The Role of SCEP and NAC in Modern MDM Infrastructure
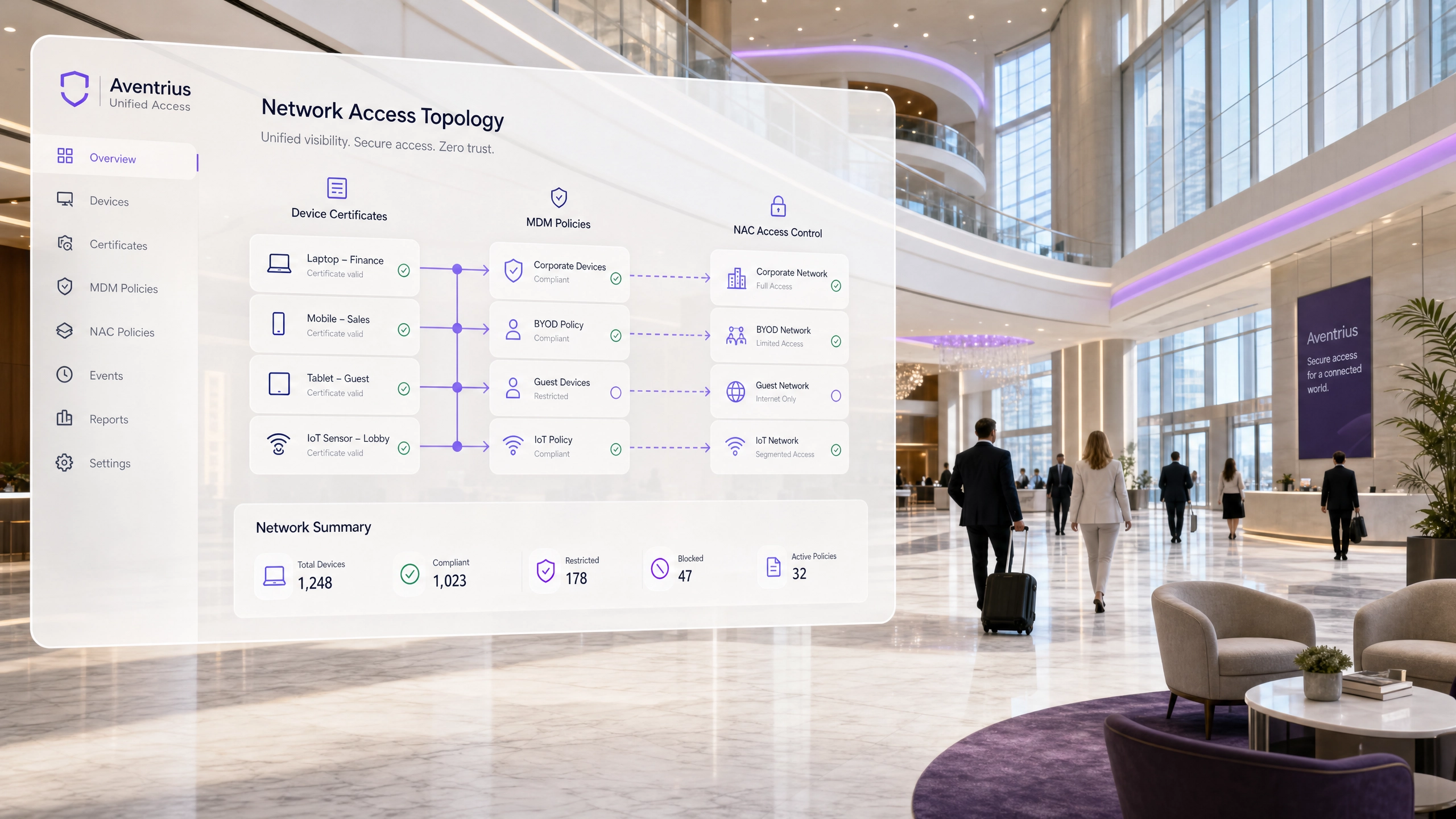
This guide provides a comprehensive technical breakdown of how SCEP and NAC integrate with MDM platforms to deliver secure, zero-touch network access at enterprise scale. It covers the full architecture from certificate issuance through 802.1X enforcement, with real-world implementation scenarios from hospitality and retail. Designed for IT leaders at large venues who need to eliminate password vulnerabilities, automate device provisioning, and satisfy compliance requirements this quarter.
Listen to this guide
View podcast transcript
- Executive Summary
- Technical Deep-Dive
- The Three-Layer Architecture
- How SCEP Automates PKI at Scale
- NAC and 802.1X EAP-TLS: The Enforcement Layer
- Guest Network Segmentation
- Implementation Guide
- Step 1: PKI and SCEP Preparation
- Step 2: MDM Configuration
- Step 3: NAC and RADIUS Setup
- Step 4: Network Infrastructure Integration
- Step 5: Parallel Deployment and Cutover
- Best Practices
- Troubleshooting & Risk Mitigation
- ROI & Business Impact
Executive Summary
For enterprise venues — from 80,000-seat stadiums to multi-site retail chains — securing the network edge has moved decisively beyond pre-shared keys and manual credential management. The proliferation of corporate endpoints, BYOD devices, and IoT infrastructure demands a zero-trust architecture that scales without burdening the IT helpdesk.
This guide details the technical architecture of integrating the Simple Certificate Enrollment Protocol (SCEP) and Network Access Control (NAC) with Mobile Device Management (MDM) infrastructure. By leveraging SCEP to automate the distribution of X.509 certificates and NAC to enforce IEEE 802.1X EAP-TLS authentication, organisations can achieve zero-touch provisioning, eliminate credential theft vectors, and enforce dynamic, posture-based network access. While public-facing access is managed through dedicated Guest WiFi solutions, this architecture secures the critical back-of-house operations that keep the venue running. The result is a measurable reduction in IT overhead, a stronger compliance posture under PCI DSS and GDPR, and a network edge that actively enforces zero-trust principles.
Technical Deep-Dive
The Three-Layer Architecture
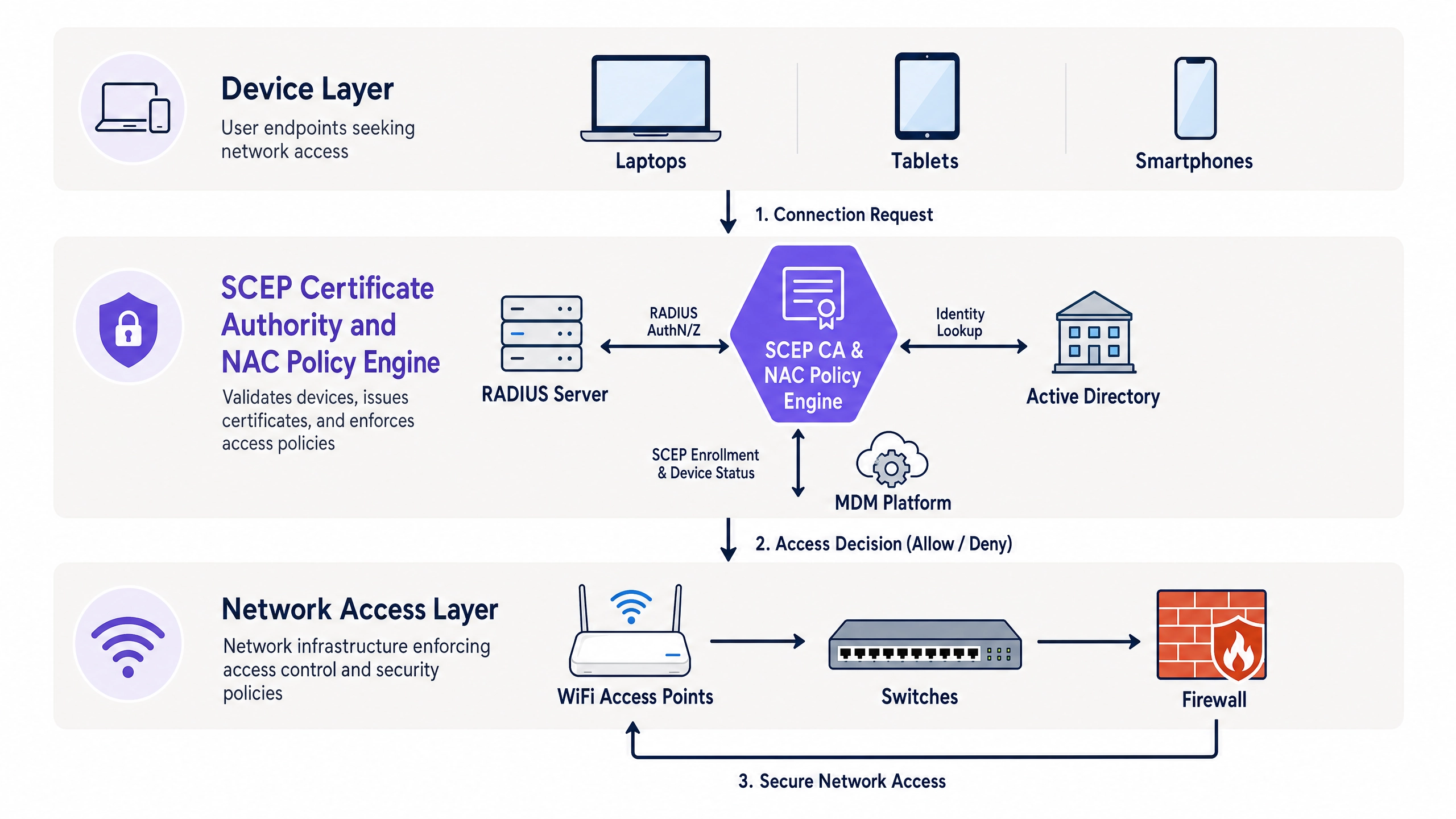
Modern network security relies on cryptographic identity rather than user knowledge. The SCEP-NAC-MDM stack operates across three primary layers:
| Layer | Component | Function |
|---|---|---|
| Device Management | MDM / UEM | Central authority for device configuration, compliance, and lifecycle |
| Identity & Issuance | PKI / SCEP / CA | Generates, issues, and manages digital certificates |
| Access Enforcement | NAC / RADIUS | Evaluates certificates and device posture before granting network access |
These layers are not sequential — they operate in a continuous feedback loop. The MDM informs the NAC of compliance status in real-time, and the NAC can trigger MDM remediation workflows when a device fails posture checks.
How SCEP Automates PKI at Scale
Deploying certificates manually is operationally impossible at scale. A 500-device estate would require an IT administrator to generate, sign, and install individual X.509 certificates on each device — a process that takes minutes per device and introduces significant human error risk. SCEP eliminates this entirely.
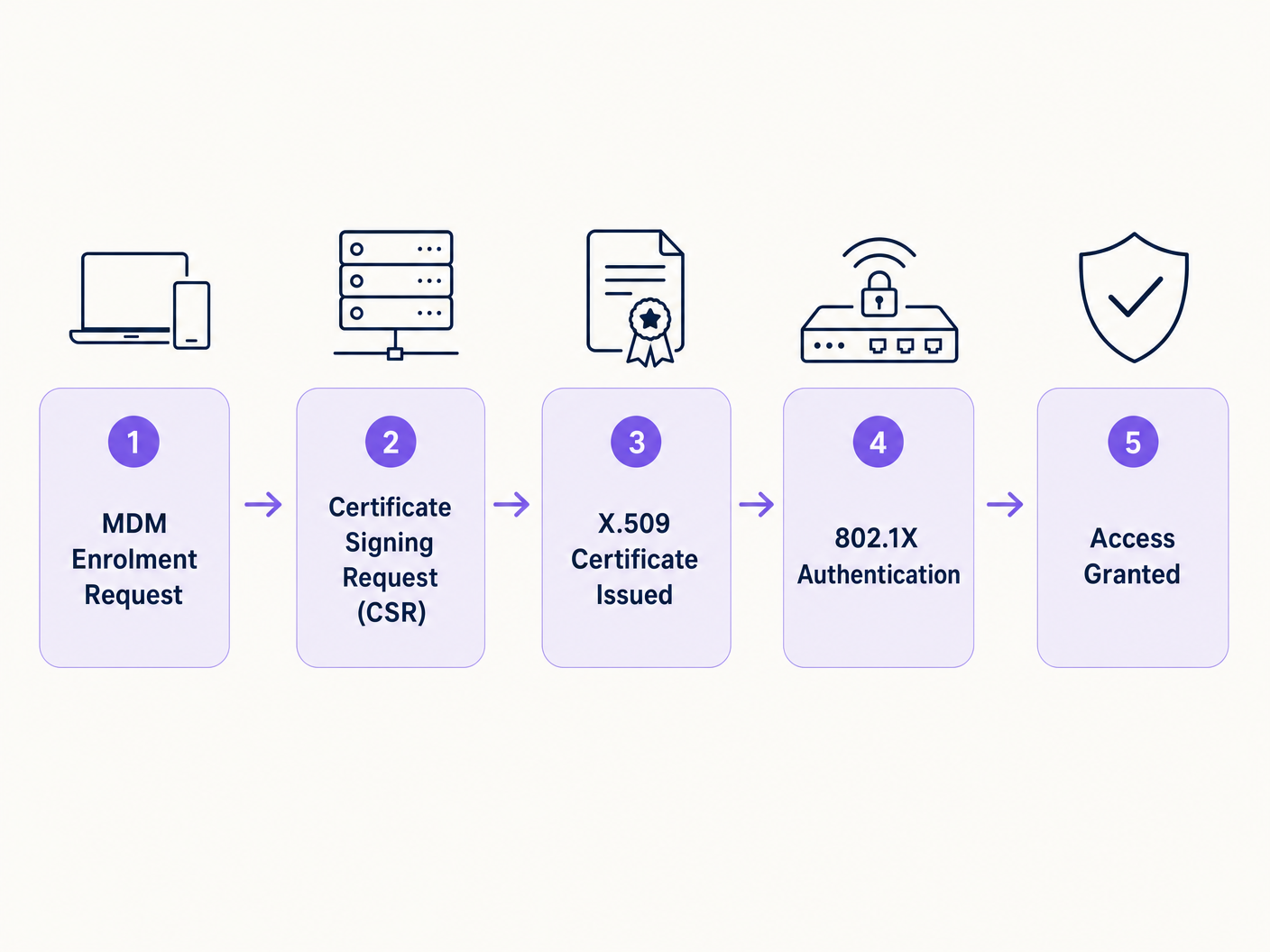
When a device enrolls in the MDM, the MDM pushes a configuration profile containing a SCEP payload. This payload instructs the device to generate a key pair locally — critically, the private key never leaves the device — and submit a Certificate Signing Request (CSR) to the SCEP server. The SCEP server, typically Microsoft's Network Device Enrollment Service (NDES) or a cloud-based equivalent, validates the request against the MDM to confirm the device is authorised. It then forwards the CSR to the Certificate Authority (CA), which issues the signed X.509 certificate. The certificate is returned to the device and installed in its secure enclave or system keystore.
This entire process happens silently, over-the-air, with zero user interaction. For a 1,000-device deployment, the entire certificate estate can be provisioned within hours of MDM enrollment completion.
NAC and 802.1X EAP-TLS: The Enforcement Layer
Once the device holds a valid certificate, it attempts to connect to the corporate SSID or wired port using IEEE 802.1X. The access point or switch acts as the authenticator, forwarding the request to the RADIUS server governed by the NAC policy engine. The most secure EAP method is EAP-TLS, which mandates mutual authentication — both the client and the RADIUS server must present valid certificates, preventing man-in-the-middle attacks via rogue access points.
The NAC performs several critical checks in sequence:
- Cryptographic Validation: Is the certificate mathematically valid and signed by a trusted root CA?
- Revocation Check: Is the certificate listed on a Certificate Revocation List (CRL) or flagged via the Online Certificate Status Protocol (OCSP)?
- Posture Assessment: By querying the MDM via API, the NAC asks: Is the device compliant? Is the OS at the required patch level? Is disk encryption enabled?
If all checks pass, the NAC sends a RADIUS Access-Accept message, typically accompanied by Vendor-Specific Attributes (VSAs) that dynamically assign the device to a specific VLAN or apply an Access Control List (ACL). A non-compliant device is dropped into a remediation VLAN with limited access — typically just enough to trigger an MDM-driven remediation workflow.
Guest Network Segmentation
In any venue environment, the corporate infrastructure must be strictly isolated from public-facing networks. Guest WiFi platforms operate on entirely separate SSIDs and VLANs, with no routing path to corporate resources. The SCEP-NAC architecture governs the corporate layer; the guest layer is governed by captive portal authentication and data capture workflows. For venues deploying WiFi Analytics , this segmentation is a prerequisite — analytics data flows through the guest network, while operational data flows through the certificate-authenticated corporate network. For further context on the underlying radio frequency architecture that underpins both networks, see Wi-Fi Frequencies: A Guide to Wi-Fi Frequencies in 2026 .
Implementation Guide
Deploying this architecture requires careful sequencing to avoid locking out legitimate users during the transition.
Step 1: PKI and SCEP Preparation
Establish a robust internal PKI or leverage a cloud-based Managed PKI (mPKI) service. Deploy and harden the SCEP server — if using Microsoft NDES, ensure it is running on a dedicated server, not co-hosted with the CA. Configure the SCEP server to use dynamic challenge passwords, generated per-device by the MDM, rather than a static shared secret. This prevents unauthorised certificate requests if the SCEP URL is discovered.
Step 2: MDM Configuration
Create the SCEP payload in your MDM platform. Define the Subject Alternative Name (SAN) fields carefully — the SAN must contain unique identifiers (such as the device serial number or user UPN) that the NAC will use for policy decisions. Push the profile to a test group of IT team devices first and validate the full enrollment flow before wider rollout.
Step 3: NAC and RADIUS Setup
Configure your NAC to trust the Root CA that issued the client certificates. Install a server certificate on the RADIUS server for EAP-TLS mutual authentication. Define access policies based on certificate attributes and MDM compliance status. Implement dynamic VLAN assignment rules: compliant corporate devices to the corporate VLAN, non-compliant devices to the remediation VLAN, and IoT devices to a dedicated, internet-restricted VLAN.
Step 4: Network Infrastructure Integration
Configure switches and wireless access points for 802.1X. For Retail environments with legacy point-of-sale hardware or Hospitality venues with smart room controllers, implement MAC Authentication Bypass (MAB) as a fallback for devices that cannot participate in EAP-TLS. Restrict MAB to specific switch ports and ensure the MAC address database is tightly controlled. For Healthcare and Transport environments, the posture assessment rules should be configured to meet sector-specific compliance requirements.
Step 5: Parallel Deployment and Cutover
Never cut over immediately. Broadcast the new 802.1X SSID in parallel with the existing network. Push the new WiFi profile via MDM. Monitor adoption and resolve enrollment failures. Once 95%+ of devices are successfully authenticated on the new SSID, decommission the legacy network.
Best Practices
Mandate EAP-TLS. Never accept EAP-PEAP or EAP-TTLS as the primary authentication method for corporate devices. These methods rely on username/password credentials inside a TLS tunnel, which remain vulnerable to credential harvesting. EAP-TLS eliminates this attack surface entirely.
Implement real-time revocation. Scheduled CRL downloads create a window of exposure. Configure the NAC to perform OCSP checks in real-time. When a device is reported lost or stolen, revoke the certificate in the CA and the device loses network access at the next authentication attempt — or immediately if Change of Authorization (CoA) is implemented.
Set sensible certificate validity periods. A one-year validity period with automated SCEP renewal triggered at the 30-day mark is the industry standard. Longer periods increase the window of exposure if a certificate is compromised; shorter periods increase the risk of renewal failures causing outages.
Segment IoT aggressively. IoT devices should never share a VLAN with corporate endpoints. Use the NAC to enforce strict ACLs on the IoT VLAN, permitting only the specific protocols and destinations each device type requires. For venues deploying location services, review Indoor WiFi Positioning Systems: How They Work and How to Deploy Them to understand how positioning infrastructure integrates with the broader network architecture.
Align with WPA3. Where hardware supports it, configure the corporate SSID to use WPA3-Enterprise, which mandates Protected Management Frames (PMF) and provides stronger cryptographic protections than WPA2. See SD-WAN vs MPLS: The 2026 Enterprise Network Guide for how this fits into the broader enterprise connectivity picture.
Troubleshooting & Risk Mitigation
| Failure Mode | Root Cause | Mitigation |
|---|---|---|
| Devices fail EAP-TLS after certificate renewal | SCEP renewal failed silently | Monitor SCEP server logs; set alerts for failed CSR submissions |
| Clock skew causes certificate validation failure | NTP misconfiguration | Enforce NTP synchronisation across all endpoints and infrastructure |
| IoT devices cannot authenticate | No 802.1X supplicant | Implement MAB with strict MAC address control and isolated VLAN |
| Mass device lockout after CA migration | Old root CA not trusted by NAC | Stage CA migrations; add new root CA to NAC trust store before revoking old |
| Revoked device retains network access | CRL-only revocation with long download interval | Implement OCSP and CoA for real-time revocation |
For BLE-based IoT devices specifically, the authentication architecture differs from WiFi-connected endpoints. Review BLE Low Energy Explained for Enterprise for the specific security considerations applicable to Bluetooth Low Energy infrastructure.
ROI & Business Impact
The business case for SCEP-NAC-MDM integration is straightforward when measured against the cost of the alternatives.
| Metric | Pre-Implementation | Post-Implementation |
|---|---|---|
| IT helpdesk tickets (network access) | High — password resets, key rotations | Near-zero — automated certificate lifecycle |
| Mean time to revoke compromised device | Hours (manual process) | Seconds (OCSP + CoA) |
| PCI DSS access control compliance | Manual, audit-intensive | Automated, continuously enforced |
| BYOD onboarding time | 15–30 minutes per device | Under 5 minutes, zero IT involvement |
For a 500-device estate, eliminating manual certificate management and password-related helpdesk tickets typically delivers a 25–35% reduction in network-related IT support overhead. The risk mitigation value — avoiding a single credential-based breach — typically exceeds the entire implementation cost. For public-sector and healthcare organisations under GDPR, the ability to demonstrate automated, auditable access control is a significant compliance asset.
Key Definitions
SCEP (Simple Certificate Enrollment Protocol)
A protocol that automates the issuance and revocation of digital certificates to devices without user intervention, acting as the communication layer between the MDM platform and the Certificate Authority.
Used by MDM platforms to seamlessly deploy X.509 certificates to thousands of endpoints at scale. IT teams encounter SCEP when configuring MDM profiles for 802.1X WiFi authentication.
NAC (Network Access Control)
A security solution that enforces policy on devices seeking to access network infrastructure, evaluating authentication credentials, certificate validity, and device compliance posture before granting access.
Acts as the gatekeeper at the network edge. IT teams configure NAC policies to define which devices get access to which VLANs based on their certificate attributes and MDM compliance status.
MDM (Mobile Device Management)
Software used by IT departments to monitor, manage, and secure employees' endpoints across multiple operating systems, serving as the central source of truth for device identity and compliance.
The initiator of the SCEP enrollment process and the source of posture data queried by the NAC. Without MDM integration, the NAC cannot perform posture-based access control.
IEEE 802.1X
An IEEE standard for port-based Network Access Control that provides an authentication mechanism to devices wishing to attach to a LAN or WLAN, requiring successful authentication before the port is opened.
The underlying protocol that forces devices to authenticate before the switch or access point allows any traffic to pass. Configured on both the network infrastructure and the device's 802.1X supplicant.
EAP-TLS (Extensible Authentication Protocol - Transport Layer Security)
The most secure EAP standard, requiring mutual authentication where both the client device and the RADIUS server must present valid digital certificates, eliminating password-based credential attacks.
The gold standard for enterprise wireless security. IT architects should mandate EAP-TLS over PEAP or TTLS wherever device certificate infrastructure is in place.
CSR (Certificate Signing Request)
A block of encoded text generated by a device containing its public key and identity details, submitted to the Certificate Authority to request a signed X.509 certificate.
Generated automatically by the device during the SCEP enrollment process. The private key corresponding to the CSR never leaves the device, ensuring the certificate cannot be duplicated.
MAB (MAC Authentication Bypass)
A fallback authentication method where the network uses the device's hardware MAC address as its credential, used for devices that lack 802.1X supplicant capability.
Used for legacy IoT devices such as printers, sensors, and smart room controllers that cannot participate in EAP-TLS. Should always result in assignment to a highly restricted VLAN.
OCSP (Online Certificate Status Protocol)
An internet protocol used for obtaining the revocation status of an X.509 digital certificate in real-time, providing an alternative to downloading and parsing Certificate Revocation Lists.
Critical for NAC systems that need to immediately block network access when a device is compromised or reported stolen. OCSP provides real-time status; CRL downloads create a revocation window.
CoA (Change of Authorization)
A RADIUS extension (RFC 5176) that allows the NAC to dynamically modify or terminate an active network session without waiting for the session to expire or the device to re-authenticate.
Used to immediately disconnect a device when its certificate is revoked or its MDM compliance status changes. Essential for real-time zero-trust enforcement.
Worked Examples
A 500-room luxury resort needs to secure its back-of-house operations network. Staff use shared tablets for housekeeping management, and management use corporate laptops. The current WPA2-PSK network has had the pre-shared key leaked multiple times, resulting in two security incidents in the past year. How should the IT team transition to certificate-based authentication without disrupting operations?
Phase 1 — Preparation (Weeks 1–2): Deploy a cloud-based RADIUS/NAC solution and integrate it with the existing MDM. Configure a SCEP profile in the MDM to push device-based certificates to all tablets and laptops. Use device-based certificates (tied to the device serial number) rather than user-based certificates, so shared tablets authenticate automatically regardless of which staff member is using them. Phase 2 — Parallel Deployment (Weeks 3–4): Broadcast a new, hidden SSID configured for 802.1X EAP-TLS. Push the new WiFi profile via MDM to all enrolled devices. Monitor the NAC dashboard for successful authentications. Phase 3 — Cutover (Week 5): Once 95%+ of devices are connected to the new SSID, decommission the legacy WPA2-PSK network. Revoke the old PSK from all documentation and access points.
A national retail chain is deploying 3,000 new Point of Sale terminals across 150 stores. The security team mandates strict PCI DSS network segmentation and zero-trust access. The deployment timeline is 8 weeks. How does SCEP and NAC facilitate this at scale without requiring IT staff at each store?
Pre-Deployment: The POS vendor pre-enrolls all 3,000 devices in the retailer's MDM using the vendor's zero-touch enrollment programme. The MDM is configured with a SCEP profile that will fire automatically upon first boot. Deployment: When a POS terminal is powered on at the store, it connects to a temporary onboarding SSID (internet-only, no corporate access). The MDM profile is pushed, the SCEP payload fires, and the device requests and receives its X.509 certificate from the CA. The MDM then pushes the corporate WiFi profile. Network Access: When the POS connects to the store's switch port, the switch initiates 802.1X. The NAC validates the certificate, queries the MDM to confirm the POS is compliant (encryption enabled, MDM agent active, no jailbreak detected), and dynamically assigns the switch port to the PCI-DSS VLAN. The POS is now operational. Zero IT staff were required at the store.
Practice Questions
Q1. Your organisation is migrating from WPA2-Enterprise using PEAP-MSCHAPv2 to EAP-TLS. During the pilot, Windows laptops and iPhones connect successfully, but 200 warehouse barcode scanners fail to authenticate. The scanners support 802.1X but cannot process the SCEP payload from the MDM — they run a proprietary embedded OS with no MDM agent support. What is the most secure architectural solution that maintains network segmentation without requiring replacement of the scanners?
Hint: Consider alternative certificate delivery mechanisms that do not require an MDM agent, and what network segmentation controls should apply to devices that cannot participate in full posture assessment.
View model answer
Since the scanners support 802.1X but not SCEP or MDM enrollment, the most secure approach is to manually provision device certificates using a dedicated certificate template with a restricted key usage profile. The certificates are installed once during a maintenance window. The NAC is configured to accept these certificates but assign the scanners to a dedicated warehouse operations VLAN with strict ACLs — not the full corporate VLAN — because posture assessment is not possible. Alternatively, if manual certificate provisioning is operationally unscalable, configure MAB as a fallback specifically for the MAC OUIs of the scanner hardware, with the NAC assigning them to the same restricted VLAN. Document this as a known exception in your risk register and schedule scanner replacement in the next hardware refresh cycle.
Q2. A network security manager notices that when an employee reports a laptop stolen, the MDM sends a remote wipe command, but the device remains connected to the corporate WiFi for up to 12 hours — the current RADIUS session timeout. During this window, the device could be used to exfiltrate data. How should the architecture be modified to terminate network access immediately upon a device being reported stolen?
Hint: The NAC needs to be informed of the status change instantly rather than waiting for the next authentication cycle. Consider both the session termination mechanism and the re-authentication prevention mechanism.
View model answer
Implement two complementary controls. First, configure the MDM to send a webhook to the NAC immediately upon a device being marked as lost or stolen. The NAC then sends a RADIUS Change of Authorization (CoA) Disconnect-Request message to the specific access point or switch port, terminating the active session immediately. Second, revoke the device's certificate in the CA and ensure the NAC is configured for real-time OCSP checking rather than CRL-based revocation. This means that even if the device reconnects before the CoA is processed, the EAP-TLS authentication will fail at the OCSP check. Both controls together reduce the exposure window from 12 hours to under 60 seconds.
Q3. During a security audit of a large conference centre's network, it is discovered that the SCEP server is exposed to the public internet using a static challenge password to allow remote device enrollment. The auditor flags this as a critical vulnerability. How should the SCEP enrollment process be re-architected to maintain remote enrollment capability while eliminating the static password risk?
Hint: The SCEP server needs a way to verify that the device requesting a certificate is actually authorised by the MDM, without relying on a shared secret that could be extracted from a device or intercepted.
View model answer
Replace the static challenge password with dynamic, per-device one-time challenge passwords generated by the MDM. The workflow becomes: (1) The MDM generates a unique, time-limited challenge password for each device during enrollment. (2) The MDM includes this challenge in the SCEP payload pushed to the device. (3) The device includes the challenge in its CSR. (4) The SCEP server validates the challenge against the MDM via API before forwarding the CSR to the CA. (5) The challenge is invalidated immediately after use. This ensures that only MDM-managed devices can successfully obtain a certificate, and that even if the SCEP URL is discovered, an attacker cannot generate valid certificates without a valid one-time challenge. Additionally, restrict the SCEP server to HTTPS only and implement IP allowlisting for the MDM's egress IPs where possible.