Best Practices for Securing K-12 School Networks with NAC
This technical reference guide provides actionable strategies for IT leaders to architect, deploy, and manage Network Access Control (NAC) in K-12 school environments. It covers essential topics from 802.1X authentication and VLAN segmentation to handling IoT devices with MAB and MPSK, ensuring robust safeguarding and compliance.
Listen to this guide
View podcast transcript
- Executive Summary
- Technical Deep-Dive
- The 802.1X Protocol and EAP Methods
- Wireless Security Standards: WPA3-Enterprise
- Network Segmentation Architecture
- Implementation Guide
- Phase 1: Discovery and Audit
- Phase 2: RADIUS Infrastructure Deployment
- Phase 3: Monitor Mode
- Phase 4: Enforcement and Segmentation
- Best Practices
- Troubleshooting & Risk Mitigation
- Common Failure Modes
- ROI & Business Impact

Executive Summary
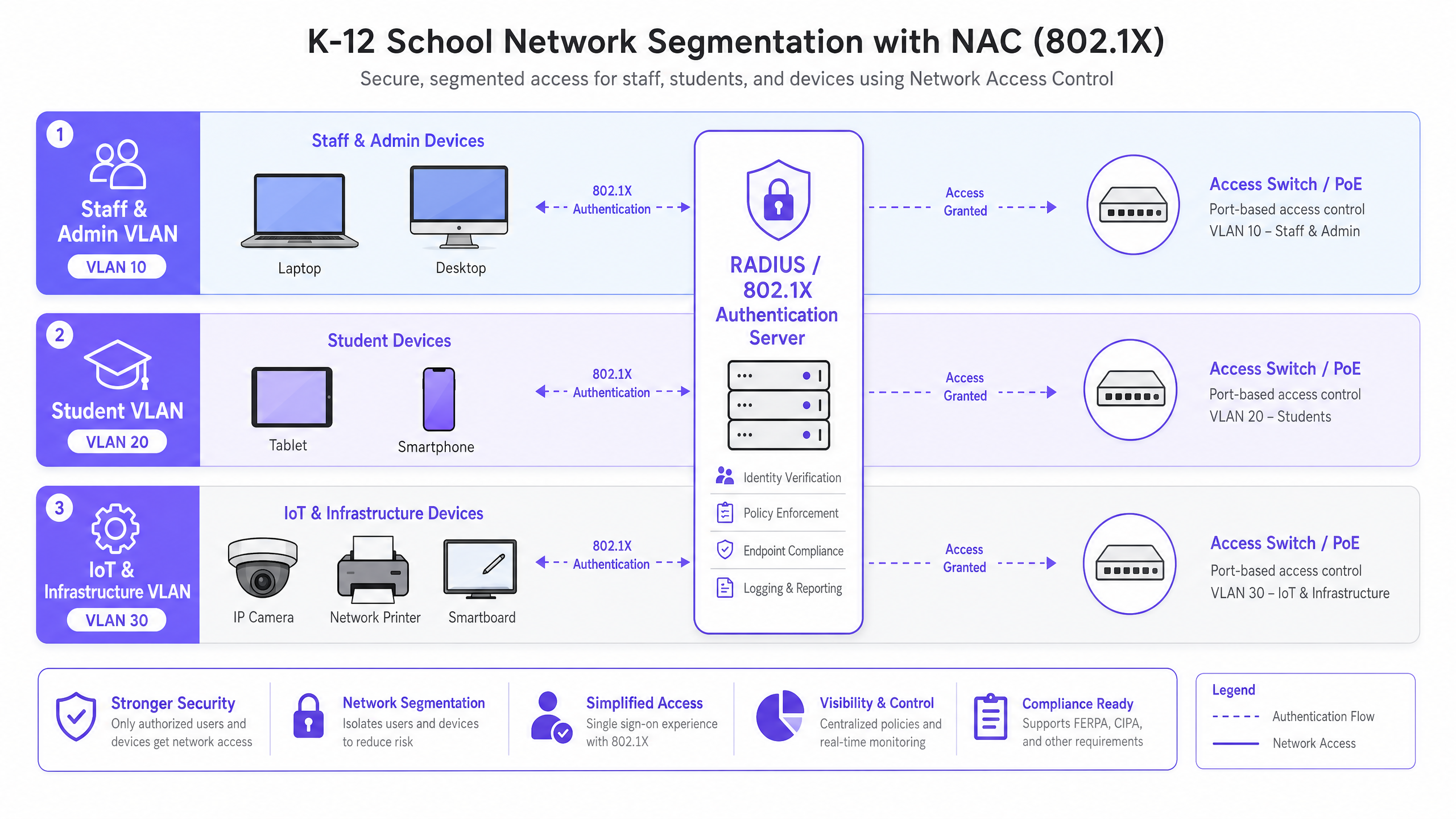
Securing a K-12 school network is fundamentally an exercise in risk mitigation, identity management, and compliance. IT leaders face the complex challenge of providing seamless access to a highly diverse user base—staff, students, visitors, and contractors—while simultaneously securing an ever-expanding array of IoT devices like smartboards and security cameras. Network Access Control (NAC) driven by IEEE 802.1X provides the architectural foundation for robust network segmentation, ensuring that devices are authenticated, authorised, and appropriately isolated before they are granted network access.
This guide provides a comprehensive technical framework for deploying NAC in educational environments. It details best practices for RADIUS integration, VLAN architecture, endpoint posture checking, and secure guest onboarding. By implementing these strategies, venue operations directors and network architects can significantly reduce their attack surface, protect sensitive safeguarding data, and maintain strict compliance with regulatory standards such as GDPR and CIPA, all without compromising the operational efficiency of the school.
Technical Deep-Dive
At its core, NAC operates on the principle of zero trust at the network edge. When a device (the supplicant) connects to an access switch or wireless access point (the authenticator), it is placed in a restricted state. The authenticator forwards the credentials to an authentication server (typically a RADIUS server) using the 802.1X protocol. Only upon successful authentication and policy evaluation is the device assigned to the appropriate VLAN with specific access control lists (ACLs) applied.
The 802.1X Protocol and EAP Methods
The Extensible Authentication Protocol (EAP) framework provides the transport mechanism for various authentication methods within 802.1X. In a K-12 environment, the most common implementations are:
- PEAP-MSCHAPv2: Often used for staff and student devices authenticating against Active Directory credentials. While easier to deploy, it is vulnerable to credential theft if the server certificate is not strictly validated by the client.
- EAP-TLS: The gold standard for enterprise security. It relies on mutual certificate-based authentication, eliminating the need for passwords entirely. This is highly recommended for managed devices (like school-issued Chromebooks or staff laptops) where a Public Key Infrastructure (PKI) or Mobile Device Management (MDM) solution can automatically provision the necessary certificates.
Wireless Security Standards: WPA3-Enterprise
For wireless networks, WPA3-Enterprise is the current benchmark. It mandates the use of Protected Management Frames (PMF) to prevent deauthentication attacks and offers a 192-bit security mode for highly sensitive environments (e.g., the staff/admin network). For student networks where WPA3-Enterprise might be too complex for BYOD scenarios, WPA3-Personal with Simultaneous Authentication of Equals (SAE) provides robust protection against offline dictionary attacks, a significant improvement over the older WPA2-PSK standard.
Network Segmentation Architecture
Effective NAC relies on rigorous network segmentation. A flat network architecture is a critical vulnerability. A standard K-12 deployment should, at a minimum, implement the following VLAN structure:
- Staff & Admin VLAN: Full access to internal resources, MIS systems, and the internet. Highly restricted lateral movement from other VLANs.
- Student VLAN: Filtered internet access with strict content filtering enforced. No access to staff resources or management interfaces.
- IoT & Infrastructure VLAN: Houses smartboards, IP cameras, and building management systems. This VLAN should have no outbound internet access unless explicitly required by a specific device, and should be isolated from user VLANs.
- Guest VLAN: Internet-only access, isolated from all internal networks, typically fronted by a captive portal for terms acceptance and identity capture.
Implementation Guide
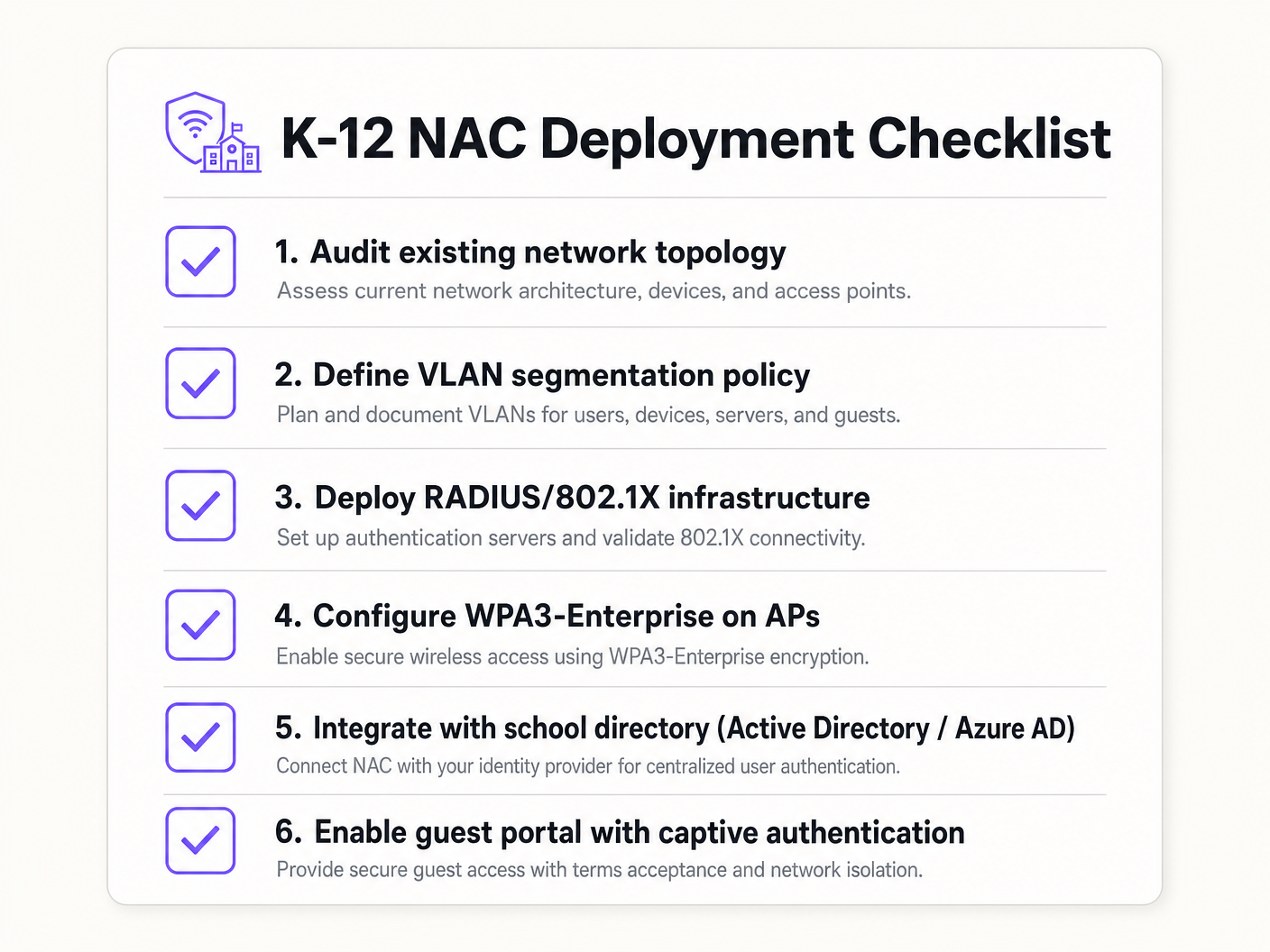
Deploying NAC requires a phased, methodical approach to avoid disrupting educational operations.
Phase 1: Discovery and Audit
Before implementing any enforcement, conduct a comprehensive network audit. Use tools to discover all connected devices, identify shadow IT (unauthorised switches or access points), and document the current state of the network. This phase is crucial for building accurate MAC Authentication Bypass (MAB) whitelists for legacy devices.
Phase 2: RADIUS Infrastructure Deployment
Deploy your RADIUS infrastructure. If using on-premises Active Directory, Network Policy Server (NPS) is a common choice. For cloud-centric environments (Azure AD, Google Workspace), cloud RADIUS solutions offer streamlined integration. Ensure that the RADIUS server is correctly configured to communicate with your directory service and that firewall rules permit LDAP/LDAPS traffic.
Phase 3: Monitor Mode
Enable 802.1X on access switches and wireless controllers in monitor mode (sometimes called open mode). In this state, the authenticator evaluates the 802.1X credentials and logs the result, but it does not block access if authentication fails. This allows IT teams to identify misconfigured devices, missing certificates, or legacy equipment that requires MAB, without causing network outages.
Phase 4: Enforcement and Segmentation
Once the monitor mode logs show a high success rate and all exceptions have been accounted for, begin enforcing 802.1X authentication. Roll this out in phases—starting with a pilot group (e.g., the IT department), then expanding to staff, and finally to students. Implement dynamic VLAN assignment via RADIUS attributes (Tunnel-Type, Tunnel-Medium-Type, Tunnel-Private-Group-ID) to ensure users are placed in the correct network segment based on their directory group membership.
Best Practices
- Implement MAB and MPSK for IoT: Legacy devices and headless IoT endpoints often lack 802.1X supplicants. Use MAC Authentication Bypass (MAB) for legacy equipment, but prefer Multi-PSK (MPSK) for modern IoT devices. MPSK assigns a unique pre-shared key to each device, ensuring that if one key is compromised, the rest of the network remains secure. For a detailed configuration walkthrough, refer to the Managing IoT Device Security with NAC and MPSK guide.
- Enforce Endpoint Posture Checking: Go beyond simple authentication by integrating posture checks. Before granting access, the NAC solution should verify that the endpoint has active antivirus software, is fully patched, and has disk encryption enabled. Non-compliant devices should be placed in a remediation VLAN.
- Integrate Guest Access with Analytics: Guest networks must be isolated and compliant. Integrating a platform like Guest WiFi ensures that visitor access is secure, GDPR-compliant, and provides valuable WiFi Analytics to understand venue usage and footfall.
- Use Certificate-Based Authentication (EAP-TLS) Where Possible: For managed devices, EAP-TLS eliminates the reliance on passwords, significantly reducing the risk of credential theft and phishing attacks.
Troubleshooting & Risk Mitigation
Common Failure Modes
- Certificate Trust Errors: If BYOD users are prompted to accept an untrusted server certificate during PEAP authentication, it trains them to ignore security warnings, creating a massive phishing vulnerability. Mitigation: Always use a certificate signed by a publicly trusted Certificate Authority (CA) for the RADIUS server, or ensure the internal CA root certificate is pushed to all managed devices via MDM.
- Directory Integration Failures: RADIUS authentication will fail if the server cannot communicate with the directory service (e.g., AD domain controllers are unreachable, or the service account password expired). Mitigation: Implement redundant RADIUS servers and monitor the health of the directory integration continuously.
- The 'Printer Problem' (Legacy Device Lockout): Enforcing 802.1X without a complete MAB whitelist will immediately disconnect legacy printers, AV equipment, and older smartboards. Mitigation: The monitor mode phase is critical. Do not move to enforcement until all non-authenticating devices have been identified and profiled.
ROI & Business Impact
While NAC is primarily a security and compliance investment, it delivers measurable business value:
- Risk Mitigation: The financial and reputational cost of a data breach involving student records is catastrophic. NAC drastically reduces the attack surface and prevents lateral movement, containing potential breaches.
- Operational Efficiency: Dynamic VLAN assignment reduces the administrative overhead of manually configuring switch ports. IT staff spend less time managing VLANs and more time on strategic initiatives.
- Compliance Assurance: A robust NAC deployment provides the audit trails and access controls required to demonstrate compliance with GDPR, CIPA, and local safeguarding regulations, simplifying audits and reducing legal exposure.
Key Definitions
Network Access Control (NAC)
A security architecture that enforces policy on devices attempting to access a network, ensuring only authenticated and compliant devices are granted entry.
Essential for IT teams to prevent unauthorized access and segment network traffic based on user roles (e.g., staff vs. student).
IEEE 802.1X
The IEEE standard for port-based Network Access Control, providing an authentication mechanism to devices wishing to attach to a LAN or WLAN.
The foundational protocol that allows switches and access points to verify user identity before granting network access.
RADIUS (Remote Authentication Dial-In User Service)
A networking protocol that provides centralized Authentication, Authorization, and Accounting (AAA) management for users who connect and use a network service.
The 'brain' of the NAC deployment, responsible for verifying credentials against a directory (like Active Directory) and assigning VLANs.
MAC Authentication Bypass (MAB)
A technique used to authenticate devices that do not support 802.1X by using their MAC address as the credential against a pre-approved whitelist.
Crucial for allowing legacy devices like older printers and smartboards onto the network without compromising the 802.1X requirement for modern devices.
Multi-PSK (MPSK)
A wireless security feature that allows multiple unique Pre-Shared Keys to be used on a single SSID, with each key assigning specific network policies or VLANs.
The best practice for securing modern IoT devices that cannot perform 802.1X authentication, isolating them securely.
Dynamic VLAN Assignment
The process where a RADIUS server instructs the switch or access point to place an authenticated user into a specific VLAN based on their directory group membership.
Reduces administrative overhead by allowing a single SSID or switch port configuration to serve multiple user types securely.
EAP-TLS (Extensible Authentication Protocol - Transport Layer Security)
An 802.1X authentication method that requires mutual certificate authentication between the client and the server, eliminating the use of passwords.
The most secure authentication method, highly recommended for school-issued managed devices to prevent credential theft.
Endpoint Posture Checking
The process of evaluating a device's security state (e.g., antivirus status, OS patch level) before granting it network access.
Ensures that even authenticated users cannot introduce malware into the network via compromised or unpatched devices.
Worked Examples
A 1500-student secondary school needs to deploy 200 new wireless environmental sensors across the campus. These sensors only support WPA2-Personal and do not have an 802.1X supplicant. How should the network architect secure these devices without compromising the main network?
The architect should deploy a dedicated hidden SSID for IoT devices and implement Multi-PSK (MPSK). Each sensor (or group of sensors) is assigned a unique, complex pre-shared key. The wireless controller or RADIUS server is configured to map these specific keys to the isolated 'IoT & Infrastructure VLAN'. This VLAN must have strict ACLs applied, denying all access to the Staff and Student VLANs, and restricting outbound internet access only to the specific cloud endpoints required by the environmental sensors.
During the rollout of 802.1X (PEAP-MSCHAPv2) for BYOD student devices, the IT helpdesk is overwhelmed with tickets from students reporting that their devices are warning them about an 'untrusted network certificate'. How should this be resolved?
The issue occurs because the RADIUS server is using a certificate signed by the school's internal, private Certificate Authority (CA), which the BYOD devices do not natively trust. The immediate fix is to replace the RADIUS server's certificate with one issued by a widely recognized public CA (e.g., DigiCert, Let's Encrypt). Long-term, the school should implement an onboarding portal that securely configures the supplicant and installs the necessary trust anchors before the device attempts to connect.
Practice Questions
Q1. A school district is migrating its directory services entirely to Google Workspace and phasing out on-premises Active Directory. They currently use NPS for RADIUS. What architectural change is required to maintain 802.1X authentication for their fleet of managed Chromebooks?
Hint: Consider how Chromebooks authenticate natively and what infrastructure is needed when AD is removed.
View model answer
The district should migrate to a cloud RADIUS provider (e.g., SecureW2, Foxpass) that integrates natively with Google Workspace, or utilize Google's own Cloud RADIUS capabilities if available in their licensing tier. They should configure the Chromebooks via the Google Admin Console to use EAP-TLS, leveraging device certificates automatically provisioned by Google's certificate management, completely removing the reliance on passwords and on-premises NPS servers.
Q2. During a network audit, the IT team discovers a consumer-grade wireless router plugged into a classroom wall port, broadcasting a hidden SSID. How does a properly configured NAC solution prevent this shadow IT from compromising the network?
Hint: Think about what happens at the switch port level when an unmanaged device is connected.
View model answer
With 802.1X enforced on the wired switch ports, the consumer router will fail authentication because it lacks valid credentials or a certificate. The switch port will either remain in an unauthorized state (blocking all traffic) or dynamically assign the port to an isolated remediation VLAN. Additionally, enterprise NAC solutions can detect the presence of NAT or multiple MAC addresses behind a single port, triggering an automatic port shutdown to isolate the rogue device.
Q3. A venue operations director at a large educational campus wants to provide seamless WiFi access for visiting parents during a sports tournament, but the IT team is concerned about GDPR compliance and network security. What is the recommended approach?
Hint: Consider the balance between ease of access and the legal requirements for capturing user data.
View model answer
The IT team should provision a dedicated Guest VLAN that is strictly isolated from all internal resources and has internet-only access. They should deploy a captive portal solution, such as Purple's Guest WiFi platform, to handle onboarding. This ensures that visitors must accept the terms and conditions and provide explicit consent for data processing before gaining access, satisfying GDPR requirements while keeping the core network secure.