The Future of Wi-Fi Security: AI-Driven NAC and Threat Detection
This authoritative guide explores the evolution of enterprise Wi-Fi security from legacy WPA2 to AI-driven Network Access Control (NAC) and threat detection. Designed for IT leaders, it provides actionable deployment strategies for securing high-density environments like retail, hospitality, and stadiums using Purple's identity-based networks.
Listen to this guide
View podcast transcript
- Executive Summary
- Technical Deep-Dive: The Shift to AI-Driven NAC
- The Failure of Legacy Wireless Security
- AI-Driven NAC Architecture
- Implementation Guide: A Phased Approach
- Phase 1: Network Audit & Segmentation
- Phase 2: Identity & Authentication
- Phase 3: AI-NAC Policy Engine Configuration
- Phase 4: Continuous Monitoring & Compliance
- Best Practices for Enterprise Wi-Fi Security
- Troubleshooting & Risk Mitigation
- ROI & Business Impact

Executive Summary
For IT managers and network architects managing high-density environments—such as retail chains, stadiums, and hospitality venues—the stakes for wireless security have never been higher. Legacy authentication methods like WPA2 Personal and static Pre-Shared Keys (PSKs) are fundamentally broken, offering zero visibility into device posture and exposing networks to credential sharing and lateral movement attacks.
The future of enterprise wireless security is identity-driven and AI-powered. This guide provides a technical deep-dive into deploying AI-driven Network Access Control (NAC) and continuous threat detection. By shifting to 802.1X, dynamic VLAN steering, and machine learning-based anomaly detection, IT teams can achieve zero-trust network access (ZTNA) at the edge. We will explore how platforms like Purple's Guest WiFi and WiFi Analytics integrate with these advanced security frameworks to deliver seamless, compliant, and highly secure connectivity without increasing IT overhead.
Technical Deep-Dive: The Shift to AI-Driven NAC
The Failure of Legacy Wireless Security
Traditional enterprise networks often rely on static VLAN assignments and shared credentials. In a sprawling Hospitality or Retail environment, this approach fails on three fronts:
- Lack of Identity Context: A device connected via a shared PSK is just a MAC address. There is no cryptographic link to a user identity.
- Vulnerability to Lateral Movement: Once an attacker compromises a shared key, they gain unfettered access to the broadcast domain.
- Operational Overhead: Managing MAC allowlists and rotating keys manually across hundreds of locations is unsustainable.
AI-Driven NAC Architecture
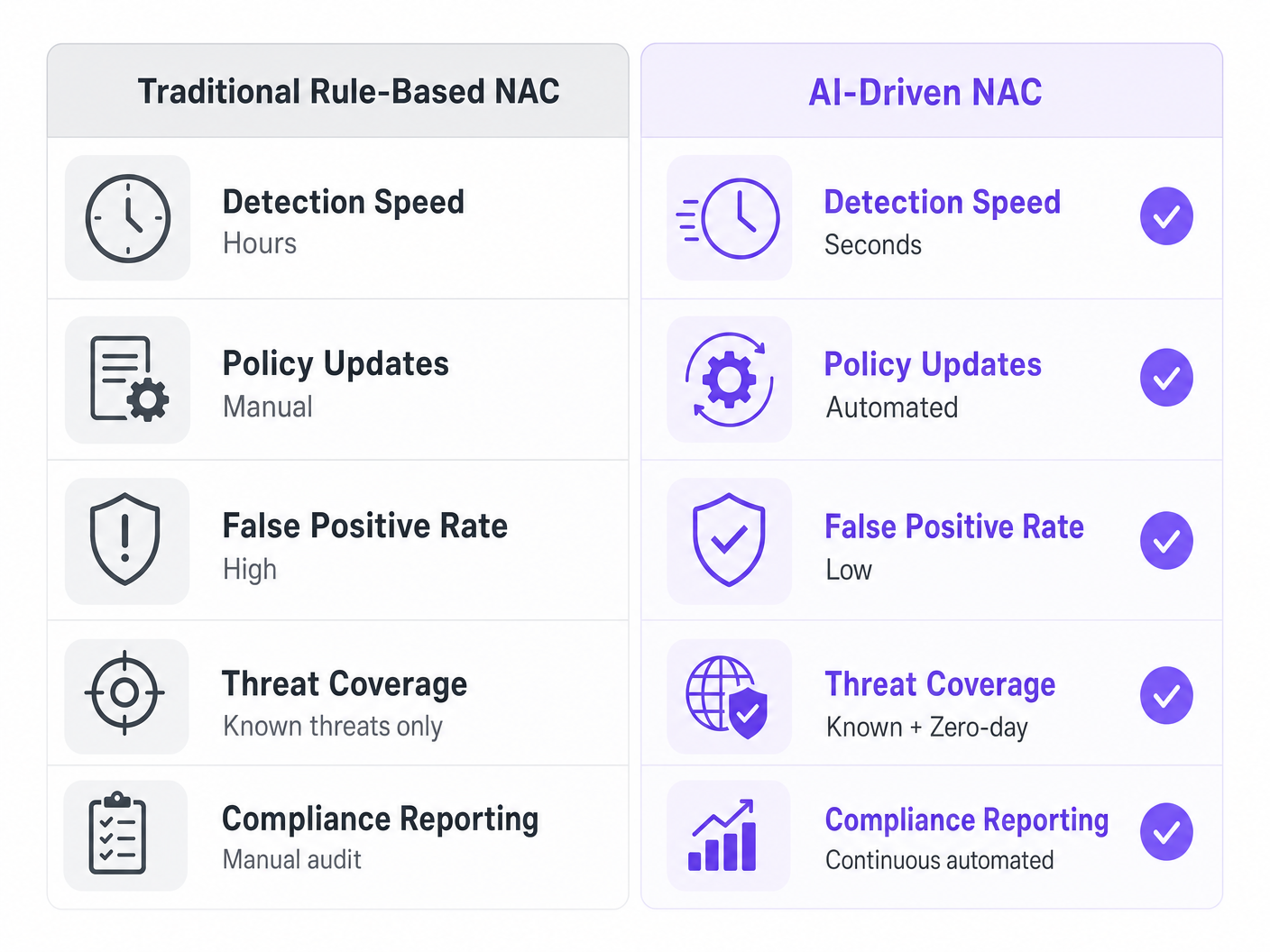
Modern Network Access Control replaces static rules with dynamic, context-aware policies. When integrated with AI and machine learning, the NAC engine doesn't just authenticate the user; it continuously evaluates the device's behaviour.
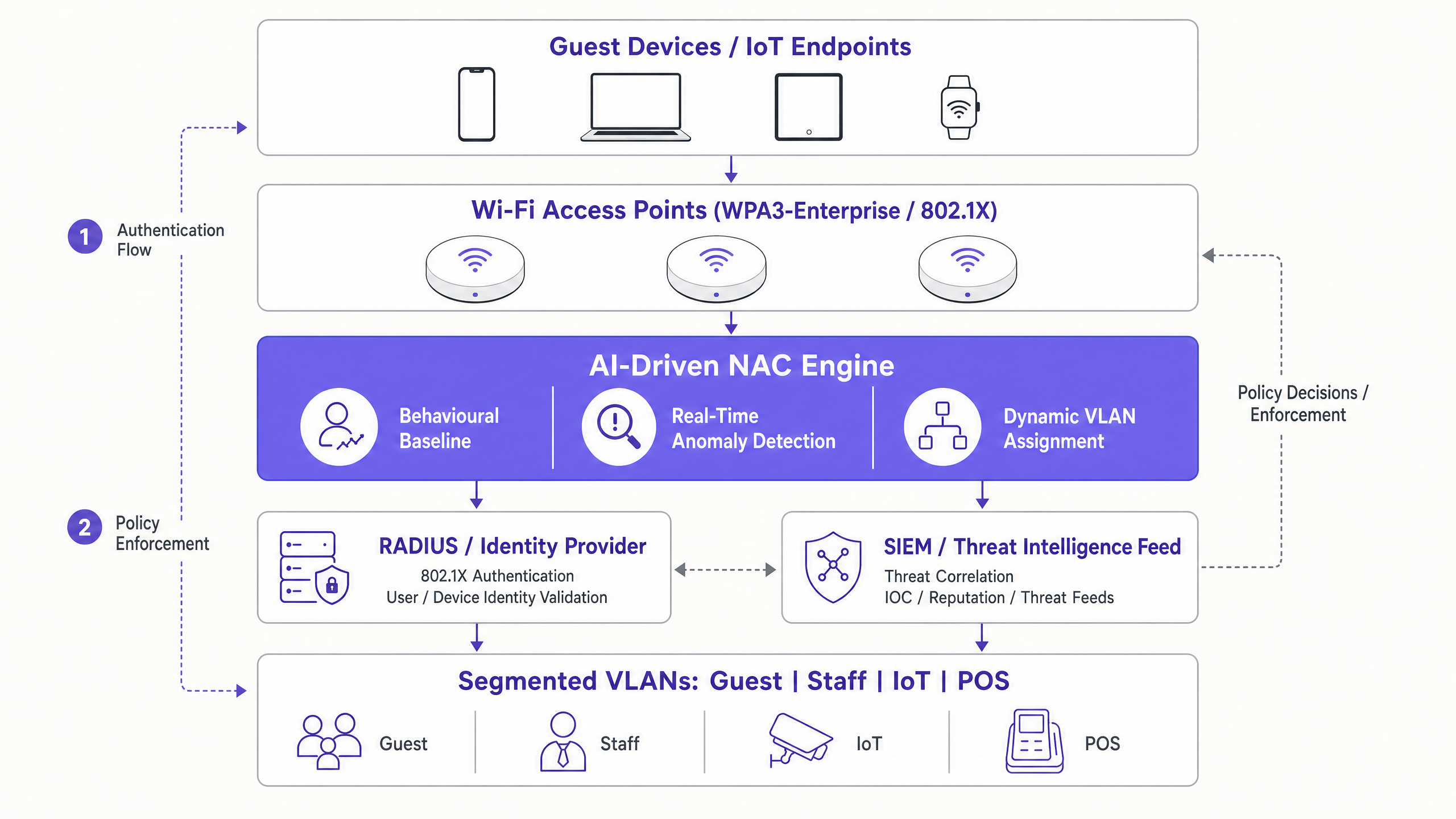
Core Components:
- 802.1X / WPA3-Enterprise: The foundation of secure access. It uses EAP (Extensible Authentication Protocol) to validate credentials against a RADIUS server or Identity Provider (IdP) before granting network access.
- Dynamic VLAN Steering: Upon successful authentication, the RADIUS server returns specific attributes (e.g., Filter-Id or Tunnel-Private-Group-Id). The access point or switch uses these attributes to dynamically place the device into the correct network segment (e.g., Staff, Guest, IoT). For specific vendor implementations, see our guide on How to Configure NAC Policies for VLAN Steering in Cisco Meraki .
- Behavioural Baselining: Machine learning algorithms establish a baseline of normal behaviour for different device types. For instance, a smart thermostat should only communicate with its designated cloud controller.
- Real-Time Threat Detection: If the thermostat suddenly initiates an SSH connection to a Point of Sale (POS) terminal, the AI engine flags this anomaly in milliseconds and triggers an automated policy response—such as quarantining the device or terminating the session.
Implementation Guide: A Phased Approach
Deploying AI-driven NAC across a distributed enterprise requires a structured approach to avoid business disruption.
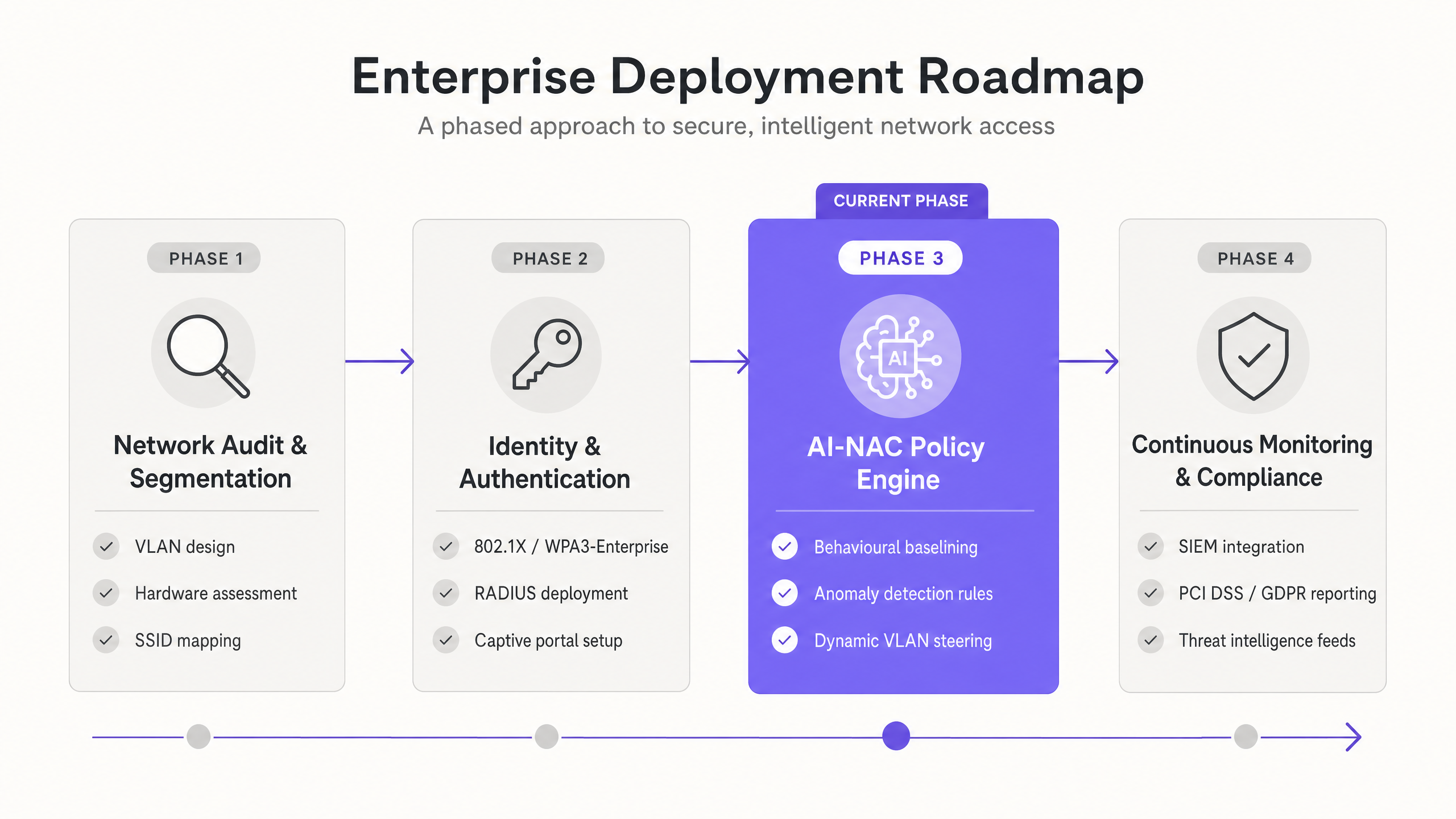
Phase 1: Network Audit & Segmentation
Before implementing NAC, the underlying network architecture must support granular segmentation.
- Map all existing SSIDs and VLANs.
- Design a robust VLAN schema isolating Guests, Staff, IoT devices, and PCI-regulated endpoints.
- Ensure existing access points and switches support 802.1X and RADIUS Change of Authorization (CoA).
Phase 2: Identity & Authentication
Move away from shared passwords to identity-based access.
- Deploy a cloud-native RADIUS infrastructure (like Purple's RADIUS-as-a-Service) to eliminate on-premise hardware.
- Integrate with corporate IdPs (e.g., Microsoft Entra ID, Okta) for staff authentication using EAP-TLS (certificate-based) or PEAP-MSCHAPv2.
- Implement secure onboarding for visitors using a compliant captive portal.
Phase 3: AI-NAC Policy Engine Configuration
Enable the intelligent routing and monitoring features.
- Configure RADIUS return attributes to enforce dynamic VLAN steering based on user group or device profiling.
- Enable machine learning traffic analysis on the wireless controller or overlay platform.
- Define automated quarantine policies for devices exhibiting high-risk behaviour (e.g., port scanning or excessive failed authentications).
Phase 4: Continuous Monitoring & Compliance
Integrate the wireless security posture with broader enterprise security operations.
- Forward wireless telemetry and authentication logs to a SIEM (Security Information and Event Management) platform.
- Automate compliance reporting for PCI DSS and GDPR. Purple's platform, for instance, ensures that guest data collection adheres strictly to UK GDPR and PECR frameworks.
Best Practices for Enterprise Wi-Fi Security
- Enforce Certificate-Based Authentication (EAP-TLS): For staff and corporate devices, EAP-TLS is the gold standard. It eliminates credential theft because the authentication relies on a cryptographic certificate installed on the device via MDM (Mobile Device Management), rather than a password.
- Leverage Identity-Based Guest Wi-Fi: For public access in Transport hubs or retail stores, use a managed captive portal that links the MAC address to a verified identity (email, SMS, or social login). This provides an audit trail and enables powerful marketing analytics.
- Implement Micro-Segmentation: Do not rely on a single 'IoT' VLAN. Segment devices by function (e.g., HVAC, security cameras, digital signage) to limit the blast radius of a compromised endpoint.
- Adopt WPA3: Mandate WPA3 for all new deployments. WPA3-Enterprise introduces mandatory Protected Management Frames (PMF), which defend against deauthentication attacks.
Troubleshooting & Risk Mitigation
Even with automated systems, IT teams must anticipate failure modes:
- RADIUS Timeout/Failure: If the NAC engine cannot reach the cloud RADIUS server, devices will fail to authenticate. Mitigation: Implement a 'fail-open' policy for critical infrastructure on a restricted VLAN, or ensure multi-region RADIUS failover.
- False Positives in Anomaly Detection: Overly aggressive AI models may quarantine legitimate devices, causing operational downtime. Mitigation: Run the AI engine in 'monitor-only' mode for the first 14-30 days to build an accurate baseline before enabling automated enforcement.
- Legacy Device Incompatibility: Older IoT devices (e.g., legacy barcode scanners) may not support 802.1X. Mitigation: Use Identity PSK (iPSK) or MAC Authentication Bypass (MAB) specifically for these devices, assigning them unique passphrases and restricting their access via strict ACLs.
ROI & Business Impact
Transitioning to an AI-driven NAC architecture delivers measurable business value beyond risk reduction:
- Reduced IT OpEx: Automating device onboarding and VLAN assignment significantly reduces helpdesk tickets related to Wi-Fi connectivity and password resets.
- Simplified Compliance: Automated reporting and strict segmentation streamline PCI DSS audits, often reducing the scope of the audit and saving thousands in compliance costs.
- Enhanced Customer Insights: By integrating secure identity validation with platforms like Purple, venues can safely gather demographic data and dwell times, driving targeted marketing campaigns while maintaining GDPR compliance.
Key Definitions
Network Access Control (NAC)
A security solution that enforces policy on devices attempting to access a network, ensuring only authenticated and compliant endpoints are granted entry.
Crucial for IT teams moving away from static passwords to identity-based, zero-trust network architectures.
802.1X
An IEEE standard for port-based network access control that provides an authentication mechanism to devices wishing to attach to a LAN or WLAN.
The foundation of enterprise Wi-Fi security, requiring a RADIUS server to validate credentials before allowing network traffic.
Dynamic VLAN Steering
The process of automatically assigning a device to a specific Virtual Local Area Network (VLAN) based on its identity or role, rather than the SSID it connected to.
Allows venues to broadcast a single SSID while securely segmenting staff, guests, and IoT devices on the backend.
RADIUS (Remote Authentication Dial-In User Service)
A networking protocol that provides centralized Authentication, Authorization, and Accounting (AAA) management for users who connect and use a network service.
The engine room of enterprise Wi-Fi, often deployed as a cloud service (RADIUS-as-a-Service) to reduce on-premise infrastructure.
EAP-TLS
Extensible Authentication Protocol-Transport Layer Security. An authentication method that uses digital certificates on both the client and the server for highly secure, mutual authentication.
The most secure authentication method for corporate devices, eliminating the vulnerabilities associated with passwords.
Identity PSK (iPSK)
A feature that allows multiple unique Pre-Shared Keys to be used on a single SSID, with each key tied to a specific device MAC address and policy.
Essential for securing headless IoT devices (like printers or smart TVs) that cannot support 802.1X authentication.
Behavioural Baselining
The use of machine learning to establish a normal pattern of network activity for a specific device or user over time.
Enables AI-driven threat detection systems to identify anomalies, such as a thermostat suddenly attempting to access a database.
Protected Management Frames (PMF)
A Wi-Fi security feature that encrypts management action frames, preventing attackers from spoofing them to disconnect clients.
Mandatory in WPA3, it mitigates deauthentication attacks commonly used by hackers to capture handshakes or disrupt service.
Worked Examples
A 400-room hotel needs to secure its network. Currently, staff, guests, and smart TVs all share the same WPA2-Personal network with a single password. How should the IT Director redesign this architecture using AI-driven NAC?
- Deploy a cloud RADIUS server and configure the access points for 802.1X authentication.
- Integrate the RADIUS server with the hotel's Azure AD for staff access via PEAP or EAP-TLS.
- Implement Purple Guest WiFi with a captive portal for visitors, placing them on an isolated Guest VLAN (e.g., VLAN 100) with client isolation enabled.
- Use Identity PSK (iPSK) for the smart TVs. The NAC engine assigns a unique pre-shared key to each TV and automatically steers them to a restricted IoT VLAN (e.g., VLAN 200) that can only communicate with the IPTV management server.
- Enable AI behavioural baselining to monitor the smart TVs for anomalous outbound traffic.
A retail chain is rolling out mobile Point of Sale (mPOS) tablets across 50 locations. How can they ensure these devices remain secure and compliant with PCI DSS on the wireless network?
- Enroll all mPOS tablets in an MDM solution and push unique client certificates to each device.
- Configure the wireless network to require WPA3-Enterprise with EAP-TLS authentication.
- Configure the NAC engine to perform a posture check (e.g., verifying the MDM profile and OS version) during authentication.
- Upon successful authentication and posture validation, dynamically steer the tablets to a dedicated, highly restricted PCI VLAN.
- Use AI threat detection to continuously monitor the tablets. If a tablet attempts to connect to an unauthorized external IP, the NAC engine automatically issues a RADIUS CoA to quarantine the device.
Practice Questions
Q1. A hospital IT director is upgrading the wireless network. They have 500 legacy infusion pumps that only support WPA2-Personal and cannot be upgraded to support 802.1X. How should these devices be secured while moving the rest of the network to WPA3-Enterprise?
Hint: Consider how to apply unique credentials to devices that don't support enterprise authentication protocols.
View model answer
The IT director should implement Identity PSK (iPSK) or MAC Authentication Bypass (MAB) for the infusion pumps. By assigning a unique passphrase to each pump's MAC address via the NAC/RADIUS server, the network can dynamically steer these legacy devices into a heavily restricted Medical IoT VLAN. The rest of the network (staff laptops, tablets) can securely use WPA3-Enterprise with EAP-TLS on the same physical infrastructure.
Q2. After deploying an AI-driven NAC solution, the network operations team receives alerts that several smart TVs in the conference centre are being automatically quarantined, disrupting a major event. What is the likely cause and how should it be resolved?
Hint: Think about the lifecycle of deploying machine learning anomaly detection.
View model answer
The likely cause is that the AI anomaly detection was enabled in 'enforcement' mode before it had time to establish an accurate behavioural baseline for the smart TVs. To resolve this, the IT team should immediately move the AI policy engine into 'monitor-only' mode, unquarantine the TVs, and allow the system to learn the normal traffic patterns of the devices for 14-30 days before re-enabling automated enforcement.
Q3. A retail business wants to offer free Guest Wi-Fi across 200 stores while capturing customer data for marketing. They also need to ensure that this public network does not compromise their PCI DSS compliance for the point-of-sale terminals. What is the recommended architecture?
Hint: Focus on segmentation and the role of the captive portal.
View model answer
The business should deploy a managed captive portal solution, like Purple Guest WiFi, on an open SSID to handle user onboarding, consent capture (GDPR), and authentication. Crucially, the underlying network infrastructure must use VLAN segmentation. Guest traffic must be placed on an isolated Guest VLAN that routes directly to the internet, with client isolation enabled. The POS terminals must reside on a completely separate, restricted PCI VLAN, secured via 802.1X or iPSK, ensuring the Guest network is entirely out of scope for the PCI DSS audit.