What Is WiFi Security? A Complete Guide to Wireless Network Security
A comprehensive technical reference for IT leaders on securing enterprise wireless networks. This guide covers the evolution of encryption protocols, architectural best practices for segmentation, and defense strategies against common WiFi threats.
🎧 Listen to this Guide
View Transcript
- Executive Summary
- Technical Deep-Dive: The Evolution of WiFi Security Protocols
- WEP (Wired Equivalent Privacy)
- WPA (Wi-Fi Protected Access)
- WPA2
- WPA3: The Current Standard
- Common WiFi Security Threats
- Implementation Guide: Architectural Best Practices
- 1. Network Segmentation and VLANs
- 2. Robust Authentication Mechanisms
- 3. Implementing Client Isolation
- Best Practices & Industry Standards
- Troubleshooting & Risk Mitigation
- ROI & Business Impact

Executive Summary
For modern enterprises—whether operating a global retail chain, a multi-site healthcare trust, or a high-capacity stadium—WiFi is no longer just an amenity; it is critical infrastructure. However, as the reliance on wireless networks grows, so does the attack surface. A compromised wireless network exposes the organization to data breaches, compliance violations (such as PCI DSS and GDPR), and severe reputational damage.
This comprehensive technical guide explores the fundamentals of WiFi security, detailing the evolution of encryption standards, common threat vectors, and architectural best practices for securing enterprise wireless environments. We will examine how to deploy robust segmentation, implement strong authentication mechanisms, and leverage platforms like Guest WiFi to maintain a secure, compliant, and high-performing network while extracting actionable business intelligence through WiFi Analytics .
Technical Deep-Dive: The Evolution of WiFi Security Protocols
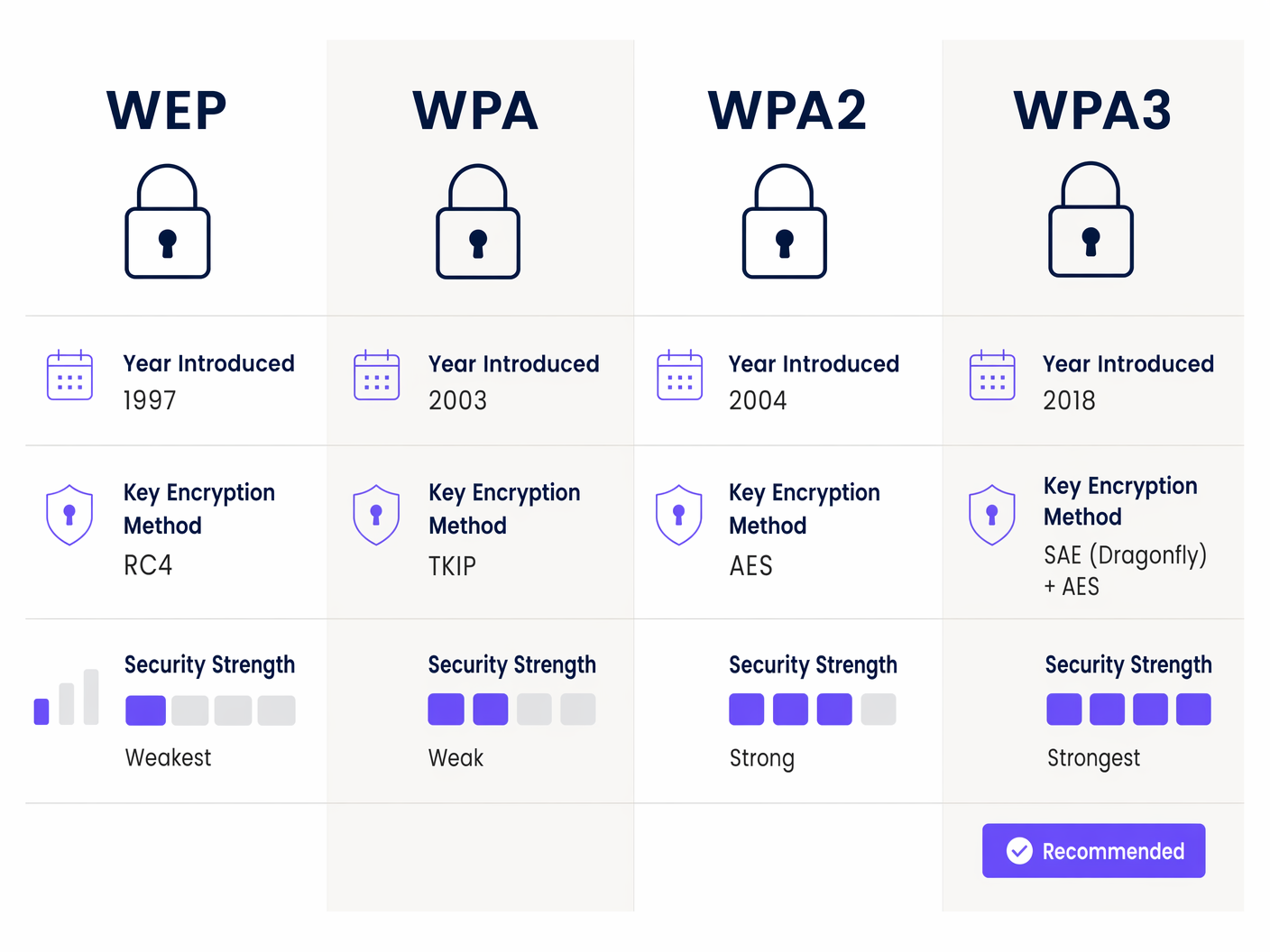
Understanding the current state of WiFi security requires a brief look at its history. The progression of security protocols reflects an ongoing arms race between network engineers and malicious actors.
WEP (Wired Equivalent Privacy)
Introduced in 1997, WEP was the original 802.11 security standard. It utilized the RC4 stream cipher for confidentiality and CRC-32 for integrity. However, cryptographic flaws in its implementation made it trivially easy to crack using readily available tools. WEP is entirely deprecated and its presence on any modern network constitutes a critical vulnerability.
WPA (Wi-Fi Protected Access)
Introduced in 2003 as an interim solution to WEP's flaws, WPA implemented the Temporal Key Integrity Protocol (TKIP). While it improved security by dynamically changing keys, it still relied on the vulnerable RC4 cipher and was eventually compromised.
WPA2
Ratified in 2004, WPA2 became the enterprise standard for over a decade. It introduced the Advanced Encryption Standard (AES) operating in Counter Mode Cipher Block Chaining Message Authentication Code Protocol (CCMP). WPA2 provided robust security but was eventually found vulnerable to offline dictionary attacks against the four-way handshake, most notably the KRACK (Key Reinstallation Attacks) vulnerability discovered in 2017.
WPA3: The Current Standard
Introduced in 2018, WPA3 addresses the shortcomings of WPA2 and is the mandatory standard for all new Wi-Fi CERTIFIED devices.
Key Enhancements in WPA3:
- Simultaneous Authentication of Equals (SAE): Replaces the Pre-Shared Key (PSK) exchange. SAE is a secure key establishment protocol that provides forward secrecy and is highly resistant to offline dictionary attacks. Even if a user chooses a weak password, the handshake cannot be cracked offline.
- WPA3-Enterprise: Offers an optional 192-bit cryptographic strength mode, utilizing Suite B cryptography (e.g., ECDSA with a 384-bit curve and HMAC-SHA384). This is critical for highly sensitive environments like government or financial institutions.
- Opportunistic Wireless Encryption (OWE): Addresses the "is public wifi safe" question. OWE, branded as Wi-Fi Enhanced Open, provides individualized data encryption on open networks without requiring user authentication, mitigating passive eavesdropping.
Common WiFi Security Threats
Enterprise networks face a variety of sophisticated threats. Understanding these vectors is crucial for implementing effective countermeasures.
- Rogue Access Points & Evil Twins: An attacker connects an unauthorized AP to the corporate network (Rogue AP) or broadcasts a legitimate-looking SSID to trick users into connecting (Evil Twin). This allows for traffic interception and credential theft.
- Man-in-the-Middle (MitM) Attacks: Attackers position themselves between the client and the AP to intercept, read, or modify unencrypted traffic.
- Deauthentication Attacks: Attackers send spoofed deauthentication frames to disconnect a client from the AP. This is often a precursor to an Evil Twin attack, forcing the client to reconnect to the attacker's AP.
- Credential Harvesting: Attackers deploy fake captive portals that mimic the legitimate splash page, tricking users into entering corporate credentials or personal information.

Implementation Guide: Architectural Best Practices
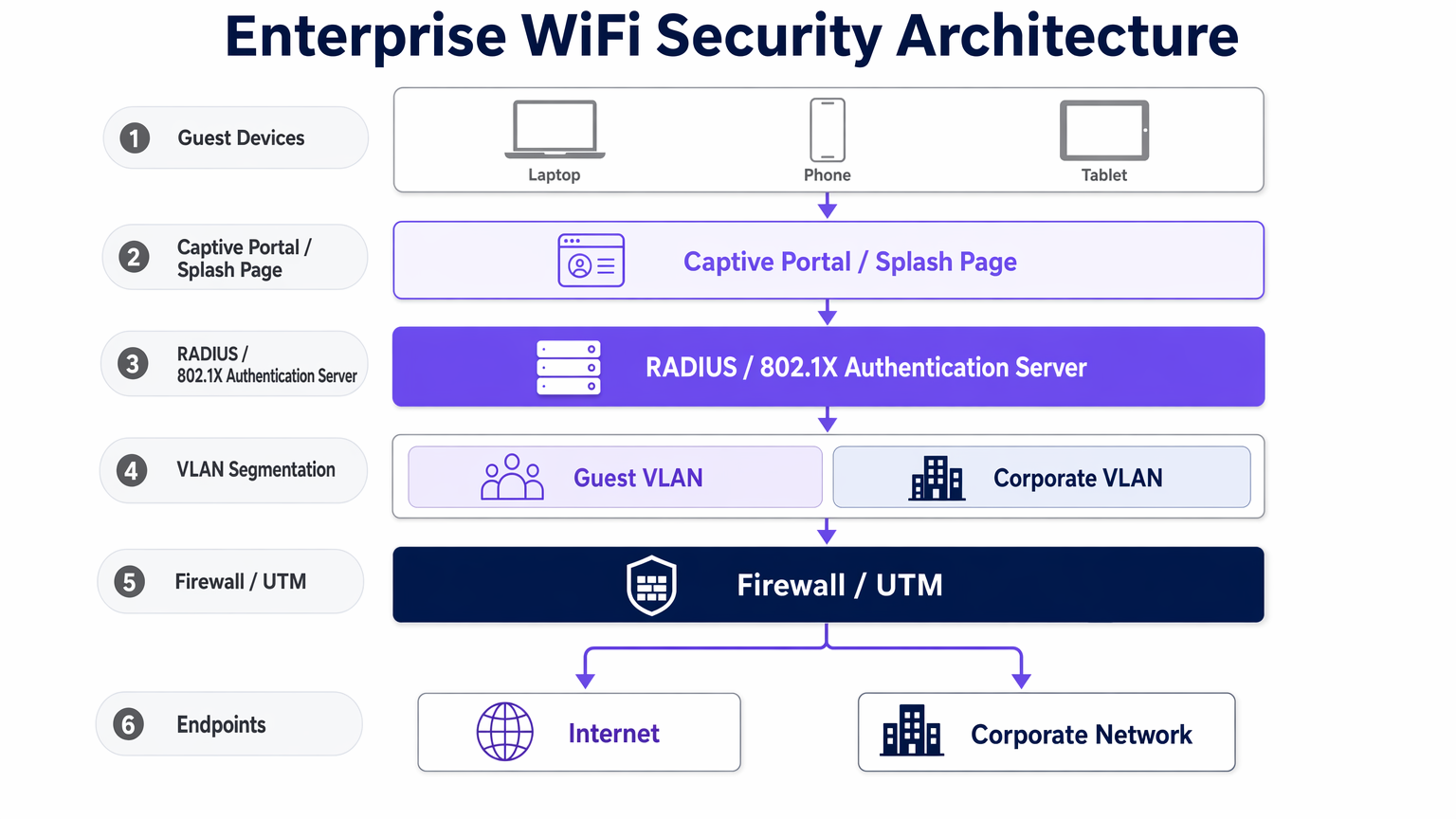
Securing an enterprise wireless network requires a defense-in-depth approach, moving beyond simple encryption to robust architectural segmentation and access control.
1. Network Segmentation and VLANs
The foundational principle of network security is isolation. Guest traffic, corporate traffic, IoT devices, and Point-of-Sale (PoS) systems must reside on logically separated Virtual Local Area Networks (VLANs).
- Guest VLAN: Must be strictly isolated from internal subnets. Traffic should be routed directly to the internet firewall.
- IoT VLAN: IoT devices often have weak security postures. Isolate them to prevent lateral movement if compromised.
2. Robust Authentication Mechanisms
- Corporate Access (802.1X): Never use Pre-Shared Keys for corporate access. Implement 802.1X authentication backed by a RADIUS server, integrating with directory services (e.g., Active Directory). This ensures that network access is tied to individual user identities and device certificates.
- Guest Access (Captive Portals): Implement a secure captive portal for guest onboarding. A robust platform like Purple not only handles terms of service acceptance but also facilitates secure authentication via social logins or SMS, ensuring traceability. For examples of effective implementations, review The 10 Best WiFi Splash Page Examples (And What Makes Them Work) or the French equivalent, Les 10 meilleurs exemples de pages de démarrage WiFi (et ce qui les rend efficaces) .
3. Implementing Client Isolation
For guest networks, enable client isolation (also known as AP isolation). This prevents devices connected to the same AP or VLAN from communicating directly with each other, mitigating the risk of peer-to-peer attacks on the public network.
Best Practices & Industry Standards
- Wireless Intrusion Prevention Systems (WIPS): Deploy WIPS to continuously monitor the RF spectrum for rogue APs, Evil Twins, and anomalous behavior. A robust WIPS can automatically contain threats by sending deauthentication frames to rogue devices.
- Passpoint (Hotspot 2.0): To streamline secure guest access, implement Passpoint. This allows devices to automatically and securely authenticate to the network using credentials provided by their mobile carrier or a third-party identity provider. Purple acts as a free identity provider for services like OpenRoaming under the Connect license, facilitating seamless and secure connectivity.
- Compliance Considerations: Ensure your WiFi architecture aligns with relevant regulatory frameworks. For example, PCI DSS requires strict segmentation of the cardholder data environment from public WiFi, while GDPR mandates the secure handling of any personally identifiable information (PII) collected during guest onboarding.
Troubleshooting & Risk Mitigation
- Failure Mode: Rogue AP Proliferation: In large venues like Retail environments, unauthorized APs can easily be plugged into exposed Ethernet ports. Mitigation: Implement port security (802.1X on wired ports) and actively monitor WIPS alerts.
- Failure Mode: Weak Captive Portal Security: A poorly configured captive portal can be bypassed or spoofed. Mitigation: Ensure the captive portal uses HTTPS with valid SSL certificates. Implement rate limiting to prevent brute-force attacks against authentication forms.
- Failure Mode: SD-WAN Integration Issues: When integrating WiFi with SD-WAN architectures, ensure security policies are consistent across the overlay network. For more context, see The Core SD WAN Benefits for Modern Businesses or Die zentralen SD-WAN-Vorteile für moderne Unternehmen .
ROI & Business Impact
Investing in robust WiFi security is not merely a cost center; it is a critical enabler for digital transformation and risk mitigation.
- Risk Mitigation: The cost of a data breach—including regulatory fines, legal fees, and reputational damage—far exceeds the investment in secure infrastructure (WPA3 hardware, WIPS, RADIUS servers).
- Operational Efficiency: Automated onboarding via 802.1X and Passpoint reduces helpdesk tickets related to password resets and connectivity issues.
- Data Integrity: Secure guest onboarding ensures the integrity of the first-party data collected for marketing and analytics. By utilizing a secure platform for Guest WiFi , venues in Hospitality and Transport can confidently leverage this data to drive loyalty programs and personalized engagement without compromising user privacy.
Key Terms & Definitions
WPA3 (Wi-Fi Protected Access 3)
The latest Wi-Fi security standard, providing enhanced cryptographic strength and replacing the vulnerable PSK exchange with SAE.
Required for all new enterprise deployments to protect against offline dictionary attacks.
SAE (Simultaneous Authentication of Equals)
A secure key establishment protocol used in WPA3 that provides forward secrecy and prevents offline cracking of passwords.
Replaces the older 4-way handshake used in WPA2, significantly improving security for networks using shared passwords.
802.1X
An IEEE standard for port-based Network Access Control, providing an authentication mechanism to devices wishing to attach to a LAN or WLAN.
The standard for enterprise corporate access, tying network authentication to directory services via a RADIUS server.
VLAN (Virtual Local Area Network)
A logical subnetwork that groups a collection of devices from different physical LANs.
Essential for segmenting guest, corporate, and IoT traffic to limit the blast radius of a potential breach.
Client Isolation
A security feature that prevents devices connected to the same AP or VLAN from communicating with each other.
Mandatory for guest networks to prevent peer-to-peer attacks and malware propagation among public users.
WIPS (Wireless Intrusion Prevention System)
A network device that monitors the radio spectrum for the presence of unauthorized access points and can automatically take countermeasures.
Critical for detecting and neutralizing Rogue APs and Evil Twin attacks in enterprise environments.
Passpoint (Hotspot 2.0)
A standard that enables cellular-like roaming for Wi-Fi networks, allowing automatic and secure authentication.
Improves user experience and security by eliminating the need to manually connect and authenticate via captive portals.
OWE (Opportunistic Wireless Encryption)
A standard that provides individualized data encryption on open Wi-Fi networks without requiring user authentication.
Improves security on public networks (like coffee shops or airports) by protecting against passive eavesdropping.
Case Studies
A 200-room hotel needs to provide seamless guest WiFi while ensuring strict compliance with PCI DSS for their on-site restaurants and bars. How should the network architecture be designed?
The network must be strictly segmented using VLANs. The Guest WiFi must operate on an isolated VLAN with client isolation enabled, routing traffic directly to the internet. The PoS systems in the restaurants must reside on a separate, highly restricted VLAN (the Cardholder Data Environment), firewalled off from all other traffic. Guest onboarding should be managed via a secure captive portal to capture marketing data compliantly.
A large retail chain is experiencing frequent 'Evil Twin' attacks where malicious actors set up rogue APs to steal customer credentials. What is the recommended technical mitigation?
Deploy a dedicated Wireless Intrusion Prevention System (WIPS). The WIPS will monitor the RF spectrum for unauthorized SSIDs mimicking the corporate network. When detected, the WIPS can automatically contain the threat by transmitting deauthentication frames to prevent clients from connecting to the rogue AP.
Scenario Analysis
Q1. You are designing the network for a large [Healthcare](/industries/healthcare) facility. They require seamless roaming for medical devices (IoT) and secure access for staff and patients. How do you segment this network?
💡 Hint:Consider the varying security capabilities of IoT devices compared to corporate laptops.
Show Recommended Approach
Implement strict VLAN segmentation. Create a dedicated IoT VLAN with restricted access only to necessary servers (no internet access if possible). Staff devices should use 802.1X on a Corporate VLAN. Patients should use a Guest VLAN with client isolation, routed through a captive portal directly to the internet.
Q2. A venue operator wants to deploy OpenRoaming to improve the guest experience but is concerned about security compared to their existing WPA2-PSK setup. What is your advice?
💡 Hint:Compare the security of shared passwords versus individualized authentication.
Show Recommended Approach
OpenRoaming (using Passpoint/802.1X) is significantly more secure than WPA2-PSK. It uses enterprise-grade encryption and individualized authentication, eliminating the risks associated with shared passwords (like offline dictionary attacks) and providing a seamless user experience.
Q3. During a security audit, legacy barcode scanners in a warehouse are found to only support WPA2-PSK. Upgrading them is not budgeted for this year. How do you mitigate the risk?
💡 Hint:If you can't upgrade the protocol, how can you limit the blast radius?
Show Recommended Approach
Isolate the legacy scanners onto a dedicated, highly restricted VLAN. Implement strict firewall rules so this VLAN can only communicate with the specific inventory servers required for operation, blocking all other internal and external access. Rotate the PSK frequently.



