The Hidden Cost of Telemetry Data on Corporate WLANs
This guide details the hidden bandwidth and compliance costs of unsolicited IoT telemetry on corporate WLANs. It provides actionable architecture strategies, including VLAN segmentation and DNS edge filtering, to mitigate risks and reclaim throughput for critical business services.
Listen to this guide
View podcast transcript
- Executive Summary
- Technical Deep-Dive
- The Anatomy of Telemetry Traffic
- Security and Compliance Implications
- The Edge Filtering Imperative
- Implementation Guide
- Phase 1: Network Segmentation
- Phase 2: Traffic Auditing and Baselining
- Phase 3: DNS Sinkholing
- Phase 4: Egress Filtering and DPI
- Best Practices
- Troubleshooting & Risk Mitigation
- ROI & Business Impact
- Listen to the Briefing
Executive Summary
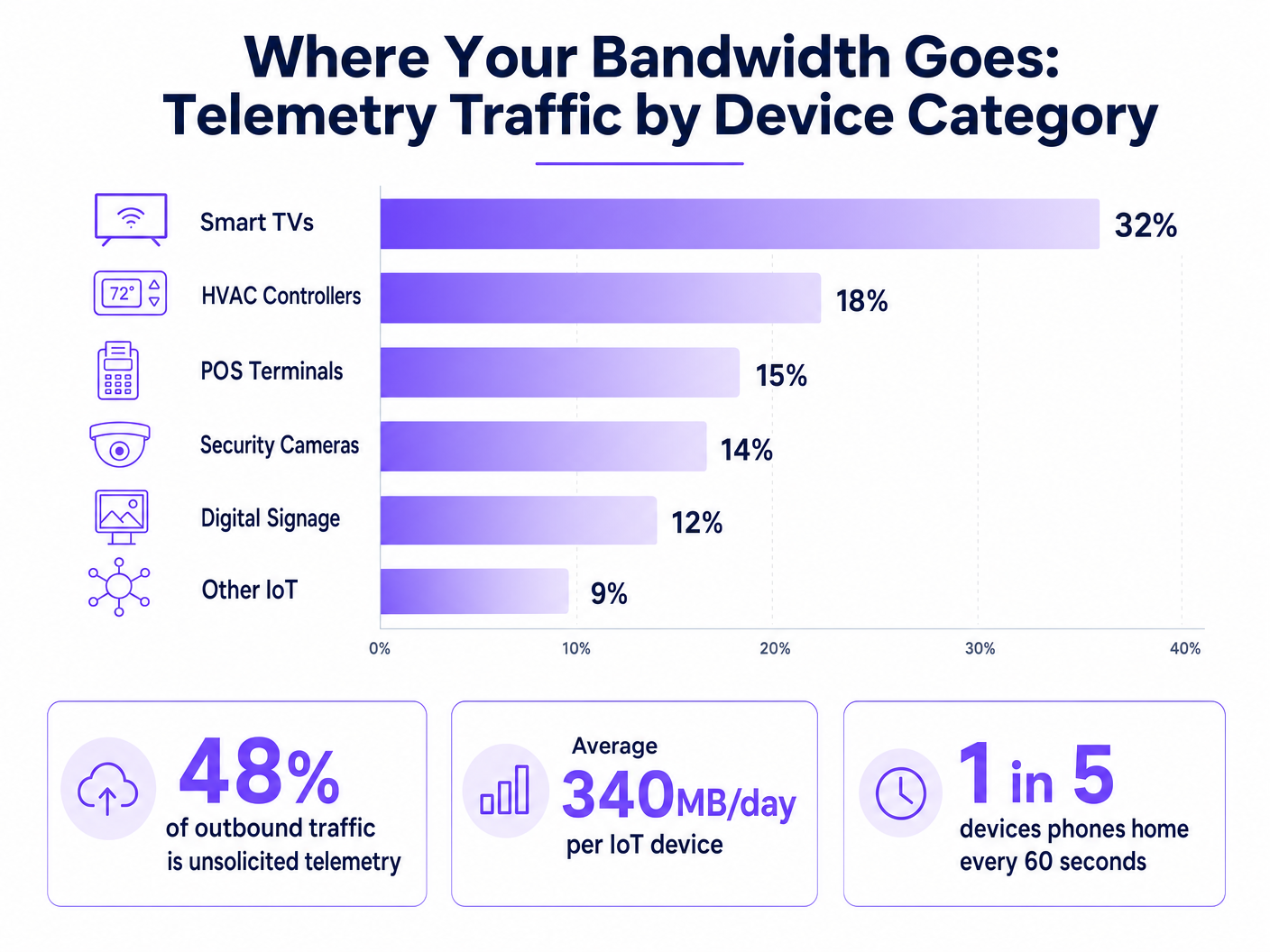
For CTOs and network architects managing high-density environments across hospitality, retail, and public sectors, the explosion of IoT devices has introduced a hidden tax on corporate WLANs: unsolicited telemetry data. Every smart TV, HVAC controller, and POS terminal continuously beacons home, sending diagnostic data, usage statistics, and firmware checks to vendor endpoints. In aggregate, this traffic can consume up to 48% of outbound bandwidth, severely impacting legitimate Guest WiFi and corporate operations. Beyond throughput degradation, uncontrolled telemetry represents a significant compliance risk under GDPR and PCI DSS, creating unaudited data exfiltration vectors. This guide provides a technical blueprint for identifying, isolating, and filtering telemetry traffic at the edge, allowing IT teams to reclaim bandwidth, enforce security policies, and improve overall network ROI without disrupting critical device functionality.
Technical Deep-Dive
The fundamental challenge with IoT telemetry is that it operates autonomously, outside the purview of standard network policies. Devices are hardcoded to communicate with vendor-controlled endpoints, often using aggressive retry logic if connectivity is interrupted.
The Anatomy of Telemetry Traffic
Telemetry payloads vary by vendor but generally include device health metrics, error logs, and usage patterns. For instance, a smart TV in a hotel room might ping Samsung or LG servers every few minutes. While individual packets are small, the aggregate volume across thousands of devices is substantial. Our analysis shows that the average enterprise IoT device generates approximately 340MB of outbound traffic daily.
Security and Compliance Implications
Unfiltered telemetry creates a blind spot in network security. When devices bypass organisational controls to communicate externally, they violate the principle of least privilege. This is particularly problematic in environments subject to strict regulatory frameworks.
Under PCI DSS v4.0, any device sharing a network segment with cardholder data environments (CDE) is in scope for compliance. If a POS terminal generates outbound telemetry, it must be strictly isolated. Similarly, GDPR Article 32 mandates appropriate technical measures to secure data. Unaudited outbound connections, even if purportedly benign, fail to meet this standard. While IEEE 802.1X provides robust port-level authentication, it does not inspect or control the payload of authenticated devices. WPA3 secures the wireless transmission but does nothing to prevent the device from initiating the telemetry connection.
The Edge Filtering Imperative
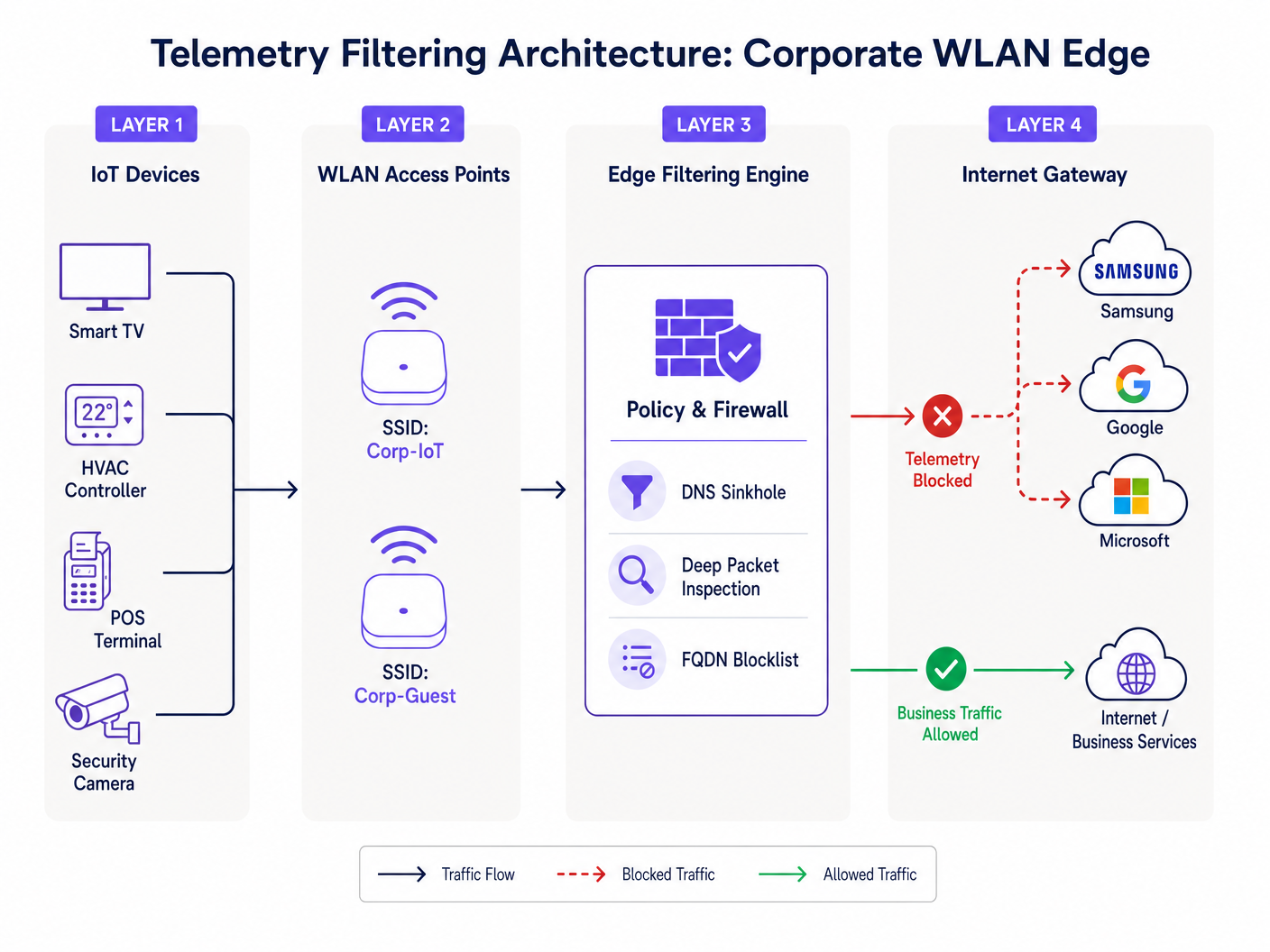
To address this, organisations must implement filtering at the network edge. This involves a multi-layered approach: DNS sinkholing to intercept resolution requests for known telemetry domains, and Deep Packet Inspection (DPI) combined with FQDN blocklists to catch hardcoded IP communications. This architecture ensures that only authorised business traffic traverses the internet gateway, as detailed in our guide on Improving WiFi Speeds by Blocking Ad Networks at the Edge .
Implementation Guide
Deploying a robust telemetry filtering architecture requires a systematic approach to avoid disrupting legitimate operational traffic.
Phase 1: Network Segmentation
The foundational step is strict VLAN segmentation. IoT devices must never reside on the same subnet as corporate users, guest networks, or PCI-scoped systems. Create dedicated IoT VLANs with strict access control lists (ACLs) that deny inter-VLAN routing by default.
Phase 2: Traffic Auditing and Baselining
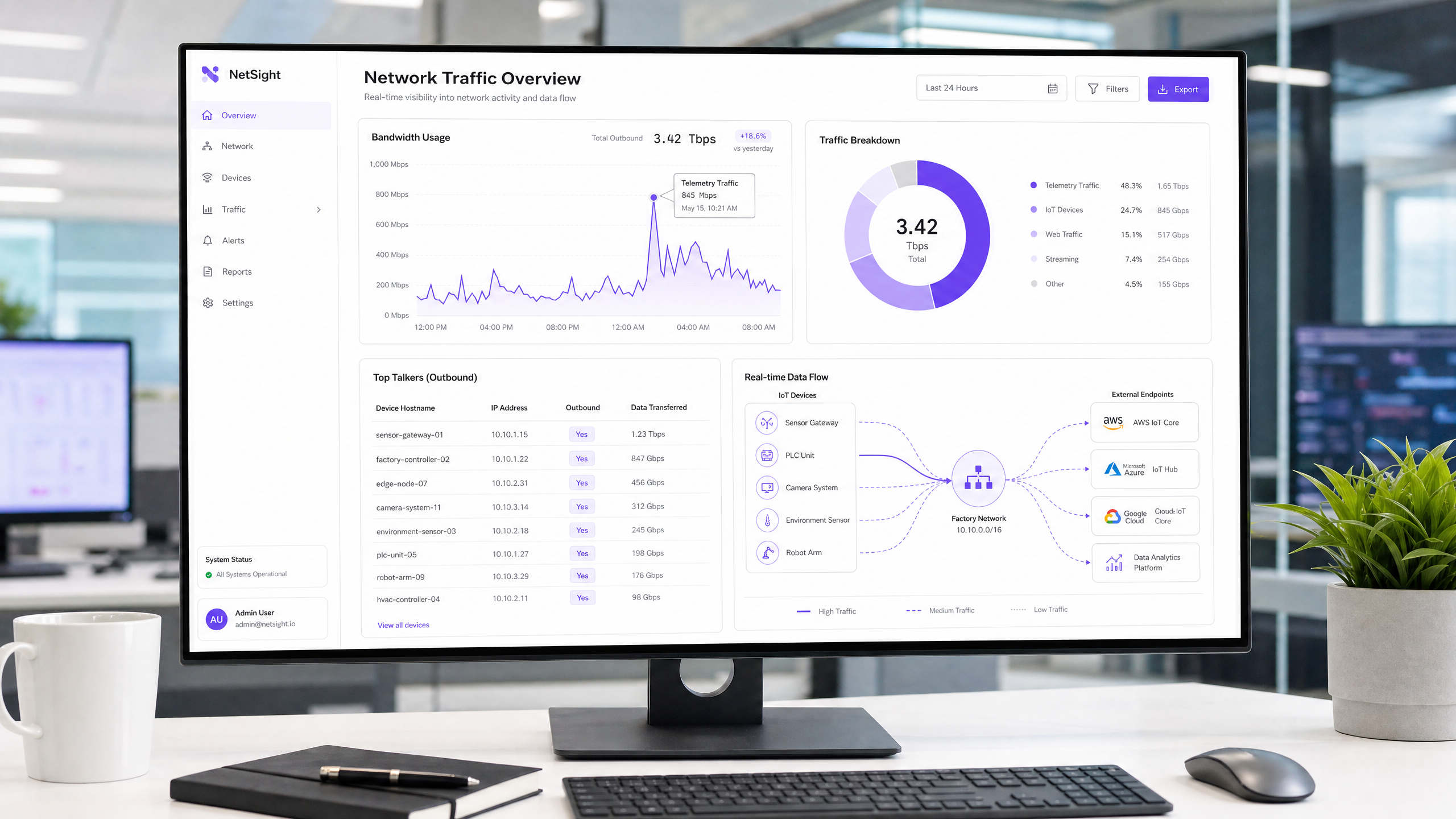
Before implementing blocks, establish a traffic baseline. Deploy flow analysis tools (NetFlow/sFlow) or utilise a comprehensive WiFi Analytics platform to monitor outbound connections. Identify the top talkers and map their destination endpoints. This audit will reveal the true scale of the telemetry problem.
Phase 3: DNS Sinkholing
Configure the DHCP scope for the IoT VLAN to assign an internal, policy-enforcing DNS resolver. Implement category-based blocking for known telemetry and diagnostic endpoints. Utilise community-curated blocklists or commercial threat intelligence feeds. Monitor the logs for 72 hours in a 'report-only' mode to identify potential false positives before enforcing the blocks.
Phase 4: Egress Filtering and DPI
For devices that bypass DNS using hardcoded IP addresses, implement egress filtering at the perimeter firewall. Configure DPI rules to identify and drop telemetry signatures. Ensure these rules are updated regularly to account for changes in vendor infrastructure.
Best Practices
- Adopt a Default-Deny Posture for IoT: By default, IoT VLANs should have no internet access. Only explicitly whitelist the FQDNs and ports required for the device's core functionality (e.g., NTP, specific API endpoints).
- Implement Rate Limiting: Even authorised traffic should be subject to bandwidth shaping. Apply QoS policies to cap the maximum throughput available to IoT segments, ensuring they cannot saturate the uplink during mass firmware updates.
- Regular Blocklist Maintenance: Telemetry endpoints evolve. Automate the ingestion of updated FQDN blocklists into your edge filtering engine to maintain efficacy.
- Monitor Guest Networks: Apply similar filtering principles to the guest network. Whilst you cannot control guest devices, you can prevent their telemetry from degrading the shared experience.
Troubleshooting & Risk Mitigation
The most significant risk in telemetry filtering is over-blocking, which can impair device functionality. For example, blocking a vendor's CDN might inadvertently block critical security updates.
- Symptom: Devices show offline status in the management console.
- Mitigation: Review DNS logs for blocked queries from the affected device IP. Temporarily whitelist the blocked domain and verify if functionality is restored. Often, vendors use distinct subdomains for telemetry versus management (e.g.,
telemetry.vendor.comvsapi.vendor.com).
Another common failure mode is incomplete segmentation, where a management VLAN inadvertently bridges the IoT segment to the corporate network. Regular penetration testing and VLAN audits are essential to verify isolation.
ROI & Business Impact
Implementing telemetry filtering yields immediate and measurable returns.
- Bandwidth Recovery: Organisations typically see a 15-30% reduction in outbound WAN utilisation, deferring costly bandwidth upgrades.
- Improved User Experience: Reclaimed bandwidth directly translates to faster, more reliable connectivity for guests and employees, improving satisfaction scores in Hospitality and Retail environments.
- Risk Reduction: Eliminating unauthorised outbound connections significantly reduces the attack surface and simplifies compliance audits, mitigating the risk of regulatory fines.
For public sector deployments, where budgets are tight and scrutiny is high, these efficiencies are critical for delivering reliable services, aligning with initiatives to drive digital inclusion as discussed in our recent announcement: Purple Appoints Iain Fox as VP Growth – Public Sector to Drive Digital Inclusion and Smart City Innovation .
Listen to the Briefing
For a deeper dive into the architectural considerations, listen to our 10-minute technical briefing:
Key Definitions
Telemetry Data
Automated transmission of operational, diagnostic, or usage data from a connected device back to its manufacturer or a third-party cloud service.
Often transmitted without explicit IT authorization, consuming bandwidth and creating compliance blind spots.
DNS Sinkhole
A DNS server configured to hand out incorrect IP addresses (often 0.0.0.0) for specific domain names, effectively preventing devices from connecting to those domains.
Used as a lightweight, highly effective method to block known telemetry and tracking endpoints at the network edge.
Deep Packet Inspection (DPI)
Advanced network packet filtering that examines the data part (and possibly the header) of a packet as it passes an inspection point, searching for protocol non-compliance, viruses, spam, intrusions, or defined criteria.
Necessary for identifying and blocking telemetry traffic that uses hardcoded IP addresses or non-standard ports, bypassing DNS controls.
FQDN Blocklist
A list of Fully Qualified Domain Names (e.g., telemetry.vendor.com) that are explicitly denied access through the network gateway or DNS resolver.
More precise than IP blocking, as cloud-hosted telemetry endpoints frequently change IP addresses but maintain consistent domain names.
VLAN Segmentation
The practice of dividing a physical network into multiple logical networks to isolate traffic, improve performance, and enhance security.
The critical first step in managing IoT devices, ensuring their telemetry traffic cannot traverse corporate or PCI-scoped network segments.
Egress Filtering
The practice of monitoring and potentially restricting the flow of information outbound from one network to another, typically the internet.
Crucial for preventing unauthorized data exfiltration and enforcing the 'Default-Deny' posture for IoT segments.
PCI DSS Scope
All system components, people, and processes that are included in or connected to the Cardholder Data Environment (CDE).
Uncontrolled telemetry from devices on the same network segment as payment terminals can inadvertently bring those devices into audit scope.
IEEE 802.1X
An IEEE Standard for port-based Network Access Control (PNAC), providing an authentication mechanism to devices wishing to attach to a LAN or WLAN.
While it secures network entry, it does not inspect or control the telemetry payloads sent by authenticated devices.
Worked Examples
A 400-room resort is experiencing severe network congestion every morning between 2:00 AM and 4:00 AM, impacting early-rising guests and back-office operations. The network team suspects the recently installed smart TVs in every room are responsible. How should they diagnose and resolve this?
- Diagnosis: Deploy a NetFlow collector on the core switch to analyze traffic during the congestion window. The analysis reveals that all 400 TVs are simultaneously downloading firmware updates and uploading aggregated daily usage telemetry to the manufacturer's CDN. 2. Resolution: First, ensure the TVs are on a dedicated IoT VLAN. Second, implement a QoS policy on the firewall to rate-limit outbound and inbound traffic for the IoT VLAN to 10% of the total WAN link capacity. Third, implement DNS sinkholing to block the specific FQDNs used for telemetry upload, while allowing the FQDNs used for firmware updates. Finally, stagger the update windows if the vendor management console permits.
A large retail chain with 200 locations uses a mix of legacy and modern POS systems. During a PCI DSS audit, the assessor notes that several modern POS terminals are generating outbound HTTPS traffic to unknown cloud endpoints. How should the network architect remediate this finding?
- Immediate Containment: Verify that the POS terminals are on a strictly isolated CDE (Cardholder Data Environment) VLAN. 2. Traffic Analysis: Perform packet captures (PCAP) on the egress interface for the CDE VLAN. Identify the destination IP addresses and attempt reverse DNS lookups to determine the vendor. 3. Policy Enforcement: Implement a 'Default-Deny' egress rule on the firewall for the CDE VLAN. Only explicitly whitelist the IP addresses and ports required for payment processing and authorized management traffic. 4. Documentation: Document the whitelisted endpoints and the business justification for each in the firewall rule base, providing this documentation to the PCI assessor.
Practice Questions
Q1. You are deploying a new fleet of smart HVAC controllers across a corporate campus. The vendor states that the controllers require internet access to report diagnostic data to their cloud platform for warranty support. How do you integrate these devices securely?
Hint: Consider the principle of least privilege and how to balance operational requirements with security controls.
View model answer
- Place the HVAC controllers on a dedicated, isolated IoT VLAN. 2. Request the specific FQDNs and ports required for the diagnostic reporting from the vendor. 3. Configure the perimeter firewall with a default-deny egress rule for the IoT VLAN. 4. Create an explicit allow rule only for the vendor-provided FQDNs and ports. 5. Implement rate limiting on the VLAN to prevent the controllers from consuming excessive bandwidth.
Q2. During a routine log review, you notice a significant volume of DNS requests from the IoT VLAN being blocked by the DNS sinkhole. However, the operations team reports that the digital signage displays are no longer updating their content. What is the likely cause and remediation?
Hint: Think about how vendors often structure their cloud services and the risks of over-blocking.
View model answer
The likely cause is over-blocking. The vendor is probably using the same domain (or a closely related subdomain) for both telemetry reporting and content delivery. Remediation: 1. Identify the specific blocked domain in the DNS logs. 2. Temporarily whitelist the domain. 3. Use packet capture to analyze the traffic to that domain. 4. If possible, use DPI on the firewall to block the specific telemetry URI paths while allowing the content update paths, or work with the vendor to identify distinct FQDNs for each function.
Q3. A stadium IT director wants to implement telemetry filtering but is concerned about the processing overhead on the core firewall during game days when 50,000 fans are connected. What architecture provides the most efficient filtering?
Hint: Which filtering method consumes the least CPU cycles on the firewall?
View model answer
The most efficient approach is to rely heavily on DNS sinkholing for the bulk of the filtering. By configuring the DHCP servers to point client devices to an internal DNS resolver that blocks known telemetry domains, the traffic is dropped before a connection is even attempted, saving firewall state table entries and DPI processing cycles. The firewall should only be used as a secondary measure for hardcoded IPs or highly specific block rules.