How to Create a WiFi Splash Page: Design, Content and Best Practices
This comprehensive guide explores the architecture, design principles, and deployment strategies required to build an effective WiFi splash page. It provides actionable insights for IT leaders on integrating captive portals with network infrastructure while ensuring GDPR compliance and maximising first-party data capture.
🎧 Listen to this Guide
View Transcript
- Executive Summary
- Technical Deep-Dive: Captive Portal Architecture
- Redirection Mechanisms
- Deployment Models: Cloud vs. On-Premise
- Implementation Guide: Designing the Splash Page
- Mobile-First Design and the Captive Network Assistant (CNA)
- Essential UI Components
- Best Practices: Compliance and Data Security
- GDPR Compliant Consent Mechanisms
- Security Standards
- Troubleshooting & Risk Mitigation
- ROI & Business Impact
Executive Summary
For enterprise IT teams and venue operations directors, deploying guest WiFi is no longer just about providing internet access—it is about establishing a secure, compliant, and commercially valuable digital touchpoint. The WiFi splash page, served via a captive portal, is the critical interface where this exchange occurs. A well-architected splash page transforms anonymous network traffic into verified first-party data, enabling targeted engagement and operational analytics.
This technical reference guide details how to create a WiFi splash page that balances user experience with stringent security and compliance requirements. We will explore the underlying captive portal architecture, evaluating the merits of cloud-hosted versus on-premise deployments. We will also define the essential design components required to minimise authentication friction, particularly on mobile devices, which account for the vast majority of guest connections.
Furthermore, this guide addresses the critical mandate of GDPR compliance, outlining how to implement explicit consent mechanisms that withstand regulatory scrutiny. By integrating these technical and design principles, organisations across Retail , Healthcare , Hospitality , and Transport can deploy robust Guest WiFi solutions that deliver measurable ROI while mitigating data privacy risks.
Technical Deep-Dive: Captive Portal Architecture
Understanding how to create a WiFi splash page requires a solid grasp of the underlying captive portal architecture. A captive portal is a network access control mechanism that intercepts HTTP/HTTPS traffic from unauthenticated clients and redirects them to a specific web page—the splash page—before granting access to the broader internet.
Redirection Mechanisms
The interception and redirection process typically relies on one of two primary methods at the gateway or wireless LAN controller (WLC) level:
- DNS Redirection: When an unauthenticated client attempts to resolve a domain name, the gateway intercepts the DNS request and returns the IP address of the captive portal server instead of the actual destination.
- HTTP 302 Redirects: The gateway intercepts HTTP GET requests from unauthenticated clients and responds with an HTTP 302 Found status code, directing the client's browser to the captive portal URL.
Simultaneously, the network infrastructure employs "walled garden" or pre-authentication access control lists (ACLs). These firewall rules block all outbound traffic except for essential services (like DHCP and DNS) and traffic destined for the captive portal server and any required authentication identity providers (e.g., Google or Facebook OAuth servers).
Deployment Models: Cloud vs. On-Premise
When architecting a splash page solution, IT leaders must choose between two primary deployment models. For a detailed comparison, refer to our guide on Cloud-Based vs. On-Premise Captive Portal: Which Is Right for Your Business? .
- Cloud-Hosted Captive Portal: The splash page and authentication backend are hosted on a vendor's infrastructure (such as Purple's platform). The local WLC or gateway is configured to redirect clients to this external URL via RADIUS (Remote Authentication Dial-In User Service). This model is highly scalable, offers centralized management across multiple sites, and ensures high availability without relying on local server hardware.
- On-Premise Captive Portal: The portal software runs on local hardware or directly on the WLC. While this offers complete local control and can function even if the WAN link is down (though internet access would still be unavailable), it requires significant maintenance overhead and lacks the cross-site analytics capabilities inherent to cloud solutions.
For most modern enterprise deployments, a cloud-hosted architecture is recommended to facilitate centralized data capture and seamless integration with WiFi Analytics platforms.
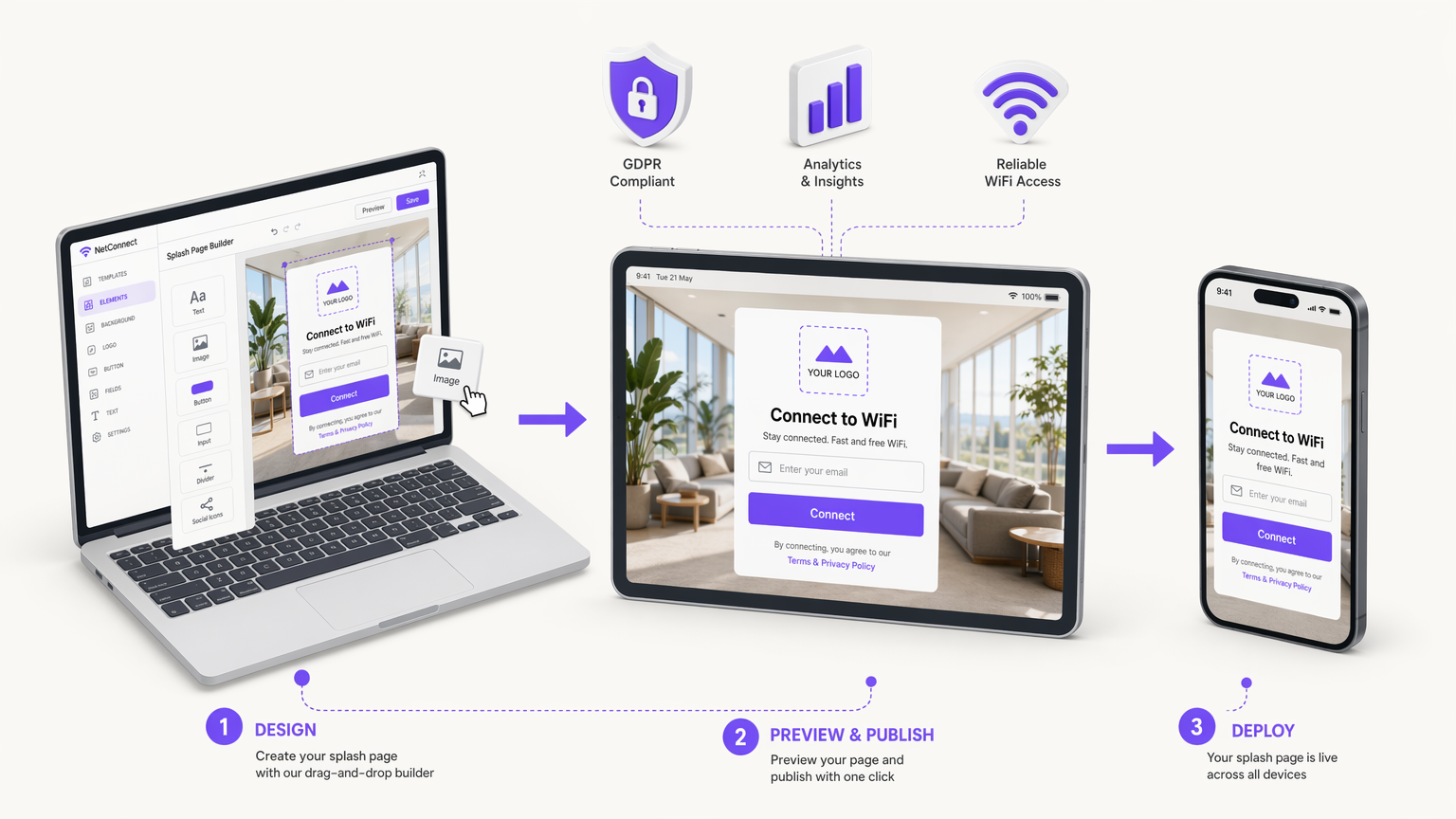
Implementation Guide: Designing the Splash Page
The design of the splash page directly impacts connection rates and data quality. A poorly designed page introduces friction, leading to high abandonment rates. When considering how to make a splash page, adhere to the following principles.
Mobile-First Design and the Captive Network Assistant (CNA)
Over 70% of guest WiFi connections originate from smartphones. Therefore, the splash page must be rigorously optimized for mobile viewports (starting at 320px width). However, mobile devices rarely use standard browsers for captive portal authentication.
Instead, operating systems employ pseudo-browsers, such as Apple's Captive Network Assistant (CNA) or Android's Captive Portal Login. These environments have restricted capabilities: they often lack persistent cookie support, have limited JavaScript execution, and do not support multiple tabs. Consequently, the authentication flow must be server-side rendered and minimize reliance on complex client-side scripting.
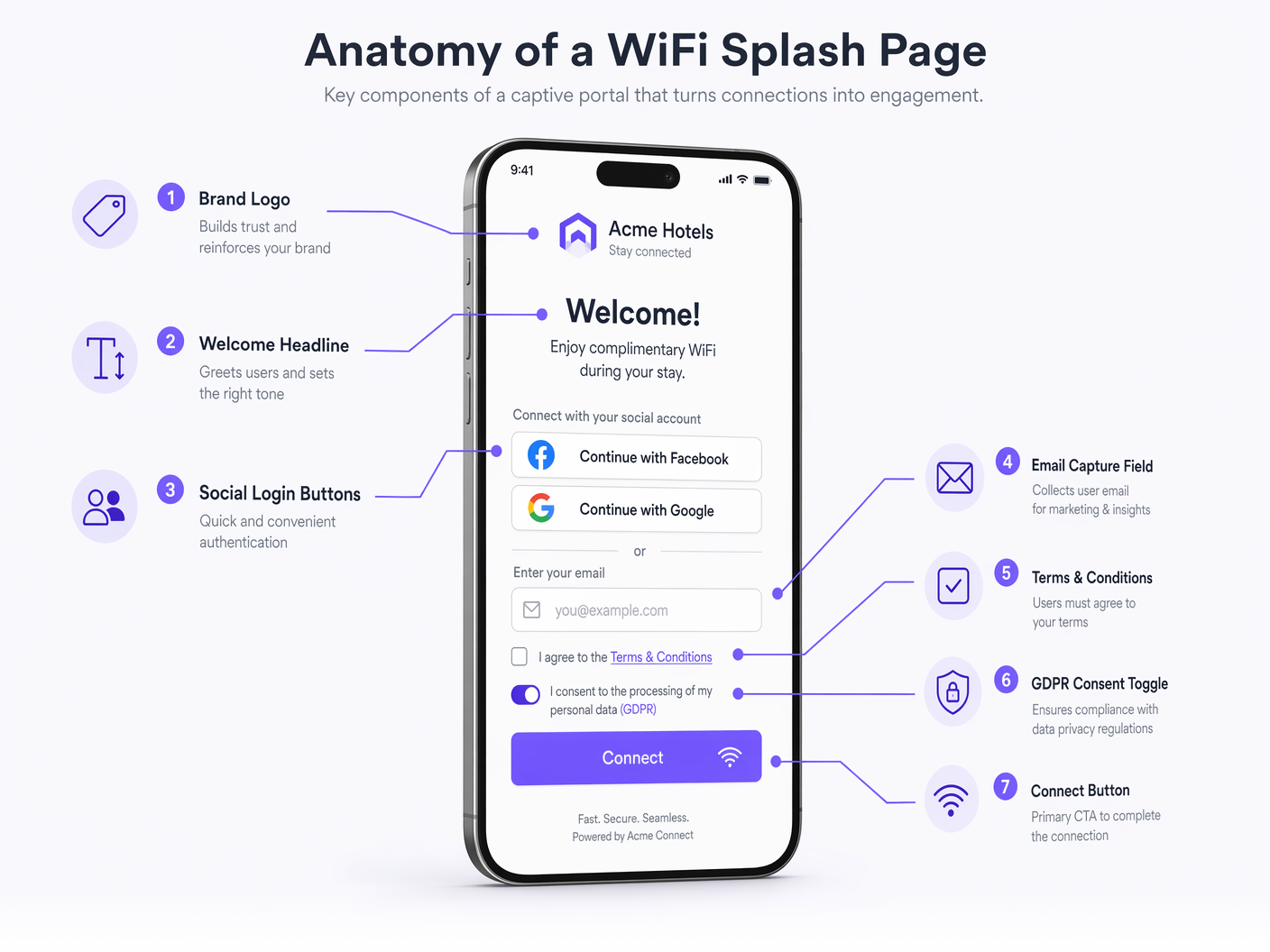
Essential UI Components
A high-converting splash page should include the following elements:
- Brand Identity: Prominent display of the corporate logo and adherence to brand color palettes. This establishes trust and verifies the network's legitimacy.
- Clear Value Proposition: A concise headline (e.g., "Connect to Complimentary High-Speed WiFi").
- Authentication Methods: Offer a balance between data collection and user convenience.
- Email Capture: The standard for building a marketing database.
- Social OAuth (Google, Facebook): Reduces friction and provides verified demographic data, but requires configuring walled garden entries for the respective identity providers.
- Click-Through: Minimal friction but yields zero data; generally discouraged for commercial deployments.
- Prominent Call-to-Action (CTA): The "Connect" button must be highly visible and accessible without scrolling (above the fold) on mobile devices.
- Post-Authentication Redirect: Upon successful authentication, redirect the user to a high-value landing page, such as a promotional offer, an app download link, or a venue map, rather than leaving them on a generic success screen.
Best Practices: Compliance and Data Security
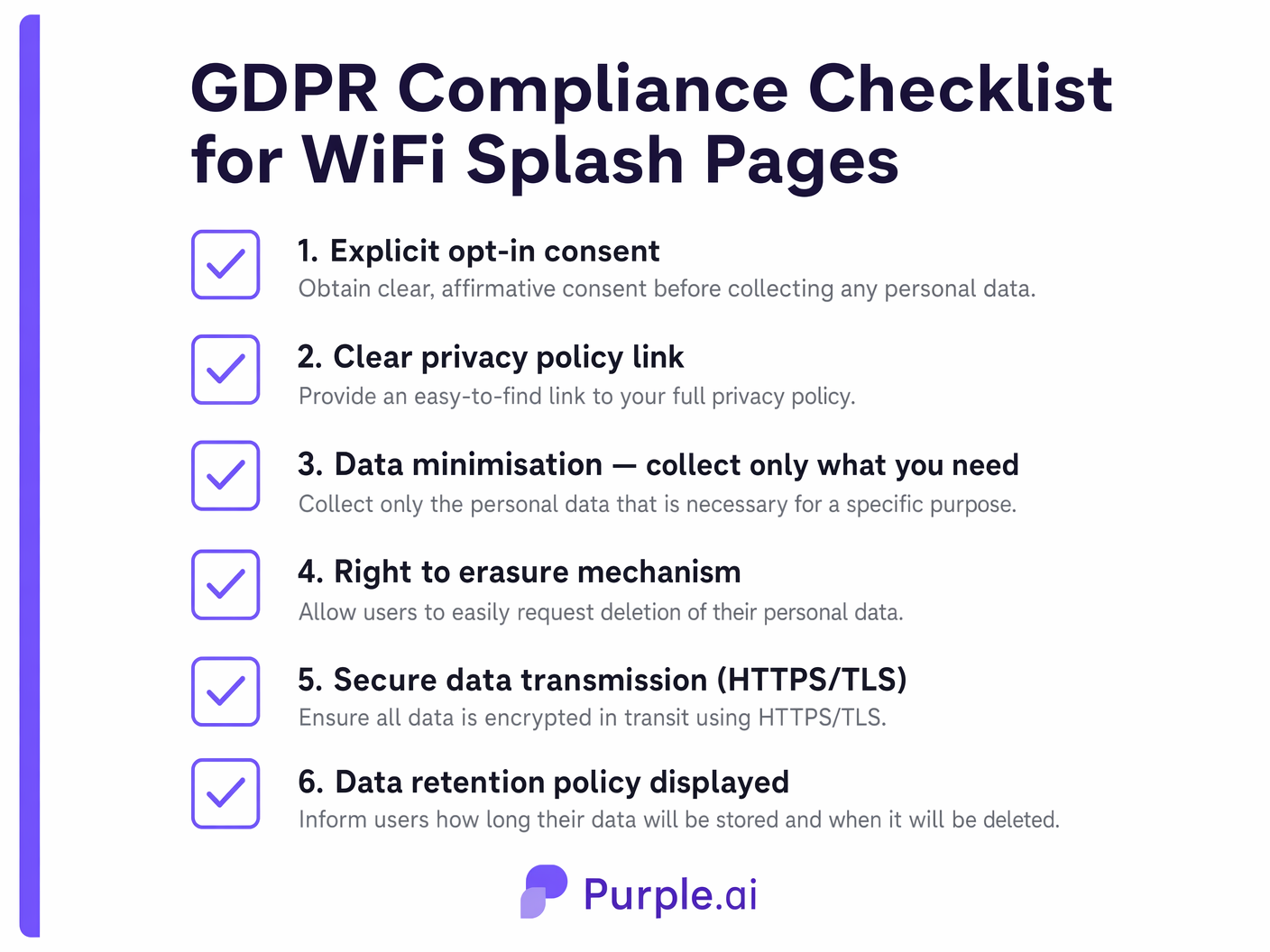
When determining how to setup a WiFi splash page, legal compliance and data security are paramount. The splash page is the primary interface for securing user consent under frameworks like the General Data Protection Regulation (GDPR) and the California Consumer Privacy Act (CCPA).
GDPR Compliant Consent Mechanisms
Under GDPR, consent for processing personal data (especially for marketing purposes) must be freely given, specific, informed, and unambiguous.
- Granular Opt-Ins: You cannot bundle acceptance of the Terms of Service (which is required for network access) with consent for marketing communications. These must be separate checkboxes.
- No Pre-Ticked Boxes: Marketing opt-in checkboxes must be unticked by default. The user must take an affirmative action to consent.
- Clear Privacy Policy: A direct, accessible link to the organization's privacy policy must be provided, detailing what data is collected, how it is used, and how long it is retained.
- Audit Trails: The captive portal backend must log the timestamp, IP address, and exact version of the terms accepted by the user to provide a verifiable audit trail of consent.
Security Standards
- HTTPS/TLS Encryption: The splash page must be served over HTTPS. Modern OS CNAs will often block or display severe warnings for HTTP captive portals. Ensure that a valid, trusted TLS certificate is installed on the portal server.
- Data Minimization: Only collect data that is strictly necessary for the stated purpose. If you only need an email address for a newsletter, do not mandate the collection of a phone number or physical address.
Troubleshooting & Risk Mitigation
Even well-designed splash pages can encounter deployment issues. IT teams should proactively mitigate the following common failure modes:
- Certificate Errors: If the gateway intercepts traffic and redirects to the portal using a self-signed or invalid certificate, the user's browser will present a security warning, effectively halting the connection process. Always use certificates from trusted Certificate Authorities (CAs).
- Walled Garden Misconfiguration: If the ACLs do not permit access to necessary external resources (e.g., CSS files hosted on a CDN, or OAuth authentication servers), the splash page will render incorrectly or authentication will fail. Regularly audit walled garden configurations.
- CNA Silent Failures: Because CNAs have limited functionality, complex JavaScript-heavy pages may simply fail to load or process forms without providing an error message to the user. Keep the HTML/CSS lightweight and rely on server-side processing.
ROI & Business Impact
The deployment of a strategic WiFi splash page shifts guest WiFi from a cost center to a revenue-enabling asset. By capturing verified user data, organizations can fuel CRM systems and marketing automation platforms.
For example, a retail chain can analyze connection data to measure dwell time and return visit frequency, correlating these metrics with targeted email campaigns initiated via the splash page. Similarly, hospitality venues can utilize the post-authentication redirect to drive immediate ancillary revenue through restaurant bookings or spa reservations. The integration of the captive portal with comprehensive WiFi Analytics provides the actionable intelligence necessary to justify the infrastructure investment and continuously optimize the guest experience.
Key Terms & Definitions
Captive Portal
A web page that a user of a public access network is obliged to view and interact with before access is granted.
The fundamental mechanism that intercepts network traffic and serves the splash page.
Splash Page
The specific user interface presented by the captive portal, used for authentication, branding, and data capture.
The digital storefront of the guest WiFi experience; the primary touchpoint for marketing and compliance.
Walled Garden
A restricted environment that controls the user's access to web content and services prior to full network authentication.
Essential for allowing the splash page to load external assets (like logos or CSS) and facilitating social OAuth logins before the user has full internet access.
Captive Network Assistant (CNA)
A limited pseudo-browser built into mobile operating systems (like iOS and Android) that automatically detects captive portals and displays the splash page.
IT teams must design splash pages specifically to function within the restricted capabilities of CNAs to ensure a smooth mobile connection experience.
HTTP 302 Redirect
An HTTP response status code indicating that the requested resource has been temporarily moved to a different URI.
One of the primary technical methods used by network gateways to intercept unauthenticated traffic and route it to the captive portal server.
RADIUS (Remote Authentication Dial-In User Service)
A networking protocol that provides centralized Authentication, Authorization, and Accounting (AAA) management for users who connect and use a network service.
Used to communicate between the local wireless controller and the cloud-hosted captive portal backend to verify user credentials and authorize network access.
MAC Authentication Bypass (MAB)
A mechanism that uses the MAC address of a device as its identity for network access control.
Often used in conjunction with captive portals to allow returning devices to bypass the splash page and connect automatically based on their previously registered MAC address.
First-Party Data
Information a company collects directly from its customers and owns entirely.
The primary business driver for deploying a splash page; capturing verified emails and demographics directly from guests rather than relying on third-party aggregators.
Case Studies
A 200-room boutique hotel needs to implement a new guest WiFi solution. The marketing director wants to capture email addresses for a loyalty program, but the IT manager is concerned about GDPR compliance and the impact on the connection experience for international guests using various mobile devices.
The hotel should deploy a cloud-hosted captive portal integrated with their existing WLC. The splash page design must be mobile-first, utilizing server-side rendering to ensure compatibility with all iOS and Android CNAs. For authentication, the page will present a simple form requesting Name and Email Address. Crucially, the form will include two separate, unticked checkboxes: one for accepting the Terms of Service (mandatory for access) and one for opting into the marketing loyalty program (optional). The portal backend will log the timestamp and consent status for audit purposes. Upon connection, users will be redirected to a dynamic landing page offering a discount on room service.
A large stadium with a capacity of 50,000 is upgrading its WiFi infrastructure. They want to use the splash page to encourage fans to download the official team app, but they anticipate massive concurrent connection attempts during the 15-minute half-time interval.
The stadium must prioritize low-friction authentication and high-performance infrastructure. The splash page should offer a 'One-Click Connect' option or social login (e.g., Google/Facebook) to minimize the time spent on the portal. The walled garden must be meticulously configured to allow access to the App Store and Google Play Store prior to full authentication. The splash page itself should be extremely lightweight (minimal high-resolution images, no heavy scripts) to ensure rapid loading even under heavy load. The primary CTA on the splash page, or the immediate post-authentication redirect, should be a direct link to download the team app.
Scenario Analysis
Q1. A retail client reports that users are seeing a blank screen when attempting to log in via Facebook on their new splash page. Users connecting via standard email capture are unaffected. What is the most likely architectural cause of this issue?
💡 Hint:Consider what network access is required before the user is fully authenticated.
Show Recommended Approach
The most likely cause is a misconfigured walled garden (pre-authentication ACL). The gateway is blocking access to Facebook's OAuth servers prior to full authentication. The IT team must update the walled garden to whitelist the specific IP ranges or domains required by the Facebook authentication API.
Q2. Your marketing team has requested that the WiFi splash page include a mandatory field for 'Mobile Phone Number' alongside 'Email Address' to support an upcoming SMS campaign. How should you advise them regarding GDPR compliance and user experience?
💡 Hint:Apply the principle of data minimization and consider the impact of friction on conversion rates.
Show Recommended Approach
You should advise against making the phone number mandatory. Under GDPR's principle of data minimization, you should only collect data strictly necessary for the service. While an email may be justified for account creation, a phone number is excessive for basic WiFi access. Furthermore, adding mandatory, high-friction fields significantly increases splash page abandonment rates. Recommend keeping the phone number field optional or removing it entirely to prioritize connection rates.
Q3. An enterprise customer wants to deploy a splash page across 50 regional offices. They currently have local Windows Server infrastructure at each site. Should they deploy an on-premise portal on their local servers or utilize a cloud-hosted solution? Justify the architectural decision.
💡 Hint:Consider scalability, centralized management, and analytics requirements for multi-site deployments.
Show Recommended Approach
They should utilize a cloud-hosted solution. While they have local infrastructure, deploying and maintaining portal software across 50 separate servers introduces significant management overhead and inconsistency risks. A cloud-hosted portal provides centralized configuration, unified analytics across all regions, and simplifies updates. It allows the IT team to manage the global WiFi experience from a single dashboard, rather than troubleshooting 50 isolated instances.



