Managing IoT Device Security with NAC and MPSK
This technical guide details how enterprise venues can secure headless IoT devices using Multiple Pre-Shared Key (MPSK) architecture and Network Access Control (NAC). It provides actionable implementation steps for achieving micro-segmentation, containing security blast radii, and maintaining compliance without sacrificing scalability.
Listen to this guide
View podcast transcript
- Executive Summary
- Technical Deep-Dive
- The Limitation of Traditional PSK and 802.1X
- The MPSK and NAC Architecture
- Audio Briefing
- Implementation Guide
- Step 1: Infrastructure Readiness Assessment
- Step 2: Define Micro-Segmentation Policies
- Step 3: Device Profiling and Key Generation
- Step 4: Integration with Analytics and Guest Networks
- Best Practices
- Troubleshooting & Risk Mitigation
- Common Failure Modes
- ROI & Business Impact

Executive Summary
Enterprise networks across Retail , Hospitality , and Transport venues are experiencing an explosion of headless IoT devices—from environmental sensors and smart thermostats to IP cameras and point-of-sale terminals. The fundamental challenge for IT managers and network architects is that the vast majority of these devices do not support enterprise-grade IEEE 802.1X authentication.
Historically, organisations have fallen back on a single, global Pre-Shared Key (PSK) for their entire IoT SSID. This creates an unacceptable security posture where a single compromised device or leaked password breaches the entire IoT network segment.
This technical reference guide details how deploying Multiple Pre-Shared Key (MPSK) architecture in conjunction with a robust Network Access Control (NAC) policy engine solves this challenge. By issuing unique credentials per device and leveraging dynamic VLAN assignment, network teams can achieve micro-segmentation, contain blast radii, and maintain strict compliance (such as PCI DSS) without sacrificing the scalability required for thousands of endpoints. When integrated with platforms like Purple's Guest WiFi and WiFi Analytics , this approach ensures seamless, secure, and highly visible network operations.
Technical Deep-Dive
The Limitation of Traditional PSK and 802.1X
In a standard enterprise environment, devices authenticate via IEEE 802.1X using certificates (EAP-TLS) or credentials (PEAP). However, headless IoT devices typically lack the supplicant software required for 802.1X. The fallback has traditionally been WPA2/WPA3-Personal using a single PSK.
The operational reality of a global PSK is severe:
- Zero Segmentation: All devices on the PSK share the same broadcast domain unless manually mapped by MAC address, which is operationally unsustainable.
- High Blast Radius: A compromised smart bulb provides lateral movement access to the entire VLAN.
- Key Rotation Nightmare: Revoking access for one compromised device requires changing the global PSK and manually updating every other device on the network.
The MPSK and NAC Architecture
MPSK (also referred to by vendors as Identity PSK or iPSK) fundamentally alters this paradigm. It allows a single SSID to accept thousands of unique passwords. The intelligence, however, lies in the integration with a NAC or RADIUS server.
When a device associates with the MPSK SSID, the wireless LAN controller (WLC) forwards the authentication request to the NAC. The NAC engine evaluates the specific password used, correlates it with the device's identity (MAC address, profiling data), and returns a RADIUS Access-Accept message containing specific attributes—most notably, the VLAN ID and Access Control List (ACL) policies.
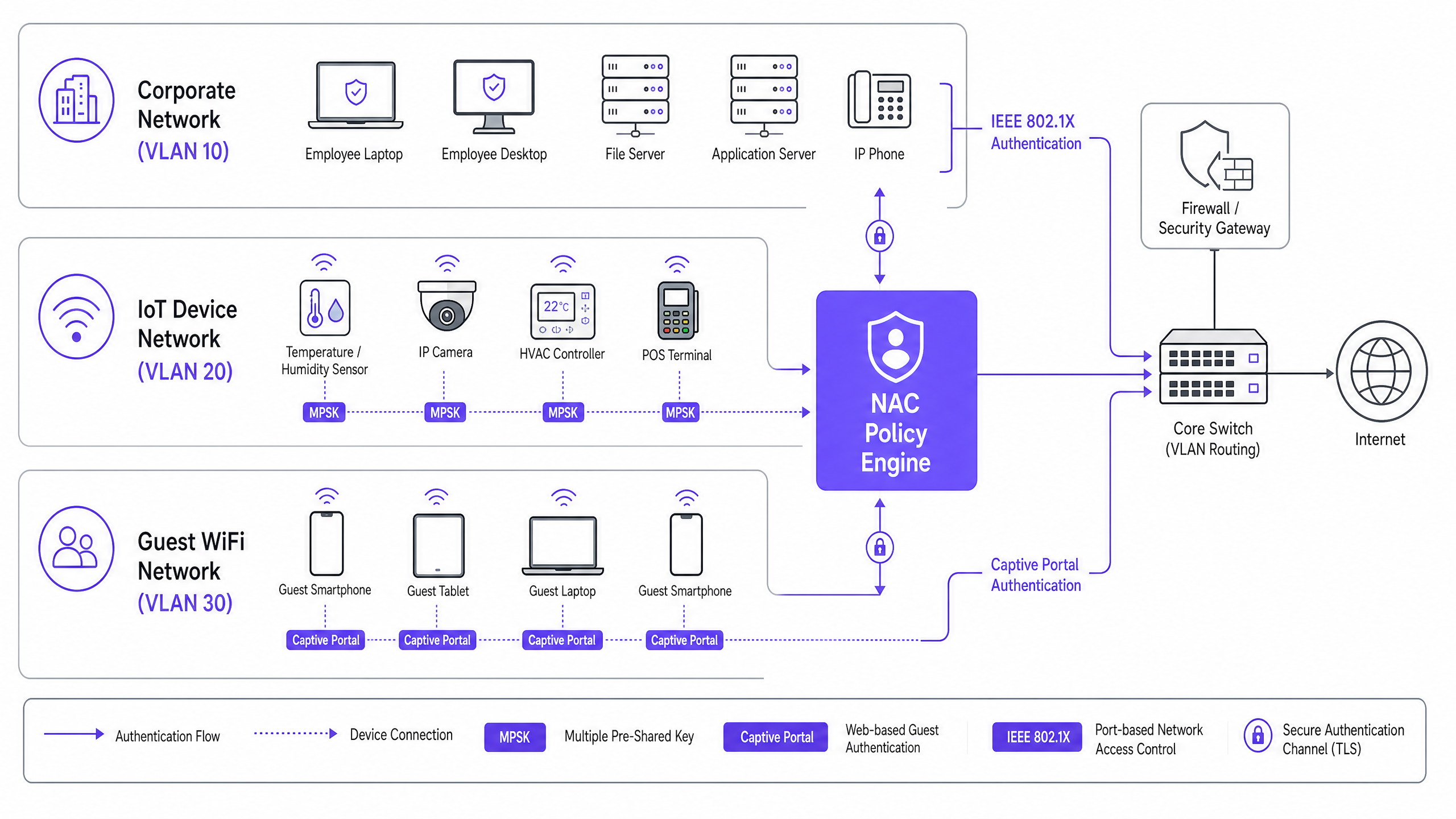
This architecture enables Dynamic VLAN Assignment. A smart thermostat and an IP camera can connect to the exact same SSID using different passwords, and the network infrastructure will drop the thermostat into VLAN 50 (restricted to cloud gateway access) and the camera into VLAN 40 (restricted to the local NVR server).

Audio Briefing
Listen to our senior consultant's technical briefing on this architecture:
Implementation Guide
Deploying MPSK with NAC requires careful planning to ensure scalability and security. Follow these steps for a successful rollout.
Step 1: Infrastructure Readiness Assessment
Ensure your wireless controllers and access points support MPSK/iPSK. Most modern enterprise networking vendors (Cisco, Aruba, Meraki, Ruckus) support this natively, provided firmware is up to date. Verify that your NAC solution can handle the anticipated load of RADIUS requests and supports dynamic VLAN assignment based on password matching.
Step 2: Define Micro-Segmentation Policies
Before generating a single key, define your VLAN architecture. Group IoT devices by function and required access.
- VLAN 40 (Security Cameras): Allow traffic only to the local NVR IP and specific NTP servers. Block internet access.
- VLAN 50 (Environmental Sensors): Allow outbound HTTPS traffic to specific vendor cloud endpoints. Block inter-VLAN routing.
- VLAN 60 (Point of Sale): Strict PCI DSS compliance. Deny all inbound traffic; allow outbound only to payment gateways.
Step 3: Device Profiling and Key Generation
Do not manually generate keys. Use the NAC's API or a self-service portal to generate unique keys per device. Bind each key to the device's MAC address. This ensures that even if an MPSK is extracted from a thermostat, it cannot be used by a rogue laptop spoofing the network.
Step 4: Integration with Analytics and Guest Networks
While IoT networks are isolated, the overarching management should be unified. Ensure your NAC deployment aligns with your broader network strategy, including Guest WiFi provisioning. Platforms that provide WiFi Analytics can offer valuable insights into device density and network health across all segments. For more on network fundamentals, review Wi Fi Frequencies: A Guide to Wi-Fi Frequencies in 2026 .
Best Practices
- Enforce MAC Binding: Always bind the MPSK to the specific MAC address of the device. If a different MAC attempts to use the key, the NAC must reject the authentication.
- Implement DHCP Fingerprinting: Use DHCP profiling within the NAC to verify device types. If an MPSK assigned to a 'Smart TV' is suddenly used by a device fingerprinting as 'Windows 11', trigger an automatic quarantine.
- Automate Lifecycle Management: Integrate MPSK generation with your IT Service Management (ITSM) platform. When a device is decommissioned in the asset register, the corresponding MPSK should be automatically revoked via API.
- Regular Auditing: Conduct quarterly audits of active MPSKs against your asset inventory to identify and prune orphaned keys.
Troubleshooting & Risk Mitigation
Common Failure Modes
- RADIUS Timeout Issues: If the NAC engine is overwhelmed or latency is high, headless devices may time out and fail to connect.
- Mitigation: Ensure high availability and localized RADIUS proxies if dealing with highly distributed environments like large retail chains.
- MAC Spoofing: An attacker clones the MAC address of an authorized IoT device and extracts its MPSK.
- Mitigation: Rely on deep packet inspection and behavioural profiling. If the "thermostat" suddenly starts scanning the network on port 22 (SSH), the NAC or IDS should immediately isolate the port.
- Roaming Disconnects: Some poorly designed IoT devices drop connection when roaming between APs using MPSK.
- Mitigation: Adjust minimum basic rates and ensure proper RF cell overlap. For deeper wireless design considerations, see BLE Low Energy Explained for Enterprise .
ROI & Business Impact
Transitioning to an MPSK/NAC architecture delivers measurable business value:
- Reduced Operational Expenditure (OpEx): Eliminates the hundreds of hours IT teams spend manually updating global PSKs when a single device is compromised or replaced.
- Compliance Assurance: For retail and hospitality venues, strict micro-segmentation is a core requirement of PCI DSS. MPSK provides a provable, auditable mechanism for isolating payment terminals, avoiding costly compliance fines.
- Risk Mitigation: By containing the blast radius of any compromised device to its specific micro-segment, the potential financial and reputational damage of a lateral-movement ransomware attack is drastically reduced.
- Future-Proofing: As enterprise networks evolve, integrating IoT security with broader WAN strategies becomes critical. For context on wider network architecture, refer to SD WAN vs MPLS: The 2026 Enterprise Network Guide and The Role of SCEP and NAC in Modern MDM Infrastructure .
Key Definitions
MPSK (Multiple Pre-Shared Key)
A wireless security feature allowing multiple unique passwords to be used on a single SSID, with each password capable of triggering different network policies.
Crucial for securing headless IoT devices that cannot support enterprise 802.1X authentication.
NAC (Network Access Control)
A security solution that enforces policy on devices attempting to access the network, ensuring they meet security requirements before granting access.
Acts as the intelligence engine behind MPSK, determining VLAN assignment based on the password used.
Dynamic VLAN Assignment
The process where a network switch or wireless controller assigns a device to a specific VLAN based on authentication credentials rather than the physical port or SSID.
Enables micro-segmentation of IoT devices broadcasting on the same wireless network.
Blast Radius
The extent of damage or lateral movement an attacker can achieve after compromising a single device or system.
MPSK and NAC drastically reduce the blast radius by isolating compromised IoT devices within strict micro-segments.
Headless Device
A computing device, typical in IoT deployments, that operates without a monitor, keyboard, or user interface.
These devices cannot prompt a user for credentials, making traditional 802.1X authentication impossible.
MAC Binding
A security control that restricts the use of a specific credential (like an MPSK) to a single, authorized MAC address.
Prevents an attacker from stealing an MPSK from a smart bulb and using it on a malicious laptop.
DHCP Fingerprinting
A profiling technique used by NAC systems to identify a device's operating system and type based on the specific sequence of DHCP options it requests.
Used to verify that a device connecting with an IoT MPSK is actually an IoT device and not a spoofed endpoint.
Micro-segmentation
A security technique that divides the network into granular, isolated zones to maintain strict access control and limit lateral movement.
The primary architectural goal of deploying MPSK and NAC for IoT security.
Worked Examples
A 300-room hotel is deploying new smart TVs, IP-based door locks, and environmental sensors. The current infrastructure uses a single global PSK for all non-corporate devices. How should the network architect redesign this for optimal security and manageability?
The architect should deploy an MPSK SSID ('Hotel-IoT'). The NAC policy engine must be configured with three distinct device profiles. Smart TVs receive unique MPSKs and are dynamically assigned to VLAN 100 (Internet only, client isolation enabled). Door locks receive unique MPSKs, are bound to their specific MAC addresses, and assigned to VLAN 110 (restricted access only to the local security server). Sensors receive unique MPSKs and are assigned to VLAN 120 (access only to the HVAC management cloud). All keys are generated via API during device onboarding.
A large retail chain needs to connect hundreds of wireless Point-of-Sale (POS) scanners and digital signage displays across 50 locations. How can they ensure PCI DSS compliance while minimizing IT overhead?
Implement a centralized NAC architecture with MPSK. The POS scanners are issued unique MPSKs and profiled into a highly restricted PCI-compliant VLAN that denies all lateral traffic and only permits outbound connections to the payment processing gateway. Digital signage displays use separate MPSKs and are dropped into a different VLAN with internet-only access for content updates. Key lifecycle management is integrated with the central asset management system.
Practice Questions
Q1. A stadium IT team needs to deploy 200 new wireless point-of-sale terminals. They plan to use MPSK. To ensure maximum security, what two profiling checks must the NAC perform before assigning the POS terminal to the secure VLAN?
Hint: Consider how to prevent a stolen MPSK from being used on a non-POS device.
View model answer
The NAC must perform MAC Binding (verifying the specific MPSK is being used by the authorized MAC address) and DHCP Fingerprinting (verifying the device requesting an IP address exhibits the characteristics of the expected POS terminal OS, not a generic laptop or smartphone).
Q2. During an audit, it is discovered that an MPSK assigned to a smart thermostat was successfully used by a contractor's laptop to gain network access. The NAC assigned the laptop to the thermostat's VLAN. What configuration failure allowed this?
Hint: Think about the relationship between the key and the device identity.
View model answer
The primary failure was a lack of MAC Binding. The MPSK was not restricted to the specific MAC address of the thermostat. Additionally, the NAC failed to enforce device profiling (e.g., DHCP fingerprinting), which would have identified the contractor's laptop as an anomalous device type for that specific key and VLAN.
Q3. A retail chain is migrating from a global PSK to MPSK. They have 5,000 legacy barcode scanners that support WPA2-Personal but cannot be updated to support newer protocols. Can MPSK be used to secure these devices, and if so, how?
Hint: Consider the client-side requirements for MPSK.
View model answer
Yes, MPSK can be used. From the perspective of the client device (the barcode scanner), MPSK is identical to standard WPA2-Personal PSK. The intelligence and differentiation happen entirely on the infrastructure side (WLC and NAC). The scanners simply need to be configured with their newly assigned, unique passwords.