The Most Secure Method of WiFi Authentication: A Comparison
This technical reference guide provides a definitive ranked comparison of WiFi authentication methods — from the deprecated WEP standard through to EAP-TLS certificate-based authentication — helping IT managers, network architects, and CTOs at enterprise venues make informed, compliance-aligned security decisions. It covers the technical architecture of each protocol, real-world deployment scenarios in hospitality and retail, and practical implementation guidance for organisations operating under PCI DSS and GDPR obligations. For venue operators and IT teams, this guide translates complex cryptographic standards into actionable deployment decisions with measurable business outcomes.
🎧 Listen to this Guide
View Transcript
- Executive Summary
- Technical Deep-Dive
- The Fundamental Security Challenge of Wireless Networks
- Protocol-by-Protocol Analysis
- EAP Methods: The Critical Decision
- Implementation Guide
- Step 1: Infrastructure Assessment and Hardware Validation
- Step 2: RADIUS and Identity Store Architecture
- Step 3: Certificate Management for EAP-TLS
- Step 4: Phased Rollout and Monitoring
- Best Practices
- Troubleshooting & Risk Mitigation
- ROI & Business Impact
Executive Summary
For enterprise venues — from expansive retail chains to high-density stadiums — the choice of WiFi authentication method directly dictates the organisation's security posture and compliance status. This guide provides a definitive technical comparison of WiFi security protocols, evaluating their architecture, vulnerabilities, and real-world applicability across hospitality, retail, healthcare, and public-sector environments.
Moving beyond legacy shared-key models, modern deployments require robust identity validation to protect corporate assets and guest data. The evolution from WEP to EAP-TLS represents a fundamental architectural shift: from network-level shared secrets to device-level cryptographic identity. By understanding this progression, IT leaders can architect secure networks that align with PCI DSS and GDPR mandates while integrating seamlessly with platforms like Purple's Guest WiFi and WiFi Analytics solutions.
The key decision for most enterprise IT teams is not whether to deploy 802.1X, but which EAP method to select and how to manage the resulting infrastructure. This guide provides the framework to make that call with confidence.
Technical Deep-Dive
The Fundamental Security Challenge of Wireless Networks
Wireless networks present a unique security challenge: the transmission medium is inherently public. Data broadcast over radio frequency travels beyond the physical boundaries of the building, the car park, and potentially into the street. Any device within range can attempt to capture that traffic. This is why the choice of authentication and encryption protocol is not a configuration detail — it is a foundational architectural decision.
The IEEE 802.11 working group has continually evolved security standards to address this challenge, and the history of that evolution is a useful lens through which to evaluate current options.
Protocol-by-Protocol Analysis
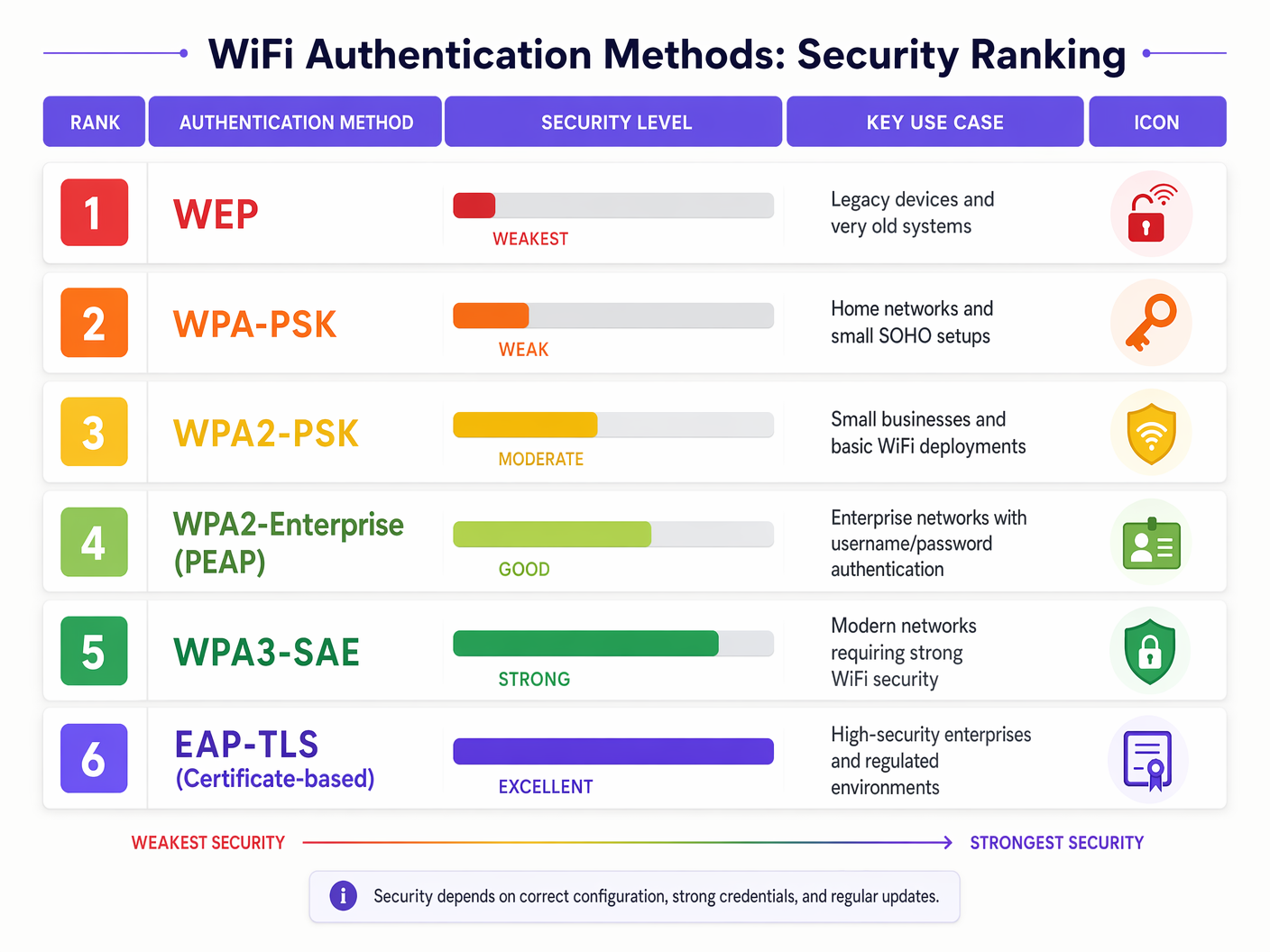
WEP (Wired Equivalent Privacy) — Deprecated
Introduced in 1997 as part of the original IEEE 802.11 standard, WEP utilised the RC4 stream cipher for confidentiality and CRC-32 for integrity verification. Cryptographic researchers identified fundamental flaws in RC4's key scheduling algorithm within a few years of deployment. Tools such as Aircrack-ng can crack a WEP key in under two minutes by passively capturing a sufficient volume of traffic. WEP is entirely deprecated by the IEEE and poses a critical security risk. Any organisation still operating WEP-protected networks is in breach of PCI DSS requirements and should treat remediation as an emergency.
| Protocol | Encryption | Key Length | Status |
|---|---|---|---|
| WEP | RC4 | 40/104-bit | Deprecated — Do Not Use |
| WPA | TKIP/RC4 | 128-bit | Deprecated |
| WPA2-PSK | AES-CCMP | 128/256-bit | Acceptable (limited use cases) |
| WPA3-SAE | AES-CCMP + SAE | 128/256-bit | Recommended (personal/small business) |
| WPA2-Enterprise | AES-CCMP + 802.1X | 128/256-bit | Recommended (enterprise) |
| WPA3-Enterprise | AES-GCMP + 802.1X | 192/256-bit | Gold Standard |
WPA and WPA2-PSK (Pre-Shared Key)
WPA replaced WEP by implementing TKIP (Temporal Key Integrity Protocol), which was itself superseded by WPA2 and its robust AES-CCMP encryption. While WPA2-PSK provides strong over-the-air encryption, it relies on a single shared password distributed to all users. This architecture carries two critical weaknesses for enterprise deployment.
First, it is vulnerable to offline dictionary attacks. An attacker who captures the four-way EAPOL handshake during a client's association can take that capture offline and brute-force the password at their leisure using GPU-accelerated tools. Second, it provides no individual user accountability. Every device on the network shares the same encryption key, meaning a compromised device can decrypt the traffic of every other device on the same network segment. For Retail environments handling payment card data, this is a direct PCI DSS violation.
WPA3-SAE (Simultaneous Authentication of Equals)
WPA3 addresses the core cryptographic weaknesses of WPA2-PSK by replacing the four-way handshake with the Dragonfly key exchange, formally known as Simultaneous Authentication of Equals (SAE). SAE provides two critical improvements: resistance to offline dictionary attacks (each authentication attempt requires an active interaction with the access point, making brute-force computationally infeasible) and forward secrecy (past session traffic cannot be decrypted even if the password is subsequently compromised). WPA3 is the correct upgrade path for venues that cannot justify the infrastructure overhead of 802.1X — smaller retail locations, IoT device networks, and branch offices.
WPA2/WPA3-Enterprise (IEEE 802.1X)
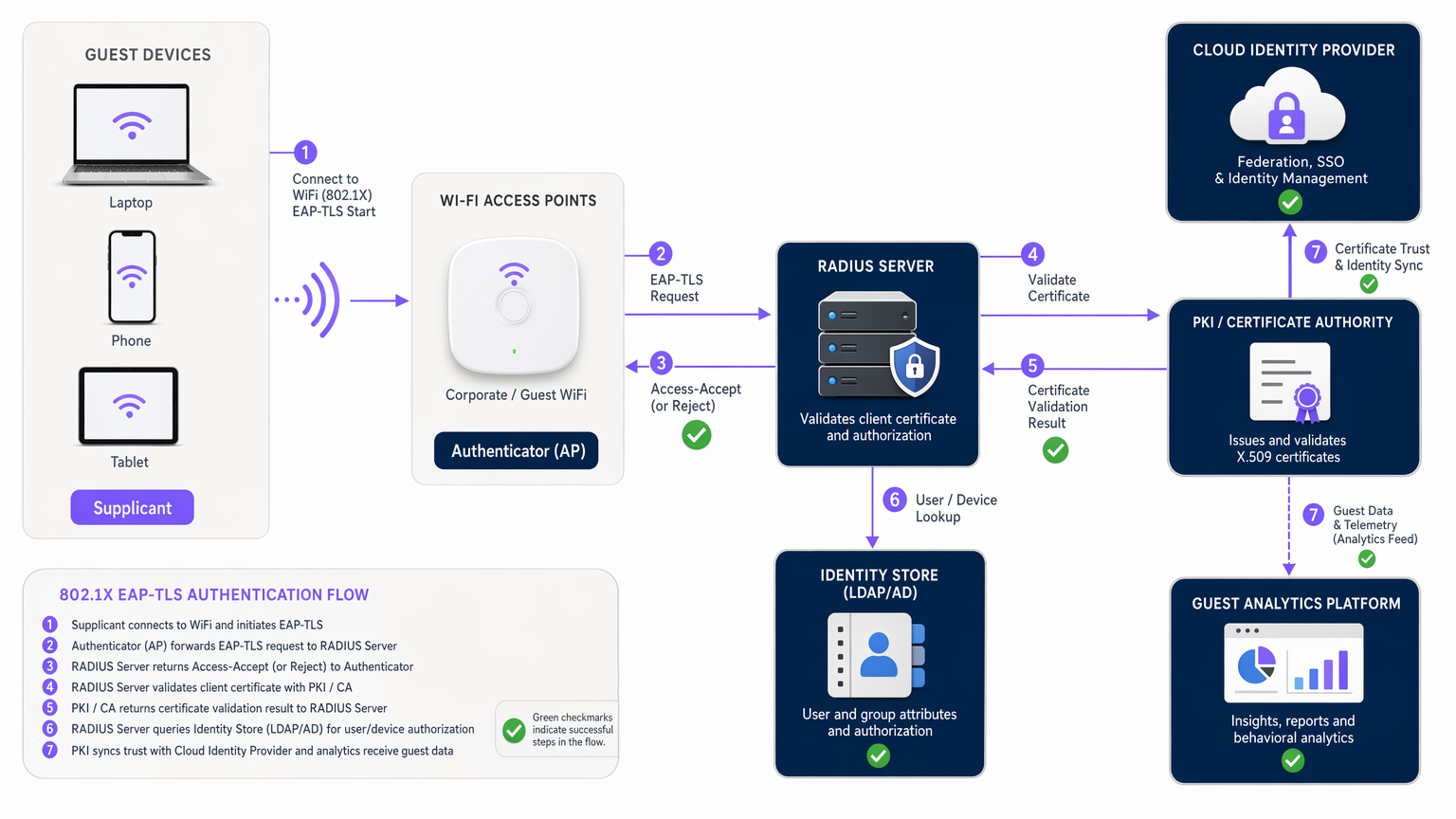
Enterprise environments require individual identity validation. The IEEE 802.1X standard defines port-based network access control, utilising the Extensible Authentication Protocol (EAP) to transport credentials from the client device (the Supplicant) through the Access Point (the Authenticator) to a central RADIUS server (the Authentication Server). The RADIUS server validates the credentials against an identity store — Active Directory, LDAP, or a cloud identity provider — and returns an Access-Accept or Access-Reject message. Only upon receiving Access-Accept does the AP grant the client full network access.
This three-party architecture is the foundation of enterprise WiFi security and is the mandatory baseline for any organisation handling sensitive data or operating in a regulated industry.
EAP Methods: The Critical Decision
Within the 802.1X framework, the choice of EAP method determines the actual strength of the authentication exchange. The two most widely deployed methods in enterprise environments are PEAP and EAP-TLS.
PEAP (Protected EAP) establishes a secure TLS tunnel using a server-side certificate, protecting the subsequent exchange of MSCHAPv2 credentials (username and password). It is operationally attractive because it does not require certificate deployment to client devices — users authenticate with their existing Active Directory credentials. However, PEAP's security depends entirely on the client correctly validating the RADIUS server's certificate. If a user is tricked into accepting a rogue server certificate — a well-documented attack vector — the attacker can harvest credentials in plain text inside the tunnel. Strict certificate validation, enforced via Group Policy or MDM, is non-negotiable in any PEAP deployment.
EAP-TLS (EAP-Transport Layer Security) is the highest-assurance authentication method available for WiFi networks. It requires mutual certificate authentication: the RADIUS server presents a certificate to the client, and the client presents a unique certificate to the RADIUS server. Both parties must successfully validate each other's certificate before any network access is granted. This eliminates password-based vulnerabilities entirely. A compromised password cannot grant network access because the attacker does not possess the private key associated with the client certificate. For a detailed comparison of these two methods, refer to our dedicated guide: EAP-TLS vs. PEAP: ¿Qué protocolo de autenticación es el adecuado para su red?
| Feature | PEAP | EAP-TLS |
|---|---|---|
| Server Certificate Required | Yes | Yes |
| Client Certificate Required | No | Yes |
| Password Used | Yes (MSCHAPv2) | No |
| Resistance to Phishing | Moderate | Very High |
| PKI Infrastructure Required | Partial | Full |
| BYOD Suitability | High | Low-Medium |
| Managed Device Suitability | High | Very High |
| Regulatory Compliance Alignment | Good | Excellent |
Implementation Guide
Deploying robust WiFi security, particularly 802.1X, requires careful architectural planning across four key workstreams.
Step 1: Infrastructure Assessment and Hardware Validation
Ensure all access points and wireless LAN controllers support the target WPA3 or 802.1X standards. Audit firmware versions across the estate. Legacy hardware may require firmware upgrades or replacement. For Hospitality environments with large, distributed AP estates, this assessment should be conducted before any procurement decisions are made.
Step 2: RADIUS and Identity Store Architecture
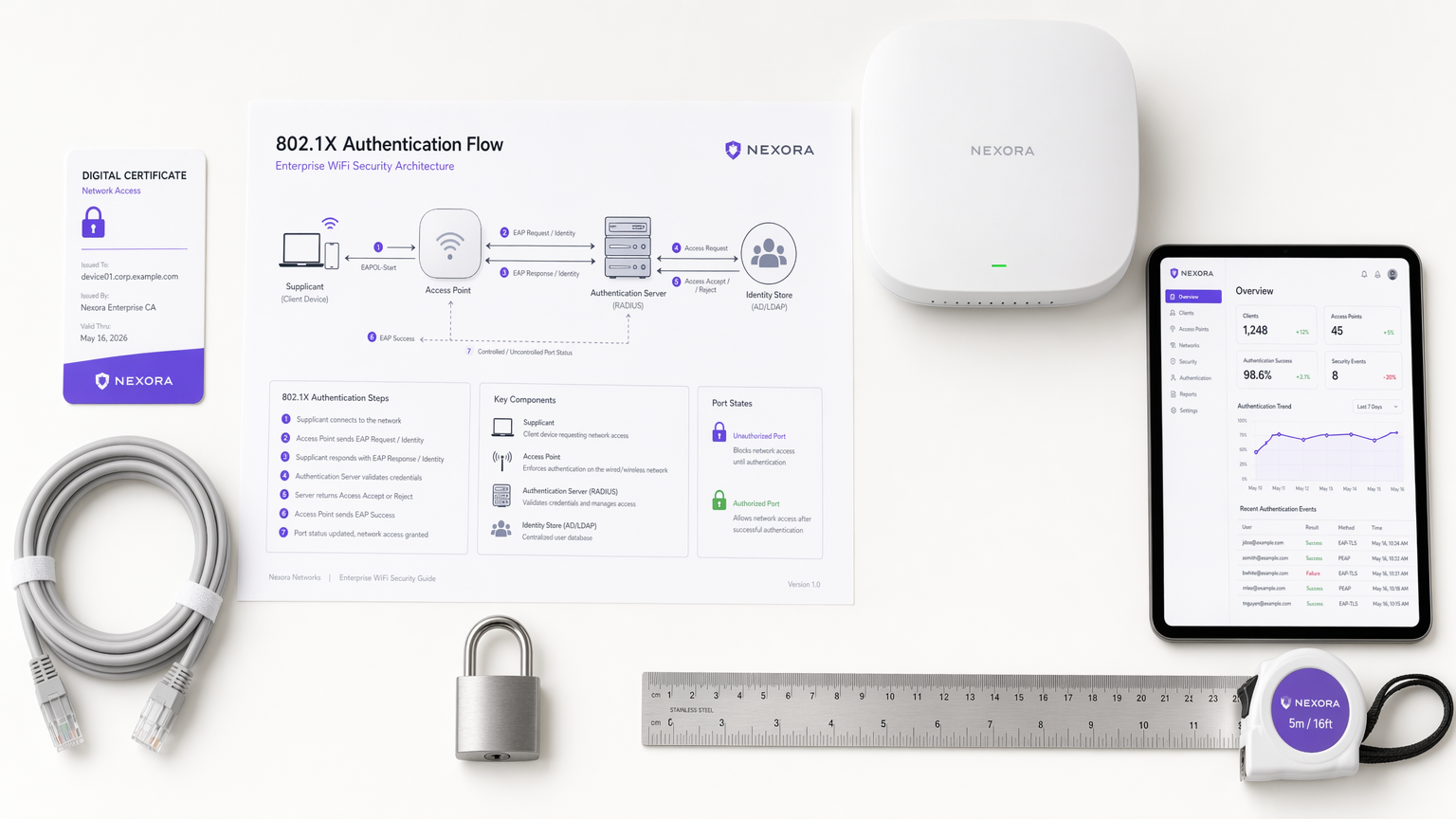
Deploy a highly available RADIUS infrastructure. For enterprise deployments, this typically means a pair of RADIUS servers (primary and secondary) at each major site, or a cloud-hosted RADIUS service for distributed organisations. Integrate the RADIUS servers with the corporate identity store. When integrating with Purple's platform, the RADIUS infrastructure communicates securely to validate user profiles and feed session data into the WiFi Analytics dashboard, enabling venue operators to correlate authentication events with visitor behaviour analytics.
Step 3: Certificate Management for EAP-TLS
For EAP-TLS deployments, establish a robust PKI. This involves deploying a Root Certificate Authority and, for larger organisations, one or more Intermediate CAs. Automate the provisioning and revocation of client certificates using an MDM solution (Microsoft Intune, Jamf, or VMware Workspace ONE). Certificate lifecycle management — including automated renewal and revocation workflows — is the most operationally critical component of an EAP-TLS deployment. A lapsed certificate is the most common cause of sudden, unexplained authentication failures. This is equally important in Healthcare environments where device availability is mission-critical.
Step 4: Phased Rollout and Monitoring
Implement the new secure SSID alongside the legacy network. Migrate users in cohorts — starting with IT staff, then department by department. Monitor RADIUS authentication logs for failure patterns. Track the authentication success rate as a key operational metric. For Transport venues such as airports and rail stations, ensure the rollout plan accounts for the high volume of transient, unmanaged devices connecting to guest networks.
Best Practices
Enforce Certificate Validation on All PEAP Clients. Configure client devices via Group Policy or MDM to strictly validate the RADIUS server's certificate and explicitly trust only the issuing Root CA. Prevent users from manually accepting untrusted certificates. This single configuration step eliminates the primary attack vector against PEAP deployments.
Implement Network Segmentation. Separate guest traffic, corporate data, and IoT devices into distinct VLANs with strict inter-VLAN firewall rules. This is a foundational security control that limits the blast radius of any single compromised device. The principles of SD-WAN architecture, discussed in The Core SD WAN Benefits for Modern Businesses , complement this approach by enabling centralised policy enforcement across distributed sites.
Automate Certificate Lifecycle Management. Set automated alerts at 90, 60, and 30 days before certificate expiry for all PKI components. Implement automated renewal where possible. Certificate expiry is the most preventable cause of authentication outages.
Deploy Wireless Intrusion Prevention (WIPS). WIPS sensors can detect rogue access points broadcasting your corporate SSID and alert the security team before any credentials are harvested. This is particularly important in high-footfall venues where an attacker could physically deploy a rogue AP without being noticed.
Adopt Passpoint/Hotspot 2.0 for Guest Networks. For guest authentication at scale, Passpoint (IEEE 802.11u / Hotspot 2.0) enables devices to automatically and securely connect using provisioned profiles, eliminating the need for captive portal interactions on repeat visits. This is the architecture that underpins OpenRoaming, the global WiFi roaming federation.
Troubleshooting & Risk Mitigation
RADIUS Timeout and Latency Issues. High latency between the access point and the RADIUS server can cause EAP timeouts, resulting in failed authentications. Ensure RADIUS servers are geographically distributed relative to the AP estate. For branch locations, consider deploying local RADIUS survivability to maintain authentication capability during WAN outages.
Certificate Expiration Failures. A lapsed server or client certificate will cause immediate authentication failures with minimal diagnostic output in the client event logs. Implement centralised PKI monitoring with automated alerting. For large certificate estates, consider a dedicated certificate lifecycle management platform.
Clock Skew and NTP Synchronisation. Certificate validity is time-bound. If the system clock on a client device or RADIUS server drifts significantly, certificate validation will fail. Ensure all network infrastructure and managed devices are synchronised to a reliable NTP source.
Rogue Access Point Attacks. In high-footfall environments, an attacker can deploy a rogue AP broadcasting a legitimate SSID to harvest credentials from misconfigured clients. WIPS deployment and strict client-side certificate validation are the primary mitigations.
BYOD Onboarding Complexity. EAP-TLS on unmanaged personal devices requires a secure onboarding workflow. Use a Network Access Control (NAC) solution or a dedicated onboarding portal to guide users through certificate installation. For guest networks, route users through a captive portal and provision Passpoint profiles for subsequent secure access.
ROI & Business Impact
Investing in robust WiFi security architecture delivers measurable business value that extends well beyond risk mitigation. The financial case for upgrading from PSK to 802.1X can be built across three dimensions.
Operational Cost Reduction. Transitioning to EAP-TLS eliminates the recurring cost of password rotation across distributed sites. For a retail chain with 50 locations, the IT overhead of manually updating PSKs following staff turnover — and the security risk during the window between an employee's departure and the password change — represents a quantifiable cost. Certificate-based authentication reduces this to a single revocation action in the PKI.
Compliance Risk Mitigation. Operating a WEP or WPA2-PSK network in an environment that processes payment card data is a direct PCI DSS violation. The cost of a single data breach — including forensic investigation, card reissuance, fines, and reputational damage — vastly exceeds the capital investment required to deploy 802.1X infrastructure.
Revenue Generation Through Secure Guest Access. Secure, profile-based guest authentication — deployed via platforms like Purple — transforms the WiFi network from a cost centre into a revenue-generating asset. By capturing verified first-party data through the authentication process, venue operators in Hospitality and Retail can build rich guest profiles, power personalised marketing campaigns, and drive measurable increases in repeat visits and spend per visit. The WiFi Analytics platform provides the intelligence layer that connects authentication events to business outcomes.
Key Terms & Definitions
IEEE 802.1X
An IEEE standard for port-based network access control that provides an authentication mechanism to devices wishing to attach to a LAN or WLAN. It defines the roles of Supplicant, Authenticator, and Authentication Server.
The foundational framework for enterprise WiFi security. IT teams encounter this when configuring RADIUS-based authentication on access points and when troubleshooting connection failures on corporate devices.
RADIUS (Remote Authentication Dial-In User Service)
A networking protocol that provides centralised Authentication, Authorisation, and Accounting (AAA) management for users who connect and use a network service. Defined in RFC 2865.
The central server infrastructure that processes authentication requests from WiFi access points and queries the identity database. Network architects must design for RADIUS high availability to prevent authentication outages.
Supplicant
The client device or software application that requests access to the network and provides credentials during the 802.1X authentication exchange.
When troubleshooting connection failures, IT teams must check the supplicant configuration — the WiFi settings on the client device — to ensure it is configured to trust the correct server certificate and use the correct EAP method.
Authenticator
The network device, typically a WiFi Access Point or managed switch, that acts as an intermediary in the 802.1X exchange, passing EAP messages between the Supplicant and the RADIUS server.
The AP enforces the security policy by blocking all network traffic from a client until the RADIUS server returns an Access-Accept message. Misconfigured authenticator settings are a common source of authentication failures.
EAP (Extensible Authentication Protocol)
An authentication framework defined in RFC 3748 that supports multiple authentication methods. EAP is not a protocol itself but a framework that carries specific authentication data over the wireless link.
IT teams select an EAP method (PEAP, EAP-TLS, EAP-TTLS) based on their infrastructure capabilities and security requirements. The choice of EAP method is the most consequential security decision in an 802.1X deployment.
PKI (Public Key Infrastructure)
The set of roles, policies, hardware, software, and procedures required to create, manage, distribute, use, store, and revoke digital certificates and manage public-key encryption.
A mandatory requirement for deploying EAP-TLS. IT teams must design a PKI architecture — including Root CA, Intermediate CAs, and certificate templates — before deploying certificate-based WiFi authentication.
WPA3-SAE (Simultaneous Authentication of Equals)
The authentication mechanism introduced in WPA3 that replaces the WPA2 four-way handshake with the Dragonfly key exchange, providing resistance to offline dictionary attacks and forward secrecy.
The recommended upgrade path from WPA2-PSK for environments where 802.1X infrastructure is not feasible. IT teams should prioritise WPA3-SAE deployment on any network that currently uses WPA2-PSK.
Passpoint / Hotspot 2.0
A Wi-Fi Alliance standard (based on IEEE 802.11u) that enables devices to automatically and securely connect to WiFi networks using provisioned profiles, without requiring manual captive portal interaction.
Critical for modern hospitality and retail guest WiFi deployments. Passpoint enables seamless, encrypted roaming for returning guests and underpins the OpenRoaming global WiFi federation, which Purple supports as an identity provider.
Forward Secrecy
A cryptographic property of a key exchange protocol that ensures session keys cannot be compromised even if the long-term private key is later exposed. Each session uses a unique, ephemeral key.
WPA3-SAE and EAP-TLS both provide forward secrecy. IT teams should cite this property when justifying the upgrade from WPA2-PSK, particularly in environments where historical traffic capture is a concern.
Case Studies
A 400-room luxury hotel is upgrading its network infrastructure. The current guest WiFi uses a single WPA2-PSK password printed on room keycards. Management wants to improve security, prevent access by non-guests, and capture guest data for CRM and marketing, while ensuring a seamless connection experience that does not require guests to repeatedly log in.
Deploy Purple's Guest WiFi platform as the identity and onboarding layer, integrated with the hotel's Property Management System (PMS). On first connection, guests are directed to a captive portal that validates their booking reference against the PMS. Upon successful validation, the Purple platform provisions a Passpoint (Hotspot 2.0) profile to the guest's device. This profile contains the credentials required for 802.1X authentication. On all subsequent connections — including roaming between APs throughout the property — the device connects automatically and securely without any portal interaction. The hotel's marketing team receives verified guest profiles in the WiFi Analytics dashboard. The IT team gains individual session accountability and can revoke access for specific devices if required.
A regional retail chain with 50 locations uses WPA2-PSK for its corporate devices — handheld scanners, inventory tablets, and back-office workstations. The IT team must manually update the PSK across all sites whenever a member of staff leaves. The security team has flagged that the current PSK has not been rotated in 14 months. The organisation also processes payment card data and is subject to PCI DSS.
Migrate all corporate devices to WPA2/WPA3-Enterprise using EAP-TLS. Deploy a cloud-hosted RADIUS service (such as Cisco Duo, JumpCloud, or a self-hosted FreeRADIUS cluster) integrated with the corporate Active Directory. Enrol all corporate devices into Microsoft Intune. Use Intune to push unique machine certificates to each device, issued by an internal Certificate Authority. Configure the WiFi profile via Intune to use EAP-TLS with the machine certificate. When a member of staff leaves, the IT team revokes the certificate for their specific device in the PKI. Access is immediately terminated without affecting any other device. The network segmentation between the corporate SSID and the guest SSID ensures that payment card data traffic is isolated, satisfying PCI DSS Requirement 1.3.
Scenario Analysis
Q1. A university campus wants to deploy secure WiFi for 20,000 students. They currently use a captive portal with Active Directory credentials. They want to move to 802.1X to encrypt over-the-air traffic. They do not have an MDM solution for student-owned devices (BYOD). Which EAP method should the network architect recommend, and what is the single most important configuration step to enforce?
💡 Hint:Consider the operational overhead of managing certificates on 20,000 unmanaged personal devices, and identify the primary attack vector against the recommended method.
Show Recommended Approach
The architect should recommend PEAP. While EAP-TLS provides higher assurance, deploying and managing client certificates on 20,000 unmanaged BYOD devices without an MDM is operationally infeasible. PEAP allows students to use their existing Active Directory credentials within a secure TLS tunnel. The single most important configuration step is to ensure the RADIUS server certificate is signed by a well-known public CA (such as DigiCert or Sectigo) and to configure the university's WiFi onboarding documentation to instruct students to verify the server certificate name before accepting. Without this, students may accept rogue server certificates, exposing their credentials to Man-in-the-Middle attacks.
Q2. A financial services firm requires the highest level of WiFi security for its corporate network. They have a fully managed device fleet controlled via Microsoft Intune. Following a recent phishing incident in which several employees surrendered their Active Directory passwords, the CISO has mandated that WiFi authentication must not rely on user passwords. Which protocol satisfies this requirement, and what infrastructure components are required?
💡 Hint:The solution must eliminate passwords from the authentication process entirely. Consider what replaces the password as the proof of identity.
Show Recommended Approach
The firm must deploy EAP-TLS. This protocol eliminates passwords entirely by requiring mutual certificate authentication. The required infrastructure components are: (1) an internal Certificate Authority (Root CA and Intermediate CA) to issue certificates; (2) Microsoft Intune configured to push unique machine certificates to all corporate devices; (3) a RADIUS server (such as NPS on Windows Server or Cisco ISE) configured to validate client certificates against the internal CA; and (4) a certificate revocation mechanism (CRL or OCSP) to enable immediate revocation of compromised or lost devices. Because EAP-TLS relies on the private key stored on the device rather than a user password, a stolen password cannot grant network access.
Q3. A stadium IT director is evaluating a proposal to upgrade their public guest WiFi. The vendor proposes using WPA3-SAE to provide better security than the current open network. The marketing director has a separate requirement to capture fan email addresses and phone numbers to build a CRM database for post-event communications. Are these two requirements compatible under the proposed architecture? If not, what is the correct solution?
💡 Hint:Consider what WPA3-SAE does and does not provide in terms of user identity capture. Think about how the business objective of data collection can be achieved alongside secure connectivity.
Show Recommended Approach
The two requirements are not compatible under the proposed WPA3-SAE architecture. WPA3-SAE provides strong encryption and resistance to dictionary attacks, but it does not capture user identity or marketing data — it simply secures the connection using a shared password. A fan connecting to a WPA3-SAE network is anonymous to the venue. The correct architecture is to deploy an open SSID (or a lightly secured network) that redirects connecting devices to a captive portal — such as Purple's Guest WiFi platform — where fans provide their details in exchange for access. The platform captures the verified first-party data for the CRM. After the initial registration, the platform can provision a Passpoint profile to the fan's device, enabling automatic, encrypted, and identity-verified connections on all subsequent visits. This architecture satisfies both the security requirement (encrypted subsequent connections) and the marketing requirement (verified identity capture).



