WiFi Landing Page vs. Splash Page: Was ist der Unterschied?
This technical reference guide clarifies the architectural and functional differences between WiFi landing pages and splash pages — two terms frequently conflated by both IT teams and marketing departments. It provides network architects, IT managers, and venue operations directors with actionable deployment strategies to optimise captive portal performance, ensure GDPR and PCI DSS compliance, and maximise ROI across enterprise venues including hospitality, retail, and public-sector environments.
Diesen Leitfaden anhören
Podcast-Transkript ansehen
- Executive Summary
- Technischer Deep-Dive
- Die Captive Portal-Architektur
- 1. Die Splash Page (Pre-Authentication-Status)
- 2. Die Landing Page (Post-Authentication-Status)
- Authentifizierungsablauf: End-to-End
- Implementierungsleitfaden
- Schritt 1: Walled Garden-Konfiguration
- Schritt 2: SSL-Zertifikatsverwaltung
- Schritt 3: CNA-Optimierung
- Schritt 4: Post-Authentication-Weiterleitungslogik
- Schritt 5: Analytics-Integration
- Best Practices
- Fehlerbehebung & Risikominderung
- ROI & Geschäftsauswirkungen

Executive Summary
Für Enterprise-IT-Teams, die hochfrequentierte Standorte verwalten – von Gastgewerbe -Immobilien bis hin zu Einzelhandel -Filialen – werden die Begriffe „Splash Page“ und „Landing Page“ häufig vermischt. Sie in der Netzwerkarchitektur als austauschbar zu behandeln, führt zu fehlerhaften User Journeys, Sicherheitslücken und verpassten Möglichkeiten zur Datenerfassung.
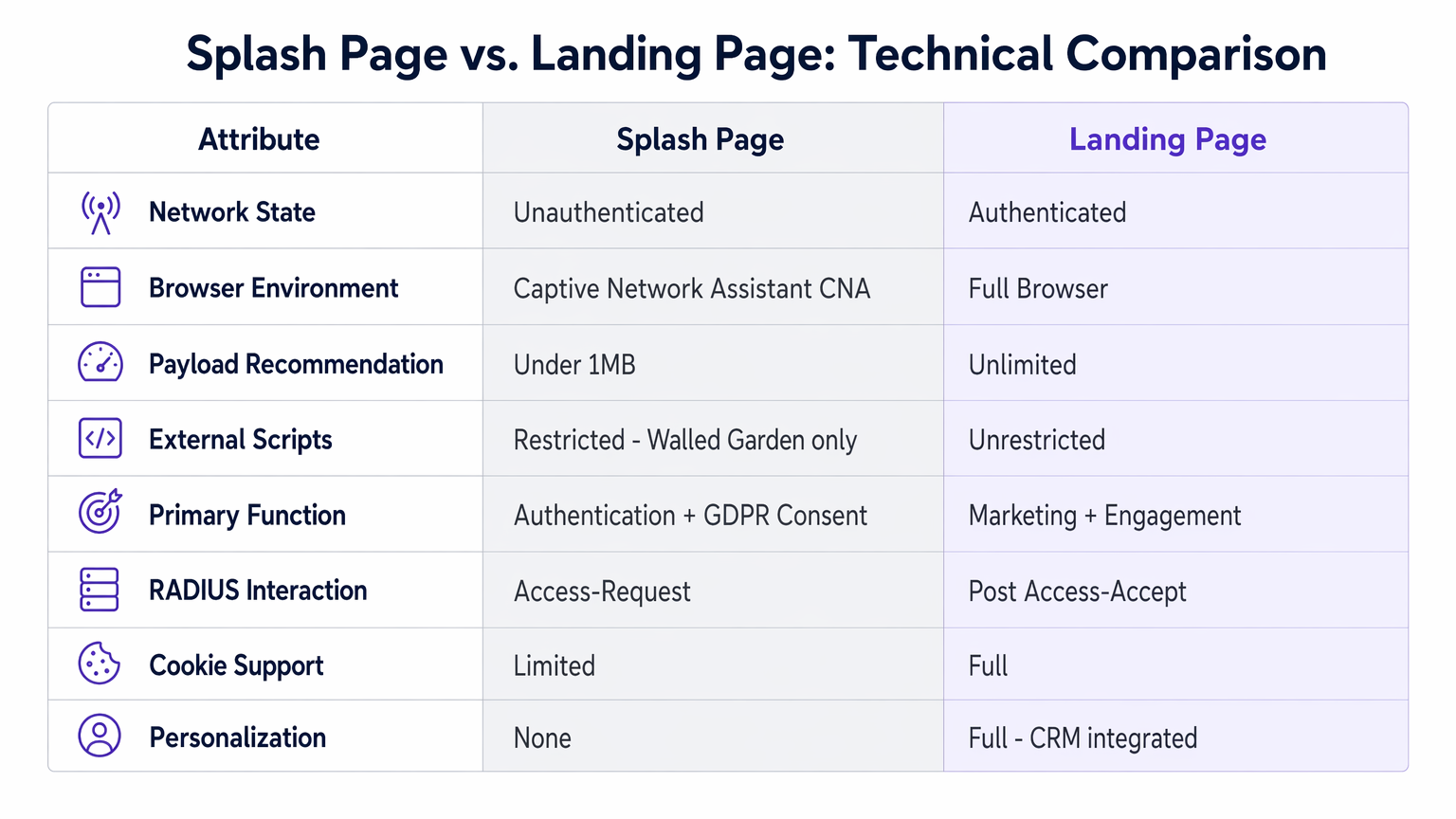
Grundsätzlich ist die Splash Page der Gatekeeper vor der Authentifizierung (Pre-Authentication). Sie existiert in der eingeschränkten Umgebung eines Walled Gardens und ist für die Identitätsprüfung, MAC-Authentifizierung sowie die rechtliche Zustimmung gemäß GDPR und PCI DSS verantwortlich. Die WiFi Landing Page ist das Ziel nach der Authentifizierung (Post-Authentication). Sie operiert im offenen Internet und nutzt die beim Login erfassten Daten, um personalisierte Erlebnisse zu bieten, App-Downloads zu fördern und durch Guest WiFi -Integrationen einen messbaren ROI zu generieren.
Dieser Leitfaden detailliert die technischen Spezifikationen, Bereitstellungsmethoden und häufigen Fehlerquellen im Zusammenhang mit dem Captive Portal-Design – und ermöglicht es Netzwerkarchitekten, robuste, konforme und umsatzgenerierende Gastzugangsnetzwerke für jeden Standorttyp aufzubauen.
Technischer Deep-Dive
Die Captive Portal-Architektur
Ein Captive Portal fängt den HTTP/HTTPS-Datenverkehr von nicht authentifizierten Clients ab und leitet ihn an eine dedizierte Weboberfläche weiter. Dieser Mechanismus basiert auf einer Kombination aus DNS-Hijacking, HTTP-302-Weiterleitung und RADIUS-Authentifizierung – wobei moderne Implementierungen zunehmend RFC 8908 (Captive Portal Identification in DHCP and Router Advertisements) übernehmen, um eine native Captive Portal-Erkennung auf Betriebssystemebene ohne fehleranfälliges HTTP-Interception zu ermöglichen.
Innerhalb dieser Architektur erfüllen die Splash Page und die Landing Page grundlegend unterschiedliche Rollen an verschiedenen Punkten im Authentifizierungslebenszyklus.
1. Die Splash Page (Pre-Authentication-Status)
Wenn sich ein Gerät mit einer SSID verbindet, weist der Wireless Controller es einem nicht authentifizierten VLAN zu. Der gesamte ausgehende Datenverkehr wird abgefangen und an den Hostnamen des Captive Portals weitergeleitet. Der Captive Network Assistant (CNA) des Betriebssystems – ein spezialisierter, in einer Sandbox ausgeführter Pseudo-Browser, der in iOS, Android und Windows integriert ist – erkennt das Captive Portal und rendert die Splash Page.
Technische Einschränkungen der CNA-Umgebung:
Der CNA ist kein vollwertiger Browser. Er arbeitet mit erheblichen Einschränkungen, die sich direkt darauf auswirken, was auf einer Splash Page bereitgestellt werden kann:
- Cookies und lokaler Speicher werden oft blockiert oder stark eingeschränkt
- Komplexe JavaScript-Frameworks können möglicherweise nicht ausgeführt werden
- Externe Ressourcen (Schriftarten, Skripte, Bilder) können nur geladen werden, wenn ihre Domains im Walled Garden auf der Whitelist stehen
- Der CNA schließt sich automatisch, wenn er erkennt, dass das Gerät Internetzugang erhalten hat, bevor der Benutzer die Authentifizierung abgeschlossen hat
- Die Sitzungspersistenz nach dem Schließen des CNA ist unzuverlässig
Hauptfunktionen der Splash Page:
Angesichts dieser Einschränkungen sollte die Splash Page ausschließlich für Folgendes konzipiert sein: Authentifizierung (Social Login via OAuth, SMS-OTP, formularbasierte Anmeldeinformationen oder Integration von Treueprogrammen); Akzeptanz der Allgemeinen Geschäftsbedingungen; Einholung der GDPR-Zustimmung; und Registrierung der MAC-Adresse für zukünftige nahtlose Logins.
Payload-Empfehlung: Halten Sie die Splash Page unter 1 MB. Verwenden Sie Inline-CSS, vermeiden Sie externe Schriftarten-Bibliotheken und minimieren Sie JavaScript. Jede externe Abhängigkeit erfordert einen entsprechenden Whitelist-Eintrag im Walled Garden – was jeweils sowohl einen Wartungsaufwand als auch ein potenzielles Sicherheitsrisiko darstellt.
2. Die Landing Page (Post-Authentication-Status)
Nach erfolgreicher Authentifizierung gibt der RADIUS-Server eine Access-Accept-Nachricht zurück. Der Wireless Controller aktualisiert die Client-Sitzung und migriert das Gerät in ein authentifiziertes VLAN mit vollständigem Internet-Routing. Der Walled Garden wird aufgehoben. Der Controller – oder die cloudbasierte Captive Portal-Plattform – gibt eine HTTP-302-Weiterleitung zur WiFi Landing Page aus.
Zu diesem Zeitpunkt arbeitet das Gerät mit einem vollwertigen Browser und uneingeschränktem Internetzugang. Die Landing Page kann den kompletten Funktionsumfang moderner Webentwicklung nutzen:
- Dynamische, personalisierte Inhalte, gesteuert durch das auf der Splash Page erfasste Benutzerprofil
- Vollständige Analytics-Instrumentierung (Google Analytics, benutzerdefinierte Tracking-Pixel, CRM-Webhooks)
- Rich Media einschließlich Video, interaktiven Karten und Treue-Dashboards
- Aufforderungen zum App-Download mit Deep-Link-Routing
- Zielgerichtete Werbeaktionen basierend auf WiFi Analytics -Daten, einschließlich Besuchshäufigkeit, Verweildauer und Standortzone
Hauptfunktionen der Landing Page: Marketing-Engagement, Anzeige von Treueprogrammen, zielgerichtete Werbeaktionen, Standortnavigation und konversionsgesteuerte Calls-to-Action.
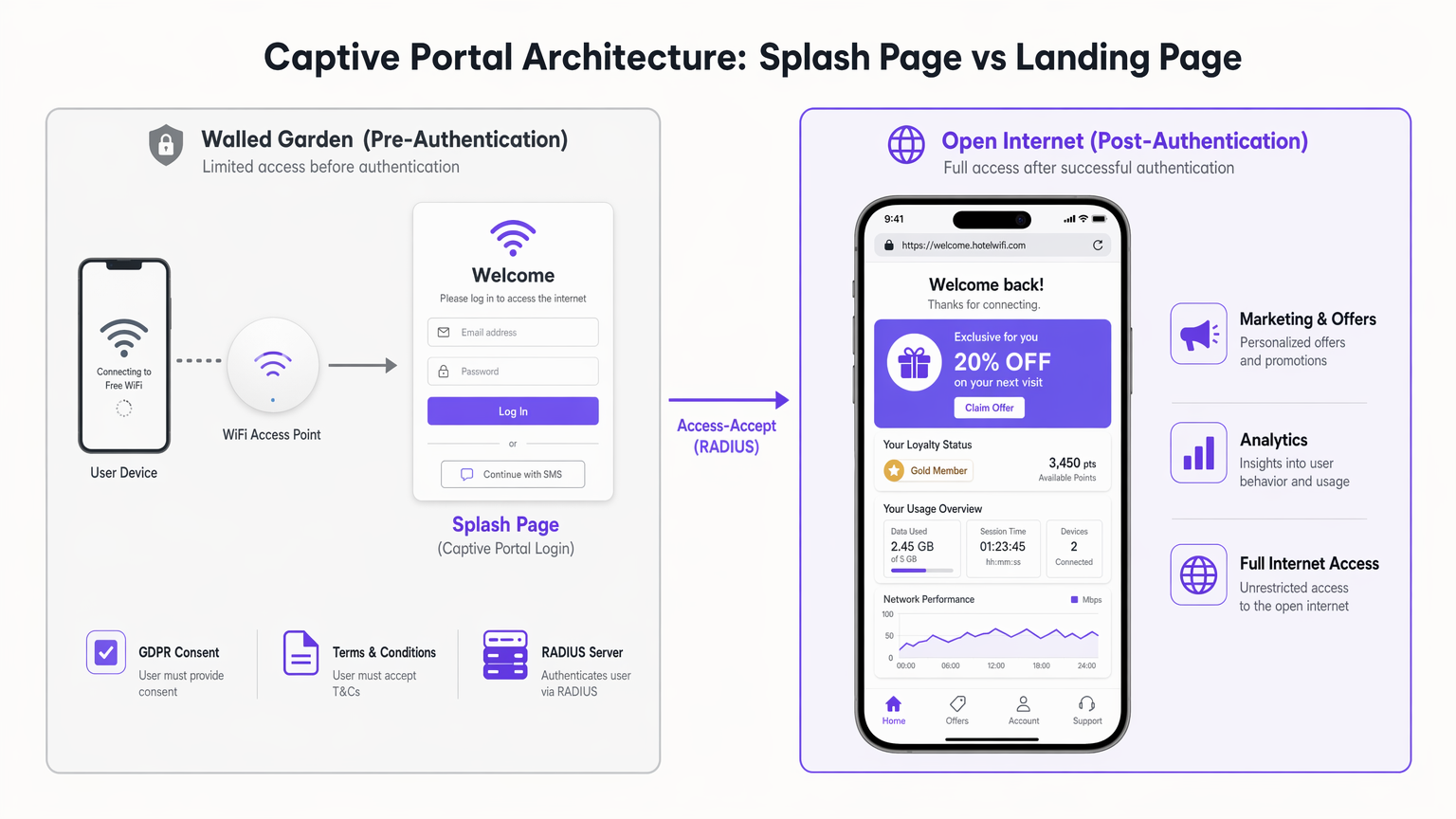
Authentifizierungsablauf: End-to-End
Die folgende Sequenz veranschaulicht den kompletten Ablauf von der SSID-Verbindung bis zur Bereitstellung der Landing Page:
- Client-Gerät verbindet sich mit der Gast-SSID
- Controller weist das Gerät einem nicht authentifizierten VLAN zu
- Client versucht eine HTTP-Anfrage; Controller fängt diese ab und gibt eine 302-Weiterleitung zur Splash Page aus
- CNA lädt die Splash Page (Assets werden nur von Domains bereitgestellt, die im Walled Garden auf der Whitelist stehen)
- Benutzer schließt die Authentifizierung ab und akzeptiert die Allgemeinen Geschäftsbedingungen
- Captive Portal-Plattform sendet einen Access-Request an den RADIUS-Server
- RADIUS gibt Access-Accept zurück; Controller empfängt eine Change of Authorization (CoA)-Nachricht
- Controller migriert den Client in das authentifizierte VLAN
- Captive Portal-Plattform gibt eine 302-Weiterleitung zur WiFi Landing Page aus
- Client-Browser lädt die vollständige Landing Page über das offene Internet
Diese saubere Trennung der Zuständigkeiten – Authentifizierung auf der Splash Page, Engagement auf der Landing Page – ist das architektonische Fundament jeder gut konzipierten Gast-WiFi-Bereitstellung.
Implementierungsleitfaden
Die Bereitstellung einer skalierbaren, unternehmenstauglichen Gast-WiFi-Lösung erfordert die Trennung der Netzwerk-Control-Plane von der User-Experience-Ebene. Die folgenden Schritte bieten ein herstellerneutrales Bereitstellungs-Framework, das auf Infrastrukturen von Cisco Meraki, Aruba, Ruckus und Ubiquiti anwendbar ist.
Schritt 1: Walled Garden-Konfiguration
Konfigurieren Sie Ihren Wireless LAN Controller (WLC) so, dass nur die Domains und IP-Bereiche auf die Whitelist gesetzt werden, die für die Funktion der Splash Page zwingend erforderlich sind. Dies umfasst typischerweise:
- Den Hostnamen der Captive Portal-Plattform (z. B.
portal.purple.ai) - Identity-Provider-Domains für Social Login (z. B.
accounts.google.com,graph.facebook.com) - SMS-Gateway-Domains bei Verwendung der OTP-Authentifizierung
- Alle CDN-Assets, die von der Splash Page selbst verwendet werden
Vermeiden Sie übermäßiges Whitelisting. Jeder zusätzliche Eintrag vergrößert die Angriffsfläche Ihres Pre-Authentication-Netzwerks und erschwert die laufende Wartung, wenn sich IP-Bereiche ändern.
Schritt 2: SSL-Zertifikatsverwaltung
Konfigurieren Sie den WLC mit einem gültigen, öffentlich vertrauenswürdigen SSL-Zertifikat für den Weiterleitungs-Hostnamen des Captive Portals. Selbstsignierte Zertifikate lösen im CNA Browser-Sicherheitswarnungen aus, was dazu führt, dass Benutzer den Verbindungsvorgang abbrechen. Der Ablauf von Zertifikaten ist eine Hauptursache für Ausfälle des Gast-WiFi – implementieren Sie eine automatisierte Erneuerung über Let's Encrypt oder Ihre Zertifikatsverwaltungsplattform.
Schritt 3: CNA-Optimierung
Konzipieren Sie die Splash Page speziell für die CNA-Umgebung. Verwenden Sie Inline-CSS, vermeiden Sie externe JavaScript-Frameworks und testen Sie über mehrere iOS- und Android-Versionen hinweg. Insbesondere das Verhalten des iOS-CNA ändert sich zwischen großen OS-Releases – pflegen Sie eine Regressionstest-Matrix, die mindestens die zwei neuesten Hauptversionen beider Plattformen abdeckt.
Schritt 4: Post-Authentication-Weiterleitungslogik
Konfigurieren Sie die Post-Authentication-Weiterleitung so, dass dynamische Landing Page-URLs unterstützt werden. Der RADIUS-Server kann herstellerspezifische Attribute (VSAs) zurückgeben, oder die Captive Portal-Plattform kann das authentifizierte Benutzerprofil verwenden, um eine personalisierte URL zu erstellen. Dies ermöglicht eine Segmentierung – ein Erstbesucher erhält ein Willkommensangebot, während ein Treuemitglied mit Gold-Status ein personalisiertes Dashboard erhält.
Schritt 5: Analytics-Integration
Instrumentieren Sie die Landing Page mit Ihrem Analytics-Stack. Da sich der Benutzer nun mit einem vollwertigen Browser im offenen Internet befindet, funktionieren Standard-Analytics-Tools normal. Integrieren Sie Ihr CRM, um ein einheitliches Kundenprofil zu erstellen, das WiFi-Sitzungsdaten mit Kaufhistorie, Treuestatus und Marketing-Engagement-Metriken kombiniert.
Einen detaillierten Vergleich von cloudbasierten gegenüber On-Premise-Captive Portal-Architekturen finden Sie unter Cloud-basiertes vs. On-Premise Captive Portal: Was ist das Richtige für Ihr Unternehmen? .
Best Practices
Authentifizierung und Marketing entkoppeln. Die wirkungsvollste architektonische Entscheidung besteht darin, die Splash Page strikt für den sicheren Zugang und die Zustimmung zu nutzen und alle Marketing-Assets auf die Landing Page zu verlagern. Dies verbessert die Verbindungsraten, reduziert Support-Tickets und vereinfacht Compliance-Audits.
MAC Authentication Bypass für wiederkehrende Benutzer nutzen. Für wiederkehrende Geräte eliminiert der MAC Authentication Bypass (MAB) die Splash Page vollständig und leitet Benutzer direkt auf eine personalisierte Landing Page weiter. Dies verbessert die User Experience für wiederkehrende Besucher in Gastgewerbe - und Einzelhandel -Umgebungen drastisch. Stellen Sie sicher, dass Ihre Datenschutzrichtlinie das persistente Geräte-Tracking ausdrücklich abdeckt.
Cloud-zentrierte Architekturen übernehmen. Genau wie sich die Netzwerkbranche in Richtung Software-Defined WAN für zentralisiertes Management bewegt hat – wie in Die zentralen SD-WAN-Vorteile für moderne Unternehmen detailliert beschrieben –, sollten Captive Portal-Plattformen cloudbasiert gehostet werden. Dies ermöglicht ein zentralisiertes Management über verteilte Standorte hinweg, schnelle Inhaltsaktualisierungen ohne Änderungen an der Controller-Firmware und eine nahtlose Integration mit externen CRMs und Marketing-Automatisierungsplattformen.
RFC 8908 für moderne OS-Kompatibilität implementieren. Die native Captive Portal-Erkennung über RFC 8908 verringert die Abhängigkeit von HTTP-Interception und verbessert die Zuverlässigkeit über moderne iOS- und Android-Versionen hinweg, die zunehmend reines HTTPS-Browsing erzwingen.
Einen Walled Garden-Audit-Zeitplan einhalten. Überprüfen Sie Walled Garden-Einträge vierteljährlich. IP-Bereiche für große Identity Provider ändern sich ohne Vorankündigung. Veraltete Einträge, die nicht mehr aufgelöst werden, verursachen Authentifizierungsfehler; fehlende Einträge blockieren legitime Authentifizierungsabläufe.
Fehlerbehebung & Risikominderung
Die Verbindungsschleife. Wenn sich ein Benutzer authentifiziert, aber wiederholt auf die Splash Page zurückgeleitet wird, überprüfen Sie, ob die RADIUS-Access-Accept-Nachricht den Controller erreicht und ob der Client erfolgreich einen DHCP-Lease im authentifizierten VLAN erhält. Überprüfen Sie außerdem, ob der CoA-Port (Change of Authorization, UDP 3799) nicht durch eine zwischengeschaltete Firewall blockiert wird.
Vorzeitiges Schließen des CNA. Wenn sich der CNA schließt, bevor sich der Benutzer authentifizieren kann, hat das Gerät wahrscheinlich vorzeitig einen Internetzugang erkannt. Dies kann auftreten, wenn der Walled Garden zu durchlässig ist und versehentlich vollständiges Internet-Routing zulässt, bevor die Authentifizierung abgeschlossen ist. Überprüfen Sie die Walled Garden-Einträge auf zu weit gefasste CIDR-Bereiche.
HTTPS-Interception-Fehler. Moderne Browser erzwingen HTTP Strict Transport Security (HSTS). Wenn ein Benutzer versucht, vor der Authentifizierung zu einer HSTS-Preloaded-Domain zu navigieren, blockiert der Browser die Captive Portal-Weiterleitung. Implementieren Sie RFC 8908, um die native Captive Portal-Erkennung zu ermöglichen, oder weisen Sie Benutzer an, zu einer Nicht-HSTS-Domain zu navigieren, um den CNA auszulösen.
Fehler bei Drittanbieter-Skripten auf der Splash Page. Wenn Marketing-Teams Tracking-Pixel oder Analytics-Skripte zur Splash Page hinzugefügt haben, schlagen diese in der CNA-Umgebung stillschweigend fehl, wenn ihre Domains nicht auf der Whitelist stehen. Die korrekte Lösung besteht darin, diese Skripte vollständig von der Splash Page zu entfernen und sie auf der Landing Page neu bereitzustellen, wo sie ordnungsgemäß funktionieren.
GDPR-Compliance-Lücken. Stellen Sie sicher, dass der Zustimmungsmechanismus auf der Splash Page die Anforderungen von GDPR Artikel 7 erfüllt – die Zustimmung muss freiwillig, spezifisch, informiert und unmissverständlich erfolgen. Vorab angekreuzte Zustimmungsfelder sind nicht konform. Führen Sie ein Zustimmungs-Audit-Protokoll für mindestens drei Jahre.
ROI & Geschäftsauswirkungen
Eine korrekt implementierte Splash-/Landing Page-Architektur verwandelt das Gast-WiFi von einer Kostenstelle in einen messbaren, umsatzgenerierenden Vermögenswert. Der finanzielle Business Case wirkt sich auf drei Dimensionen aus.
Datenerfassung und First-Party Intelligence. Durch die Optimierung der Splash Page erhöhen Standorte die Verbindungsraten und das Volumen der erfassten First-Party-Daten. In Gesundheitswesen - und Transport -Umgebungen unterstützen diese Daten operative Analysen – Besucherströme, Verweildauer nach Zone und Prognosen von Spitzennachfragen – und ermöglichen Entscheidungen zur Ressourcenzuweisung mit messbaren Kosteneinsparungen.
Direkte Umsatzzuordnung. Die Landing Page ist die primäre Konversionsfläche. Eine Stadion-Bereitstellung kann die Landing Page nutzen, um Essens- und Getränkebestellungen direkt an den Platz zu bewerben, wodurch der Netzwerkzugang direkt mit Transaktionsumsätzen korreliert wird. Ein Hotel kann Spa-Buchungen oder Zimmer-Upgrades anbieten. Ein Einzelhändler kann zonenspezifische Werbeaktionen ausspielen, die durch Echtzeit-Standortdaten aus WiFi Analytics gesteuert werden.
Loyalität und Kundenbindung. Personalisierte Landing Page-Erlebnisse – gesteuert durch das auf der Splash Page erfasste Benutzerprofil – steigern das Engagement in Treueprogrammen. Wiederkehrende Benutzer, die ein personalisiertes Willkommenserlebnis erhalten, weisen im Vergleich zu Benutzern, denen eine generische Landing Page präsentiert wird, eine deutlich höhere Sitzungsdauer und Wiederholungsbesuchsfrequenz auf.
Die messbaren KPIs für eine Gast-WiFi-Bereitstellung sollten Folgendes umfassen: WiFi-Verbindungsrate (Ziel >70 % der Standortbesucher), Datenerfassungsrate (Ziel >85 % der verbundenen Benutzer), Landing Page-Klickrate auf den primären CTA und direkte Umsätze, die WiFi-gesteuerten Werbeaktionen zugeordnet werden.
Hören Sie sich unten den vollständigen technischen Briefing-Podcast an:
Schlüsseldefinitionen
Captive Portal
A web-based access control mechanism that intercepts network traffic from unauthenticated clients and redirects them to an authentication interface before granting broader network access.
The overarching system IT teams deploy to manage guest access, enforce acceptable use policies, capture user consent, and collect first-party data.
Splash Page
The initial authentication interface presented within the captive portal flow, operating within the restricted Walled Garden environment before the user has been granted internet access.
Where network architects must focus on lightweight design, identity verification, and legal consent. Incorrectly overloading this page with marketing assets is the leading cause of guest WiFi connection failures.
WiFi Landing Page
The post-authentication destination page loaded in the user's full browser after the device has been granted internet access by the RADIUS server.
Where marketing and operations teams deploy rich media, personalised content, loyalty integrations, and engagement campaigns. Operates without the constraints of the Walled Garden.
Walled Garden
A restricted network environment that allows unauthenticated users to access only a specific, explicitly whitelisted set of IP addresses or hostnames, blocking all other internet traffic.
The technical boundary within which the Splash Page must operate. Every external resource used by the Splash Page must have its domain or IP range added to the Walled Garden whitelist.
Captive Network Assistant (CNA)
A specialised, sandboxed pseudo-browser built into mobile operating systems (iOS, Android, Windows) that automatically detects and renders captive portal login pages.
The primary reason Splash Pages must be lightweight and avoid complex JavaScript, external cookies, or large media assets. CNA behaviour varies between OS versions and requires ongoing regression testing.
MAC Authentication Bypass (MAB)
A network access control technique that authenticates devices based on their hardware MAC address without requiring user interaction, enabling seamless login for returning devices.
Used to provide frictionless login experiences for returning guests or registered IoT devices. Requires integration between the RADIUS server and the venue's loyalty or device registry database.
RADIUS (Remote Authentication Dial-In User Service)
A networking protocol providing centralised Authentication, Authorisation, and Accounting (AAA) management for network access, defined in RFC 2865.
The backend server infrastructure that validates credentials submitted on the Splash Page, instructs the controller to grant access, and returns user attributes used to personalise the Landing Page.
RFC 8908
The IETF standard defining the Captive Portal API, enabling devices to discover and interact with captive portals natively through DHCP options and Router Advertisements rather than relying on HTTP interception.
A modern standard that improves captive portal reliability across iOS 14+ and Android 11+, reducing CNA-related connection failures caused by HTTPS interception issues.
Change of Authorization (CoA)
A RADIUS extension (RFC 5176) that allows the RADIUS server to dynamically modify an active network session — for example, migrating a client from an unauthenticated to an authenticated VLAN after successful login.
The mechanism by which the captive portal platform instructs the wireless controller to grant internet access after the user completes authentication on the Splash Page.
Ausgearbeitete Beispiele
A 500-room hotel resort is experiencing high drop-off rates on their guest WiFi login. The marketing team recently added a 4MB promotional video and a complex interactive venue map to the initial connection screen. Connection rates have dropped from 68% to 31% since the update. How should the network architect resolve this?
The architect must decouple the authentication and marketing functions. Step 1: Replace the current connection screen with a lightweight Splash Page under 1MB, containing only the authentication form (room number and last name), a GDPR-compliant consent checkbox, and Terms and Conditions acceptance. Step 2: Remove all external script dependencies from the Splash Page and serve all assets from the captive portal platform's own CDN, which is already whitelisted in the Walled Garden. Step 3: Configure the wireless controller's post-authentication redirection to send the user to a newly created Landing Page hosted on the open internet. Step 4: Move the 4MB promotional video and interactive venue map to this Landing Page. Step 5: Instrument the Landing Page with the hotel's CRM integration to personalise the welcome message based on the authenticated user profile. Step 6: Implement MAC Authentication Bypass for returning guests to eliminate the Splash Page entirely on subsequent visits.
A retail chain wants to offer seamless WiFi access to returning loyalty programme members across 50 locations, bypassing the login screen while still displaying a personalised welcome offer and current loyalty points balance. What is the recommended technical architecture?
Implement MAC Authentication Bypass (MAB) integrated with the loyalty database via RADIUS. Architecture: (1) When a returning device associates with the SSID, the controller sends a RADIUS Access-Request containing the device MAC address. (2) The RADIUS server queries the loyalty database to match the MAC address to a loyalty profile. (3) If a match is found, the RADIUS server returns an Access-Accept with a vendor-specific attribute (VSA) containing a signed user token. (4) The controller grants immediate internet access and issues a redirect to the Landing Page URL, appending the signed token as a query parameter. (5) The cloud-hosted Landing Page decodes the token, queries the loyalty API for the user's current points balance and personalised offer, and renders a customised welcome experience. For new users or unrecognised devices, the standard Splash Page flow is presented, with an option to link the device to their loyalty account for future seamless access.
Übungsfragen
Q1. A public sector organisation requires all guest WiFi users to accept a lengthy Acceptable Use Policy (AUP) before accessing the internet. The communications team also wants to display a dynamic feed of upcoming community events and a live social media wall. How should you architect this requirement across the captive portal flow?
Hinweis: Consider the constraints of the Captive Network Assistant (CNA) and the Walled Garden when deciding where to place each content element.
Musterlösung anzeigen
Place the Acceptable Use Policy (AUP) on the Splash Page to ensure legal compliance before authentication. The AUP should be presented as inline text or a scrollable div — not loaded from an external URL — to avoid Walled Garden dependencies. Once the user accepts the AUP and is authenticated, redirect them to the Landing Page to display the dynamic community events feed and social media wall. The social media wall in particular requires external API calls that cannot function within the Walled Garden, making the Landing Page the only viable location.
Q2. During a new deployment at a conference centre, users report that the login screen appears correctly but when they click 'Sign in with LinkedIn', the page times out and returns an error. The controller configuration and RADIUS server are both functioning correctly for email/password authentication. What is the most likely cause and resolution?
Hinweis: Think about what network access is required for a third-party OAuth identity provider to complete its authorisation flow during the pre-authentication phase.
Musterlösung anzeigen
The Walled Garden configuration is incomplete. LinkedIn's OAuth flow requires the client device to communicate with LinkedIn's authorisation servers (e.g., www.linkedin.com, api.linkedin.com) during the pre-authentication phase. These domains are not whitelisted, so the OAuth redirect fails. The resolution is to identify all IP ranges and hostnames used by LinkedIn's OAuth API and add them to the Walled Garden whitelist on the wireless controller. Note that LinkedIn (and other major identity providers) may use multiple CDN-hosted domains — review the OAuth documentation or use a packet capture to identify all required endpoints.
Q3. A retail client wants to track user behaviour on the initial WiFi login screen using Google Analytics 4 and a custom retargeting pixel from their advertising platform. The marketing team has provided a tag manager snippet to be added to the Splash Page. Why is this technically problematic, and what is the recommended alternative that preserves the marketing team's measurement requirements?
Hinweis: Evaluate the capabilities of the CNA mini-browser and the implications of adding external script domains to the Walled Garden.
Musterlösung anzeigen
This is problematic for two reasons. First, the CNA often blocks cookies and restricts JavaScript execution, rendering client-side tracking scripts ineffective or unreliable. Second, Google Tag Manager and advertising pixels load scripts from multiple external domains — adding all of these to the Walled Garden creates significant security exposure and ongoing maintenance overhead. The recommended alternative is a two-part approach: (1) Capture the authentication event server-side via the captive portal platform's API or RADIUS accounting logs, and push this event to Google Analytics 4 using the Measurement Protocol (server-side), which does not require client-side JavaScript. (2) Deploy the full Google Tag Manager container and retargeting pixel on the post-authentication Landing Page, where the full browser environment ensures reliable script execution and cookie-based tracking functions normally.
Weiterlesen in dieser Reihe
Mitarbeiter-WiFi Captive Portal: Onboarding und Authentifizierung von Mitarbeitern
Eine umfassende technische Referenz für IT-Leiter zur Konzeption und Bereitstellung von Mitarbeiter-WiFi Captive Portals. Dieser Leitfaden behandelt EAP-TLS-Authentifizierung, BYOD-Onboarding, VLAN-Segmentierung und Bandbreitenmanagement zur Steigerung der betrieblichen Effizienz und Minimierung von Sicherheitsrisiken.
So richten Sie einen WiFi Hotspot für Ihr Unternehmen ein
Dieser maßgebliche Leitfaden bietet IT-Führungskräften, Netzwerkarchitekten und Direktoren für Veranstaltungsbetrieb eine praktische, herstellerunabhängige Blaupause für die Bereitstellung sicherer, konformer und geschäftsfördernder Gast-WiFi-Hotspots. Er behandelt kritische Architektur-Entscheidungen – von VLAN-Segmentierung und Captive Portal-Konfiguration bis hin zu GDPR-Konformität und Traffic Shaping – und zeigt, wie Netzwerkinfrastruktur von einem Kostenfaktor in eine umsatzsteigernde Analyseplattform umgewandelt werden kann, unter Nutzung der Gast-WiFi- und Analysefunktionen von Purple.
Purple vs. Cisco Spaces (DNA Spaces): Wann man sich für welches entscheiden sollte
Dieser technische Referenzleitfaden bietet einen umfassenden Vergleich von Purple und Cisco Spaces (ehemals DNA Spaces) für die Bereitstellung von Enterprise Captive Portals und Gast-WiFi. Er bewertet architektonische Unterschiede, die Tiefe der Marketingautomatisierung und die kritische Frage der Hardware-Herstellerbindung, um IT-Führungskräften zu helfen, fundierte Infrastruktur-Entscheidungen zu treffen.