WiFi-Zertifikatsauthentifizierung: Wie digitale Zertifikate drahtlose Netzwerke sichern
Dieser maßgebliche Leitfaden beschreibt detailliert, wie X.509 digitale Zertifikate und EAP-TLS anfällige Passwörter in Unternehmens-WiFi ersetzen. Er bietet Netzwerkarchitekten und IT-Managern praktische Implementierungsschritte, PKI-Architekturdesign und eine Analyse des Geschäftsnutzens (ROI).
🎧 Diesen Leitfaden anhören
Transkript anzeigen
- Zusammenfassung für Führungskräfte
- Technischer Deep-Dive: Die Architektur des Vertrauens
- X.509-Zertifikate und PKI-Hierarchie
- 802.1X und EAP-TLS Authentifizierungsablauf
- Die Rolle von Purple im Identitäts-Ökosystem
- Implementierungsleitfaden
- 1. Entwurf der PKI- und RADIUS-Infrastruktur
- 2. Automatisierung der Zertifikatsregistrierung
- 3. Netzwerkkonfiguration und Segmentierung
- Best Practices
- Fehlerbehebung & Risikominderung
- ROI & Geschäftsauswirkungen

Zusammenfassung für Führungskräfte
Die Ära des Pre-Shared Key (PSK) in drahtlosen Unternehmensnetzwerken ist funktional beendet. Für IT-Manager, Netzwerkarchitekten und CTOs, die Unternehmensumgebungen, Gastgewerbebetriebe und Einzelhandelsketten beaufsichtigen, birgt die Abhängigkeit von gemeinsam genutzten Passwörtern ein inakzeptables Risiko, operativen Mehraufwand und Compliance-Verstöße. WiFi-Zertifikatsauthentifizierung – insbesondere über IEEE 802.1X und EAP-TLS – ersetzt erratbare Passwörter durch kryptografisch sichere X.509 digitale Zertifikate.
Durch die mathematische Bindung einer Identität an ein bestimmtes Gerät ermöglicht die Zertifikatsauthentifizierung gegenseitige Authentifizierung, Zero-Trust Network Access (ZTNA) und sofortige Sperrung. Dieser Leitfaden bietet eine definitive technische Referenz dazu, wie digitale Zertifikate drahtlose Netzwerke sichern, und beschreibt die zugrunde liegende Public Key Infrastructure (PKI), die Bereitstellungsarchitektur und die konkreten geschäftlichen Auswirkungen des Übergangs zu einem zertifikatsgestützten Modell. Für Organisationen, die Guest WiFi neben Unternehmensnetzwerken nutzen, ist die ordnungsgemäße Segmentierung dieser Umgebungen bei gleichzeitiger Aufrechterhaltung eines robusten Identitätsmanagements ein kritisches Compliance-Mandat.
Technischer Deep-Dive: Die Architektur des Vertrauens
X.509-Zertifikate und PKI-Hierarchie
Im Mittelpunkt der WiFi-Zertifikatsauthentifizierung steht das X.509 digitale Zertifikat. Im Gegensatz zu einem Passwort ist ein Zertifikat kein geteiltes Geheimnis. Es basiert auf asymmetrischer Kryptografie: einem öffentlichen Schlüssel, der im Zertifikat eingebettet ist, und einem privaten Schlüssel, der sicher in der Hardware des Geräts (wie einem TPM oder Secure Enclave) gespeichert ist.
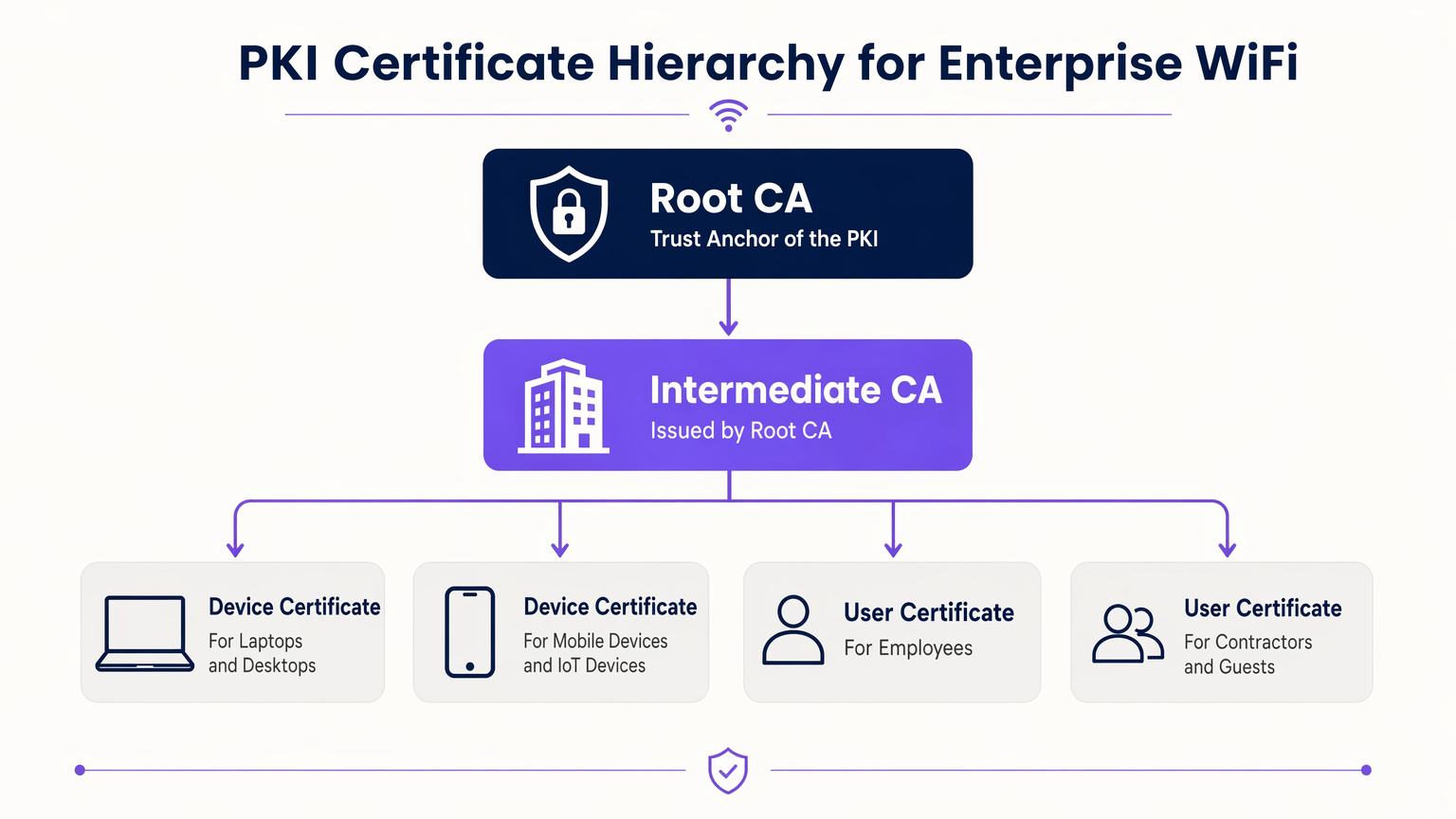
Das Vertrauensmodell für diese Zertifikate ist die Public Key Infrastructure (PKI). In einer Unternehmensumgebung ist eine mehrstufige PKI-Hierarchie Best Practice:
- Root Certificate Authority (CA): Der ultimative Vertrauensanker, der offline gehalten wird, um Kompromittierungen zu verhindern.
- Intermediate CA: Von der Root CA ausgestellt, bleibt dieser Server online, um aktiv Zertifikate für Endgeräte auszustellen und zu widerrufen.
- End-Entity Certificates: Bereitgestellt auf Client-Geräten (Laptops, Telefone, IoT-Sensoren) und Infrastruktur (RADIUS-Server, Access Points).
802.1X und EAP-TLS Authentifizierungsablauf
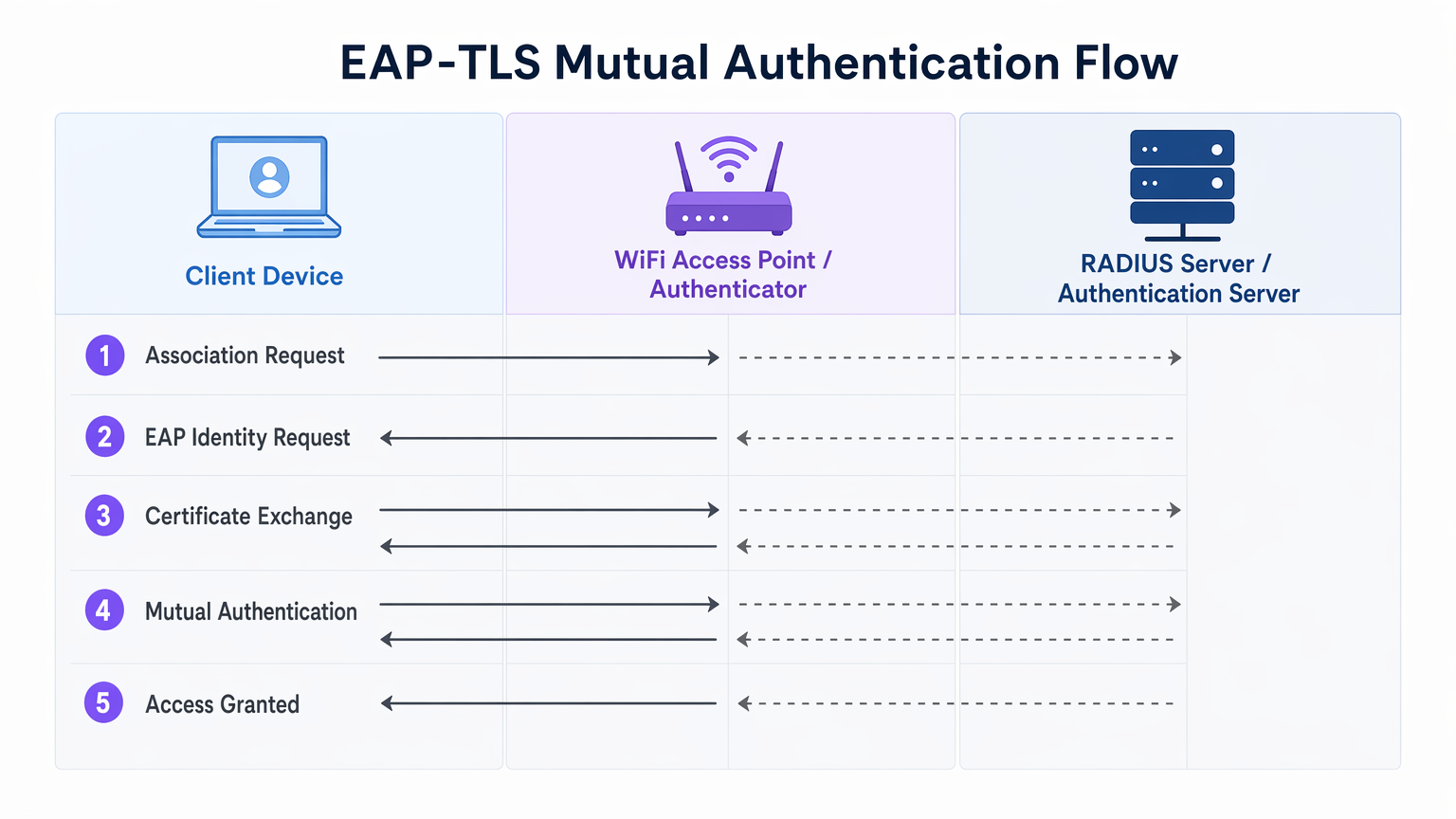
Die Sicherheit von Unternehmens-WiFi basiert auf dem IEEE 802.1X-Standard für die portbasierte Netzwerkzugriffskontrolle. In Verbindung mit EAP-TLS (Extensible Authentication Protocol - Transport Layer Security) ermöglicht es die gegenseitige Authentifizierung.
- Assoziation: Das Client-Gerät verbindet sich mit dem Access Point (Authenticator). Der Netzwerkzugriff wird auf Port-Ebene blockiert.
- Identitätsanfrage: Der AP fordert die Identität des Clients an und leitet den EAP-Verkehr an den RADIUS-Server (Authentifizierungsserver) weiter.
- Server-Authentifizierung: Der RADIUS-Server präsentiert sein Zertifikat dem Client. Der Client überprüft das Zertifikat des Servers anhand seiner vertrauenswürdigen Root CAs, um Rogue AP (Evil Twin)-Angriffe zu verhindern.
- Client-Authentifizierung: Der Client präsentiert sein Zertifikat dem RADIUS-Server. Der Server validiert die Signatur, den Gültigkeitszeitraum und den Widerrufsstatus des Zertifikats.
- Zugriff gewährt: Nach erfolgreicher gegenseitiger Authentifizierung sendet der RADIUS-Server eine
Access-Accept-Nachricht, die oft herstellerspezifische Attribute (VSAs) enthält, um den Client dynamisch einem bestimmten VLAN zuzuweisen.
Die Rolle von Purple im Identitäts-Ökosystem
Während Unternehmensgeräte Unternehmens-PKI und EAP-TLS verwenden, benötigen Gast- und BYOD (Bring Your Own Device)-Benutzer einen anderen Ansatz. Hier integrieren sich Guest WiFi -Plattformen wie Purple in die Architektur. Purple fungiert als robuster Identitätsanbieter für öffentliche SSIDs, erfasst Erstanbieterdaten und ermöglicht Dienste wie OpenRoaming unter der Connect-Lizenz. Dies gewährleistet ein nahtloses, sicheres Onboarding für Gäste, ohne die zertifikatsgesicherte Unternehmens-SSID zu kompromittieren.
Implementierungsleitfaden
Die Bereitstellung der Zertifikatsauthentifizierung erfordert eine sorgfältige Orchestrierung über Ihre Netzwerk-, Identitäts- und Geräteverwaltungssilos hinweg.
1. Entwurf der PKI- und RADIUS-Infrastruktur
- Bereitstellung einer zweistufigen PKI: Verwenden Sie niemals eine flache PKI. Halten Sie die Root CA offline.
- Implementierung von redundantem RADIUS: Stellen Sie mindestens zwei RADIUS-Server (z. B. FreeRADIUS, Cisco ISE, Aruba ISE) in einem Aktiv-Aktiv- oder Aktiv-Passiv-Cluster bereit.
- Konfiguration der Widerrufsprüfung: Entscheiden Sie sich zwischen CRL (Certificate Revocation List) und OCSP (Online Certificate Status Protocol). Für hohe Sicherheits- und geringe Latenzanforderungen ist OCSP obligatorisch.
2. Automatisierung der Zertifikatsregistrierung
Die manuelle Zertifikatsbereitstellung ist nicht skalierbar. Integrieren Sie Ihre PKI in Ihre Mobile Device Management (MDM)- oder Unified Endpoint Management (UEM)-Lösung (z. B. Microsoft Intune, Jamf).
- Verwenden Sie SCEP (Simple Certificate Enrolment Protocol) oder das moderne EST (Enrolment over Secure Transport), um Zertifikate automatisch an in die Domäne eingebundene und verwaltete Geräte zu übertragen.
- Stellen Sie sicher, dass die MDM-Nutzlast sowohl das Client-Zertifikat als auch das vertrauenswürdige Root CA-Zertifikat für den RADIUS-Server enthält.
3. Netzwerkkonfiguration und Segmentierung
- Konfigurieren Sie Ihre WLAN-Controller und Access Points für die Verwendung von WPA3-Enterprise (oder WPA2-Enterprise als Fallback).
- Ordnen Sie RADIUS-Antworten dynamischen VLAN-Zuweisungen zu, um eine Mikrosegmentierung durchzusetzen.
- Sorgen Sie für eine strikte Firewall-Trennung zwischen der Unternehmens-802.1X-SSID und der Captive Portal SSID, die von Ihrer WiFi Analytics -Plattform verwaltet wird.
Best Practices
- Gültigkeitszeiträume abstimmen: Legen Sie die Lebensdauer von Client-Zertifikaten fest (z. B. 1 JJahr) an Ihre MDM-Check-in- und Geräteaktualisierungszyklen anzupassen.
- OCSP-Antworten cachen: Konfigurieren Sie Ihren RADIUS-Server so, dass er OCSP-Antworten (OCSP Stapling) zwischenspeichert, um Authentifizierungs-Timeouts zu verhindern, falls der externe OCSP-Responder nicht erreichbar ist.
- Den Edge überwachen: Verwenden Sie Ihr Netzwerkmanagementsystem, um 802.1X-Timeout- und Ablehnungsraten zu überwachen. Ein plötzlicher Anstieg deutet oft auf eine abgelaufene Zwischen-CA oder eine falsch konfigurierte MDM-Nutzlast hin.
- OpenRoaming nutzen: Für Gastnetzwerke nutzen Sie Passpoint/OpenRoaming-Technologien, bei denen Purple als Identitätsanbieter fungiert und öffentlichen Nutzern ein zertifikatähnliches, nahtloses Roaming ermöglicht.
Fehlerbehebung & Risikominderung
| Fehlermodus | Grundursache | Minderungsstrategie |
|---|---|---|
| Client lehnt Serverzertifikat ab | Die Root-CA des RADIUS-Servers befindet sich nicht im Vertrauensspeicher des Clients. | Pushen Sie die Root-CA über die MDM-Nutzlast, bevor Sie 802.1X erzwingen. |
| Authentifizierung läuft ab | Der RADIUS-Server kann den OCSP-Responder nicht erreichen oder die CRL ist zu groß. | Implementieren Sie OCSP-Caching auf dem RADIUS-Server; stellen Sie sicher, dass der OCSP-Responder hochverfügbar ist. |
| Angriffe durch Rogue APs | Clients sind so konfiguriert, dass sie die Serverzertifikatsvalidierung umgehen. | Erzwingen Sie eine strikte Servervalidierung im MDM-Supplikantenprofil. Erlauben Sie Benutzern niemals, bei unbekannten Zertifikaten auf „Vertrauen“ zu klicken. |
| VLAN-Zuweisung schlägt fehl | RADIUS VSAs stimmen nicht mit der Switch/AP-Konfiguration überein. | Standardisieren Sie VSA-Namenskonventionen bei Ihren Netzwerkhardwareanbietern. |
ROI & Geschäftsauswirkungen
Der Übergang zur WiFi-Zertifikatsauthentifizierung liefert messbare Geschäftsergebnisse für Unternehmensbetreiber:
- Reduzierter Helpdesk-Aufwand: Passwort-Resets machen bis zu 30 % der IT-Helpdesk-Tickets aus. Die automatische Zertifikatsregistrierung eliminiert WiFi-Passwort-bezogene Supportanrufe.
- Beschleunigte Compliance: PCI DSS Anforderung 8 schreibt eindeutige IDs für alle Benutzer vor. EAP-TLS bietet einen kryptografischen Audit-Trail darüber, welches Gerät genau auf das Netzwerk zugegriffen hat, was Compliance-Audits in Retail und Hospitality Umgebungen vereinfacht.
- Eindämmung von Sicherheitsverletzungen: Im Falle eines verlorenen oder gestohlenen Geräts beendet der Widerruf eines einzelnen Zertifikats sofort den Netzwerkzugriff, während ein kompromittierter PSK eine globale Passwortrotation erfordert.
Schlüsselbegriffe & Definitionen
EAP-TLS
Extensible Authentication Protocol with Transport Layer Security. The most secure WiFi authentication method, requiring digital certificates on both the client and the server.
Used when an organisation mandates zero-trust network access and wants to eliminate password-based vulnerabilities.
PKI (Public Key Infrastructure)
The framework of hardware, software, policies, and procedures needed to create, manage, distribute, and revoke digital certificates.
The foundational architecture IT teams must build or procure before deploying certificate-based WiFi.
RADIUS
Remote Authentication Dial-In User Service. A networking protocol that provides centralized Authentication, Authorization, and Accounting (AAA) management.
The server that sits between your WiFi Access Points and your Active Directory/PKI to make the actual 'allow or deny' decision.
802.1X
An IEEE standard for port-based Network Access Control (PNAC). It provides an authentication mechanism to devices wishing to attach to a LAN or WLAN.
The protocol configured on the Access Point that blocks network traffic until the RADIUS server confirms the device is authenticated.
OCSP (Online Certificate Status Protocol)
An internet protocol used for obtaining the revocation status of an X.509 digital certificate in real-time.
Preferred over CRLs in enterprise environments to ensure a stolen device's certificate is rejected instantly.
MDM / UEM
Mobile Device Management / Unified Endpoint Management. Software used to manage, secure, and deploy policies to corporate devices.
The delivery mechanism used to push digital certificates to laptops and phones without manual IT intervention.
Supplicant
The software client on the end-user device that handles the 802.1X authentication process.
Configured via MDM to ensure the device knows which certificates to present and which RADIUS servers to trust.
VSA (Vendor-Specific Attribute)
Custom attributes passed in RADIUS messages to provide specific instructions to network hardware, such as assigning a specific VLAN.
Used to dynamically segment users (e.g., putting an IoT sensor on a restricted VLAN and a CEO's laptop on the corporate VLAN) based on their certificate.
Fallstudien
A 400-room luxury hotel needs to secure its back-of-house corporate WiFi for staff tablets and POS terminals, while maintaining a separate guest network. They currently use a single WPA2-PSK for staff.
- Deploy a two-tier PKI and redundant RADIUS servers.\n2. Use the hotel's MDM to push device certificates via SCEP to all staff tablets and POS terminals.\n3. Configure the corporate SSID for WPA3-Enterprise with EAP-TLS.\n4. Segment the network: Corporate traffic routes internally; guest traffic routes to a separate VLAN managed by Purple's captive portal for analytics.
A large public-sector organisation is experiencing high helpdesk volume due to 90-day WiFi password rotation policies on their corporate network.
Transition from PEAP-MSCHAPv2 (username/password) to EAP-TLS (certificates). Issue 1-year device certificates via Active Directory Certificate Services (AD CS) and Group Policy to all Windows laptops. Configure RADIUS to validate the certificates against AD.
Szenarioanalyse
Q1. Your network monitoring tool alerts you to a sudden 100% failure rate for all 802.1X authentications across your [Retail](/industries/retail) stores. The RADIUS server logs show 'Unknown CA'. What is the most likely cause?
💡 Hinweis:Consider the lifecycle of the certificates in your PKI hierarchy.
Empfohlenen Ansatz anzeigen
The Intermediate CA certificate installed on the RADIUS server has expired. When the Intermediate CA expires, the RADIUS server can no longer validate the chain of trust for the client certificates, causing all authentications to fail. The mitigation is to renew the Intermediate CA and update the RADIUS server.
Q2. You are designing the WiFi architecture for a new corporate headquarters. You need to support corporate laptops, BYOD smartphones, and guest users. How should you structure the SSIDs and authentication?
💡 Hinweis:Remember the rule: Segment the Guests from the Certs.
Empfohlenen Ansatz anzeigen
Deploy two distinct SSIDs. 1) 'Corp-WiFi': Uses WPA3-Enterprise with EAP-TLS for corporate laptops, authenticated via certificates pushed by MDM. 2) 'Guest-WiFi': Uses an open network with a captive portal managed by Purple for BYOD and guests, providing client isolation and routing directly to the internet.
Q3. During an audit of your [Healthcare](/industries/healthcare) network, the auditor notes that users are occasionally prompted to 'Accept' a new certificate when connecting to the corporate WiFi. Why is this a security risk?
💡 Hinweis:Think about what mutual authentication is designed to prevent.
Empfohlenen Ansatz anzeigen
This indicates that the client supplicant is not configured to strictly validate the server certificate. If users can manually accept unknown certificates, an attacker can set up a rogue Access Point (Evil Twin) and trick devices into connecting, potentially intercepting traffic or harvesting credentials. The fix is to push a strict MDM profile that hardcodes the trusted Root CA and prevents user overrides.



