How to Configure WPA2-Enterprise on Common Access Point Platforms (Cisco, Aruba, Ubiquiti)
This technical reference guide provides senior IT professionals and network architects with a definitive, vendor-specific walkthrough for deploying WPA2-Enterprise on Cisco, Aruba, and Ubiquiti platforms. It details architecture, RADIUS integration, compliance requirements, and real-world deployment scenarios across enterprise and venue environments.
GuidesSlugPage.podcastTitle
GuidesSlugPage.podcastTranscript
Executive Summary
Deploying WPA2-Enterprise is no longer an optional security upgrade; it is the fundamental baseline for any enterprise wireless network. For IT managers and network architects operating in hospitality, retail, and public-sector environments, the shift from pre-shared keys to 802.1X authentication is driven by stringent compliance mandates, including PCI DSS and GDPR. This technical reference guide provides actionable, platform-specific configuration steps for the three dominant access point vendors: Cisco, Aruba, and Ubiquiti.
By transitioning to WPA2-Enterprise, organisations eliminate the risks associated with shared credentials, gain granular per-session audit trails, and enable dynamic network segmentation. When implemented correctly, this architecture not only secures the corporate perimeter but also integrates seamlessly alongside visitor networks managed by a comprehensive Guest WiFi platform. The following sections detail the technical architecture, deployment steps, and risk mitigation strategies required for a successful rollout.

Technical Deep-Dive
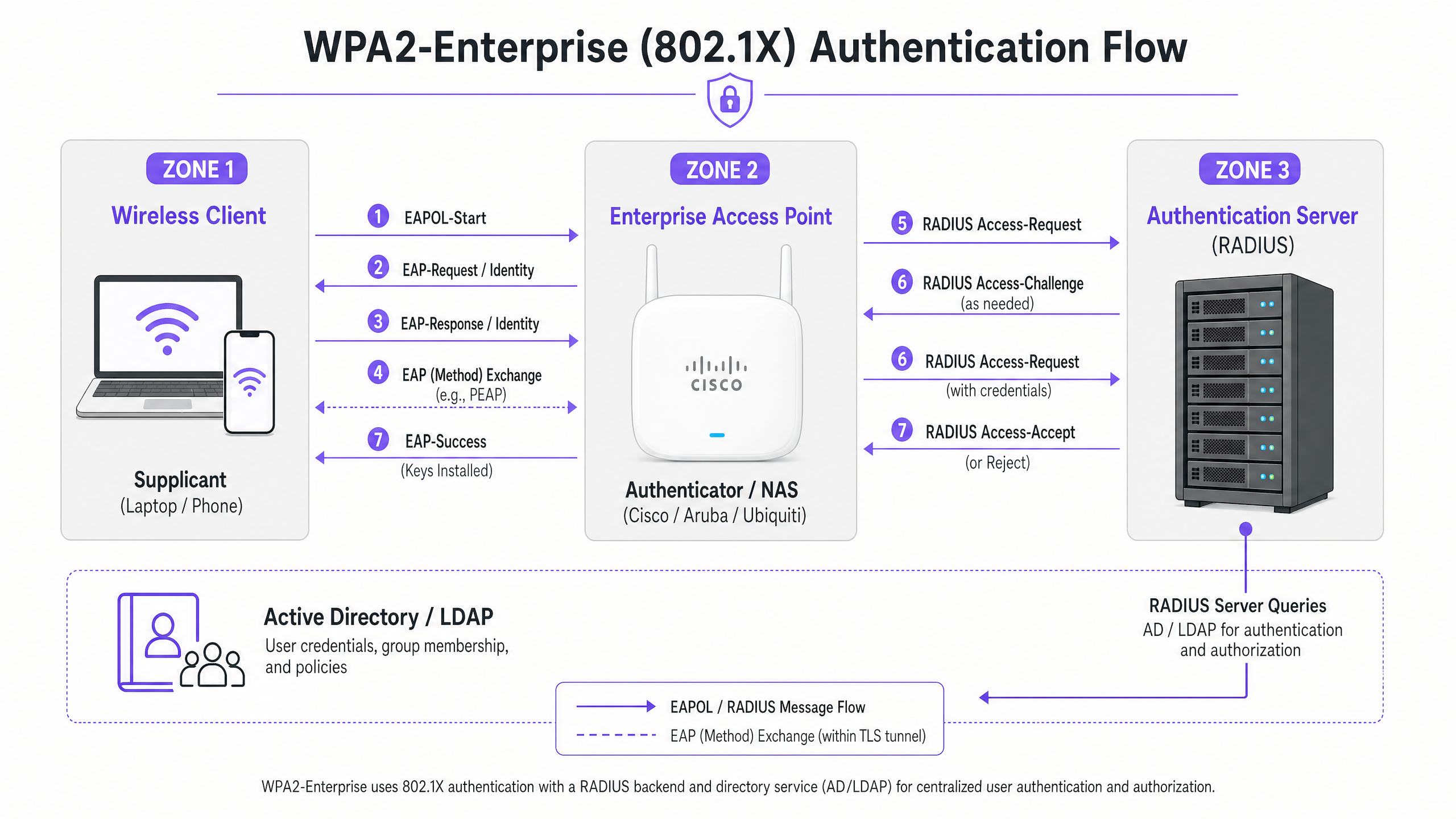
WPA2-Enterprise relies on the IEEE 802.1X standard to deliver port-based network access control. Unlike WPA2-Personal, which uses a static Pre-Shared Key (PSK), WPA2-Enterprise requires every supplicant (client device) to authenticate individually against an external Authentication Server (typically a RADIUS server) before network access is granted.
The architecture consists of three primary components:
- The Supplicant: The client device attempting to connect to the network.
- The Authenticator: The enterprise access point or wireless LAN controller (e.g., Cisco WLC, Aruba Mobility Controller) that facilitates the authentication process.
- The Authentication Server: The backend RADIUS server (e.g., Cisco ISE, Aruba ClearPass, Windows NPS) that validates credentials against a directory service like Active Directory or LDAP.
The EAP Exchange Process
The authentication process utilises the Extensible Authentication Protocol (EAP) encapsulated over LAN (EAPOL). The authenticator acts purely as a pass-through proxy during the initial phase. Once the RADIUS server validates the credentials, it returns an Access-Accept message to the authenticator, which then derives the necessary encryption keys to secure the wireless session.
The choice of EAP method is critical. PEAP-MSCHAPv2 is the most widely deployed method as it supports legacy Active Directory password authentication while securing the exchange within a TLS tunnel established by the server's certificate. However, for maximum security, EAP-TLS is recommended. EAP-TLS requires mutual certificate authentication—both the server and the client must present valid certificates—which mitigates credential theft but requires a robust Public Key Infrastructure (PKI) or Mobile Device Management (MDM) solution for certificate distribution.
Implementation Guide
The fundamental principles of configuring WPA2-Enterprise are consistent across vendors, but the execution varies based on the management interface and ecosystem.
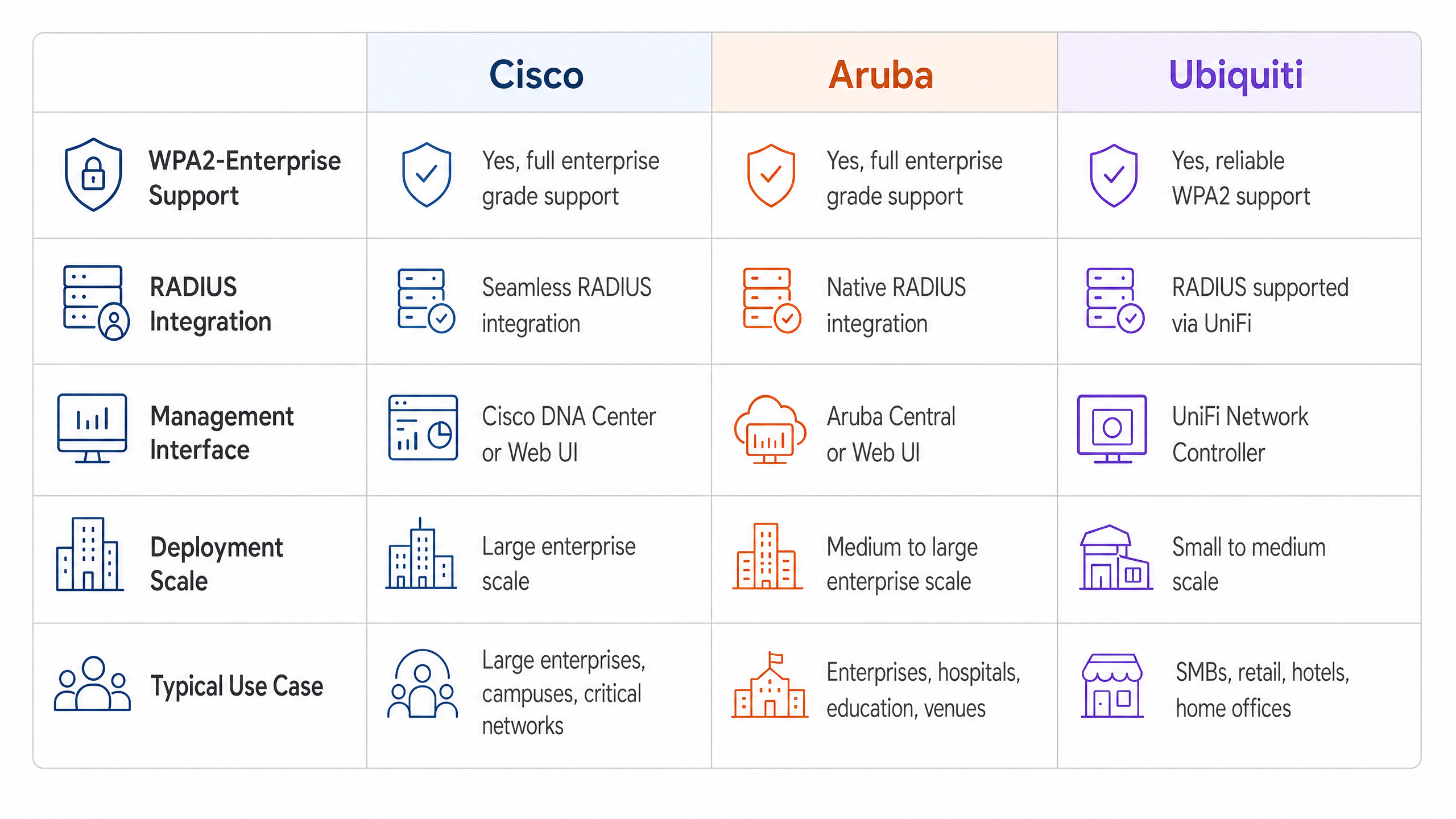
Cisco (Catalyst and Meraki)
Cisco environments typically scale from campus deployments to distributed enterprise networks.
Cisco Catalyst (WLC/DNA Center):
- Define RADIUS Servers: Navigate to the Security tab, select AAA, and configure the primary and secondary RADIUS Authentication and Accounting servers. Ensure the shared secret matches the RADIUS server configuration.
- Create WLAN Profile: Under the WLANs tab, create a new profile.
- Configure Security Policies: Set Layer 2 Security to WPA+WPA2 and enable 802.1X as the Authentication Key Management (AKM) method.
- Bind AAA Servers: Map the previously defined RADIUS servers to the WLAN profile. Enable 'AAA Override' if dynamic VLAN assignment is required.
Cisco Meraki:
- SSID Configuration: In the Meraki Dashboard, navigate to Wireless > SSIDs and select the target network.
- Access Control: Set the association requirement to 'WPA2-Enterprise with my RADIUS server'.
- RADIUS Settings: Input the IP addresses, authentication port (typically 1812), accounting port (1813), and shared secrets for your RADIUS infrastructure. Meraki’s dashboard includes a built-in testing tool to verify RADIUS connectivity before deployment.
Aruba Networks
Aruba is the dominant platform in Hospitality and higher education, heavily leveraging its ClearPass Policy Manager for advanced access control.
- Define AAA Profile: In Aruba Central or the Mobility Controller UI, create a new AAA profile. This profile dictates how authentication is handled.
- Configure RADIUS Server Group: Add your RADIUS servers to a server group, specifying failover rules and timeout values. Attach this group to the AAA profile.
- Virtual AP Configuration: Create or modify a Virtual AP (SSID) profile. Set the security type to WPA2-Enterprise.
- Attach Profiles: Bind the AAA profile to the Virtual AP profile. If using ClearPass, ensure that the RADIUS CoA (Change of Authorization) port (3799) is permitted through any intervening firewalls to allow dynamic policy enforcement.
Ubiquiti (UniFi)
Ubiquiti provides a cost-effective solution for Retail and SMB environments via the UniFi Network Controller.
- RADIUS Profile Creation: Navigate to Settings > Profiles > RADIUS. Create a new profile with the IP address, ports (1812/1813), and shared secret of your external RADIUS server.
- SSID Configuration: Go to Settings > WiFi and create a new wireless network.
- Security Settings: Select 'WPA2 Enterprise' as the security protocol and attach the newly created RADIUS profile.
- Note on RADIUS Infrastructure: Unlike enterprise controllers that may offer localised survivable RADIUS, UniFi relies heavily on external servers (e.g., FreeRADIUS, Windows NPS). Ensure reliable connectivity between the UniFi APs and the RADIUS backend.
Best Practices
To ensure a resilient and secure deployment, network architects must adhere to several critical best practices:
- Enforce Certificate Validation: Client devices must be explicitly configured to validate the RADIUS server's certificate against a trusted Certificate Authority (CA). Failing to do so exposes the network to 'Evil Twin' attacks where rogue access points harvest user credentials.
- Implement RADIUS Redundancy: The RADIUS server is in the critical path for network access. Always configure primary and secondary RADIUS servers. In distributed environments, consider cloud-hosted RADIUS solutions for high availability.
- Utilise Dynamic VLAN Assignment: Use RADIUS attributes (e.g.,
Tunnel-Pvt-Group-ID) to dynamically assign users to specific VLANs based on their Active Directory group membership. This enforces network segmentation without broadcasting multiple SSIDs. - Enable RADIUS Accounting: Do not configure authentication alone. RADIUS accounting (Port 1813) is mandatory for generating the audit trails required for compliance frameworks.
- Protect the Network Edge: Read more about securing your infrastructure in our guide on how to Protect Your Network with Strong DNS and Security .
Troubleshooting & Risk Mitigation
Even with careful planning, deployments can encounter issues. Common failure modes include:
- Shared Secret Mismatches: A simple typo in the RADIUS shared secret will result in silent authentication failures. Verify secrets on both the authenticator and the RADIUS server.
- Time Synchronization Errors: Certificate validation requires accurate timekeeping. Ensure all APs, controllers, and RADIUS servers are synchronised via a reliable NTP source.
- Firewall Blocking RADIUS Traffic: Ensure UDP ports 1812 (Authentication) and 1813 (Accounting) are open between the APs/Controllers and the RADIUS server. If using CoA, ensure UDP 3799 is open.
- Client Supplicant Misconfiguration: The most common issue is the client device not being configured to trust the CA that issued the RADIUS server's certificate. Use MDM or Group Policy to push the correct wireless profiles to corporate devices.
For a broader understanding of authentication protocols, review How to Configure 802.1X WiFi Authentication: A Step-by-Step Guide .
ROI & Business Impact
Transitioning to WPA2-Enterprise delivers significant business value beyond raw security improvements.
- Risk Mitigation: Eliminating shared passwords drastically reduces the attack surface and the risk of a data breach, which can carry severe financial and reputational penalties.
- Operational Efficiency: Integrating WiFi authentication with existing identity providers (like Active Directory) automates the onboarding and offboarding of employees. When an employee leaves, disabling their AD account instantly revokes their WiFi access.
- Compliance Enablement: Granular audit trails and per-user authentication are prerequisites for PCI DSS and ISO 27001 compliance.
- Unified Infrastructure: By using dynamic VLAN assignment, venues can run corporate, back-of-house, and IoT traffic securely over the same physical hardware used for guest access. The guest network can then be monetised and analysed using a dedicated WiFi Analytics solution, maximising the return on hardware investment. Ensure you have the necessary bandwidth by understanding What Is a Leased Line? Dedicated Business Internet .
GuidesSlugPage.keyDefinitionsTitle
WPA2-Enterprise
A security protocol for wireless networks that uses IEEE 802.1X to provide per-user authentication via an external server, rather than a single shared password.
The mandatory standard for securing corporate and operational WiFi networks in enterprise environments.
802.1X
An IEEE standard for port-based network access control that provides an authentication mechanism to devices wishing to attach to a LAN or WLAN.
The underlying framework that makes WPA2-Enterprise work.
RADIUS
Remote Authentication Dial-In User Service; a networking protocol that provides centralized Authentication, Authorization, and Accounting (AAA) management.
The server component that validates user credentials against a database like Active Directory.
Supplicant
The software client on a device (laptop, smartphone) that communicates with the authenticator to request network access.
The endpoint that must be configured with the correct EAP settings and certificate trust.
Authenticator
The network device (Access Point or Switch) that facilitates the authentication process by passing messages between the supplicant and the authentication server.
The Cisco, Aruba, or Ubiquiti hardware managed by the IT team.
EAP (Extensible Authentication Protocol)
An authentication framework frequently used in wireless networks and point-to-point connections, supporting multiple authentication methods.
The protocol used to encapsulate the credential exchange.
PEAP-MSCHAPv2
An EAP method that encapsulates the MSCHAPv2 password exchange within a secure TLS tunnel established by the server's certificate.
The most common deployment method as it balances security with the convenience of using standard AD passwords.
Dynamic VLAN Assignment
The process where a RADIUS server instructs the access point to place an authenticated user onto a specific VLAN based on their identity or group membership.
Crucial for network segmentation, allowing different user types to share the same physical APs securely.
GuidesSlugPage.workedExamplesTitle
A 200-room hotel needs to deploy secure WiFi for its back-of-house staff (housekeeping, management) using existing Aruba access points, while keeping the staff traffic strictly separated from the guest network.
The IT team configures a single 'Hotel_Staff' SSID using WPA2-Enterprise. They integrate Aruba ClearPass with the hotel's Active Directory. In ClearPass, they configure enforcement policies: if a user is in the 'Management' AD group, ClearPass returns a RADIUS attribute assigning them to VLAN 10 (Management Network). If the user is in the 'Housekeeping' group, they are assigned to VLAN 20 (Operations Network). The APs are configured to enforce these dynamic VLAN assignments.
A national retail chain with 50 locations uses Cisco Meraki. They need to secure their point-of-sale (POS) terminals over WiFi to meet PCI DSS compliance, replacing their old WPA2-Personal setup.
The network architect deploys a cloud-hosted RADIUS service to avoid deploying local servers at each store. In the Meraki dashboard, they configure the 'Retail_POS' SSID for WPA2-Enterprise and point it to the cloud RADIUS IPs. They generate unique client certificates for each POS terminal via their MDM platform and configure the RADIUS server to require EAP-TLS. The Meraki APs are configured to send both RADIUS Authentication and Accounting data to the cloud service.
GuidesSlugPage.practiceQuestionsTitle
Q1. Your organisation is deploying WPA2-Enterprise using Ubiquiti UniFi access points. During testing, clients can connect successfully, but the compliance team notes that there are no logs of user session durations or data usage in the central logging system. What is the most likely configuration omission?
GuidesSlugPage.hintPrefixAuthentication grants access, but another process tracks usage.
GuidesSlugPage.viewModelAnswer
The RADIUS Accounting port (1813) has not been configured or is being blocked by a firewall. While Authentication (port 1812) is working, Accounting must be explicitly enabled to generate session audit trails.
Q2. A user reports they cannot connect to the corporate WPA2-Enterprise network. You check the Cisco WLC logs and see the AP is passing the EAP-Request, but the RADIUS server logs show an 'Access-Reject' due to 'Unknown CA'. What needs to be fixed?
GuidesSlugPage.hintPrefixThink about the trust relationship established during the TLS tunnel setup.
GuidesSlugPage.viewModelAnswer
The client device's supplicant is not configured to trust the Certificate Authority (CA) that issued the RADIUS server's certificate. The client is terminating the connection to prevent a potential Evil Twin attack. The CA certificate must be pushed to the client device.
Q3. You are designing a network for a stadium. You need to support corporate staff, ticketing terminals, and guest WiFi. How should you architect the SSIDs to minimize RF interference while maintaining security?
GuidesSlugPage.hintPrefixAvoid broadcasting an SSID for every single use case.
GuidesSlugPage.viewModelAnswer
Deploy a maximum of two SSIDs. One SSID for Guests using a captive portal (like Purple). A second SSID for all corporate operations using WPA2-Enterprise. Use Dynamic VLAN Assignment via the RADIUS server to segment the corporate staff onto one VLAN and the ticketing terminals onto another based on their authentication credentials.



