How to Configure 802.1X WiFi Authentication: A Step-by-Step Guide
This technical guide provides a step-by-step walkthrough for configuring 802.1X enterprise WiFi authentication. It covers RADIUS server setup, certificate deployment, and practical deployment strategies for IT leaders across high-footfall venues.
GuidesSlugPage.podcastTitle
GuidesSlugPage.podcastTranscript
- Executive Summary
- Technical Deep-Dive: The 802.1X Architecture
- The Three Core Components
- EAP Methods: Choosing the Right Security Posture
- Implementation Guide: Step-by-Step Configuration
- Step 1: RADIUS Server Preparation
- Step 2: Policy Configuration
- Step 3: Access Point Configuration
- Step 4: Client Supplicant Provisioning
- Best Practices & Industry Standards
- Troubleshooting & Risk Mitigation
- ROI & Business Impact
Executive Summary
For enterprise networks, shared PSKs (Pre-Shared Keys) are no longer sufficient to secure corporate infrastructure. As organisations face stricter compliance mandates (PCI DSS, GDPR) and an expanding attack surface, transitioning to 802.1X authentication is a critical security imperative.
This guide provides a practical, vendor-neutral deployment walkthrough for configuring 802.1X on enterprise access points. We cover the core architecture—Supplicant, Authenticator, and Authentication Server—along with certificate management, RADIUS configuration, and common deployment pitfalls. For IT managers and network architects operating in retail, hospitality, or public-sector environments, this reference provides the actionable steps needed to implement robust, identity-based network access control while keeping corporate and guest traffic strictly separated.
Listen to our companion podcast briefing below for a 10-minute overview of the architecture and implementation strategies.
Technical Deep-Dive: The 802.1X Architecture
The IEEE 802.1X standard defines port-based network access control. In a wireless context, it prevents a client device from sending or receiving data traffic until it has successfully authenticated against a central directory.
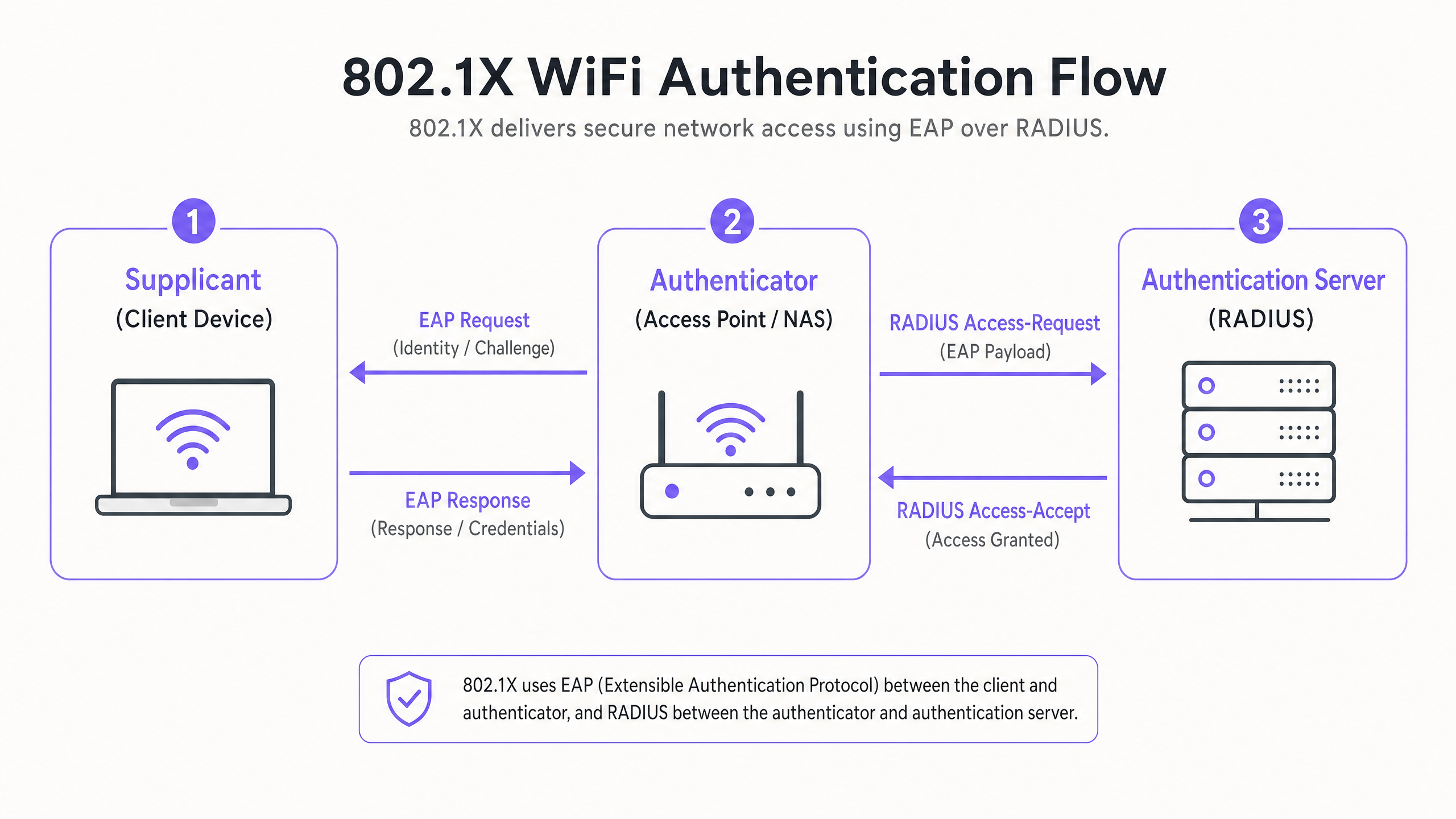
The Three Core Components
- The Supplicant (Client Device): The software on the laptop, smartphone, or IoT device requesting access. It must support the chosen EAP (Extensible Authentication Protocol) method.
- The Authenticator (Access Point / WLC): The network device acting as the gatekeeper. It opens a "controlled port" that only allows EAP traffic until authentication succeeds.
- The Authentication Server (RADIUS): The central server (e.g., Microsoft NPS, FreeRADIUS, Cisco ISE) that validates credentials against an identity store (like Active Directory) and returns an Access-Accept or Access-Reject message.
EAP Methods: Choosing the Right Security Posture
The choice of EAP method dictates your security level and deployment complexity.
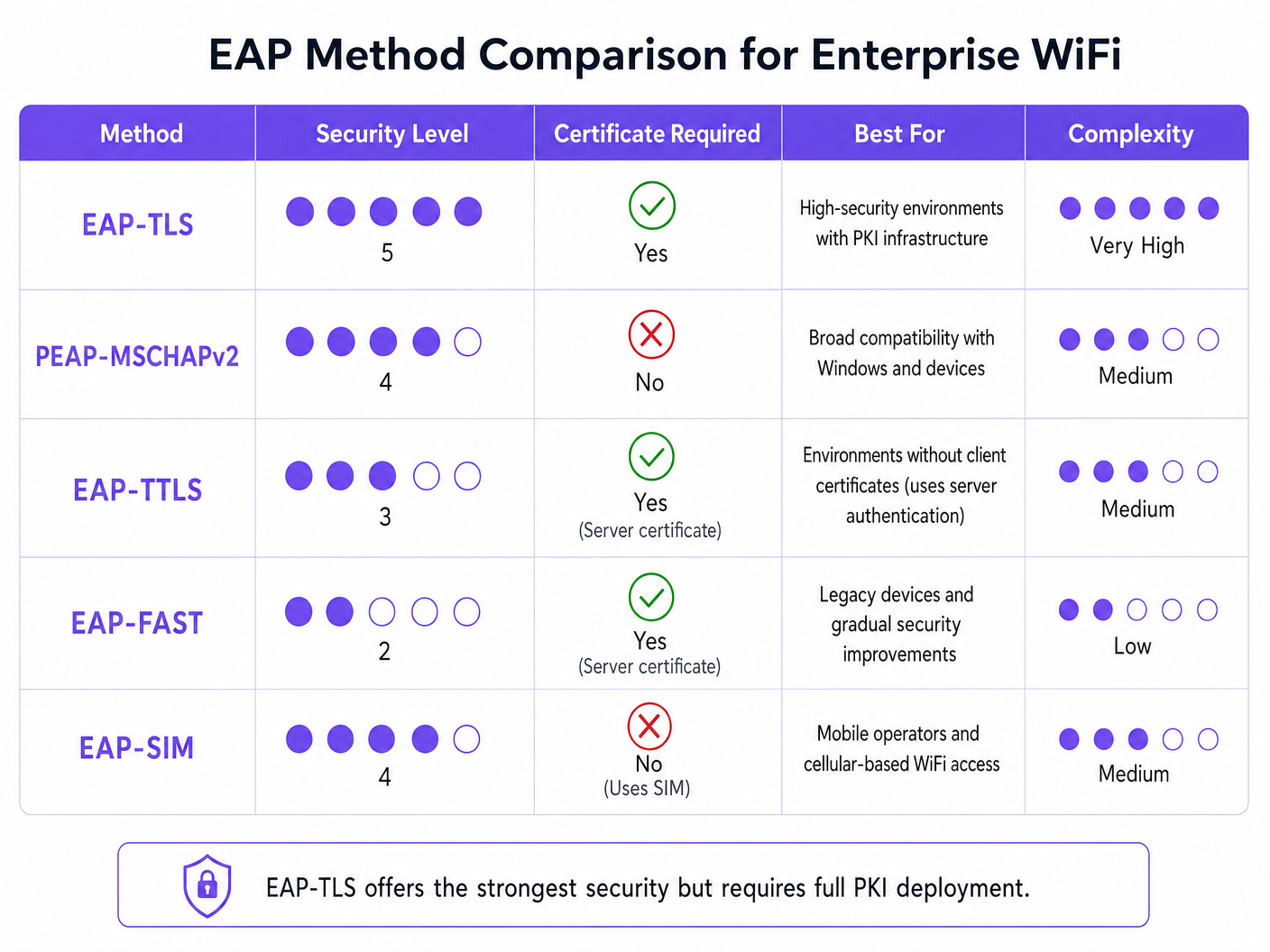
- EAP-TLS (Transport Layer Security): The gold standard. Requires both server and client certificates. No passwords are transmitted. Essential for high-security environments but requires a full Public Key Infrastructure (PKI).
- PEAP-MSCHAPv2 (Protected EAP): The most common enterprise deployment. Uses a server-side certificate to create a secure TLS tunnel, inside which the client sends a username and password. Easier to deploy but vulnerable to credential harvesting if client devices are not configured to strictly validate the server certificate.
- EAP-SIM/AKA: Utilises SIM card credentials for authentication. Increasingly relevant for seamless onboarding in Transport hubs and large public venues.
Implementation Guide: Step-by-Step Configuration
Deploying 802.1X requires coordinated configuration across your RADIUS server, your access points, and your client devices.
Step 1: RADIUS Server Preparation
Whether you are using Microsoft Network Policy Server (NPS) or an alternative, the core principles remain identical.
- Define RADIUS Clients: Register each Access Point (or Wireless LAN Controller) in your RADIUS server. Assign a strong, randomly generated Shared Secret (minimum 22 characters) to secure communications between the AP and the RADIUS server.
- Install the Server Certificate: For PEAP or EAP-TLS, install an X.509 certificate on the RADIUS server. Using a certificate from a trusted public Certificate Authority (CA) simplifies deployment for BYOD environments, as the root certificate is already trusted by client operating systems.
Step 2: Policy Configuration
Configure your network policies to dictate access rights based on identity.
- Connection Request Policies: Define how the RADIUS server handles incoming requests. Typically, this involves matching the NAS-Port-Type (Wireless - IEEE 802.11) and authenticating requests locally.
- Network Policies: Map Active Directory groups to network access rights. For example, map the 'Domain Computers' group to the corporate VLAN. Use RADIUS attributes (
Tunnel-Type=VLAN,Tunnel-Medium-Type=802,Tunnel-Private-Group-ID=[VLAN_ID]) to dynamically assign VLANs upon successful authentication.
Step 3: Access Point Configuration
Configure the SSID on your wireless infrastructure (e.g., Meraki, Aruba, Cisco).
- Create a new SSID and select WPA2-Enterprise or WPA3-Enterprise.
- Enter the IP address of your primary and secondary RADIUS servers.
- Input the Shared Secret defined in Step 1.
- Enable Dynamic VLAN Assignment if your RADIUS server is pushing VLAN attributes.
Step 4: Client Supplicant Provisioning
This is the most critical and often overlooked step. Do not rely on users to manually configure their devices.
- Corporate Devices: Use Group Policy Objects (GPO) or your Mobile Device Management (MDM) platform to push the WiFi profile. The profile must specify the trusted Root CA and the exact server name of your RADIUS server to prevent Evil Twin attacks.
- BYOD: Implement an onboarding portal or MDM solution to push secure profiles to employee-owned devices.
Best Practices & Industry Standards
To ensure a robust deployment, adhere to the following architectural best practices:
- Strict Certificate Validation: Never allow clients to blindly accept any server certificate. This is the primary vector for PEAP credential harvesting.
- Isolate Guest Traffic: Your 802.1X infrastructure is for corporate access. Guest traffic must remain completely segregated. Implement a dedicated Guest WiFi platform with its own captive portal and analytics layer. As discussed in our guide on Protect Your Network with Strong DNS and Security , logical separation is fundamental to network defence.
- Implement Redundancy: RADIUS is a critical path service. Deploy primary and secondary RADIUS servers. In distributed environments like large Retail chains, consider local RADIUS proxies for survivability if the WAN link drops.
Troubleshooting & Risk Mitigation
When deployments fail, it usually comes down to a few common configuration errors:
- RADIUS Timeout Errors: Often caused by a mismatched Shared Secret between the AP and the RADIUS server, or firewall rules blocking UDP ports 1812 (Authentication) and 1813 (Accounting).
- Client Rejection: Check the RADIUS event logs (e.g., Windows Event Viewer -> Custom Views -> Server Roles -> Network Policy and Access Services). Look for Event ID 6273. Common causes include expired client certificates or the client failing to trust the server's certificate chain.
- VLAN Assignment Failures: If authentication succeeds but the client gets no IP address, verify that the switch port connected to the AP is configured as a trunk port allowing the dynamically assigned VLAN.
ROI & Business Impact
Implementing 802.1X drives significant operational and security ROI:
- Risk Mitigation: Eliminates the risk of a single compromised PSK breaching the entire corporate network, directly supporting PCI DSS and GDPR compliance efforts.
- Operational Efficiency: Centralises access control. When an employee leaves, disabling their Active Directory account immediately revokes their WiFi access. No need to rotate PSKs across the enterprise.
- Network Visibility: Provides granular visibility into exactly who is on the network and what device they are using, enabling better capacity planning and threat hunting.
For complex, high-density environments like stadiums or Hospitality venues, managing corporate security alongside guest access is challenging. By securing corporate assets with 802.1X and leveraging a robust WiFi Analytics platform for visitor traffic, IT leaders can deliver secure, scalable connectivity that serves both the business and its customers. For insights on managing high-density environments, review our Zoo and Theme Park WiFi: High-Footfall Venue Connectivity Guide .
GuidesSlugPage.keyDefinitionsTitle
802.1X
An IEEE standard for port-based network access control that provides an authentication mechanism to devices wishing to attach to a LAN or WLAN.
The foundational protocol for enterprise WiFi security, replacing vulnerable shared passwords.
Supplicant
The client device or software application requesting access to the network.
IT teams must manage supplicant configuration via MDM to ensure secure connections.
Authenticator
The network device (Access Point or Switch) that facilitates the authentication process by acting as a proxy between the Supplicant and the Authentication Server.
Configured with the RADIUS server IP and a shared secret to securely forward EAP traffic.
RADIUS
Remote Authentication Dial-In User Service; a networking protocol that provides centralized Authentication, Authorization, and Accounting (AAA) management.
The backend server (like Microsoft NPS) that actually validates the user's credentials against a directory.
EAP (Extensible Authentication Protocol)
An authentication framework frequently used in wireless networks and point-to-point connections, supporting multiple authentication methods.
The 'language' spoken between the Supplicant and the RADIUS server.
EAP-TLS
An EAP method that uses Transport Layer Security, requiring both server and client-side certificates for mutual authentication.
The most secure method available, often mandated for high-security or classified environments.
PEAP
Protected Extensible Authentication Protocol; encapsulates EAP within an encrypted and authenticated TLS tunnel.
The most widely deployed enterprise method, balancing security with ease of deployment by only requiring a server-side certificate.
Dynamic VLAN Assignment
The process where a RADIUS server instructs the Access Point to place an authenticated user onto a specific VLAN based on their directory group membership.
Crucial for segmenting network traffic (e.g., separating HR, Engineering, and IoT devices) while broadcasting only a single corporate SSID.
GuidesSlugPage.workedExamplesTitle
A 300-room luxury hotel needs to secure its back-of-house operational network (staff tablets, VoIP phones, management laptops) while keeping it entirely separate from the guest network. They currently use a single PSK for staff.
- Deploy Microsoft NPS linked to the hotel's existing Active Directory.
- Configure PEAP-MSCHAPv2, using a public certificate (e.g., DigiCert) on the NPS server to simplify tablet onboarding.
- Create an 802.1X SSID ('Hotel_Ops') on the APs.
- Use the hotel's MDM platform to push the 'Hotel_Ops' WiFi profile to all staff tablets and laptops, explicitly configuring the profile to trust the DigiCert root CA and validate the NPS server name.
- Maintain the existing open guest SSID, routing it through Purple's captive portal for terms acceptance and analytics, ensuring guest VLANs cannot route to the operational VLANs.
A university campus is migrating to 802.1X and needs to support a massive BYOD environment for 15,000 students across various operating systems.
- Deploy a robust RADIUS cluster (e.g., FreeRADIUS or Cisco ISE) with load balancing.
- Implement PEAP-MSCHAPv2 for broad device compatibility.
- Deploy an onboarding portal (e.g., SecureW2) that automatically configures the student's device supplicant to use the correct EAP settings and trust the university's RADIUS server certificate.
- Use dynamic VLAN assignment via RADIUS attributes to place students into appropriate subnets based on their campus location to manage broadcast domains.
GuidesSlugPage.practiceQuestionsTitle
Q1. Your organisation is deploying 802.1X using PEAP-MSCHAPv2. During testing, users report they are prompted to 'Accept a Certificate' when connecting for the first time. How should you address this?
GuidesSlugPage.hintPrefixConsider the security implications of allowing users to make trust decisions regarding network infrastructure.
GuidesSlugPage.viewModelAnswer
You must configure the client supplicant profiles (via MDM or Group Policy) to explicitly trust the Root CA that issued the RADIUS server's certificate, and to validate the specific server name. Relying on users to manually accept certificates trains them to ignore security warnings and leaves the network vulnerable to Evil Twin (credential harvesting) attacks.
Q2. You need to secure a fleet of warehouse barcode scanners. They support WPA2-Enterprise but do not have a mechanism to install client certificates or join Active Directory. What is the most secure deployment approach?
GuidesSlugPage.hintPrefixEvaluate the EAP methods that do not require client-side certificates but still provide encrypted authentication.
GuidesSlugPage.viewModelAnswer
Deploy PEAP-MSCHAPv2. Create a dedicated service account in your directory for the scanners. Configure the RADIUS server with a server certificate to establish the TLS tunnel, and configure the scanners to authenticate using the service account credentials inside the tunnel. Ensure the RADIUS policy restricts this service account to a specific, isolated warehouse VLAN.
Q3. After configuring the APs and the RADIUS server, client devices successfully authenticate (verified in RADIUS logs with an Access-Accept), but they fail to receive an IP address and cannot access the network. What is the most likely infrastructure issue?
GuidesSlugPage.hintPrefixAuthentication has succeeded, meaning the 802.1X phase is complete. The issue lies in the subsequent network provisioning phase.
GuidesSlugPage.viewModelAnswer
The most likely issue is a VLAN misconfiguration on the wired network. If the RADIUS server is using dynamic VLAN assignment to place the client on a specific VLAN (e.g., VLAN 20), the switch port connecting the Access Point must be configured as an 802.1Q trunk port that allows VLAN 20. If the VLAN is not trunked to the AP, the client's DHCP requests will be dropped.



