How to Configure NAC Policies for VLAN Steering in Cisco Meraki
This authoritative guide provides IT leaders, network architects, and venue operations directors with a practical, step-by-step framework for configuring NAC policies and VLAN steering in Cisco Meraki environments. It covers 802.1X implementation, IoT device isolation via MAC Authentication Bypass, and seamless integration with Purple's guest WiFi analytics platform to ensure secure, compliant, and high-performance network segmentation across hospitality, retail, and public-sector deployments.
Listen to this guide
View podcast transcript
- Executive Summary
- Technical Deep-Dive
- The Architecture of Dynamic VLAN Steering
- Authentication Mechanisms
- Implementation Guide
- Step 1: Plan Your VLAN Architecture
- Step 2: Configure the Switch Infrastructure
- Step 3: Configure the Meraki SSID for 802.1X
- Step 4: Enable RADIUS Override for VLAN Tagging
- Step 5: Configure Guest Access with Purple
- Best Practices
- Troubleshooting & Risk Mitigation
- Common Failure Modes
- ROI & Business Impact
- Listen to the Briefing
Executive Summary
For enterprise venues — from high-density stadiums to sprawling hospitality complexes — a flat network is a compromised network. Broadcasting multiple SSIDs to segment traffic degrades RF performance, wastes valuable airtime, and creates an administrative burden that scales poorly across multi-site deployments. The modern standard is dynamic segmentation: broadcasting a single secure SSID and relying on Network Access Control (NAC) to automatically profile, authenticate, and steer devices into the correct VLAN.
This guide provides senior IT architects and operations directors with a practical blueprint for configuring NAC policies for VLAN steering in Cisco Meraki. We bypass the academic theory to focus on deployment realities: implementing IEEE 802.1X for corporate devices, utilizing MAC Authentication Bypass (MAB) for headless IoT systems, and integrating seamlessly with Guest WiFi platforms like Purple to ensure secure, compliant access across Retail , Hospitality , and other enterprise environments. By mastering these configurations, organisations can mitigate security risks, ensure PCI DSS compliance, and optimise network throughput — all from a single, centrally managed SSID.
Technical Deep-Dive
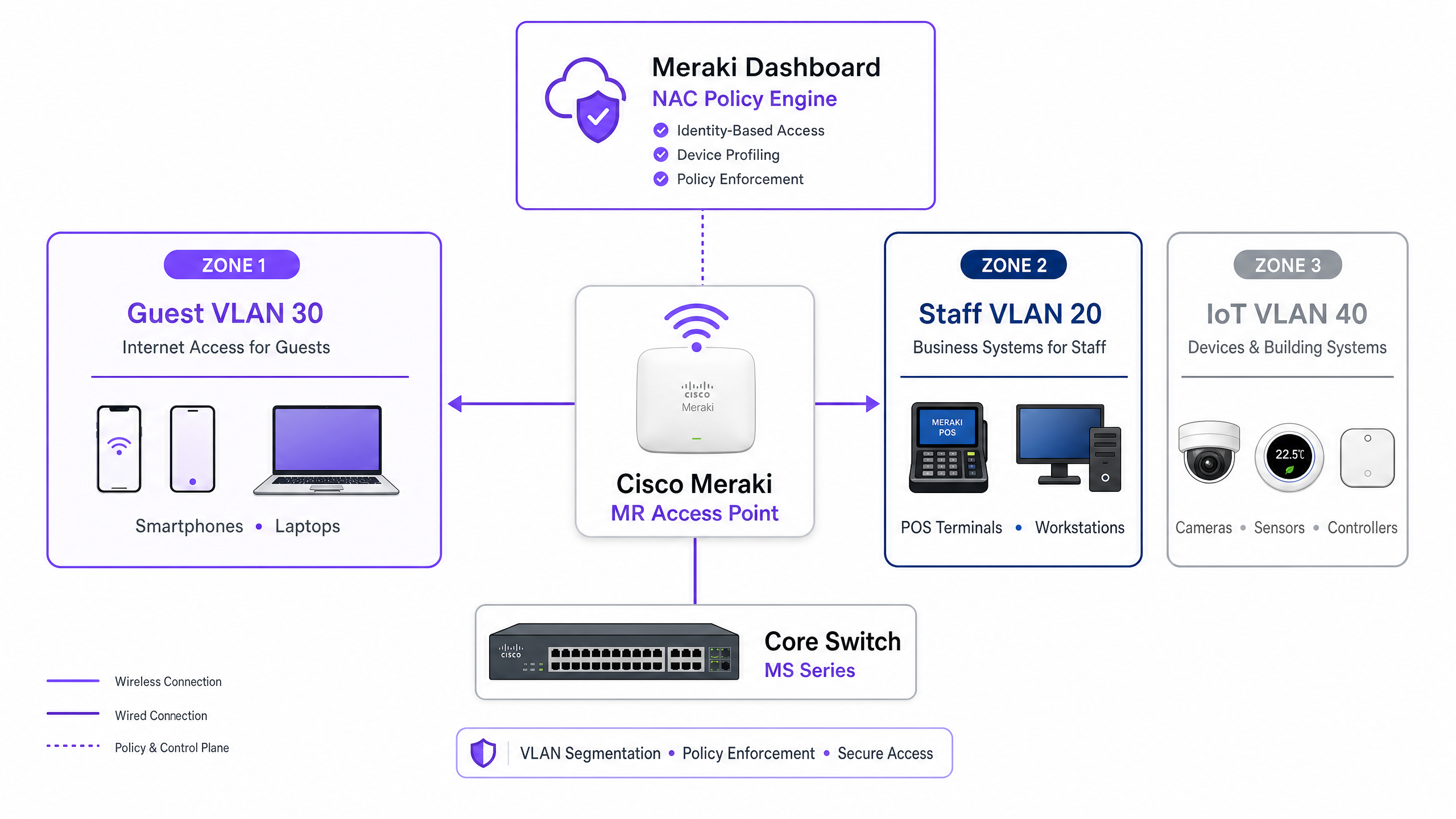
The Architecture of Dynamic VLAN Steering
VLAN steering in a Meraki environment relies on the interaction between three core components: the Meraki Access Point (acting as the authenticator), the client device (the supplicant), and the NAC/RADIUS server (the authentication server). This three-party model is defined by the IEEE 802.1X standard and forms the backbone of any enterprise-grade access control deployment.
When a device associates with the network, the AP intercepts the traffic and forwards an Access-Request to the RADIUS server. Upon successful authentication, the RADIUS server responds with an Access-Accept message. Crucially, for VLAN steering to occur, this message must include specific IETF standard RADIUS attributes that instruct the AP on which VLAN to apply:
| RADIUS Attribute | ID | Value | Purpose |
|---|---|---|---|
| Tunnel-Type | 64 | 13 (VLAN) | Specifies the tunnelling protocol |
| Tunnel-Medium-Type | 65 | 6 (802) | Specifies the transport medium |
| Tunnel-Private-Group-ID | 81 | e.g., 20 |
Specifies the target VLAN ID |
When the Meraki AP receives these attributes, it dynamically tags the client's traffic with the specified VLAN ID before forwarding it to the switchport. This process is transparent to the end user and completes within milliseconds of association.
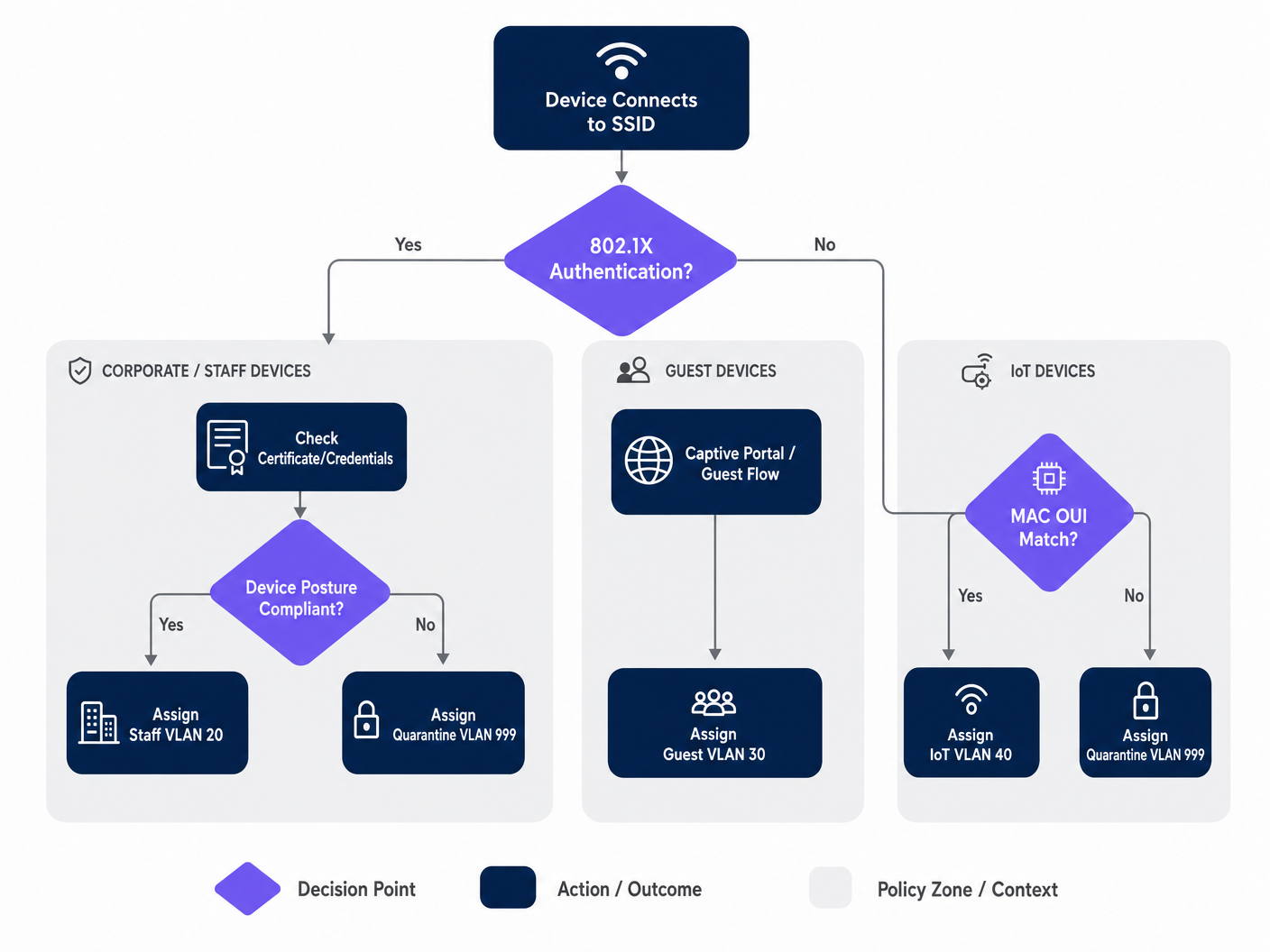
Authentication Mechanisms
Enterprise networks typically require a multi-tiered approach to authentication, as the device population in any given venue is heterogeneous. The three primary mechanisms are:
IEEE 802.1X (EAP-TLS or PEAP) is the gold standard for corporate and staff devices. Authentication is based on digital certificates (EAP-TLS) or secure credentials (PEAP-MSCHAPv2), providing robust encryption and identity validation. This is the recommended approach for any device managed by the organisation's MDM platform.
MAC Authentication Bypass (MAB) is essential for headless devices — IP cameras, POS terminals, building management sensors, and smart TVs — that cannot run an 802.1X supplicant. The MAC address is used as the identifier. While less secure than certificate-based authentication (MAC addresses can be spoofed), MAB combined with strict VLAN ACLs provides an acceptable security posture for isolated IoT segments. For a comprehensive treatment of this topic, refer to our guide on Managing IoT Device Security with NAC and MPSK .
Captive Portal Authentication is used for guest access. Devices are placed in a restricted pre-authentication state until the user completes a login flow — typically social login, email registration, or a simple click-through — hosted by a platform like Purple. This captures first-party data while steering the device into an isolated guest VLAN.
Implementation Guide
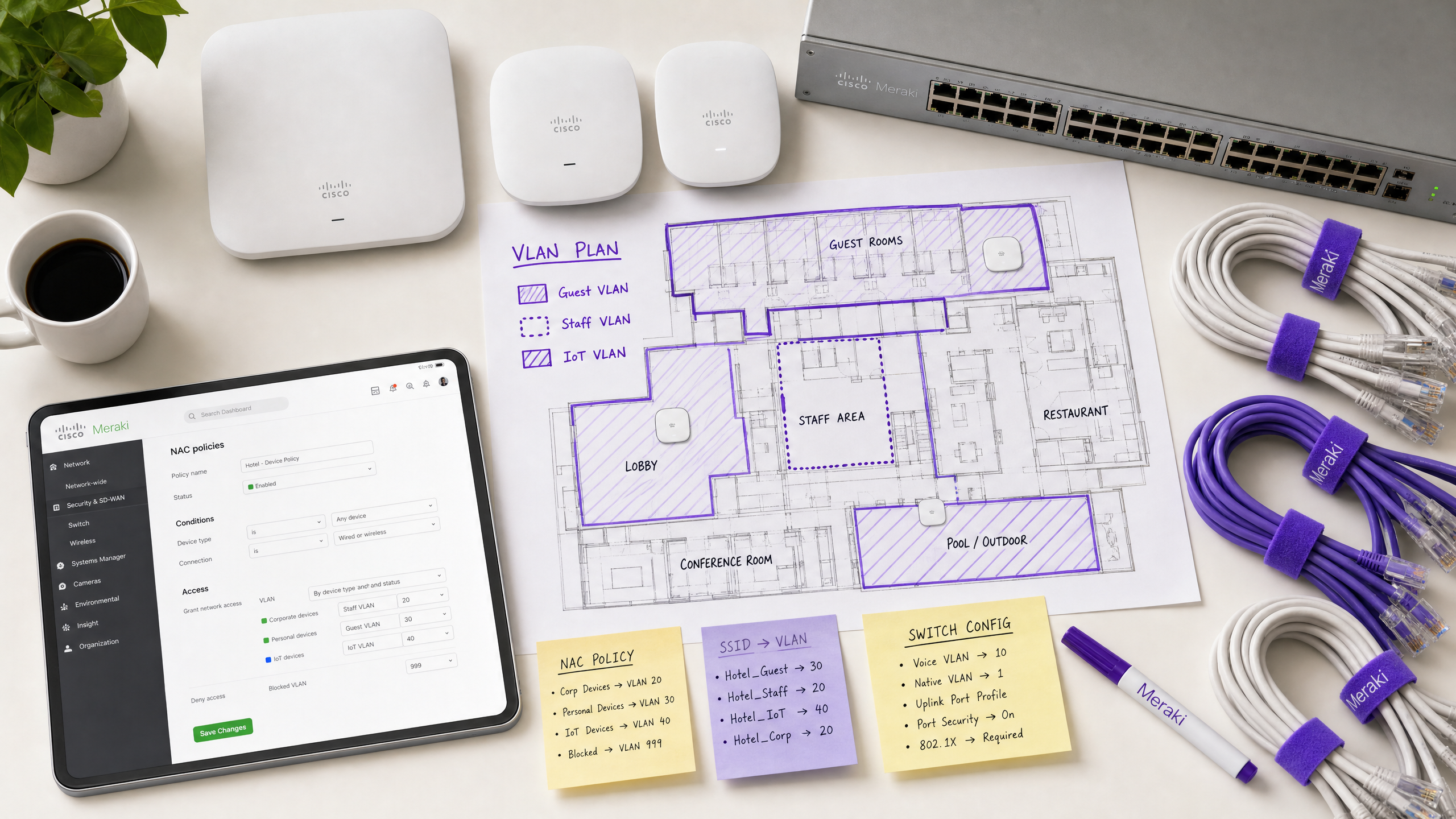
Step 1: Plan Your VLAN Architecture
Before touching the Meraki Dashboard, define your VLAN segmentation strategy. A typical enterprise venue deployment uses the following structure:
| VLAN ID | Name | Purpose | Authentication Method |
|---|---|---|---|
| 10 | Management | Network infrastructure | Static |
| 20 | Staff | Corporate devices, internal systems | 802.1X (EAP-TLS) |
| 30 | Guest | Visitor internet access | Captive Portal (Purple) |
| 40 | IoT | Cameras, sensors, smart devices | MAB |
| 50 | POS | Payment terminals (PCI scope) | 802.1X (Certificate) |
| 999 | Quarantine | Failed authentication, unknown devices | None |
Step 2: Configure the Switch Infrastructure
Before configuring the wireless settings, the wired infrastructure must be prepared. The switchports connecting to the Meraki APs must be configured as trunk ports, allowing all VLANs that the AP might dynamically assign. This is the single most common oversight in failed deployments.
In the Meraki Dashboard, navigate to Switch > Monitor > Switch ports, select the ports connected to your APs, set the Type to Trunk, configure the Native VLAN (typically your management VLAN), and in the Allowed VLANs field, specify all potential client VLANs explicitly (e.g., 20,30,40,50,999).
Step 3: Configure the Meraki SSID for 802.1X
Navigate to Wireless > Configure > Access control and select the target SSID. Under Network access, select Enterprise with 802.1X. Scroll down to the RADIUS servers section and add your NAC server details: IP address, port (default 1812 for authentication, 1813 for accounting), and the shared secret. For redundancy, add a secondary RADIUS server.
Step 4: Enable RADIUS Override for VLAN Tagging
This is the critical step that enables the Meraki AP to accept VLAN assignments from the NAC server. On the same Access control page, scroll to the Addressing and traffic section. Set Client IP assignment to Bridge mode — this ensures clients receive IP addresses from the local DHCP server on their assigned VLAN, not from the AP's NAT. Under VLAN tagging, select Use VLAN tag from RADIUS.
Step 5: Configure Guest Access with Purple
For guest networks, create a separate SSID configured with an open association and a captive portal integration. Set Network access to Open (no encryption) and configure the Splash page to point to your Purple portal URL. Set the VLAN tagging to assign all pre-authenticated traffic to a dedicated, isolated guest VLAN (e.g., VLAN 30) and enable Client isolation to prevent lateral movement between guest devices. Purple's WiFi Analytics platform will handle the authentication flow and data capture.
Best Practices
Implement a Fail-Closed Posture with Critical Authentication VLANs. If the RADIUS server becomes unreachable, do not fail open and grant full network access. Configure a critical authentication VLAN that provides basic internet connectivity but blocks access to all internal resources until the NAC server is restored. This is especially important for retail environments where POS terminals must continue to process payments even during a RADIUS outage.
Enable Fast BSS Transition (802.11r) for Seamless Roaming. Dynamic VLAN assignment can introduce latency during roaming as the device must re-authenticate at each AP. Enabling 802.11r ensures seamless handoffs for voice and video applications across the venue. This is non-negotiable for hospitality environments where guests move continuously through the property. Understanding Wi Fi Frequencies: A Guide to Wi-Fi Frequencies in 2026 can also help optimise channel planning for dense deployments.
Segment IoT Traffic Aggressively. Never mix IoT devices with corporate or guest traffic. Use MAB to identify these devices and steer them into dedicated VLANs with strict Layer 3 firewall rules permitting only the specific ports and destinations required for device operation. A compromised IP camera should never be able to reach your POS network or corporate file servers.
Enforce WPA3 on Corporate SSIDs. Where device compatibility allows, configure corporate SSIDs to use WPA3-Enterprise. This provides stronger encryption and eliminates vulnerabilities associated with WPA2 PMKID attacks.
Troubleshooting & Risk Mitigation
Common Failure Modes
Clients Fail to Obtain an IP Address. This is almost always a switchport configuration issue. Verify that the switchport connected to the AP is configured as a trunk and that the dynamically assigned VLAN is allowed on that trunk. Also, verify the DHCP server has an active scope for that VLAN and that the DHCP relay agent (if applicable) is configured correctly.
Authentication Timeouts. If devices are timing out during the 802.1X handshake, check the network latency between the Meraki APs and the RADIUS server. High latency can cause EAP timers to expire. The Meraki Dashboard's Event Log will show 8021x_auth_timeout events if this is occurring.
Incorrect VLAN Assignment. Use the Meraki Dashboard's Event Log to view the RADIUS Access-Accept messages. Verify that the NAC server is sending the correct Tunnel-Private-Group-ID attribute. If it is missing or incorrect, the issue lies within the NAC policy configuration, not the Meraki AP. Most NAC platforms (Cisco ISE, ClearPass) provide detailed RADIUS authentication logs that will show exactly what attributes were returned.
MAC Randomization Breaking MAB. Modern iOS and Android devices randomize their MAC addresses by default. For guest networks managed by Purple, this is handled gracefully through the captive portal flow — identity is established by the user's login, not the MAC address. For IoT devices using MAB, ensure the actual hardware MAC address is registered in the endpoint database, as these devices do not randomize.
ROI & Business Impact
Implementing NAC-driven VLAN steering delivers measurable business value for enterprise venues across multiple dimensions:
| Business Outcome | Mechanism | Measurable Impact |
|---|---|---|
| Reduced Operational Overhead | Fewer SSIDs to manage | 60-70% reduction in SSID count |
| Enhanced Security Posture | Automated micro-segmentation | Contained blast radius for breaches |
| Compliance Enablement | Identity-based access control | PCI DSS, GDPR, ISO 27001 alignment |
| Guest Data Capture | Purple captive portal integration | First-party data at scale |
| Network Performance | Reduced management frame overhead | Improved throughput in high-density areas |
For Healthcare and Transport operators, the compliance argument alone justifies the investment. The ability to demonstrate that patient records are on a strictly isolated VLAN, or that ticketing systems are segregated from public WiFi, is a material risk mitigation that satisfies both internal audit and external regulatory requirements.
For hospitality and retail operators, the integration with Purple's guest WiFi platform transforms the guest network from a cost centre into a revenue-generating asset. Every authenticated guest session becomes a data point, feeding into marketing automation, loyalty programmes, and venue analytics — all while the underlying NAC policy ensures that guest traffic never touches internal systems.
Listen to the Briefing
For a deeper dive into deployment strategies and common pitfalls, listen to our 10-minute technical briefing podcast:
Key Definitions
Network Access Control (NAC)
A security architecture that enforces policy on devices seeking to access network resources, typically evaluating identity, device posture, and compliance status before granting access and assigning a network segment.
IT teams deploy NAC platforms (such as Cisco ISE or Aruba ClearPass) to act as the central policy engine, deciding which VLAN a device belongs in based on who or what it is, and what state it is in.
VLAN Steering (Dynamic VLAN Assignment)
The process of automatically assigning a client device to a specific Virtual Local Area Network (VLAN) upon successful authentication, regardless of which physical port or SSID they connect to.
Essential for high-density venues to reduce the number of broadcasted SSIDs while maintaining strict security segmentation between guest, staff, and IoT device populations.
IEEE 802.1X
An IEEE standard for port-based network access control that provides an authentication mechanism to devices wishing to attach to a LAN or WLAN, using the Extensible Authentication Protocol (EAP) framework.
The gold standard for authenticating corporate laptops and staff smartphones, ensuring only verified users with valid credentials or certificates can access internal resources.
MAC Authentication Bypass (MAB)
A fallback authentication method where a device's MAC address is used as its identity credential when it cannot support 802.1X. The MAC address is sent to the RADIUS server as both the username and password.
Crucial for onboarding headless IoT devices — printers, cameras, sensors, and POS terminals — onto a secure, segmented network without requiring user intervention.
RADIUS (Remote Authentication Dial-In User Service)
A networking protocol that provides centralised Authentication, Authorisation, and Accounting (AAA) management for users and devices connecting to a network service.
The protocol used by the Meraki AP to communicate with the NAC server. The AP sends Access-Request messages; the NAC server responds with Access-Accept (including VLAN attributes) or Access-Reject.
Captive Portal
A web page that a user of a public-access network is obliged to view and interact with before full network access is granted. Typically used for terms acceptance, login, or data capture.
The primary method for onboarding guest users in hospitality, retail, and public-sector environments. Platforms like Purple host the captive portal, capturing analytics data and enforcing terms of service.
Client Isolation
A wireless security feature that prevents devices connected to the same SSID or VLAN from communicating directly with each other, forcing all traffic through the gateway.
A mandatory setting for Guest VLANs to prevent malicious actors from scanning or attacking other guests' devices. Should be enabled on any SSID where untrusted devices are expected.
Fast BSS Transition (802.11r)
An IEEE 802.11 amendment that enables fast and secure handoffs from one access point to another by pre-caching authentication keys, reducing roaming latency from hundreds of milliseconds to under 50ms.
Must be enabled when using 802.1X and dynamic VLAN assignment in venues where users are mobile, to prevent voice calls or video streams from dropping as users move between access points.
EAP-TLS (Extensible Authentication Protocol - Transport Layer Security)
A mutual authentication method within the 802.1X framework that uses digital certificates on both the client and the authentication server, providing the highest level of security for wireless authentication.
The recommended authentication method for PCI DSS-scoped devices and any environment where credential theft is a significant risk. Requires a PKI infrastructure to issue and manage client certificates.
Worked Examples
A 400-room hotel needs to deploy a secure wireless network. They require staff to access internal booking systems securely, guests to access the internet via a branded captive portal, and smart TVs in the rooms to connect to a local media server. They want to minimise SSID broadcast overhead to ensure optimal performance in high-density areas.
The IT team should deploy two SSIDs. SSID 1: 'Hotel_Secure' configured for 802.1X. Staff authenticate using EAP-TLS with corporate certificates issued by the hotel's PKI. The NAC server (Cisco ISE) recognises the staff identity and returns RADIUS attributes assigning them to VLAN 20 (Staff), which has full access to the PMS and booking systems. The Smart TVs, lacking 802.1X capabilities, are profiled using MAC Authentication Bypass (MAB). The NAC server recognises the TV MAC OUI prefixes and assigns them to VLAN 40 (IoT), which has ACLs permitting access only to the media server on port 8080 and the internet. SSID 2: 'Hotel_Guest' configured as Open with a Purple captive portal. Guests connect, are redirected to the Purple splash page, and upon successful social login or email registration, are assigned to VLAN 30 (Guest) with client isolation enabled. The Purple platform captures first-party data for the hotel's CRM and marketing automation.
A retail chain is rolling out new wireless Point-of-Sale (POS) terminals across 50 locations. These devices must be strictly segmented to comply with PCI DSS requirements. However, the IT team is concerned about what happens if the central RADIUS server goes offline during peak trading hours.
The POS terminals should connect to an 802.1X-enabled SSID, utilising certificate-based authentication (EAP-TLS) to ensure strong identity validation. The NAC policy will steer these devices into a dedicated, highly restricted POS VLAN (VLAN 50) with Layer 3 firewall rules permitting traffic only to the payment gateway IPs on the required ports. To mitigate the risk of RADIUS server failure, the IT team must configure a Critical Authentication VLAN on the Meraki access points. If the AP cannot reach the RADIUS server within the configured timeout, it will automatically drop the POS terminals into this critical VLAN. This VLAN should be configured with strict ACLs that allow traffic only to the essential payment processing gateways, ensuring transactions can continue while blocking all other network access. A secondary RADIUS server at each location provides an additional layer of redundancy.
Practice Questions
Q1. A hospital IT director reports that newly installed wireless IP cameras are failing to connect to the 'Med_Secure' SSID, which is configured for 802.1X. The cameras do not support certificate-based authentication and have no user interface. How should the network architecture be adjusted to securely onboard these devices?
Hint: Consider how headless devices are profiled and authenticated when they cannot run an 802.1X supplicant.
View model answer
The IT team must utilise MAC Authentication Bypass (MAB) on the NAC server. The cameras' MAC addresses should be added to the endpoint database and profiled as 'IoT_Camera'. When a camera attempts to connect, the NAC server will use the MAC address as the authentication credential and return the RADIUS attributes to steer the camera into an isolated IoT VLAN. Strict Layer 3 ACLs should be applied to this VLAN, permitting traffic only to the camera management server and blocking all other internal network access. The hospital should also consider using DHCP fingerprinting as a secondary profiling method to verify the device type matches the expected profile for the registered MAC address.
Q2. During a network audit at a retail chain, it is discovered that staff laptops on the dynamic VLAN are successfully authenticating via 802.1X (the Event Log shows Access-Accept messages with the correct VLAN ID) but are not receiving IP addresses. Guest devices on a separate SSID are functioning normally. What is the most likely configuration error and how would you resolve it?
Hint: The authentication is succeeding — the issue is in the data path after the VLAN tag is applied.
View model answer
The most likely issue is that the physical switchport connecting the Meraki AP to the core switch is not configured correctly. While the AP is successfully authenticating the client and tagging the traffic with the Staff VLAN ID, the switchport is likely configured as an access port (or a trunk port that is missing the Staff VLAN in its allowed list). The switchport must be configured as a trunk, and the dynamically assigned Staff VLAN must be explicitly listed in the allowed VLANs. The IT team should navigate to Switch > Monitor > Switch ports in the Meraki Dashboard, select the port connected to the AP, verify it is set to Trunk type, and confirm the Staff VLAN ID is included in the Allowed VLANs field.
Q3. A stadium wants to offer seamless WiFi to 50,000 fans during events while securely connecting point-of-sale terminals and digital signage. The current network team proposes broadcasting five different SSIDs to separate the traffic. Why is this a poor design for a high-density environment, and what is the recommended architecture?
Hint: Consider the impact of management frames on wireless airtime in a high-density environment.
View model answer
Broadcasting five SSIDs creates excessive management frame overhead — each SSID requires its own beacon frames broadcast at regular intervals by every access point. In a high-density environment like a stadium with hundreds of APs, this management frame overhead consumes a significant proportion of available airtime, directly reducing the throughput available for user data. The recommended approach is to broadcast a maximum of two SSIDs: one Open SSID with a Purple captive portal for the 50,000 fans, steering them to a Guest VLAN with client isolation; and one 802.1X-enabled secure SSID for all corporate devices. The NAC policy will then dynamically steer POS terminals into a PCI-compliant VLAN and digital signage into an IoT VLAN based on their identity, without requiring additional SSIDs.