How to Collect First-Party Data Through WiFi
This authoritative guide provides IT leaders and venue operators with a technical blueprint for transforming guest WiFi infrastructure into a compliant, high-yield first-party data collection engine. It covers captive portal architecture, splash page optimisation, CRM integration, and strategies for maximising data yield while maintaining GDPR compliance. Designed for IT managers, network architects, and CTOs across hospitality, retail, and public-sector environments.
🎧 Listen to this Guide
View Transcript
- Executive Summary
- Technical Deep-Dive: Architecture and Standards
- The Captive Portal and Authentication Flow
- Data Collection Mechanisms and Protocols
- Security and Compliance Standards
- Implementation Guide: From Deployment to Integration
- Step 1: Network Configuration and Walled Garden Setup
- Step 2: Splash Page Design and Optimisation
- Step 3: CRM and Marketing Automation Integration
- Best Practices for Maximising Data Yield
- Troubleshooting & Risk Mitigation
- Captive Portal Not Displaying
- Low Data Capture Rates
- MAC Address Randomisation
- ROI & Business Impact
- Marketing Efficiency and Revenue Generation
- Operational Intelligence
- Enhancing the Customer Experience
Executive Summary
For modern physical venues — from high-street retail and international airports to sprawling hospitality groups — guest WiFi is no longer merely a cost centre or a basic utility. When architected correctly, it is the most efficient engine for first-party data collection available to brick-and-mortar operations. In an era defined by the deprecation of third-party cookies and stringent privacy regulations like GDPR and CCPA, acquiring direct, consented customer data is a strategic imperative.
This guide provides a comprehensive technical blueprint for IT leaders, network architects, and venue operations directors. It details how to transform existing wireless infrastructure into a secure, compliant, and high-yield data capture platform using Guest WiFi solutions. We will explore the technical architecture required to capture this data, the deployment of captive portals for seamless authentication, and the integration pathways necessary to pipe clean, actionable data directly into your CRM and marketing automation platforms. By implementing the strategies outlined here, organisations can achieve significant ROI through enhanced customer intelligence, targeted marketing, and operational efficiency, while maintaining robust security and compliance postures.
Technical Deep-Dive: Architecture and Standards
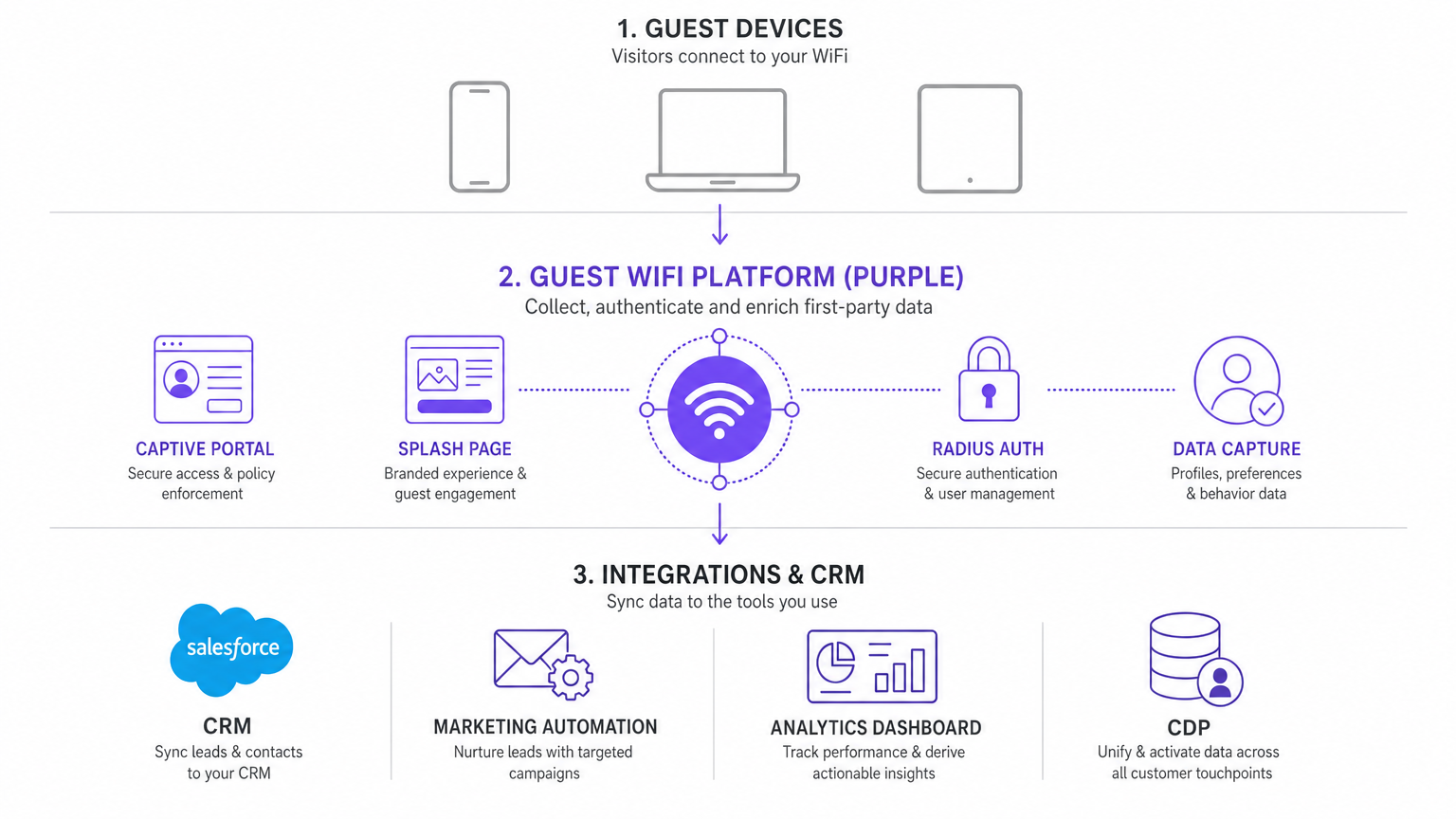
The foundation of effective first-party data collection through WiFi lies in a robust, secure, and well-integrated technical architecture. This section deconstructs the core components and industry standards that govern these deployments.
The Captive Portal and Authentication Flow
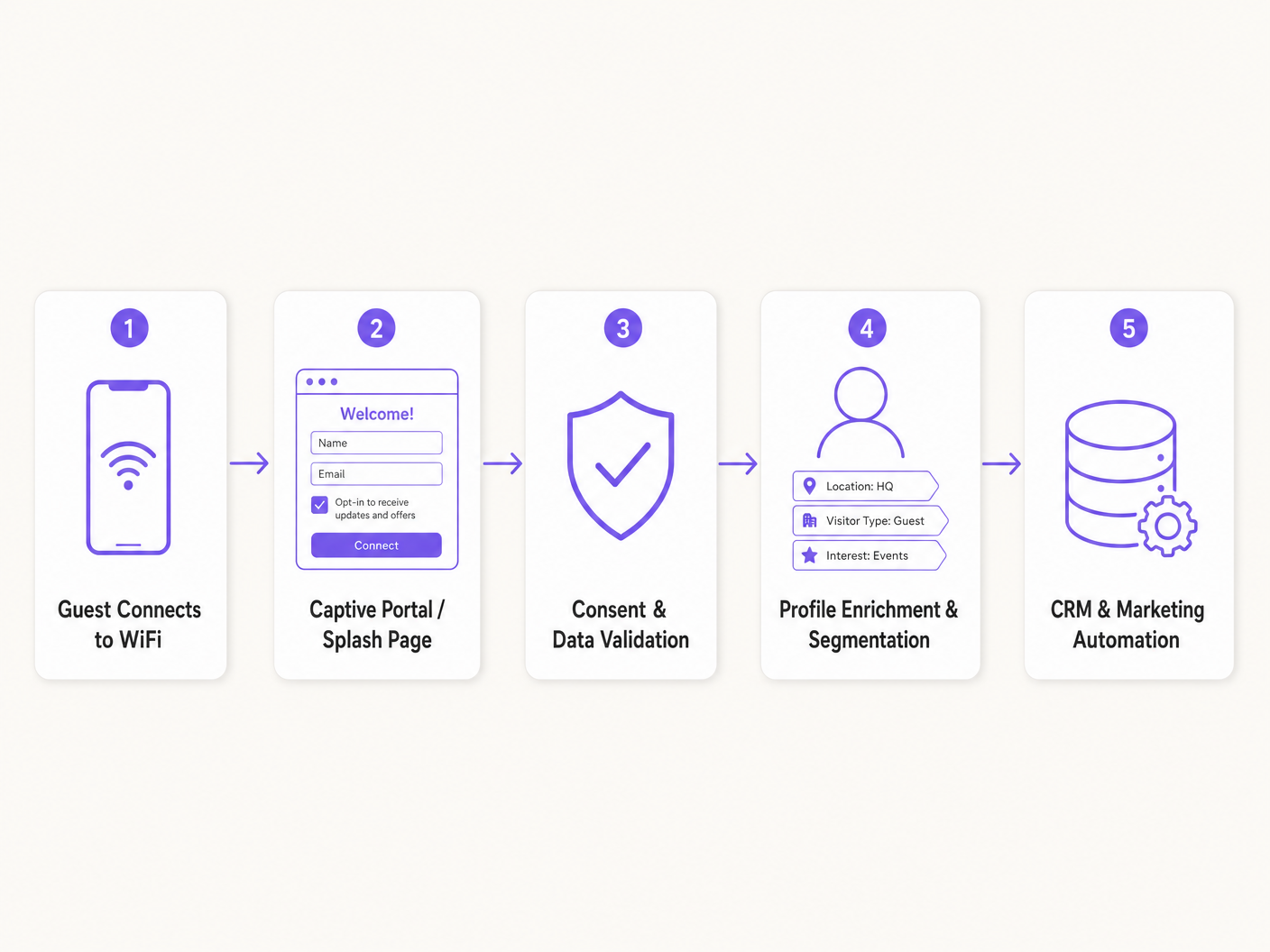
The primary mechanism for data capture is the captive portal — a web page that intercepts HTTP/HTTPS requests from unauthenticated devices and redirects them to a login or splash page. This interception is typically handled by the Wireless LAN Controller (WLC) or the access point (AP) itself, acting as a walled garden.
When a guest device associates with the Service Set Identifier (SSID), it receives an IP address via DHCP. Upon attempting to access the internet, the network infrastructure intercepts the traffic and presents the captive portal. This is where the value exchange occurs: internet access in return for user data and consent.
Authentication is generally managed via RADIUS (Remote Authentication Dial-In User Service). The captive portal communicates with a RADIUS server, which authenticates the user credentials (e.g., email address, social media token) and authorises access. The RADIUS server then sends an Access-Accept message to the WLC/AP, along with attributes such as session limits or bandwidth restrictions, allowing the device to bypass the walled garden.
Data Collection Mechanisms and Protocols
Modern WiFi Analytics platforms employ several methods to collect data:
Explicit Data Capture: This is data actively provided by the user via the splash page form. It typically includes Personally Identifiable Information (PII) such as name, email address, phone number, and demographic details.
Implicit Data Capture (Device Analytics): This involves collecting metadata from the guest device, such as the MAC address, device type, operating system, and browser information. While MAC addresses are increasingly subject to randomisation (e.g., iOS 14+ Private Wi-Fi Addresses), they remain useful for session management within a single visit.
Location and Presence Analytics: By analysing Received Signal Strength Indicator (RSSI) data from multiple APs, the system can triangulate device location. This enables the collection of dwell time, footfall patterns, and zone-based analytics, providing rich behavioural data without requiring active user input. For more advanced implementations, consider exploring the Indoor Positioning System: UWB, BLE, & WiFi Guide .
Security and Compliance Standards
Data collection must adhere to strict security and privacy standards to mitigate risk and ensure compliance.
GDPR and CCPA Compliance: The captive portal must present clear, unambiguous opt-in mechanisms for marketing communications. Consent must be granular, allowing users to accept terms of service without necessarily opting into marketing. The platform must also support data subject access requests (DSARs) and the right to be forgotten.
Data Encryption: All data transmitted between the guest device, the captive portal, and the backend databases must be encrypted using TLS 1.2 or higher. Data at rest should be encrypted using industry-standard algorithms (e.g., AES-256).
PCI DSS: If the captive portal processes payments (e.g., for premium tiered WiFi), the architecture must comply with the Payment Card Industry Data Security Standard to ensure the secure handling of payment card information.

Implementation Guide: From Deployment to Integration
Deploying a first-party data collection strategy requires a systematic approach, moving from network configuration through to seamless integration with enterprise systems.
Step 1: Network Configuration and Walled Garden Setup
The first step is configuring the network infrastructure to support the captive portal. This involves defining the guest SSID and configuring the Walled Garden — a list of IP addresses or domains that unauthenticated users can access. This is crucial for allowing devices to load the captive portal resources (e.g., images, CSS) and to reach external authentication providers (e.g., Facebook, Google) before full internet access is granted.
Actionable Advice: Ensure that the Walled Garden includes the necessary domains for your chosen authentication methods and any CDN hosting your splash page assets. Failure to do so will result in a broken user experience and a failed authentication flow.
Step 2: Splash Page Design and Optimisation
The splash page is the critical conversion point. Its design directly impacts the data capture rate.
Frictionless Onboarding: Keep the form fields to an absolute minimum. Ask only for the data you genuinely need (e.g., email address and name). Long forms cause high abandonment rates.
Progressive Profiling: Instead of asking for all information upfront, use progressive profiling. Ask for an email address on the first visit, and on subsequent visits, prompt for additional details like date of birth or interests.
Mobile Optimisation: The vast majority of guest WiFi connections are initiated from mobile devices. The splash page must be fully responsive and load quickly over potentially slow initial connections.
Step 3: CRM and Marketing Automation Integration
The collected data is only valuable if it is actionable. Integrating the guest WiFi platform with your CRM (e.g., Salesforce, HubSpot) and marketing automation tools is essential. This integration is typically achieved via REST APIs or Webhooks. When a user authenticates, a Webhook can trigger an immediate data transfer to the CRM, creating a new contact record or updating an existing one.
Data Mapping: Carefully map the fields from the captive portal to the corresponding fields in your CRM. Ensure data types align and that consent flags are accurately synchronised.
Segmentation: Use the collected data (e.g., location visited, frequency of visits, demographic information) to segment your audience within the CRM. This enables highly targeted and relevant marketing campaigns. For specific industry applications, see our guides on Retail , Healthcare , Hospitality , and Transport .
Best Practices for Maximising Data Yield
To maximise the volume and quality of first-party data collected, consider the following best practices.
Offer a Clear Value Exchange: Guests are more likely to provide their data if they perceive value in return. This could be high-speed internet access, exclusive discounts, or access to a loyalty programme.
Leverage Social Authentication: Offering social login options (e.g., Google, Facebook, Apple) reduces friction and often yields more accurate data, as users are less likely to input fake email addresses when authenticating via an existing trusted account.
Implement Seamless Re-authentication: Use token-based authentication to recognise returning guests and automatically connect them, improving the user experience while still logging their visit data.
Localise the Experience: For multi-national deployments, ensure the captive portal automatically detects the user's language and presents the splash page accordingly. This significantly improves conversion rates. For example, you can review our Spanish and German guides: Cómo utilizar WiFi Analytics para mejorar la experiencia del cliente and Wie man WiFi Analytics nutzt, um die Kundenerfahrung zu verbessern .
Troubleshooting & Risk Mitigation
Even with careful planning, deployments can encounter issues. Here are the most common failure modes and their mitigation strategies.
Captive Portal Not Displaying
This is the most frequent issue. It is often caused by incorrect Walled Garden configurations or DNS resolution failures. Mitigation: Verify the Walled Garden entries. Ensure the DNS server assigned via DHCP is reachable and functioning correctly. Check that the AP/WLC can communicate with the captive portal server over the required ports (typically 80 and 443).
Low Data Capture Rates
If the captive portal is displaying but users are not authenticating, the friction is too high. Mitigation: Review the splash page design. Are there too many fields? Is the value proposition unclear? A/B test different designs and authentication methods to optimise the conversion rate.
MAC Address Randomisation
The introduction of MAC randomisation in modern mobile operating systems complicates device tracking across multiple visits. Mitigation: Shift focus from device-centric tracking to identity-centric tracking. Encourage users to authenticate via email or social login, and use these persistent identifiers (e.g., an email hash) to track behaviour across sessions, rather than relying solely on the MAC address.
ROI & Business Impact
Marketing Efficiency and Revenue Generation
By building a robust first-party database, organisations can significantly reduce their reliance on expensive third-party data and advertising networks. Targeted email or SMS campaigns based on verified visit history and demographic data consistently outperform generic broadcast campaigns. For instance, a retail chain can trigger a promotional offer to a customer who has dwelled in a specific department for over ten minutes, driving immediate conversion.
Operational Intelligence
Beyond marketing, the data collected provides critical operational intelligence. Heatmaps and footfall analytics allow venue operators to optimise staffing levels based on peak traffic times, improve store layouts to reduce bottlenecks, and measure the impact of physical marketing displays.
Enhancing the Customer Experience
Ultimately, the goal is to use this data to improve the customer experience. Recognising returning loyal customers, understanding their preferences, and providing a seamless, secure connection builds brand affinity and drives repeat visits. As the industry evolves, integrating these capabilities with broader IoT initiatives will become increasingly important. For a broader perspective, review our Internet of Things Architecture: A Complete Guide and explore emerging trends like Wi Fi in Auto: The Complete 2026 Enterprise Guide .
Key Terms & Definitions
Captive Portal
A web page that the user of a public-access network is obliged to view and interact with before full internet access is granted. It acts as the primary interface for the data collection value exchange.
This is the primary user interface for data collection and the point where the value exchange occurs between the venue and the guest.
Walled Garden
A restricted network environment that allows access only to specific, pre-approved websites or IP addresses prior to full authentication.
Crucial for allowing devices to load the splash page assets and communicate with social login providers (like Google or Facebook) before the user has internet access.
RADIUS (Remote Authentication Dial-In User Service)
A networking protocol that provides centralised Authentication, Authorisation, and Accounting (AAA) management for users who connect and use a network service.
The backend engine that validates user credentials collected on the splash page and instructs the network controller to grant or deny internet access.
Progressive Profiling
The practice of collecting user information gradually over multiple interactions, rather than requesting a large amount of data upfront at the initial login.
Used to reduce friction on the initial WiFi login while still building a comprehensive customer profile over time through repeat visits.
First-Party Data
Information a company collects directly from its customers and owns entirely, typically gathered through direct interactions such as WiFi login, purchases, or loyalty programme enrolment.
Highly valuable, accurate, and compliant data that forms the foundation of modern targeted marketing, contrasting with purchased third-party data which is increasingly restricted.
MAC Address Randomisation
A privacy feature in modern operating systems (iOS 14+, Android 10+) where a device uses a temporary, randomised MAC address when scanning for or connecting to networks.
IT teams must understand this to realise why tracking unique visitors based solely on hardware MAC addresses is no longer reliable for cross-session analytics.
RSSI (Received Signal Strength Indicator)
A measurement of the power level present in a received radio signal, expressed in decibels relative to a milliwatt (dBm).
Used by WiFi analytics platforms to estimate the distance between a guest device and multiple access points, enabling location triangulation and footfall tracking.
Webhook
An HTTP callback mechanism that allows a web application to send real-time data to another application as soon as a specific event occurs.
The mechanism used to push data from the WiFi platform to a CRM or marketing automation tool in real-time as soon as a guest authenticates, enabling event-driven marketing workflows.
SSID (Service Set Identifier)
The name assigned to a wireless network, used by devices to identify and connect to a specific WiFi network.
Venues typically configure a dedicated guest SSID separate from their corporate network to isolate guest traffic and apply captive portal policies.
Case Studies
A 200-room hotel needs to increase its direct marketing database but is currently seeing a 60% drop-off rate on its guest WiFi splash page, which asks for Name, Email, Phone Number, Date of Birth, and Room Number.
The IT team should implement a Progressive Profiling strategy. The initial splash page should be simplified to ask only for Email Address and a mandatory Terms of Service checkbox, with an optional Marketing Opt-in. On subsequent visits (recognised via a persistent token), the portal can prompt for one additional piece of information — such as Date of Birth for birthday offers — before granting access. This reduces the initial barrier to entry while building a richer profile over time.
A large retail chain wants to trigger real-time, in-store promotional emails to customers when they enter specific departments, but their current WiFi data is siloed and only exported manually once a week.
The network architecture must be updated to utilise Webhooks. When a guest authenticates on the WiFi and their device is located in a specific zone (determined by AP triangulation using RSSI data), the WiFi platform triggers a Webhook containing the user's ID and location data. This Webhook is received by the marketing automation platform, which immediately evaluates the data against campaign rules and dispatches the targeted email or push notification.
Scenario Analysis
Q1. Your marketing team wants to implement a splash page that requires users to log in using their Google account to capture rich demographic data. What network configuration is absolutely necessary for this to work, and what will happen if it is not in place?
💡 Hint:Consider how the device communicates with Google's authentication servers before it has full internet access.
Show Recommended Approach
You must configure the Walled Garden on the Wireless LAN Controller or Access Point to include the specific IP addresses and domains required by Google's OAuth authentication API (e.g., accounts.google.com, oauth2.googleapis.com). If the device cannot reach Google's servers while in the pre-authenticated state, the OAuth flow will fail silently or display an error, and the user will be unable to log in. This is the single most common cause of failed social login deployments.
Q2. A venue is seeing a high number of 'unique visitors' in their analytics dashboard, but the actual footfall in the physical location is significantly lower. What technical factor is most likely causing this discrepancy, and how should it be addressed?
💡 Hint:Think about how modern mobile operating systems handle network probing to protect user privacy.
Show Recommended Approach
This is most likely caused by MAC address randomisation. Modern iOS and Android devices frequently change their MAC addresses when scanning for networks. If the analytics platform relies solely on MAC addresses to identify unique devices, a single device randomising its MAC address across multiple scans will be counted as multiple unique visitors. The solution is to rely on authenticated sessions — specifically, the persistent user identifier (e.g., email address or hashed email) — for accurate unique visitor counts, rather than hardware MAC addresses.
Q3. You need to ensure that customer data captured via the guest WiFi is immediately available in your Salesforce CRM to trigger a welcome email within 30 seconds of a guest connecting. Which integration method is most appropriate, and why is a nightly batch export insufficient?
💡 Hint:Consider the difference between scheduled data synchronisation and event-driven architecture.
Show Recommended Approach
The most appropriate method is using Webhooks configured on the WiFi platform to trigger on the authentication event. A Webhook sends an HTTP POST request with the user's data payload directly to the Salesforce API the moment authentication succeeds, achieving near-real-time data transfer. A nightly batch export is insufficient because it introduces a latency of up to 24 hours, making it impossible to trigger timely, contextually relevant communications like a welcome email or an in-venue offer.



