What Is First-Party Data and Why Does It Matter for Businesses?
This guide provides a definitive technical reference on first-party data — what it is, how it differs from second- and third-party data, and why the deprecation of third-party cookies and tightening privacy regulation make a first-party data strategy non-negotiable for venue operators. It covers the architecture of guest WiFi as a compliant, high-yield collection mechanism, with implementation guidance for hospitality, retail, events, and public-sector environments, and maps directly to Purple's guest WiFi and analytics platform.
🎧 Listen to this Guide
View Transcript
- Executive Summary
- Technical Deep-Dive
- Defining First-Party Data: A Precise Taxonomy
- Why the Third-Party Data Model Is Failing
- Guest WiFi as a First-Party Data Collection Architecture
- Implementation Guide
- Phase 1: Infrastructure Assessment and Consent Framework Design (Weeks 1–4)
- Phase 2: Platform Deployment and Integration (Weeks 5–10)
- Phase 3: Data Quality and Governance (Ongoing)
- Best Practices
- Troubleshooting & Risk Mitigation
- ROI & Business Impact
- Measuring the Value of a First-Party Data Asset
- Case Study 1: Regional Hotel Chain — Hospitality
- Case Study 2: Retail Estate — Multi-Site Retail
- Expected Outcomes by Venue Type

Executive Summary
The third-party data model is structurally broken. Google's deprecation of third-party cookies in Chrome, Apple's App Tracking Transparency framework, and the enforcement trajectory of GDPR and the UK Data Protection Act 2018 have collectively dismantled the data infrastructure that most marketing and analytics teams relied on for the past decade. Organisations that have not yet built a first-party data strategy are operating on borrowed time.
First-party data — collected directly from your guests and customers, with explicit consent, through your own channels — is more accurate, more durable, and more compliant than any alternative. For physical venue operators in hospitality , retail , transport , and healthcare , the guest WiFi network is one of the most efficient first-party data collection mechanisms available. Every authenticated connection is a consented data capture event that builds a persistent, actionable guest profile.
This guide covers the technical architecture of first-party data collection via Guest WiFi , the compliance framework required for GDPR-safe deployment, implementation patterns across venue types, and the ROI case for investing in WiFi Analytics as the activation layer for your first-party dataset.
Technical Deep-Dive
Defining First-Party Data: A Precise Taxonomy
The industry uses "first-party data" loosely, but for architecture and compliance purposes, precision matters. The data landscape divides into three tiers:
| Data Type | Source | Consent Trail | Compliance Risk | Durability |
|---|---|---|---|---|
| First-party | Collected directly by your organisation from individuals with a direct relationship | Full, auditable, owned by you | Low | High — not subject to third-party policy changes |
| Second-party | Another organisation's first-party data accessed via direct partnership | Partial — depends on partner's consent framework | Medium | Medium — subject to partnership terms |
| Third-party | Aggregated by data brokers from multiple sources | Weak or absent — no direct relationship | High — increasingly untenable under GDPR | Low — cookie deprecation, platform restrictions |
Within first-party data, there are four distinct data classes that a well-architected collection system should capture:
Identity data encompasses the core identifiers collected at authentication: name, email address, phone number, and demographic attributes voluntarily provided during registration. This is the anchor that ties all subsequent behavioural observations to a known individual.
Behavioural data is generated passively through network interaction: connection timestamps, session duration, visit frequency, dwell time by zone, device type, and operating system. For venue operators, this is often the most operationally valuable data class because it reveals how guests actually use your space, not just how they describe their preferences.
Transactional data flows from point-of-sale systems, booking engines, loyalty programme interactions, and e-commerce platforms. When integrated with WiFi-derived identity and behavioural data, it enables true attribution — connecting physical presence to commercial outcome.
Declared preference data is what guests tell you directly through surveys, preference centres, and registration forms. It is the highest-quality signal for personalisation but requires active guest participation to collect.
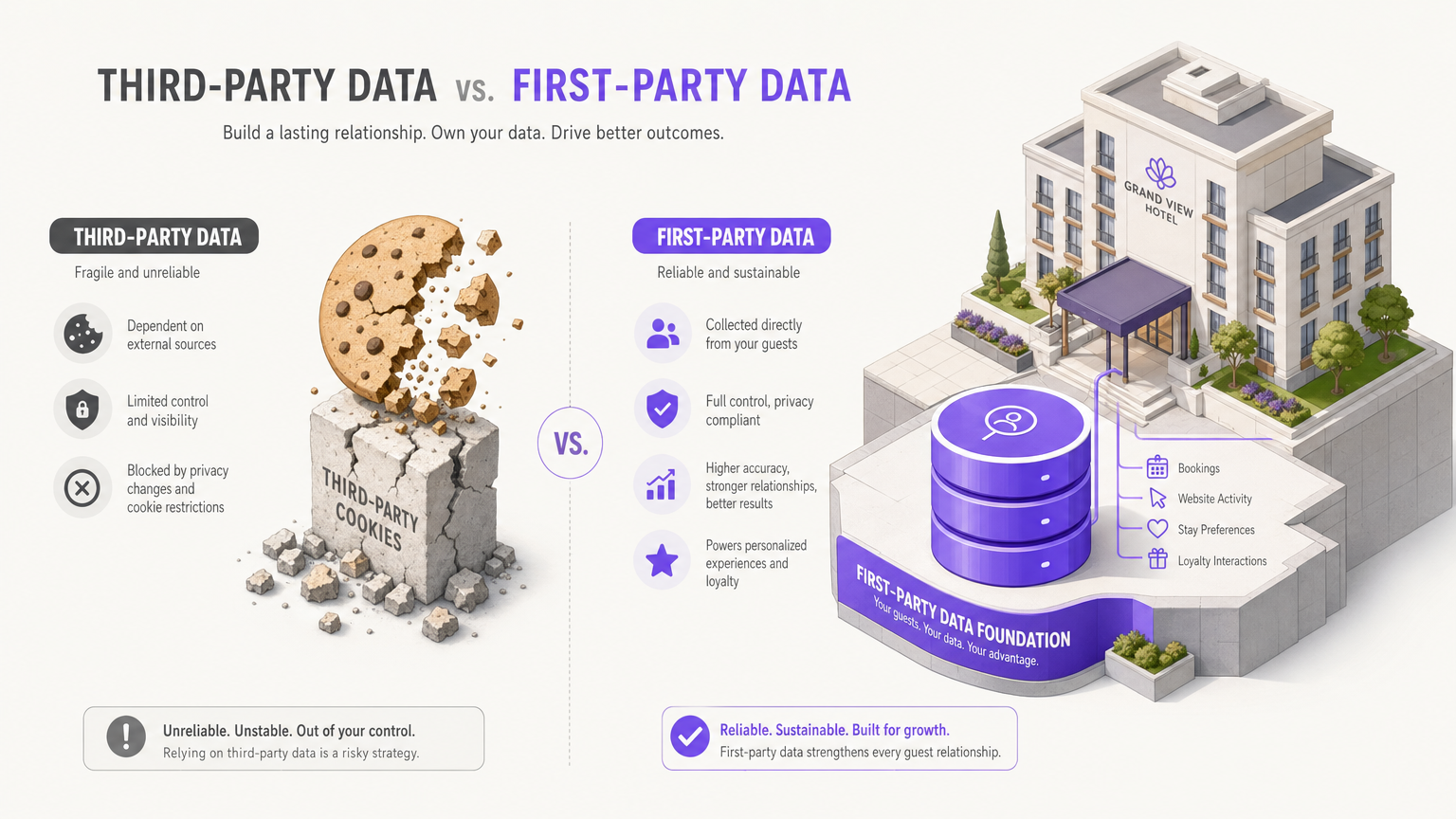
Why the Third-Party Data Model Is Failing
The structural collapse of third-party data is not a single event — it is a convergence of regulatory, technical, and commercial pressures that have been building for several years.
On the regulatory side, GDPR's requirement for freely given, specific, informed, and unambiguous consent has made the implicit data collection practices of the third-party ecosystem legally precarious. The UK Information Commissioner's Office has issued substantial fines for consent violations, and enforcement is intensifying. The ePrivacy Directive's requirements for cookie consent have further eroded the practical utility of third-party tracking.
On the technical side, Apple's Intelligent Tracking Prevention and App Tracking Transparency framework have significantly degraded the accuracy of cross-site tracking on iOS devices. Safari's aggressive cookie partitioning means that third-party cookies have an effective lifespan of seven days for some use cases. Android's Privacy Sandbox initiative is following a similar trajectory.
For venue operators, the practical implication is straightforward: the audience data you purchase from third-party brokers is becoming less accurate, less complete, and more legally exposed with each passing quarter. The organisations that will win the next decade are those building proprietary first-party datasets now.
Guest WiFi as a First-Party Data Collection Architecture
The guest WiFi network is uniquely positioned as a first-party data collection mechanism for physical venues. Unlike a mobile app — which requires download, installation, and active engagement — WiFi connectivity is a utility that guests actively seek. The connection event is the natural moment of consent capture.
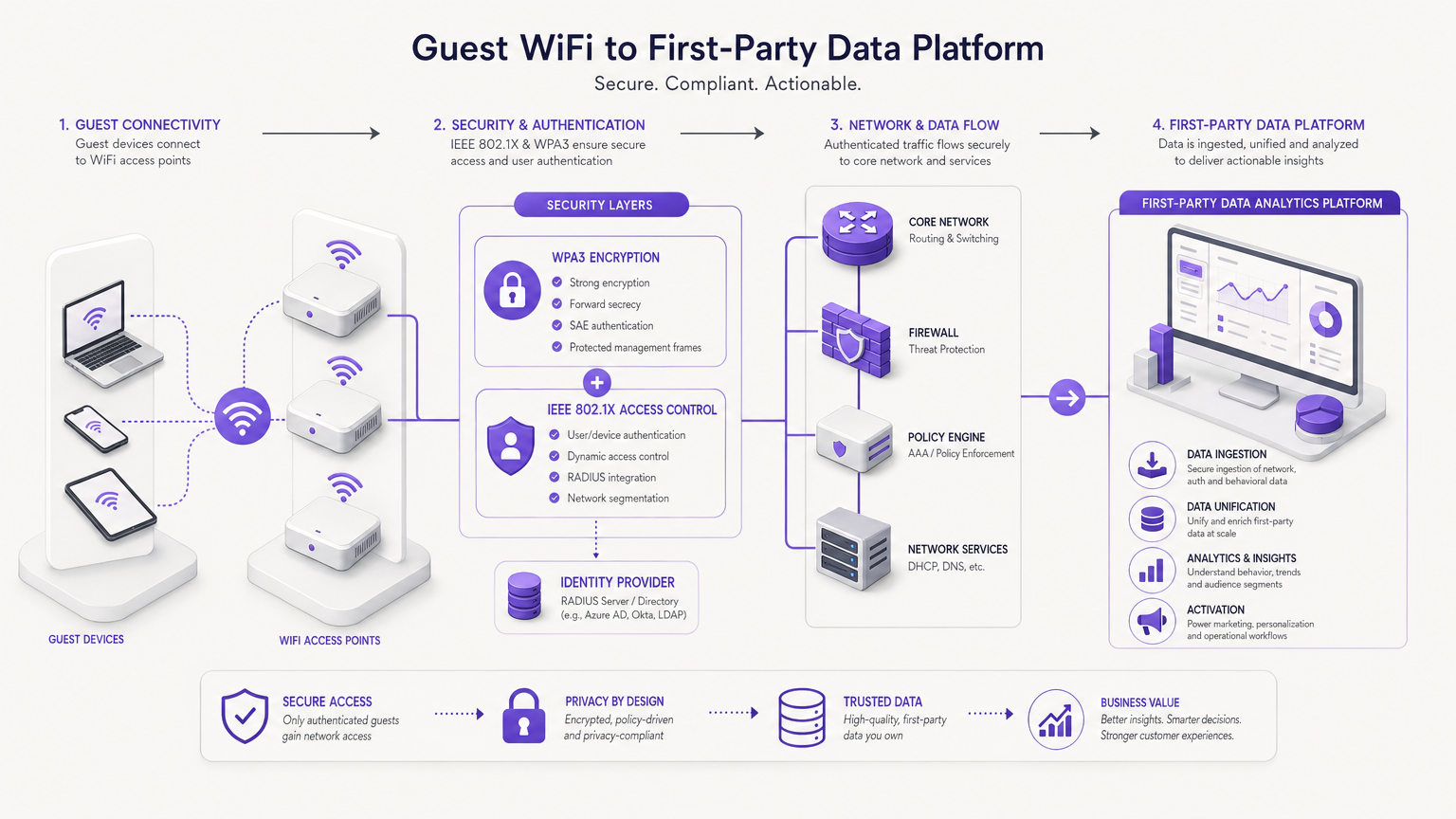
The technical architecture of a compliant WiFi first-party data collection system operates across four layers:
Layer 1 — Network Access Control: IEEE 802.1X provides port-based network access control, ensuring that devices cannot access network resources until they have completed the authentication process. This is the technical gate that makes authenticated data collection possible. WPA3 encryption with Simultaneous Authentication of Equals (SAE) ensures that session data in transit is protected with forward secrecy, meaning that even if a session key is compromised, historical session data cannot be decrypted.
Layer 2 — Captive Portal and Consent Capture: The captive portal — or splash page — is the interface through which guests authenticate and provide consent. A properly configured captive portal presents a clear privacy notice, captures explicit consent for specific data uses (marketing communications, analytics, third-party sharing), records the consent timestamp and privacy notice version, and provides a clear mechanism for guests to withdraw consent. Purple's platform handles this consent workflow natively, with consent records stored in an auditable log.
Layer 3 — Identity Resolution and MAC Address Handling: Modern iOS and Android devices randomise their MAC address by default as a privacy protection measure. This means the device identifier visible at the network layer may change between visits, breaking persistent visitor identification if MAC address is used as the primary key. The correct architectural response is to anchor persistent identification to the authenticated identity — the email address or phone number provided at login — rather than the device identifier. Once a guest authenticates, their device's randomised MAC is mapped to their persistent profile, and subsequent connections from the same device are recognised through the authentication credential rather than the hardware identifier.
Layer 4 — Data Ingestion and Unification: Connection events, session data, and location signals from access point triangulation are ingested into the analytics platform and normalised against the guest profile. For multi-venue operators, this layer is where cross-location intelligence is built. A guest recognised at your London venue on Monday and your Edinburgh venue on Thursday is a single profile with two behavioural events, not two separate anonymous visitors.
For organisations interested in extending location intelligence beyond basic WiFi coverage mapping, the Indoor Positioning System: UWB, BLE, & WiFi Guide provides a detailed technical reference on combining WiFi with Ultra-Wideband and Bluetooth Low Energy for sub-metre positioning accuracy.
Implementation Guide
Phase 1: Infrastructure Assessment and Consent Framework Design (Weeks 1–4)
Before deploying any data collection capability, the compliance and legal framework must be in place. Engage your Data Protection Officer or legal counsel to review and approve the privacy notice language for your captive portal. The notice must specify: the categories of data being collected, the legal basis for processing (typically legitimate interests for analytics, explicit consent for marketing), the retention periods for each data category, the third parties with whom data may be shared, and the guest's rights under GDPR including the right to access, rectification, erasure, and portability.
Concurrently, conduct an infrastructure audit. Document your existing access point estate: vendor, firmware version, VLAN configuration, and RADIUS server integration status. Identify gaps in coverage that would result in incomplete data capture. For retail environments, ensure that your access point placement provides sufficient density for meaningful dwell time measurement — a general rule of thumb is one access point per 1,000 to 1,500 square metres for analytics purposes, which may be denser than your pure connectivity requirements.
Phase 2: Platform Deployment and Integration (Weeks 5–10)
Deploy the captive portal and configure the authentication workflow. Purple supports multiple authentication methods — email registration, social login via OAuth (Google, Facebook, Apple), phone number verification via SMS OTP, and loyalty programme integration. The choice of authentication method directly affects your data capture rate and the richness of the identity data collected. Email registration provides the most durable identifier for CRM integration. Social login provides higher conversion rates but may return limited profile data depending on the platform's API permissions.
Configure your VLAN segmentation to ensure that guest WiFi traffic is isolated from corporate and payment card networks. This is a mandatory PCI DSS requirement and a security best practice regardless of payment card scope. The guest VLAN should route through a dedicated internet breakout with appropriate content filtering and bandwidth management policies.
Integrate the WiFi analytics platform with your downstream systems: CRM for guest profile synchronisation, email marketing platform for campaign activation, and loyalty system for points and rewards integration. Purple provides pre-built connectors for major CRM and marketing automation platforms, reducing integration development time significantly.
Phase 3: Data Quality and Governance (Ongoing)
Establish data quality monitoring from day one. Key metrics to track include: authentication rate (the percentage of connected devices that complete the login flow), data completeness (the percentage of profiles with a valid email address), consent rate (the percentage of authenticated guests who consent to marketing communications), and return visitor recognition rate (the percentage of return visits where the guest is successfully matched to an existing profile).
Implement data retention automation. Configure your platform to automatically purge session logs after your defined retention period and to honour deletion requests within the 30-day window required by GDPR. Maintain an audit log of all data subject access requests and deletion actions.
For guidance on activating your first-party dataset to improve customer experience, the guide Wie man WiFi Analytics nutzt, um die Kundenerfahrung zu verbessern and its Spanish equivalent Cómo utilizar WiFi Analytics para mejorar la experiencia del cliente provide detailed operational playbooks.
Best Practices
Consent architecture: Always use a double opt-in mechanism for marketing consent — a checkbox on the splash page followed by a confirmation email. This provides a stronger consent record and reduces the risk of invalid email addresses entering your CRM. Store the consent record with the IP address, timestamp, and privacy notice version hash.
Data minimisation: Collect only the data you have a defined use case for. GDPR's data minimisation principle is not just a compliance requirement — it is good data hygiene. Profiles bloated with unused attributes are harder to maintain, more expensive to store, and create unnecessary compliance surface area.
Network segmentation: Maintain strict VLAN separation between guest WiFi, corporate network, and any network segments that carry payment card data. Reference PCI DSS Requirement 1.3 for detailed network segmentation guidance. IEEE 802.1X with dynamic VLAN assignment is the recommended implementation pattern for environments with multiple user classes.
MAC randomisation mitigation: Do not attempt to defeat MAC address randomisation through technical means — this is a privacy protection and circumventing it may constitute a GDPR violation. Instead, design your authentication flow to maximise first-connection login rates, as authenticated identity is a more reliable persistent identifier than any device-level signal.
Cross-venue identity resolution: For multi-venue operators, implement a master guest identity record with venue-specific behavioural sub-records. This architecture allows you to answer questions like "what is this guest's behaviour across all our venues" while maintaining the ability to personalise at the individual venue level.
For broader context on how WiFi integrates with IoT sensor networks and building management systems, the Internet of Things Architecture: A Complete Guide provides a useful reference architecture.
Troubleshooting & Risk Mitigation
Low authentication rates: If fewer than 40% of connected devices are completing the login flow, the most common causes are: splash page load time exceeding three seconds (optimise assets and CDN configuration), form fields requesting too much information (reduce to email address only for initial capture), and unclear value proposition on the splash page (test messaging that emphasises free, fast WiFi). A/B test your splash page design — small changes in copy and layout can move authentication rates by 10–15 percentage points.
MAC randomisation breaking return visitor recognition: If your return visitor recognition rate is below 60%, you likely have a high proportion of iOS 14+ and Android 10+ devices using randomised MACs. Ensure your authentication flow is prompting guests to log in on every visit, not just their first. Consider implementing a "remember me" token stored in the device's browser local storage to streamline re-authentication without relying on MAC address.
GDPR consent record gaps: If your consent audit reveals gaps — profiles with marketing consent flags but no corresponding consent timestamp or privacy notice version — you have a compliance risk. Audit your historical data, suppress any profiles without a valid consent record from marketing sends, and implement a re-consent campaign to rebuild your opted-in audience on a clean legal basis.
Data silos preventing activation: The most common reason first-party data fails to deliver ROI is that it sits in the WiFi analytics platform without being activated in downstream systems. Prioritise CRM integration in your deployment plan. A guest profile that exists only in your WiFi platform cannot drive email campaigns, loyalty rewards, or personalised offers. The data must flow to the systems where it can be acted upon.
PCI DSS scope creep: If your guest WiFi network is on the same physical infrastructure as your payment processing network, you may inadvertently be bringing your WiFi infrastructure into PCI DSS scope. Engage a Qualified Security Assessor to review your network segmentation before deployment. The cost of a QSA review is significantly lower than the cost of a PCI DSS remediation project.
ROI & Business Impact
Measuring the Value of a First-Party Data Asset
The ROI of a first-party data programme is measured across three dimensions: direct revenue impact from data-driven campaigns, operational efficiency gains from behavioural intelligence, and risk mitigation value from reduced compliance exposure.
Direct revenue impact is the most straightforward to measure. Track the incremental revenue attributable to campaigns that used first-party WiFi data for targeting or personalisation, compared to a control group that received generic communications. In hospitality environments, personalised email campaigns to WiFi-authenticated guests consistently outperform generic broadcast campaigns by a factor of two to three times on open rate and four to six times on conversion rate, based on Purple platform data across the estate.
Operational efficiency is measured through the lens of venue optimisation. Dwell time data from WiFi analytics enables staffing decisions — if your analytics show that footfall peaks between 12:00 and 14:00 on Thursdays, you can optimise staffing rotas accordingly. Zone-level traffic data informs merchandising decisions in retail environments. Queue time data informs service design in transport and healthcare settings.
Risk mitigation value is harder to quantify but significant. The cost of a GDPR enforcement action — which can reach 4% of global annual turnover under Article 83(5) — dwarfs the cost of a properly implemented first-party data programme. The shift from third-party to first-party data reduces your exposure to enforcement actions arising from unlawful data processing.
Case Study 1: Regional Hotel Chain — Hospitality
A regional hotel chain operating twelve properties across the UK deployed Purple's guest WiFi platform across its estate. Prior to deployment, the chain had no systematic mechanism for capturing guest contact data at the property level — loyalty programme enrolment was handled at the front desk and achieved a 15% capture rate.
Following deployment of Purple's captive portal with email registration, the chain achieved a 68% authentication rate across connected devices, with 54% of authenticated guests providing marketing consent. Within six months, the chain had built a first-party database of 47,000 opted-in guest profiles, compared to 8,200 loyalty programme members prior to deployment.
The chain used the WiFi-derived dataset to run a re-engagement campaign targeting guests who had stayed once but not returned within twelve months. The campaign achieved a 34% open rate and a 6.2% booking conversion rate, generating £180,000 in incremental room revenue from a single campaign send. The ROI on the annual platform licence was achieved within the first campaign cycle.
Case Study 2: Retail Estate — Multi-Site Retail
A fashion retailer operating 45 stores across the UK and Ireland implemented Purple's WiFi analytics platform to address a specific operational problem: the marketing team had no visibility into in-store behaviour and could not measure the impact of digital advertising campaigns on physical store visits.
The deployment enabled the retailer to build a cross-channel attribution model. Customers who clicked on a paid social campaign and subsequently visited a store within seven days were identified through the WiFi authentication match against the CRM record. This attribution data revealed that paid social was driving 23% more in-store visits than previously attributed, which directly informed a reallocation of £400,000 in annual media spend from lower-performing channels.
The dwell time data also revealed a significant insight: customers who spent more than twelve minutes in the store had a 3.4x higher average transaction value than customers who spent fewer than six minutes. This insight drove a store layout redesign in five pilot locations, with fitting rooms relocated to increase average dwell time. The pilot stores showed an 18% increase in average transaction value over the following quarter.
For more on how WiFi analytics applies specifically to the Retail sector, Purple's industry page provides detailed use cases and deployment patterns.
Expected Outcomes by Venue Type
| Venue Type | Typical Authentication Rate | Time to Actionable Dataset | Primary ROI Driver |
|---|---|---|---|
| Hotel (200+ rooms) | 55–70% | 4–8 weeks | Re-engagement campaigns, upsell personalisation |
| Retail store (high street) | 35–50% | 6–10 weeks | Cross-channel attribution, dwell time optimisation |
| Stadium / arena | 60–75% | Per-event | Sponsor activation, F&B upsell, post-event re-engagement |
| Conference centre | 70–85% | Per-event | Delegate profiling, exhibitor lead generation |
| Public sector / transport hub | 40–60% | 8–12 weeks | Footfall planning, service design, accessibility insight |
The Wi-Fi in Auto: The Complete 2026 Enterprise Guide provides a useful parallel reference for organisations considering first-party data collection in automotive and transport contexts, where the same architectural principles apply in a mobile environment.
Key Terms & Definitions
First-Party Data
Data collected directly by an organisation from individuals with whom it has a direct relationship, through its own channels and touchpoints, with explicit consent. The organisation owns the data and controls its use.
IT teams encounter this when architecting data collection systems for guest WiFi, mobile apps, loyalty programmes, and website analytics. It matters because it is the only data class that is fully compliant under GDPR and immune to third-party platform policy changes.
Captive Portal
A web page presented to a network user before they are granted access to the internet. In the context of guest WiFi, it serves as the authentication interface and the primary mechanism for consent capture and identity data collection.
Network architects configure captive portals through access point management platforms (e.g., Cisco Meraki, Aruba, Ruckus) or overlay platforms like Purple. The portal's design directly affects authentication rate and data quality.
MAC Address Randomisation
A privacy feature implemented in iOS 14+, Android 10+, and Windows 10+ that causes devices to use a different, randomly generated MAC address for each WiFi network, preventing persistent tracking via hardware identifier.
IT teams must account for MAC randomisation when designing return visitor recognition systems. The correct mitigation is to anchor persistent identification to an authenticated credential (email address) rather than the device MAC address.
IEEE 802.1X
An IEEE standard for port-based network access control that provides an authentication mechanism for devices wishing to attach to a LAN or WLAN. It uses the Extensible Authentication Protocol (EAP) and typically integrates with a RADIUS server for credential validation.
Network architects use 802.1X to ensure that only authenticated devices gain network access, which is the technical prerequisite for tying behavioural data to a known identity. It is also a requirement for enterprise-grade network security and is referenced in PCI DSS network segmentation guidance.
WPA3
The third generation of the Wi-Fi Protected Access security protocol, introducing Simultaneous Authentication of Equals (SAE) for stronger password-based authentication and mandatory forward secrecy, ensuring that session keys cannot be retroactively decrypted even if the long-term key is compromised.
IT teams should require WPA3 on all new access point deployments. For guest WiFi specifically, WPA3-Personal with SAE provides significantly stronger protection for guest session data than WPA2-PSK, which is vulnerable to offline dictionary attacks.
GDPR Consent Record
A structured data record that documents the fact of a data subject's consent, including: the identity of the data subject, the specific processing activities consented to, the timestamp of consent, the version of the privacy notice presented, and the mechanism through which consent was given.
Under GDPR Article 7(1), the data controller bears the burden of demonstrating that consent was obtained. IT teams must ensure that the consent record is stored as a first-class data object, retrievable on demand for data subject access requests and regulatory audits.
Data Minimisation
The GDPR principle (Article 5(1)(c)) that personal data collected must be adequate, relevant, and limited to what is necessary in relation to the purposes for which it is processed.
IT architects should apply data minimisation when designing captive portal registration forms and analytics data schemas. Collecting data fields without a defined use case creates unnecessary compliance surface area and increases the cost of data management.
Identity Resolution
The process of matching and unifying data records that refer to the same individual across multiple data sources, channels, or touchpoints into a single, coherent profile.
For multi-venue operators, identity resolution is the technical challenge of recognising that a guest who visited your London property last month and your Edinburgh property this week is the same person. Email address is the most reliable cross-channel identifier for first-party identity resolution in physical venue contexts.
Dwell Time
The duration for which a guest's device remains connected to a WiFi access point or within range of a set of access points, used as a proxy for the time the guest spends in a specific zone or venue.
Venue operations directors use dwell time data to optimise staffing, layout, and service design. In retail, dwell time correlates strongly with transaction value. In hospitality, zone-level dwell time data informs F&B placement and amenity utilisation decisions.
PCI DSS Network Segmentation
The practice of isolating the cardholder data environment (CDE) from other network segments using firewalls, VLANs, or other access controls, as required by PCI DSS Requirement 1.3, to reduce the scope of PCI DSS compliance assessment.
IT teams deploying guest WiFi in retail or hospitality environments must ensure that the guest VLAN is completely isolated from any network segment that processes, stores, or transmits payment card data. Failure to maintain this segmentation can bring the entire guest WiFi infrastructure into PCI DSS scope.
Case Studies
A 350-room hotel group with four properties wants to build a first-party guest database to replace its reliance on OTA (Online Travel Agency) booking data. The group currently has no CRM and no systematic guest contact capture. The IT team has Cisco Meraki access points deployed across all properties. What is the recommended deployment approach?
Step 1 — Compliance foundation (Week 1–2): Engage legal counsel to draft a GDPR-compliant privacy notice covering WiFi data collection. Define consent categories: analytics (legitimate interests basis), marketing email (explicit consent), third-party sharing (explicit consent). Establish data retention periods: session logs 90 days, guest profiles with marketing consent 3 years, profiles without consent 12 months.
Step 2 — Infrastructure configuration (Week 2–4): Configure Cisco Meraki access points to redirect unauthenticated clients to Purple's captive portal. Create a dedicated guest VLAN (e.g., VLAN 100) isolated from the corporate and PMS networks. Configure RADIUS integration between Meraki and Purple's authentication service. Test MAC address randomisation handling — ensure that returning guests are prompted to re-authenticate and that the authentication credential (email) is used as the persistent identifier.
Step 3 — Captive portal design (Week 3–4): Design the splash page with email registration as the primary authentication method. Include a clear value proposition ('Free high-speed WiFi — takes 30 seconds to connect'). Place the marketing consent checkbox below the fold with clear opt-in language. A/B test two versions of the splash page to optimise authentication rate before full rollout.
Step 4 — CRM integration (Week 4–6): Select and deploy a CRM platform (e.g., HubSpot, Salesforce, or a hospitality-specific PMS with CRM capability). Configure Purple's API integration to sync authenticated guest profiles to the CRM in real time. Map the data fields: email address, first name, visit date, property, device type, marketing consent flag, consent timestamp.
Step 5 — First campaign and measurement (Week 8–12): Once the database reaches 1,000+ opted-in profiles, run a first re-engagement campaign targeting guests who stayed 3–12 months ago. Measure open rate, click rate, and booking conversion. Use this as the baseline ROI measurement for the programme.
A retail chain with 80 stores wants to measure the offline impact of its digital advertising campaigns. The marketing team currently attributes all conversions to the last digital click, which they suspect is significantly undercounting the value of upper-funnel channels. The IT team has Aruba access points deployed. How should they architect a WiFi-based attribution solution?
Step 1 — Identity bridge design: The core of the attribution solution is an identity bridge between the digital advertising ecosystem and the in-store WiFi dataset. Customers who authenticate to the store WiFi with their email address create a first-party identifier. The same email address used for online account registration, loyalty programme membership, or email marketing opt-in becomes the matching key.
Step 2 — CRM unification: Ensure that the WiFi-derived guest profiles are synchronised to the central CRM with a consistent email-based primary key. Configure deduplication logic to merge profiles where the same email address appears in both the WiFi dataset and the existing CRM. This unified profile is the foundation for attribution.
Step 3 — Campaign tagging and UTM configuration: Tag all digital advertising campaigns with UTM parameters that are captured in the CRM when a customer clicks through to the website or app. Record the campaign source, medium, and campaign name against the customer's CRM record.
Step 4 — Attribution window configuration: Define the attribution window — the maximum time between a digital ad interaction and an in-store WiFi connection that counts as an attributed visit. A 7-day window is standard for fashion retail; a 30-day window may be appropriate for considered purchases. Configure the attribution logic in your analytics platform.
Step 5 — Measurement and reporting: Build a dashboard that shows, for each campaign: total digital clicks, attributed in-store visits (WiFi connections within the attribution window from customers with a matching CRM record), and in-store transaction value for attributed visitors. Compare the average transaction value of attributed visitors versus non-attributed visitors to quantify the in-store revenue impact of digital campaigns.
Scenario Analysis
Q1. Your organisation operates a chain of 25 conference centres across the UK. The marketing director wants to use WiFi data to send personalised follow-up emails to event delegates after each event. The IT team has flagged that the current captive portal only asks for a name and accepts anonymous access. What changes are required before the marketing use case can be lawfully implemented?
💡 Hint:Consider both the technical changes to the authentication flow and the legal changes to the consent framework. GDPR requires that consent for marketing communications is explicit, specific, and freely given — it cannot be bundled with the terms of service for WiFi access.
Show Recommended Approach
Three changes are required. First, the captive portal must be updated to require email address capture as a mandatory field for authentication — anonymous access must be removed or made a separate, non-marketing-consented path. Second, a clearly worded marketing consent checkbox must be added to the splash page, separate from the WiFi terms of service, with language such as 'I agree to receive marketing communications from [Organisation Name] about future events and offers.' This checkbox must be unchecked by default. Third, the consent record infrastructure must be updated to store the timestamp, privacy notice version, and specific consent flag for each profile. Only profiles with a valid marketing consent record should be included in post-event email sends. The privacy notice must also be updated to describe the marketing use case specifically. Once these changes are in place, the marketing use case is lawfully implementable.
Q2. A stadium operator is preparing for a major concert series. The venue has 45,000 capacity and expects 80% of attendees to attempt WiFi connection. The current infrastructure uses WPA2-PSK with a shared password published on event programmes. The IT director wants to implement a first-party data capture solution for the series. What are the key architectural decisions and what is the recommended approach?
💡 Hint:Consider the authentication method that maximises both data capture rate and data quality at scale. Also consider the network capacity requirements for 36,000 simultaneous connection attempts and the specific compliance requirements for event-based data collection.
Show Recommended Approach
The recommended approach involves four key decisions. First, replace WPA2-PSK with an open network plus captive portal architecture — WPA2-PSK with a shared password provides no per-user authentication and cannot support first-party data capture. The captive portal should use email registration with a single field to maximise completion rate at scale. Second, pre-provision the network for peak load: 36,000 simultaneous connections requires careful DHCP pool sizing (minimum /15 subnet for the guest VLAN), RADIUS server capacity planning, and access point density review — stadium environments typically require higher AP density than the manufacturer's coverage specifications suggest due to RF interference from crowd density. Third, implement event-specific consent language that references the specific event and the operator's identity — generic venue WiFi consent language may not be specific enough for GDPR purposes when the data will be used for post-event marketing. Fourth, configure data retention to align with the event marketing use case — post-event email campaigns should be sent within 30 days of the event, and profiles without subsequent engagement should be suppressed or deleted within 12 months. The WPA3 transition should be planned for the following season to improve session security.
Q3. A retail IT director has been told by the marketing team that their paid social campaigns are 'not working' because in-store sales have not increased despite significant digital ad spend. The IT team has Purple WiFi deployed across all 60 stores with email authentication. How would you design a measurement framework to test whether the paid social campaigns are actually driving in-store visits that are not being attributed?
💡 Hint:The key is the identity bridge between the digital advertising ecosystem and the in-store WiFi dataset. Consider what identifier exists in both environments and how you would construct the attribution logic.
Show Recommended Approach
The measurement framework requires three components. First, build the identity bridge: export the hashed email addresses of customers who clicked on paid social ads from your ad platform (Facebook/Meta and Google both support customer list matching with hashed emails). Match these against the WiFi authentication dataset — customers who clicked an ad and subsequently authenticated to store WiFi within a defined attribution window (7 days recommended for fashion retail) are attributed visits. Second, define the control group: customers in the CRM who did not receive the paid social ad (or who were in a holdout group) serve as the control. Compare the in-store visit rate of the exposed group versus the control group within the attribution window. The difference is the incremental visit rate attributable to the campaign. Third, layer transaction data: for attributed visitors, pull their in-store transaction value from the POS system (matched via loyalty card or email at checkout). Calculate the revenue per attributed visit and multiply by the incremental visit count to get the total incremental revenue. Compare this to the campaign spend to calculate ROAS. This framework will typically reveal that paid social is driving 20–40% more in-store visits than last-click digital attribution suggests, which has direct implications for media budget allocation.



