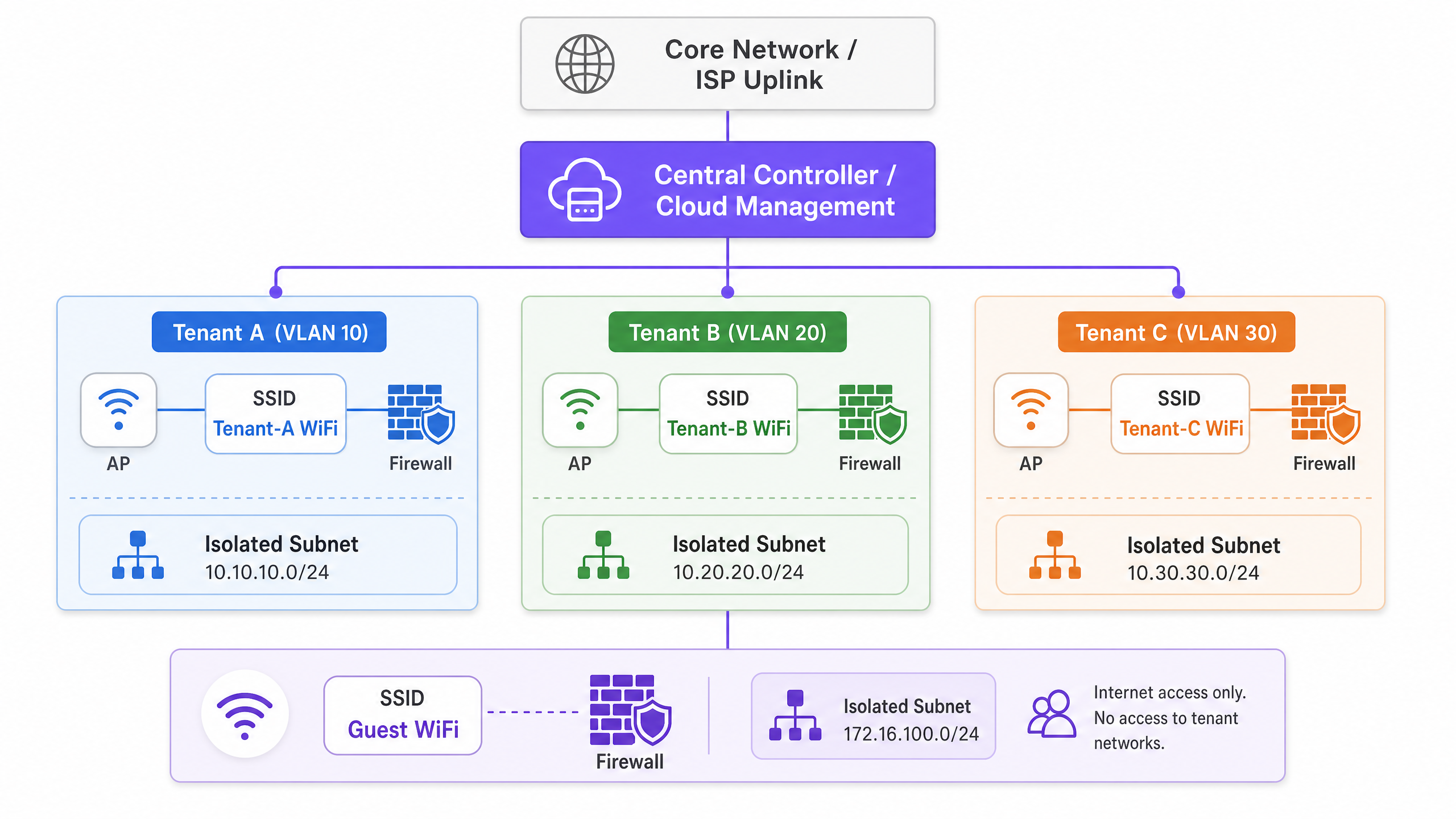
Best Practices
- Zentralisiertes Cloud-Management: Der operative Aufwand für die Verwaltung einer verteilten MDU-Umgebung ohne eine zentrale Übersicht ist nicht tragbar. Ein Cloud-Controller ermöglicht Zero-Touch-Provisioning, Firmware-Management und zentralisierte Richtliniendurchsetzung.
- Dynamische VLAN-Zuweisung: Anstatt „Tenant_A_WiFi“, „Tenant_B_WiFi“ usw. auszustrahlen, strahlen Sie eine einzige „MDU_Secure“ SSID aus und verwenden Sie 802.1X/RADIUS, um authentifizierte Benutzer dynamisch in ihr korrektes VLAN zu verschieben. Dies reduziert den Beacon-Overhead drastisch.
- Standortbasierte Dienste: Nutzen Sie BLE (Bluetooth Low Energy), das in moderne APs integriert ist, für Asset-Tracking oder Wegfindung. Weitere Informationen dazu finden Sie unter BLE Low Energy Explained for Enterprise .
- Für die Umgebung optimieren: Das physische Layout eines MDU-Bürokomplexes erfordert eine spezifische Abstimmung. Beachten Sie Office Wi Fi: Optimize Your Modern Office Wi-Fi Network für umgebungsspezifische Anpassungen.
Fehlerbehebung & Risikominderung
Häufige Fehlerursachen
- Trunk-Port-Fehlkonfiguration: Die häufigste Ursache für „verbunden, kein Internet“ in Multi-Tenant-Setups. Wenn ein VLAN in einem Trunk-Link zwischen dem AP und dem Gateway fehlt, schlagen DHCP-Anfragen fehl.
- Minderung: Implementieren Sie eine automatisierte Konfigurationsprüfung und dokumentieren Sie die Spanning-Tree-Topologie streng.
- SSID-Overhead: Das Ausstrahlen von 10 SSIDs auf einem einzelnen AP bedeutet, dass das Funkmodul einen erheblichen Prozentsatz seiner Zeit nur mit der Übertragung von Beacon-Frames verbringt, wodurch wenig Airtime für tatsächliche Daten verbleibt.
- Minderung: Konsolidieren Sie SSIDs und verwenden Sie eine dynamische VLAN-Zuweisung.
- Offenlegung der Management-Ebene: Wenn ein Mieter die Management-Schnittstelle eines APs oder Switches anpingen oder darauf zugreifen kann, ist das Netzwerk grundlegend kompromittiert.
- Minderung: Verwenden Sie ein dediziertes, Out-of-Band-Management-VLAN und wenden Sie strenge Access Control Lists (ACLs) an, die den gesamten RFC 1918-Verkehr von Mieter-Subnetzen zum Management-Subnetz blockieren.
ROI & Geschäftsauswirkungen
Der Übergang zu einer robusten Multi-Tenant-Architektur verwandelt das Netzwerk von einem notwendigen Übel in ein strategisches Asset.
- Reduzierte Betriebskosten (OpEx): Zentralisiertes Management und logische Segmentierung reduzieren die Notwendigkeit von Vor-Ort-Einsätzen. Support-Desks können Probleme remote diagnostizieren und feststellen, ob ein Fehler in der gemeinsamen Infrastruktur oder in der spezifischen Konfiguration des Mieters liegt.
- Compliance und Risikominderung: Durch die Isolierung von Payment Card Industry (PCI)-Daten (z.B. in Einzelhandelseinheiten) oder sensiblen Patientendaten (z.B. in Healthcare -Einrichtungen in gemischt genutzten Gebäuden) wird der Umfang von Compliance-Audits drastisch reduziert, was erhebliche Beratungsgebühren einspart.
- Monetarisierung: Mit einer stabilen, segmentierten Architektur können Betreiber gestaffelte Bandbreitenpakete für Mieter anbieten und so wiederkehrende Einnahmen generieren. Darüber hinaus kann das Gastnetzwerk für die Datenerfassung und das Marketing genutzt werden, wodurch Besucherfrequenz in umsetzbare Informationen umgewandelt wird.
Hören Sie sich unseren technischen Briefing-Podcast unten an, um eine ausführliche Diskussion dieser Architekturprinzipien zu erhalten:
Schlüsseldefinitionen
VLAN (Virtual Local Area Network)
A logical grouping of network devices that appear to be on the same local LAN, regardless of their physical location.
Used in MDUs to logically separate traffic from different tenants sharing the same physical switches and APs, reducing broadcast traffic and improving performance.
IEEE 802.1Q
The networking standard that supports VLANs on an Ethernet network by inserting a 32-bit tag into the Ethernet frame.
This is the underlying protocol that allows a single trunk cable to carry traffic for multiple isolated tenant networks.
IEEE 802.1X
An IEEE standard for port-based network access control (PNAC), providing an authentication mechanism to devices wishing to attach to a LAN or WLAN.
Essential for enterprise MDU deployments, it allows individual user authentication (via RADIUS) rather than relying on a shared password, enabling dynamic VLAN assignment.
RADIUS (Remote Authentication Dial-In User Service)
A networking protocol that provides centralised Authentication, Authorization, and Accounting (AAA) management for users who connect and use a network service.
The server component in an 802.1X deployment that verifies credentials and tells the AP which VLAN to assign the tenant device to.
Trunk Port
A network switch port configured to carry traffic for multiple VLANs simultaneously, using 802.1Q tags to keep the traffic separated.
The critical link between access switches and the core network. Misconfiguring a trunk port is the most common cause of tenant connectivity failure.
Co-Channel Interference (CCI)
Interference that occurs when two or more access points are transmitting on the exact same frequency channel within hearing distance of each other.
A major issue in dense MDUs (like hotels or apartment blocks) that causes devices to wait for the channel to clear, drastically reducing network throughput.
Dynamic VLAN Assignment
The process where a RADIUS server instructs the network access device (AP or switch) to place an authenticated user into a specific VLAN based on their identity.
Allows venue operators to broadcast a single secure SSID for all tenants, assigning them to their isolated networks post-authentication, thereby saving RF airtime.
Captive Portal
A web page that the user of a public-access network is obliged to view and interact with before access is granted.
Used on the Guest VLAN in an MDU to enforce terms of service, collect marketing data, or process payments before granting internet access.
Ausgearbeitete Beispiele
A mixed-use retail and office complex (MDU) needs to provide secure WiFi for 15 independent retail tenants, a shared corporate office space, and public guest WiFi. The venue operator wants to use a single physical network infrastructure to reduce costs but must ensure PCI DSS compliance for the retailers.
- Deploy enterprise-grade APs managed by a central cloud controller.
- Create a 'Management' VLAN (VLAN 10) strictly for network devices.
- Create a 'Guest' VLAN (VLAN 20) with client isolation enabled and a captive portal. Route this traffic directly to the internet, bypassing internal networks.
- For the office space, create a 'Corporate' VLAN (VLAN 30) using 802.1X authentication.
- For the retail tenants, implement Dynamic VLAN Assignment. Broadcast a single 'Retail_Secure' SSID using 802.1X. When a retail device authenticates via the central RADIUS server, the server passes a Vendor-Specific Attribute (VSA) that assigns the device to its specific tenant VLAN (e.g., VLANs 101-115).
- Configure the core firewall to block all inter-VLAN routing between the retail VLANs, ensuring strict isolation required for PCI DSS.
A 400-room hotel ([Hospitality](/industries/hospitality)) is upgrading its network. They need to support guest devices, staff tablets for housekeeping, and new IoT smart thermostats in every room. They currently experience frequent dropouts during peak evening hours.
- Conduct an active RF site survey to identify interference and plan AP placement (likely moving from hallway deployments to in-room or every-other-room deployments to handle density).
- Segment traffic logically: Guest (VLAN 100), Staff (VLAN 200), IoT (VLAN 300).
- Implement per-user bandwidth limiting on the Guest SSID (e.g., 10 Mbps down / 5 Mbps up) to prevent a few heavy users from saturating the WAN link during peak hours.
- For the IoT thermostats, use a dedicated hidden SSID with WPA3-Personal (if supported) or MAC Authentication Bypass (MAB) if they lack advanced supplicants. Apply strict egress filtering on VLAN 300 so thermostats can only communicate with the specific cloud management server.
Übungsfragen
Q1. You are designing the WiFi architecture for a new 50-unit premium apartment complex. The developer wants to offer 'Included Gigabit WiFi' as a selling point. They propose installing a standard consumer-grade wireless router in the telecom closet of each apartment, all wired back to a central unmanaged switch. What are the primary architectural flaws with this proposal, and what is the enterprise alternative?
Hinweis: Consider RF interference, management overhead, and broadcast domain size.
Musterlösung anzeigen
The proposed design has severe flaws. 1) RF Interference: 50 independent consumer routers will cause massive Co-Channel Interference (CCI), severely degrading performance. 2) Management: There is no central visibility; troubleshooting requires accessing 50 individual routers. 3) Security: An unmanaged switch means all apartments share a single broadcast domain, allowing tenants to potentially intercept each other's traffic.
The enterprise alternative is to deploy centrally managed, enterprise-grade APs (e.g., Wi-Fi 6/6E) in the apartments, connected to managed PoE switches. Implement 802.1X authentication with Dynamic VLAN Assignment so each tenant is logically isolated on their own VLAN, regardless of which AP they connect to. This provides central visibility, RF coordination, and strict security isolation.
Q2. During the commissioning phase of a multi-tenant office building, Tenant A (on VLAN 10) reports they cannot access the internet. You verify that the AP is broadcasting the SSID, the client connects successfully, and 802.1X authentication passes. However, the client device is assigning itself an APIPA address (169.254.x.x). What is the most likely configuration error in the infrastructure?
Hinweis: Follow the path of the DHCP request from the AP to the DHCP server.
Musterlösung anzeigen
The most likely issue is a misconfigured trunk port between the Access Point and the Access Switch, or between the Access Switch and the Core/Distribution switch. Because the client receives an APIPA address, the DHCP Discover broadcast is not reaching the DHCP server. If authentication passes, the RADIUS server is correctly assigning VLAN 10, but if VLAN 10 is not explicitly permitted on the 802.1Q trunk links along the path, the traffic is dropped at the switch port. The engineer must verify the 'switchport trunk allowed vlan' configuration on all uplinks.
Q3. A stadium ([Transport](/industries/transport) hub / event space) requires a multi-tenant network for operations staff, ticketing vendors, and public guest WiFi. To save time, the junior engineer suggests creating three SSIDs using WPA2-PSK, with a different password for each group. Why is this unacceptable for the ticketing vendors, and what must be implemented instead?
Hinweis: Consider compliance requirements for processing payments.
Musterlösung anzeigen
Using WPA2-PSK is unacceptable for ticketing vendors because they process payments, making them subject to PCI DSS (Payment Card Industry Data Security Standard) compliance. PSKs offer weak security, are easily shared, and do not provide individual user accountability. Furthermore, a shared PSK network does not inherently prevent devices from communicating with each other (client isolation).
Instead, the architecture must implement 802.1X with RADIUS authentication (preferably using WPA3-Enterprise) to provide individual, auditable access. The ticketing vendors must be placed on a dedicated, strictly isolated VLAN, with core firewall rules explicitly denying any routing between the ticketing VLAN and the guest or operations VLANs.