The Impact of MAC Randomization on NAC and How to Overcome It
This guide provides a deep-dive technical reference on the impact of MAC address randomization on Network Access Control (NAC) systems and guest WiFi architectures. It explains the mechanics of per-network and periodic MAC rotation across iOS, Android, and Windows, and details the cascading failures this causes — from captive portal fatigue and DHCP exhaustion to policy enforcement breakdown and inaccurate analytics. IT leaders and network architects will find actionable, vendor-neutral strategies for migrating from device-centric to identity-centric authentication using IEEE 802.1X, Passpoint (Hotspot 2.0), and OpenRoaming, with concrete implementation guidance for hospitality, retail, healthcare, and public-sector environments.
Listen to this guide
View podcast transcript
- Executive Summary
- Technical Deep-Dive: The Mechanics of MAC Randomization
- How Operating Systems Handle Randomization
- The Cascade of Failures on Network Infrastructure
- The IEEE Standard Context
- Implementation Guide: Migrating to Identity-Centric Architecture
- Phase 1: Immediate Mitigations (Week 1–2)
- Phase 2: Deploy IEEE 802.1X for Known Users (Month 1–3)
- Phase 3: Implement Passpoint and OpenRoaming for Transient Guests (Month 3–6)
- Best Practices for Enterprise Deployment
- Troubleshooting & Risk Mitigation
- Common Failure Modes and Resolutions
- ROI & Business Impact
Executive Summary
MAC address randomization — now the default behaviour on iOS 14+, Android 10+, and Windows 11 — has fundamentally broken the device-centric authentication model that enterprise NAC systems have relied on for two decades. When a device rotates its MAC address, the network treats it as a brand-new client. The consequences are immediate and operational: captive portals force returning guests to re-authenticate, DHCP scopes exhaust in high-density environments, NAC policies fail to apply, and analytics platforms report wildly inflated visitor counts.
For IT leaders managing Hospitality properties, Retail estates, Healthcare campuses, or Transport hubs, this is not a theoretical risk — it is an active operational problem affecting guest satisfaction, security posture, and marketing data quality.
The solution is architectural, not cosmetic. Networks must migrate from authenticating hardware identifiers (MAC addresses) to authenticating verified user identities via IEEE 802.1X, Passpoint (Hotspot 2.0), and OpenRoaming. This guide provides the technical depth and implementation roadmap to make that transition this quarter.
Technical Deep-Dive: The Mechanics of MAC Randomization
MAC randomization is not a monolithic standard. Its implementation varies significantly across device ecosystems, creating unpredictable and layered challenges for network engineers.
How Operating Systems Handle Randomization
Modern operating systems implement MAC randomization in two distinct modes, both of which disrupt legacy NAC architectures:
Per-Network Randomization (Default Behaviour): The device generates a unique, locally administered MAC address for each SSID it connects to. This address is derived from a hash of the SSID and a device-specific seed, meaning it is stable for that specific network but entirely different from the hardware MAC. This is the default on iOS 14+, Android 10+, and Windows 11.
Periodic Rotation (Enhanced Privacy Mode): Features such as Apple's 'Private Wi-Fi Address' (iOS 15+) and Android's 'Use randomized MAC' with enhanced tracking protection will rotate the randomized MAC address for a given SSID on a daily or weekly schedule, or after a configurable period of inactivity. This is the more disruptive mode for enterprise environments.
Furthermore, devices use randomized MACs during active scanning (Probe Requests) — before any association occurs. This means even passive analytics engines that track probe requests cannot reliably count unique devices.
The Cascade of Failures on Network Infrastructure
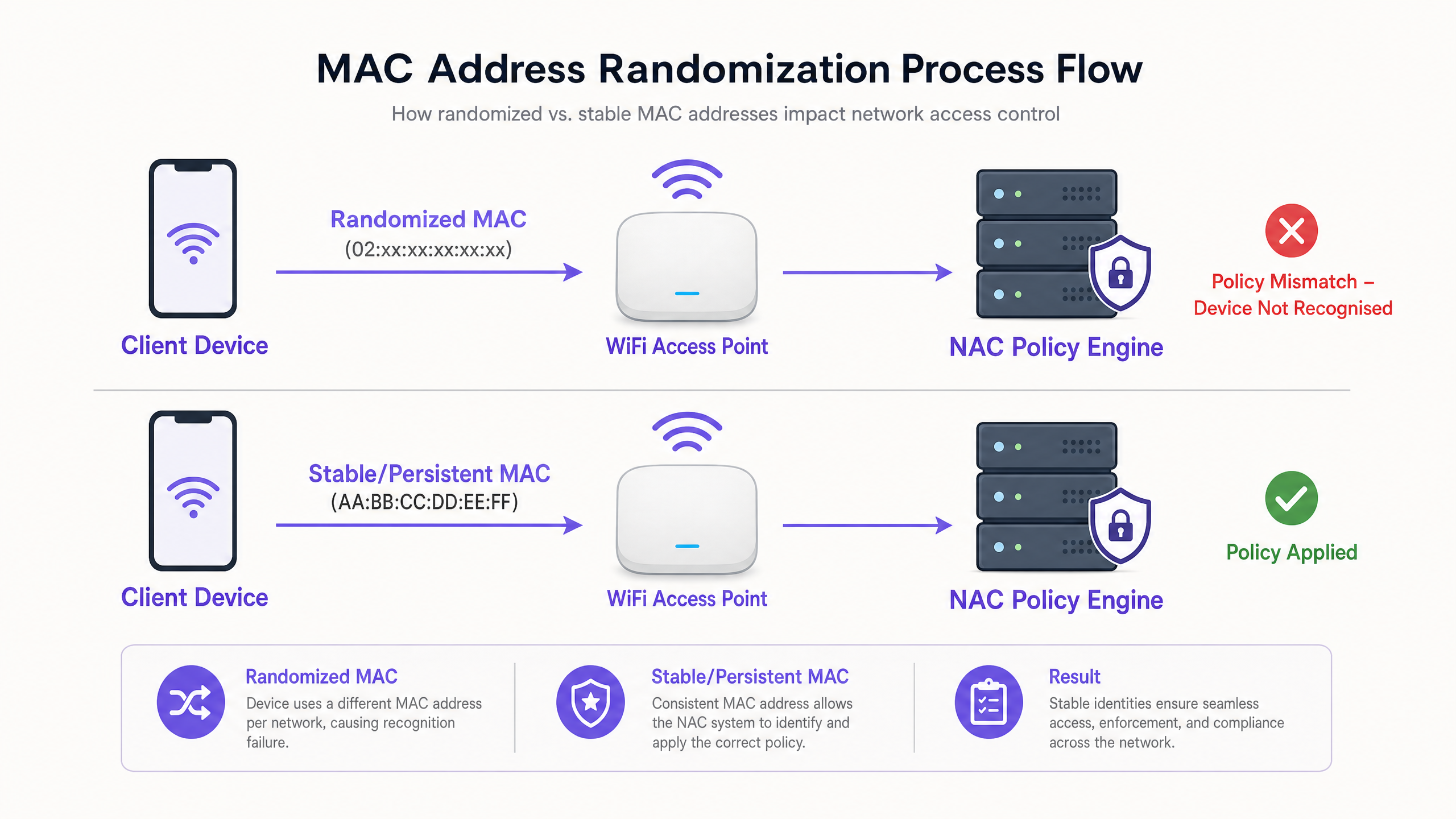
When a device rotates its MAC address, the network treats it as a net-new client. This single event triggers a cascade of architectural failures across multiple network layers:
| Failure Mode | Technical Cause | Business Impact |
|---|---|---|
| Captive Portal Fatigue | NAC session cache keyed on MAC; rotation invalidates the cache entry | Returning guests forced to re-authenticate; increased support tickets |
| DHCP Scope Exhaustion | Each new MAC consumes a new IP lease; old leases not released until TTL expires | New devices unable to obtain IP addresses; network outage for guests |
| NAC Policy Mismatch | Policies (VLAN, rate limit, ACL) bound to MAC; new MAC has no policy | Security controls bypass; guests may land on wrong VLAN |
| Analytics Inflation | Analytics keyed on Layer 2 MAC; one device appears as multiple unique visitors | Inaccurate footfall data; marketing decisions based on false metrics |
| Session Continuity Loss | AP roaming and load balancing rely on MAC for session handoff | Degraded roaming experience; dropped sessions during movement |
The IEEE Standard Context
The locally administered address bit (the second-least-significant bit of the first octet) is set to 1 in randomized MACs, distinguishing them from globally unique hardware addresses. A MAC beginning with 02:, 06:, 0A:, or 0E: in the first octet is definitively a locally administered (potentially randomized) address. Network engineers can use this to detect randomized clients at the RADIUS or DHCP server level, though detection alone does not resolve the authentication problem.
For further context on the RF environment in which these devices operate, see our guide on Wi-Fi Frequencies: A Guide to Wi-Fi Frequencies in 2026 .
Implementation Guide: Migrating to Identity-Centric Architecture
The only durable solution to MAC randomization is to decouple authentication and policy enforcement from hardware identifiers entirely. The following three-phase implementation roadmap provides a vendor-neutral path to an identity-centric network.
Phase 1: Immediate Mitigations (Week 1–2)
Before undertaking a full architectural migration, implement these tactical mitigations to stabilise the environment:
- Reduce DHCP Lease Times: On guest VLANs, reduce lease duration from the typical 24 hours to 1–4 hours. This reclaims IP addresses from transient devices faster and prevents scope exhaustion. In stadiums or conference centres with high turnover, consider leases as short as 30 minutes.
- Increase DHCP Pool Size: Expand the guest DHCP scope to accommodate the inflated demand from rotating MACs as a short-term buffer.
- Update Helpdesk Scripts: Instruct support staff that when troubleshooting a guest connection issue, they must ask for the device's current randomized MAC for that specific SSID (found in the Wi-Fi network details), not the hardware MAC from the general device settings.
Phase 2: Deploy IEEE 802.1X for Known Users (Month 1–3)
IEEE 802.1X is the cornerstone of identity-centric network access. Instead of authenticating the device via its MAC, the network authenticates the user via credentials, certificates, or tokenized identities through an EAP (Extensible Authentication Protocol) exchange with a RADIUS server.
Key configuration steps:
- Deploy a RADIUS server (e.g., FreeRADIUS, Cisco ISE, Aruba ClearPass) integrated with your identity directory (Active Directory, LDAP, or a cloud IdP).
- Create a dedicated WPA3-Enterprise SSID for known users (staff, registered guests, loyalty members).
- Provision 802.1X credentials via a Mobile Device Management (MDM) solution for corporate devices, or via a self-service onboarding portal for BYOD and registered guests.
- Update NAC policies to enforce VLAN assignment, ACLs, and rate limits based on RADIUS attributes (e.g.,
Tunnel-Private-Group-IDfor VLAN assignment) rather than MAC addresses.
Phase 3: Implement Passpoint and OpenRoaming for Transient Guests (Month 3–6)
For transient guests — hotel visitors, retail shoppers, stadium attendees — managing 802.1X credentials individually is impractical. Passpoint (Hotspot 2.0 / IEEE 802.11u) solves this by enabling seamless, automated, and encrypted authentication without a captive portal.
Passpoint allows a device to automatically discover a compatible network and authenticate using credentials provided by a trusted Identity Provider (IdP). The user never sees a login page.
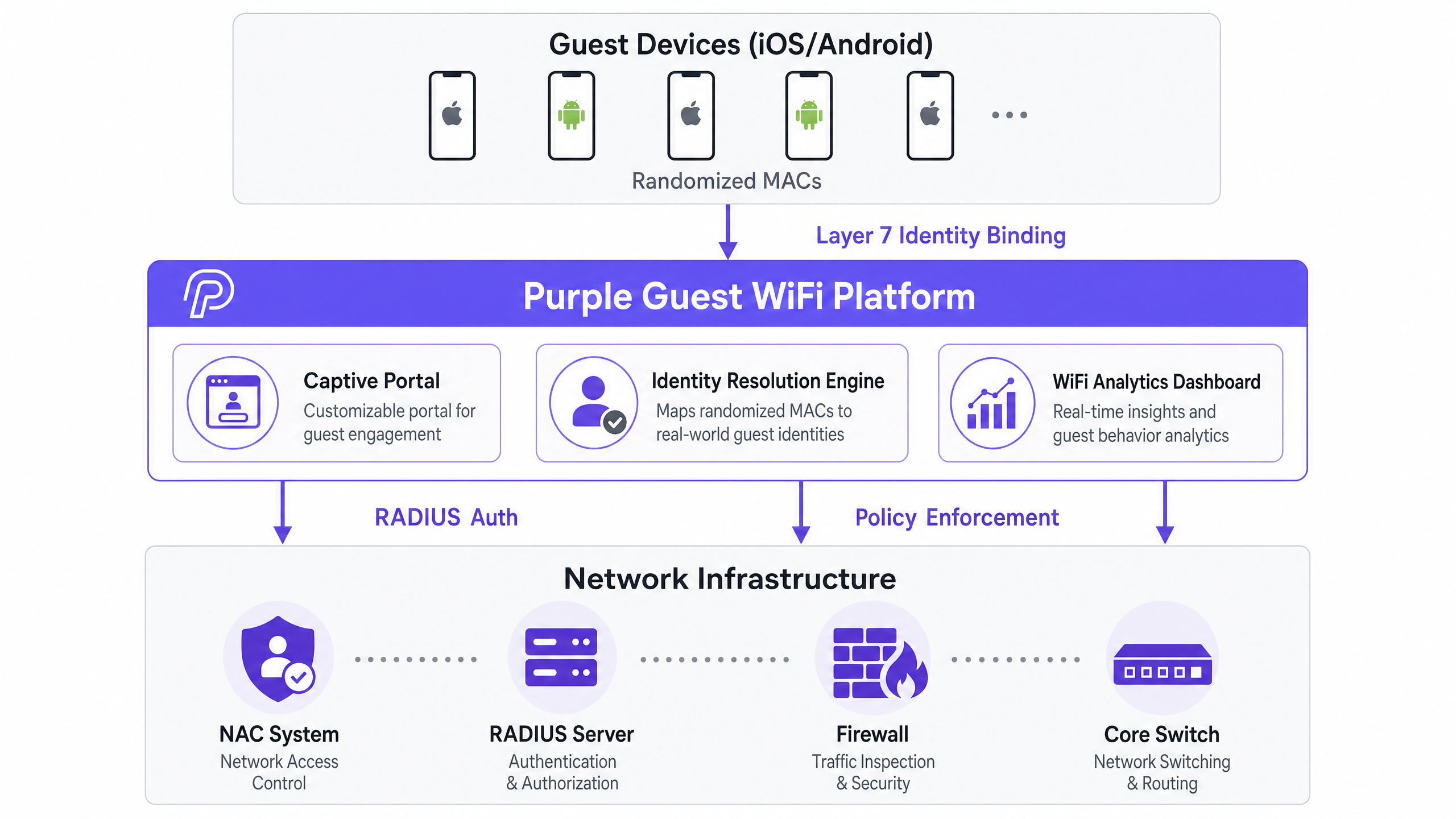
Purple's role as an Identity Provider: Purple's Guest WiFi platform acts as a free identity provider for services like OpenRoaming under the Connect licence. When a guest authenticates through a Purple-powered captive portal or loyalty app at one venue, Purple provisions them with Passpoint credentials. On subsequent visits to any OpenRoaming-enabled venue in the federation, the device connects automatically and securely — with the user's identity verified at Layer 7, regardless of their MAC address.
This architecture also feeds directly into the WiFi Analytics platform, where visitor counts, dwell times, and return visit rates are calculated from verified identities rather than ephemeral MAC addresses.
Best Practices for Enterprise Deployment
The following vendor-neutral best practices apply across all deployment scales:
Decouple Policy from MAC Addresses: Audit every NAC policy in your environment. Any policy that references a specific MAC address or MAC-based device group must be migrated to reference a user identity attribute (RADIUS username, Active Directory group, certificate CN). This is a non-negotiable prerequisite for a MAC-randomization-resilient network.
Segment IoT Devices Separately: Most enterprise IoT devices (access control readers, HVAC controllers, digital signage) do not implement MAC randomization. However, they should be isolated on a dedicated VLAN using MPSK or certificate-based authentication rather than MAC Authentication Bypass (MAB), which remains vulnerable to spoofing. For a detailed treatment of this topic, see our guide on Managing IoT Device Security with NAC and MPSK (también disponible en español: Gestión de la seguridad de dispositivos IoT con NAC y MPSK ).
Adopt WPA3 as the Baseline: WPA3-Personal (SAE) and WPA3-Enterprise provide significantly stronger protection than WPA2 and are required for Passpoint R3 deployments. Ensure your access point firmware and client supplicants support WPA3 before beginning Phase 3.
Validate Compliance Logging: Under GDPR and PCI DSS, you must be able to attribute network activity to a specific user or device. A MAC-based logging system is no longer sufficient. Ensure your SIEM and logging infrastructure captures authenticated user identities from RADIUS accounting records, not just MAC addresses from DHCP logs.
For context on related enterprise networking decisions, see our guide on SD-WAN vs MPLS: The 2026 Enterprise Network Guide and our primer on BLE Low Energy Explained for Enterprise .
Troubleshooting & Risk Mitigation
Common Failure Modes and Resolutions
Symptom: DHCP pool exhausted during peak hours despite normal footfall. Diagnosis: Check DHCP lease logs for multiple leases assigned to the same physical device (identifiable by correlating with AP association logs). If a single device has consumed 3+ leases in 24 hours, MAC rotation is confirmed. Resolution: Reduce lease times immediately. Implement Phase 2 (802.1X) for high-frequency users to stabilise their identity.
Symptom: Returning guests repeatedly redirected to captive portal. Diagnosis: The NAC session cache is keyed on MAC. Confirm by checking if the guest's current MAC matches the cached MAC from their last session. Resolution: Implement Passpoint for returning guests via a loyalty app or profile provisioning. This is the only permanent fix.
Symptom: Analytics reporting 3x expected unique visitor counts. Diagnosis: The analytics platform is counting unique MAC addresses rather than unique authenticated sessions. Resolution: Migrate analytics to rely on Layer 7 identity data from captive portal authentication logs or RADIUS accounting. Discard MAC-based visitor counting entirely.
Symptom: IoT device loses VLAN assignment after apparent reconnection. Diagnosis: Confirm whether the IoT device firmware implements MAC randomization (rare but present in some consumer-grade IoT devices deployed in enterprise environments). Resolution: Migrate IoT authentication to MPSK or certificate-based 802.1X. Do not rely on MAB for any device that may implement randomization.
ROI & Business Impact
Addressing MAC randomization is not a cost centre — it is a revenue and compliance enabler.
Operational Cost Reduction: Eliminating captive portal-related support tickets delivers immediate savings. For a large hotel chain with 200 properties, reducing guest WiFi support calls by even 30% can represent tens of thousands of pounds in annual helpdesk cost reduction.
Marketing Data Quality: Accurate, identity-based visitor analytics directly improves the ROI of marketing campaigns. When footfall data is based on verified identities rather than rotating MACs, conversion rate calculations, dwell time analysis, and return visit attribution become reliable inputs for business decisions.
Compliance Assurance: GDPR requires that data processing is tied to identifiable individuals with appropriate consent. A MAC-based system cannot reliably link network activity to a specific person. An identity-centric system with verified authentication provides the audit trail required for GDPR compliance and PCI DSS network segmentation logging.
Guest Experience and Revenue: In hospitality, a frictionless, automatic Wi-Fi connection (via Passpoint) is increasingly a competitive differentiator. Hotels and venues that eliminate the captive portal for returning guests report measurably higher guest satisfaction scores and increased dwell time — both of which correlate with higher ancillary revenue per visit.
Key Definitions
MAC Address Randomization
A privacy feature in modern operating systems (iOS 14+, Android 10+, Windows 11) where a device generates a locally administered, temporary MAC address instead of using its burned-in hardware address when connecting to or scanning for Wi-Fi networks. The randomized address may be per-network (stable for a given SSID) or periodically rotated.
IT teams encounter this when devices fail to bypass captive portals on return visits, when analytics platforms report inflated unique visitor counts, or when DHCP scopes exhaust unexpectedly in high-density environments.
Network Access Control (NAC)
A security framework and associated technology that enforces policy on devices attempting to access a network, determining the level of access granted based on device identity, posture (compliance state), and user credentials. Common NAC platforms include Cisco ISE, Aruba ClearPass, and Forescout.
NAC systems traditionally relied on MAC addresses for device profiling, policy enforcement, and session tracking — a paradigm that MAC randomization has fundamentally undermined.
Captive Portal
A web page that intercepts a user's HTTP traffic and requires interaction (login, terms acceptance, or payment) before granting network access. Captive portals typically use MAC address caching to recognise returning users and bypass re-authentication.
MAC randomization breaks the 'Remember Me' functionality of captive portals, as the returning device presents a new MAC address that does not match the cached session.
IEEE 802.1X
An IEEE standard for port-based Network Access Control that provides an authentication mechanism for devices connecting to a LAN or WLAN. It uses the Extensible Authentication Protocol (EAP) to authenticate users or devices against a RADIUS server, binding network access to a verified identity rather than a hardware address.
802.1X is the primary architectural solution to MAC randomization for enterprise environments, shifting authentication from the device layer to the identity layer.
Passpoint (Hotspot 2.0 / IEEE 802.11u)
A Wi-Fi Alliance certification programme and associated IEEE standard that enables devices to automatically discover, select, and authenticate to Wi-Fi networks using credentials provided by a trusted Identity Provider, without user interaction or captive portal redirection.
Passpoint is the recommended solution for eliminating MAC-dependent captive portals for transient guest populations in hospitality, retail, and public venues.
OpenRoaming
A Wireless Broadband Alliance (WBA) federation of Wi-Fi networks and identity providers that enables devices to seamlessly and securely connect to participating networks globally, using their existing cellular, enterprise, or social credentials.
Purple acts as an identity provider for OpenRoaming under the Connect licence, allowing venues to offer automatic, secure guest Wi-Fi access while maintaining identity visibility for analytics and compliance.
DHCP Scope Exhaustion
A network condition where a DHCP server has assigned all available IP addresses in its configured pool and cannot service new DHCP requests, causing new clients to fail to obtain network connectivity.
A direct operational symptom of MAC randomization in high-density environments. A single physical device rotating its MAC address can consume multiple IP leases, rapidly depleting the available pool.
Layer 7 Identity Binding
The process of associating network activity, session data, and analytics with a specific authenticated user identity at the application layer (Layer 7 of the OSI model), rather than relying on network-layer identifiers such as MAC addresses (Layer 2) or IP addresses (Layer 3).
Essential for accurate Wi-Fi analytics, GDPR-compliant session logging, and reliable NAC policy enforcement in a post-MAC randomization network architecture.
Locally Administered Address (LAA)
A MAC address in which the second-least-significant bit of the first octet (the 'U/L' bit) is set to 1, indicating the address has been assigned by software rather than the hardware manufacturer. Randomized MAC addresses are always locally administered addresses.
Network engineers can detect randomized clients at the RADIUS or DHCP server by checking for the LAA bit. First octets of 02, 06, 0A, or 0E indicate a locally administered address.
Worked Examples
A 500-store retail chain is experiencing DHCP pool exhaustion during peak weekend trading hours. The network team has not increased footfall, but DHCP logs show the guest VLAN scope is consistently exhausted by midday on Saturdays. The current lease time is 24 hours.
Step 1 — Confirm the root cause: Pull DHCP lease logs and cross-reference with AP association logs. Look for multiple leases assigned to the same physical device within a 24-hour window. If a device appears with 3+ different MAC addresses in a single day, MAC rotation is confirmed as the primary driver.
Step 2 — Immediate mitigation: Reduce DHCP lease times on the guest VLAN from 24 hours to 2 hours. This reclaims IP addresses from transient shoppers and rotating MACs significantly faster. Also expand the DHCP pool size as a buffer.
Step 3 — Medium-term fix: Implement Passpoint provisioning via the brand's loyalty app. Frequent shoppers who install the app receive a Passpoint profile that authenticates them automatically on 802.1X, bypassing the MAC-dependent captive portal. Their session is now tied to their loyalty identity, not their MAC.
Step 4 — Update NAC policies: Ensure VLAN assignment and rate limiting policies reference the RADIUS username attribute, not the MAC address. This ensures consistent policy application regardless of MAC rotation.
A 400-room hotel group is receiving guest complaints that they have to log in to the hotel WiFi every day of their stay, despite the captive portal displaying a 'Remember this device for 7 days' option. The hotel's IT team has confirmed the NAC is configured correctly with a 7-day session cache.
Step 1 — Diagnose the MAC rotation: Ask a guest to check their iPhone or Android settings for the specific hotel SSID. On iOS, navigate to Settings > Wi-Fi > [Hotel SSID] and check if 'Private Wi-Fi Address' is set to 'Rotating'. If enabled, the device rotates its MAC daily, invalidating the 7-day session cache every 24 hours.
Step 2 — Short-term guest communication: Update the hotel's WiFi welcome screen and in-room materials to instruct guests on how to set their Private Wi-Fi Address to 'Fixed' for the hotel SSID. This is a stopgap measure only.
Step 3 — Permanent architectural fix: Deploy a Passpoint R2 configuration on the hotel's access points. Integrate with Purple's Guest WiFi platform as the Identity Provider. Guests who authenticate once via the captive portal on day one are provisioned with a Passpoint profile. For the remainder of their stay — and on future visits — their device connects automatically and securely without any portal interaction.
Step 4 — Validate with RADIUS accounting: Confirm that RADIUS accounting logs are capturing the guest's authenticated identity (email or loyalty ID) rather than just the MAC address, to ensure GDPR-compliant session logging.
Practice Questions
Q1. A stadium IT director notices that their guest Wi-Fi analytics platform is reporting 58,000 unique visitors during a match, but the stadium's verified capacity is 32,000. The analytics vendor confirms the platform counts unique MAC addresses. What is the most likely cause, and what architectural change is required to produce accurate visitor counts?
Hint: Consider how many times a single device's MAC address might rotate during a 3-hour event, and what layer of the network stack the analytics platform is reading from.
View model answer
The analytics platform is counting unique MAC addresses at Layer 2, and MAC randomization is causing each physical device to appear as multiple unique visitors as it rotates its address during the event. The 58,000 figure likely represents MAC rotation events rather than actual individuals. The architectural fix is to migrate the analytics platform to count unique authenticated identities at Layer 7 — specifically, unique captive portal authentication sessions or RADIUS accounting records. Each authenticated session is tied to a verified identity (email, phone number, or social login), which does not change when the MAC rotates. This will produce an accurate, GDPR-compliant visitor count.
Q2. You are the network architect for a large NHS trust deploying a new NAC solution. You need to ensure that medical IoT devices (infusion pumps, patient monitoring systems) remain securely connected to a clinical VLAN, while guest devices (patients and visitors) are isolated on an internet-only VLAN. The trust's CISO has flagged that MAC Authentication Bypass (MAB) is insufficient for clinical device security. How do you design the authentication architecture for each device class?
Hint: Differentiate the authentication capabilities of headless medical IoT devices versus consumer smartphones. Consider which devices can support 802.1X certificates and which cannot.
View model answer
For medical IoT devices: Deploy 802.1X with EAP-TLS (certificate-based authentication) for devices that support it. For legacy devices that cannot support 802.1X, use MPSK (Multi Pre-Shared Key) with a unique PSK per device, ensuring each device is isolated even if one PSK is compromised. Maintain a strict device inventory and provision certificates or PSKs via the MDM/device management system. Assign clinical VLAN via RADIUS attributes on successful authentication.
For guest devices (patients and visitors): Assume all MACs are randomized. Deploy a captive portal for initial authentication (email/SMS verification for GDPR consent). For returning guests, integrate with Purple's Passpoint/OpenRoaming to enable automatic reconnection on subsequent visits. Assign all guest traffic to an internet-only VLAN with no access to clinical networks, enforced at the RADIUS level by user group, not by MAC address.
Q3. A luxury retail brand wants to implement a 'frictionless' Wi-Fi experience where VIP loyalty members connect automatically without any portal interaction when they enter any of the brand's 80 flagship stores globally. Given that MAC randomization makes MAC-based session caching unreliable, what is the most robust architectural approach, and what data does the brand gain as a result?
Hint: MAC caching is not a viable mechanism for 'frictionless' return visits. Consider what persistent, non-rotating identifier can be used instead, and how it is provisioned to the device.
View model answer
The most robust approach is Passpoint (Hotspot 2.0) provisioned via the brand's loyalty app. When a VIP member first authenticates (via the app or a one-time captive portal), the Purple Guest WiFi platform provisions a Passpoint profile containing 802.1X credentials tied to the member's loyalty identity. The profile is installed on the device and stored securely. On subsequent visits to any of the 80 stores, the device automatically discovers the Passpoint-enabled SSID and authenticates in the background using the stored credentials — no portal, no interaction, no MAC dependency.
The brand gains: (1) accurate, identity-linked connection events for each store visit, enabling precise footfall attribution to specific loyalty members; (2) dwell time and visit frequency data tied to verified identities for CRM enrichment; (3) a GDPR-compliant audit trail linking network access to explicit consent captured during initial onboarding; and (4) the ability to trigger real-time personalised marketing messages based on in-store presence, using the WiFi Analytics platform.