What Is a WiFi Splash Page?
This technical reference guide provides IT managers and network architects with a definitive explanation of WiFi splash pages, their architectural relationship with captive portals, and actionable deployment strategies. It covers implementation best practices, compliance requirements, and how to measure the business impact of your guest WiFi infrastructure.
🎧 Listen to this Guide
View Transcript

Executive Summary
For IT managers and network architects operating at scale, the distinction between network access control and user presentation is critical. A WiFi splash page is the presentation layer—the branded, interactive web interface presented to users connecting to a guest wireless network. While often conflated with a captive portal (the underlying network mechanism that intercepts traffic), the splash page serves as the front door to the user experience, handling authentication, data capture, and compliance consent.
Deploying an effective splash page requires balancing minimal friction for the user with maximum data fidelity and security for the business. This guide breaks down the technical architecture of splash pages, details implementation strategies across complex environments like hospitality and retail, and provides a framework for turning an operational necessity into a measurable asset using solutions like Guest WiFi .
Technical Deep-Dive: Architecture and Standards
To understand a splash page, one must first understand the architecture of the captive portal that serves it. The captive portal operates at OSI Layers 2 and 3. When a device associates with a guest SSID, it is typically placed into a pre-authentication VLAN. In this state, the access controller intercepts DNS queries and HTTP requests, executing a 302 redirect to the splash page URL.
The splash page itself operates at Layer 7. It is the HTML, CSS, and JavaScript interface that captures user credentials or consent. Modern operating systems (iOS, Android, Windows) utilize built-in Captive Portal Network Assistant (CNA) mechanisms—such as Apple's queries to captivenetwork.apple.com—to detect this redirection and automatically surface the splash page in a pseudo-browser.
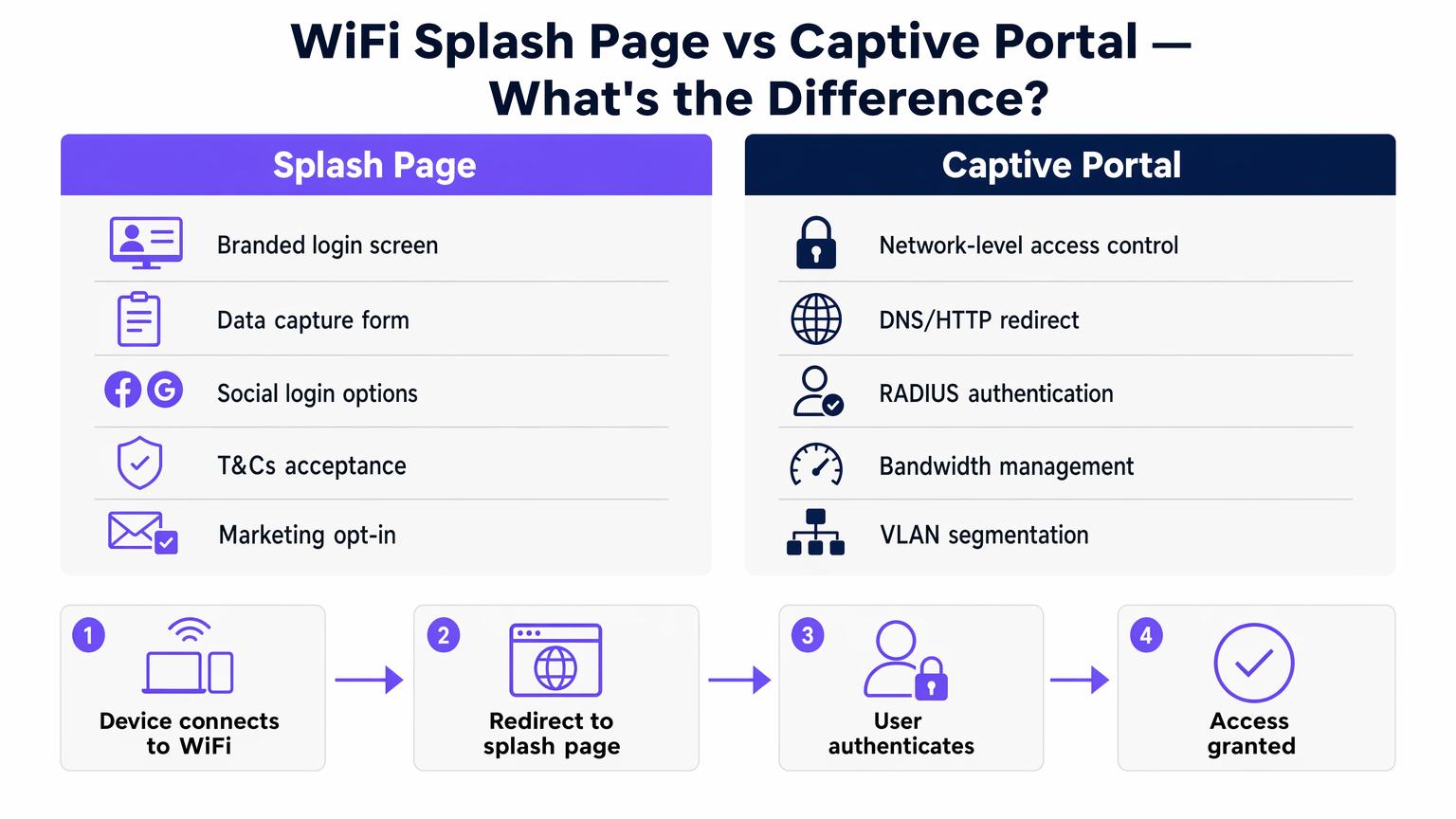
Once the user completes the authentication flow on the splash page, the captive portal controller receives an API or RADIUS (Remote Authentication Dial-In User Service) authorization message. The controller then updates its state tables, moving the device's MAC address to an authorized state, often shifting the client to a post-authentication VLAN with full internet routing and applying bandwidth or session-timeout policies.
Authentication Mechanisms and 802.1X
While simple splash pages rely on open networks with MAC-based authentication post-registration, enterprise environments increasingly look toward secure onboarding. Passpoint (Hotspot 2.0) and profile-based authentication leverage 802.1X/EAP (Extensible Authentication Protocol) to provide encrypted connections. In these scenarios, the splash page may serve as the initial onboarding portal where a user registers and downloads a secure profile, moving away from legacy open SSIDs. Purple operates as a free identity provider for services like OpenRoaming, bridging the gap between splash page registration and seamless, secure subsequent connections.
Implementation Guide
Deploying a splash page across a distributed enterprise requires standardisation. Whether you are outfitting a Retail chain or a Hospitality venue, the implementation approach dictates the operational overhead.
- Architecture Selection: Choose between on-premise controllers and cloud-managed solutions. Cloud-based architectures—detailed in our guide on Cloud-Based vs. On-Premise Captive Portal: Which Is Right for Your Business? —offer centralized management of splash pages across multiple AP vendors, reducing configuration drift.
- Walled Garden Configuration: Ensure that the IP addresses and domains required to load the splash page (including CDNs, social login APIs, and authentication servers) are explicitly permitted in the pre-authentication ACLs (Access Control Lists). Failure to configure the walled garden correctly results in a splash page that fails to load.
- Authentication Strategy: Select authentication methods that align with business goals. Social login (OAuth) and form-based registration yield high-quality data for WiFi Analytics , whereas a simple click-through offers high throughput but zero data capture.
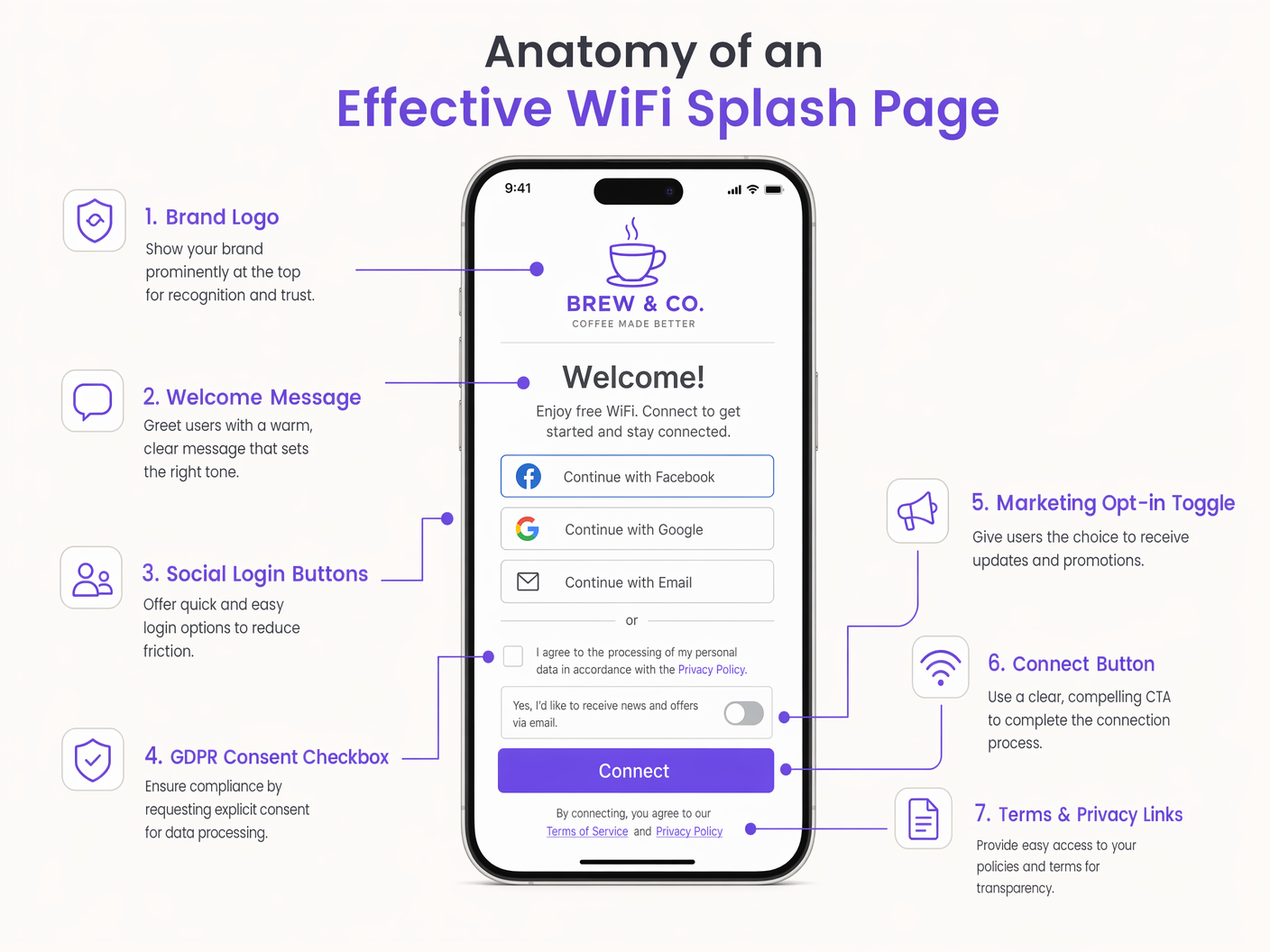
- Responsive Design: Over 80% of guest WiFi connections originate from mobile devices. The splash page must be highly responsive, utilizing minimal payloads to ensure rapid rendering even in high-density, high-interference RF environments.
Best Practices and Compliance
A splash page is a primary compliance checkpoint. Operating in jurisdictions governed by GDPR or CCPA requires strict adherence to data privacy standards.
- Explicit Consent: Marketing opt-ins must utilize unchecked checkboxes. Pre-ticked boxes violate GDPR Article 7.
- Data Minimisation: Only request data necessary for the service or agreed-upon marketing.
- PCI DSS Scope: Ensure the guest WiFi network is logically separated (via VLANs and firewall rules) from the corporate network and point-of-sale (POS) systems to prevent scope creep into PCI compliance audits.
- Accessibility: Ensure the splash page complies with WCAG (Web Content Accessibility Guidelines) standards, utilizing appropriate contrast ratios and screen-reader-friendly HTML semantics.
Listen to our senior technical briefing on splash page architecture and deployment strategies:
Troubleshooting & Risk Mitigation
Even well-architected deployments encounter issues. Common failure modes include:
- HTTPS Interception Failures: As the web moves entirely to HTTPS, legacy captive portals attempting to intercept HTTPS traffic without a trusted certificate will trigger severe browser security warnings (HSTS errors). The mitigation is relying on the OS-level CNA mechanisms which utilize HTTP for detection, or implementing secure onboarding via Passpoint.
- DNS Resolution Latency: If the DNS server assigned in the pre-authentication state is slow or unresponsive, the initial redirect will fail. Ensure local, highly available DNS resolvers are utilized for the guest network.
- MAC Randomization: Modern mobile OSs utilize randomized MAC addresses for privacy. While this complicates long-term tracking of unauthenticated users, splash pages that tie sessions to authenticated user profiles (e.g., email or CRM ID) mitigate the impact on analytics and session management.
ROI & Business Impact
The business impact of a splash page deployment transitions IT from a cost centre to a revenue enabler. By capturing first-party data, the splash page feeds directly into marketing and operational systems.
For example, in Transport hubs, splash page analytics provide real-time footfall and dwell time metrics. The return on investment is measured not just in reduced support tickets due to a seamless connection experience, but in the actionable data generated. The network effect strategy—offering free connectivity to drive user acquisition—relies entirely on the splash page as the conversion mechanism. A well-optimised splash page reduces churn, enables retail media monetisation, and supports loyalty integrations, delivering measurable business value long after the initial connection.
Key Terms & Definitions
Splash Page
The web-based presentation layer presented to a user attempting to connect to a guest network, used for authentication, consent, and branding.
The primary user interface for guest WiFi, managed jointly by IT and marketing.
Captive Portal
The network-layer infrastructure that intercepts traffic and redirects unauthenticated users to the splash page.
The gatekeeper mechanism configured on access controllers or cloud platforms.
Walled Garden
A whitelist of IP addresses or domains that a user can access before completing authentication on the splash page.
Critical for allowing social logins and CDNs to function during the login process.
Captive Network Assistant (CNA)
The OS-level pseudo-browser that automatically detects a captive portal and pops up the splash page.
Reduces user friction by eliminating the need to manually open a browser to trigger the redirect.
RADIUS
Remote Authentication Dial-In User Service; a networking protocol that provides centralized Authentication, Authorization, and Accounting (AAA).
Used by the captive portal to validate credentials and apply network policies post-login.
MAC Randomization
A privacy feature in modern operating systems that generates a temporary MAC address for each wireless network.
Impacts the ability to track returning devices without requiring them to re-authenticate via the splash page.
VLAN Segmentation
The practice of logically dividing a physical network into multiple broadcast domains.
Essential for isolating guest WiFi traffic from corporate infrastructure for security and PCI compliance.
Passpoint (Hotspot 2.0)
A standard for seamless, secure authentication to public WiFi networks using 802.1X, bypassing the traditional open SSID splash page.
The evolution of guest WiFi, where the splash page serves as the initial provisioning portal rather than a daily login screen.
Case Studies
A 200-room hotel needs to deploy a guest WiFi solution that integrates with their property management system (PMS) to restrict bandwidth for non-guests while offering premium tiers for loyalty members.
- Deploy a cloud-managed captive portal integrated with the existing AP infrastructure via RADIUS.
- Configure the splash page to request Room Number and Guest Last Name.
- The captive portal queries the PMS API via a webhook to validate the credentials.
- Upon successful validation, the RADIUS server returns a vendor-specific attribute (VSA) applying a premium bandwidth policy profile to the user's session.
A large retail chain experiences a 40% drop-off rate on their guest WiFi splash page. They currently require a 6-field registration form including postal address.
- Redesign the splash page to utilize Social Login (Google, Apple) and a simplified 2-field email registration form.
- Implement progressive profiling: capture minimal data on the first visit, and prompt for additional details (like birth month for loyalty rewards) upon subsequent reconnections.
- Ensure the walled garden includes the necessary OAuth domains for social providers.
Scenario Analysis
Q1. A venue reports that users connecting via Android devices are seeing the splash page, but users on iOS devices are getting a blank white screen. What is the most likely architectural configuration error?
💡 Hint:Consider the specific domains that different operating systems use to detect captive portals.
Show Recommended Approach
The walled garden (pre-authentication ACL) is likely misconfigured. It is allowing the Android connectivity check domains but blocking Apple's CNA domains (e.g., captivenetwork.apple.com). The access controller must be updated to allow traffic to the specific domains Apple uses for captive portal detection.
Q2. The marketing team wants to add a Facebook login option to the existing splash page. From a network engineering perspective, what configuration change is required before this can function?
💡 Hint:How does the device reach Facebook's servers before the user is fully authenticated?
Show Recommended Approach
The network engineer must update the walled garden to include Facebook's OAuth domains and CDNs. Without this, the device cannot reach Facebook to complete the authentication handshake while still in the restricted pre-authentication state.
Q3. During a compliance audit, it is discovered that the splash page includes a pre-ticked box stating 'I agree to receive marketing emails'. What is the immediate risk, and what is the remediation?
💡 Hint:Consider GDPR Article 7 regarding consent.
Show Recommended Approach
The immediate risk is non-compliance with GDPR, which mandates that consent must be freely given and unambiguous. Pre-ticked boxes are legally invalid. The remediation is to immediately update the splash page HTML to ensure the marketing opt-in checkbox is unchecked by default, requiring an affirmative action from the user.



