Technical Guides
Deep, expert-led guides covering guest WiFi, analytics, captive portals, and modern venue technology. Each guide includes diagrams, worked examples, and audio podcasts.
209 guides
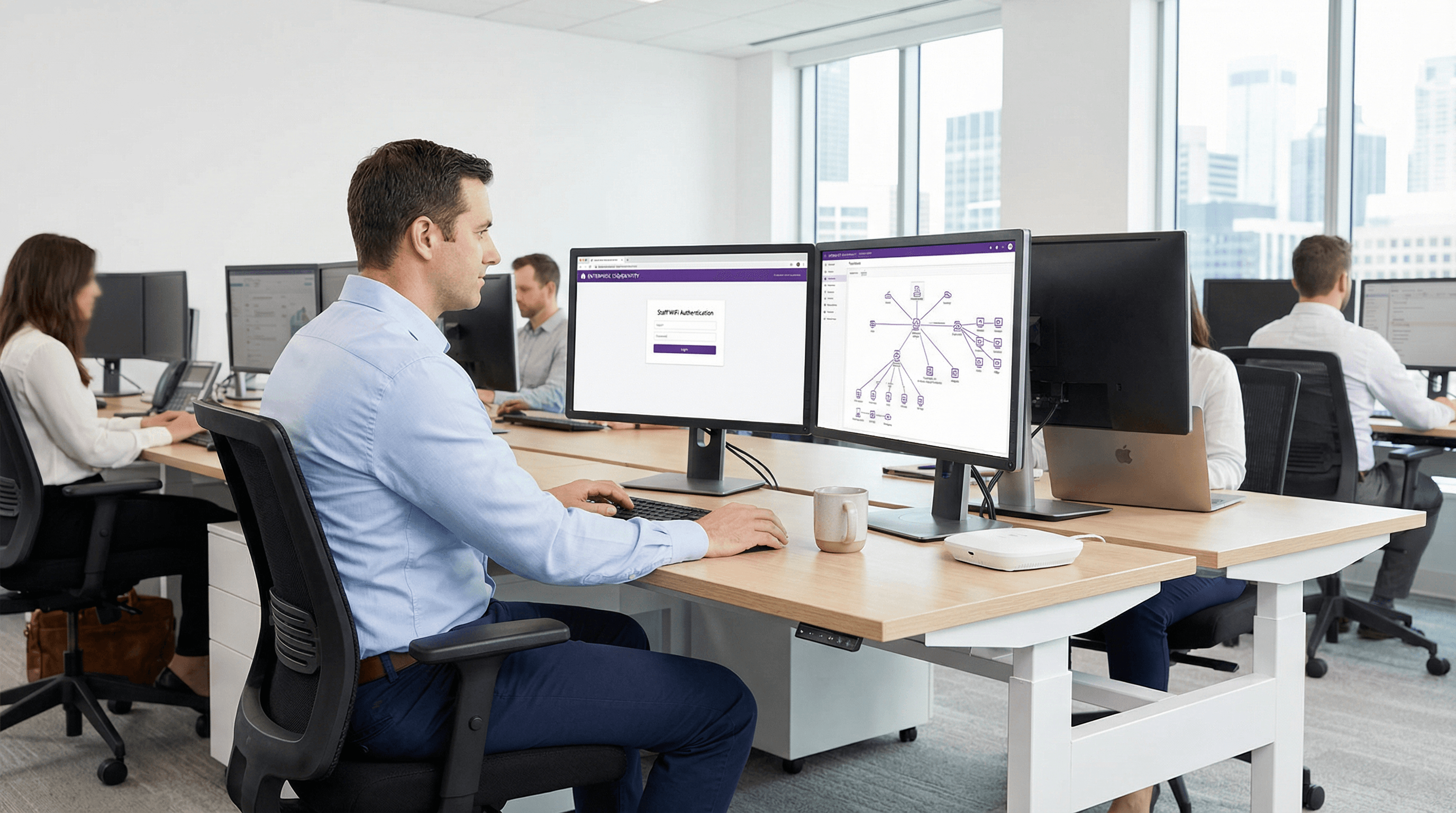
SAML Authentication for Staff WiFi
This guide provides a technical deep-dive into leveraging SAML 2.0 for enterprise-grade staff WiFi authentication, covering protocol architecture, Identity Provider integration, and deployment best practices. It equips IT leaders and network architects with actionable guidance on connecting Azure AD or Okta to the Purple WiFi intelligence platform to replace insecure pre-shared keys with robust, identity-driven access control. The result is a measurable improvement in security posture, compliance readiness, and operational efficiency across hotels, retail chains, stadiums, and public-sector venues.
NAC (Network Access Control) Explained
An authoritative technical reference for IT leaders on Network Access Control (NAC), explaining its architecture, deployment models, and critical role in enterprise WiFi security. This guide provides actionable insights for securing network access across hospitality, retail, and corporate environments, detailing how platforms like Purple integrate to enforce robust access policies.
MAC Address Randomisation: What It Is and How to Handle It
This guide provides IT leaders and network architects with a comprehensive technical overview of MAC address randomisation. It details the impact on enterprise and guest WiFi networks and presents actionable strategies, including Purple's SecurePass technology, to mitigate risks and maintain robust analytics and security.
802.1X vs PSK vs Open WiFi: Which Authentication Method Is Right for You?
This guide provides a definitive, vendor-neutral comparison of the three primary WiFi authentication methods—802.1X (WPA2/3-Enterprise), Pre-Shared Key (PSK), and Open WiFi—tailored for IT managers, network architects, and CTOs in hospitality, retail, events, and the public sector. It cuts through technical complexity to deliver actionable deployment guidance, real-world case studies, and a clear decision framework for securing both staff and guest networks. Understanding which authentication model to deploy is not merely a technical choice; it is a strategic business decision with direct implications for security posture, regulatory compliance, operational efficiency, and the ability to extract commercial value from your WiFi infrastructure.
How to Integrate Guest WiFi Data with Your CRM
This guide provides a comprehensive technical reference for IT managers, network architects, and marketing leaders on integrating guest WiFi analytics with CRM platforms such as Salesforce and HubSpot. It covers the strategic rationale, core architectural patterns (Direct API and Webhooks), available data fields, and step-by-step deployment guidance. Venue operators in hospitality, retail, and events will find actionable frameworks for building a compliant, scalable, first-party data pipeline that drives measurable marketing ROI.
GDPR Compliance for Guest WiFi Data Collection
This guide provides IT managers, network architects, and Data Protection Officers with a comprehensive, actionable framework for achieving GDPR compliance across guest WiFi deployments in hospitality, retail, and public-sector venues. It covers the full spectrum of data collected by guest WiFi networks, the legal requirements for obtaining valid consent, best-practice data retention policies, and how to implement a defensible compliance architecture. Venue operators will learn how to transform their guest WiFi from a potential regulatory liability into a strategic asset that builds customer trust and drives measurable business intelligence.
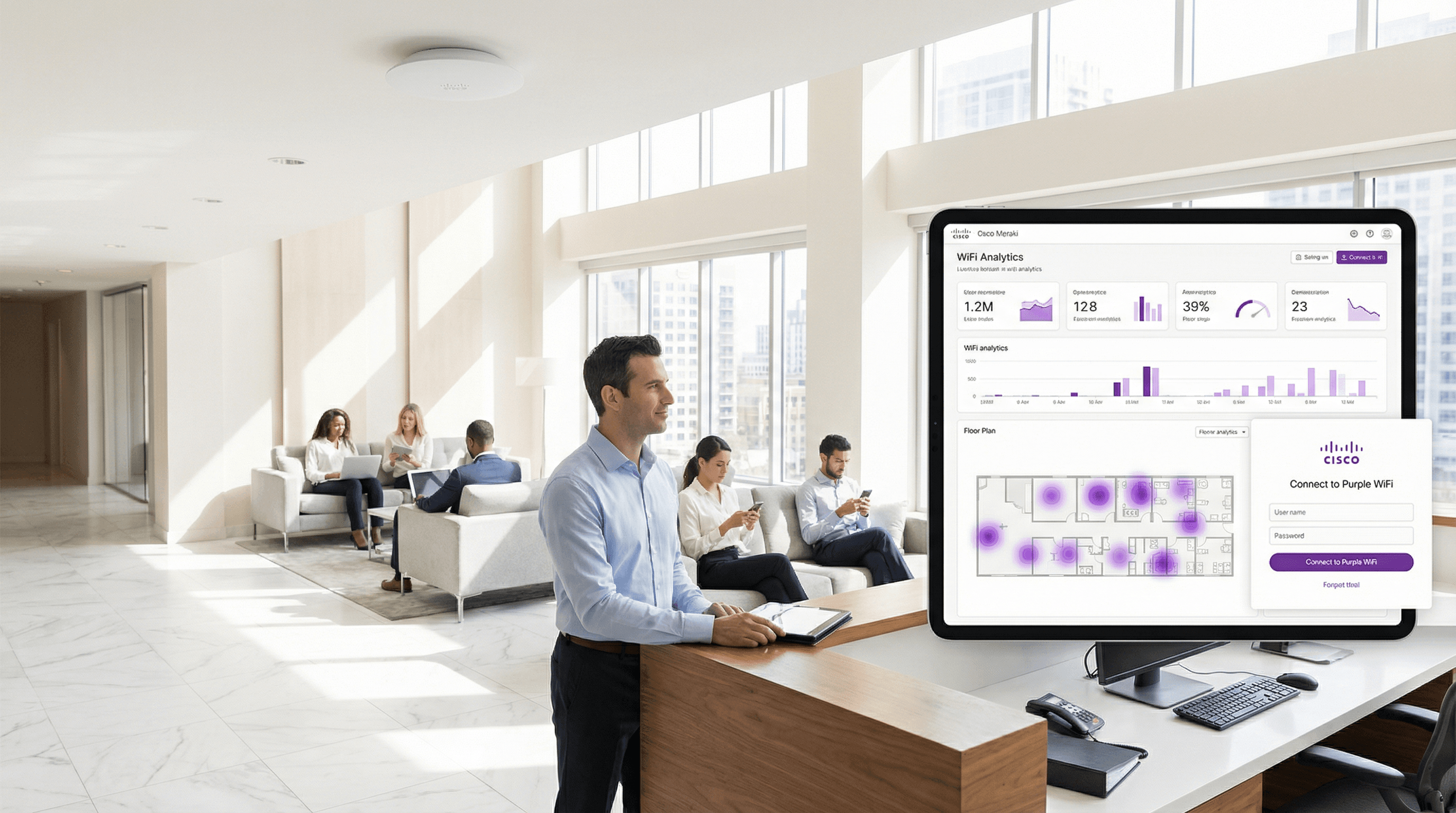
Cisco Meraki Integration with Purple WiFi
This guide provides a definitive technical reference for deploying Purple WiFi on Cisco Meraki infrastructure, covering the dual-layer integration architecture — Dashboard API provisioning and Captive Portal API authentication — alongside step-by-step RADIUS and splash page configuration. It is designed for network engineers and IT managers who need to move from a functional guest WiFi deployment to a strategic guest intelligence platform, with measurable ROI outcomes drawn from live enterprise deployments including McDonald's Belgium, Harrods, and AGS Airports.
What is RADIUS Authentication and How Does It Work?
This guide provides a definitive technical reference on RADIUS authentication for IT leaders managing enterprise and guest WiFi deployments. It demystifies the AAA protocol, explains how 802.1X and EAP methods work together, and details how Purple's cloud-based platform simplifies deployment for hotels, retail chains, stadiums, and public-sector organisations. Readers will leave with a clear implementation roadmap, real-world case studies, and the decision frameworks needed to migrate from insecure pre-shared keys to a robust, identity-driven network access control architecture.
What is a Captive Portal and How Does It Work?
A comprehensive technical reference for IT managers and venue operators on the architecture, deployment, and business impact of captive portals. This guide provides actionable insights into device detection, the Captive Network Assistant (CNA), and best practices for implementation in enterprise environments.
Identity-Based Networking: What It Is and Why It Matters
This guide provides a comprehensive technical reference on Identity-Based Networking (IBN) — what it is, how it works, and why it is a critical investment for any organisation managing large, diverse user populations across hotels, retail chains, stadiums, and public-sector venues. It covers the core IEEE 802.1X architecture, Purple's cloud-native implementation, real-world deployment scenarios, and a clear ROI framework to support procurement decisions.
Ubiquiti UniFi and Purple WiFi: Integration Guide
This guide provides a definitive technical reference for integrating the Purple WiFi intelligence platform with Ubiquiti UniFi network deployments, covering architecture, step-by-step controller configuration, and GDPR-compliant data capture. It is designed for IT managers, network architects, and operations directors who need to deploy a secure, feature-rich guest WiFi experience across hospitality, retail, events, and public-sector environments. By correctly configuring the UniFi Network Controller to leverage Purple's external captive portal, organisations can transform a standard cost centre into a valuable source of visitor analytics and marketing intelligence.

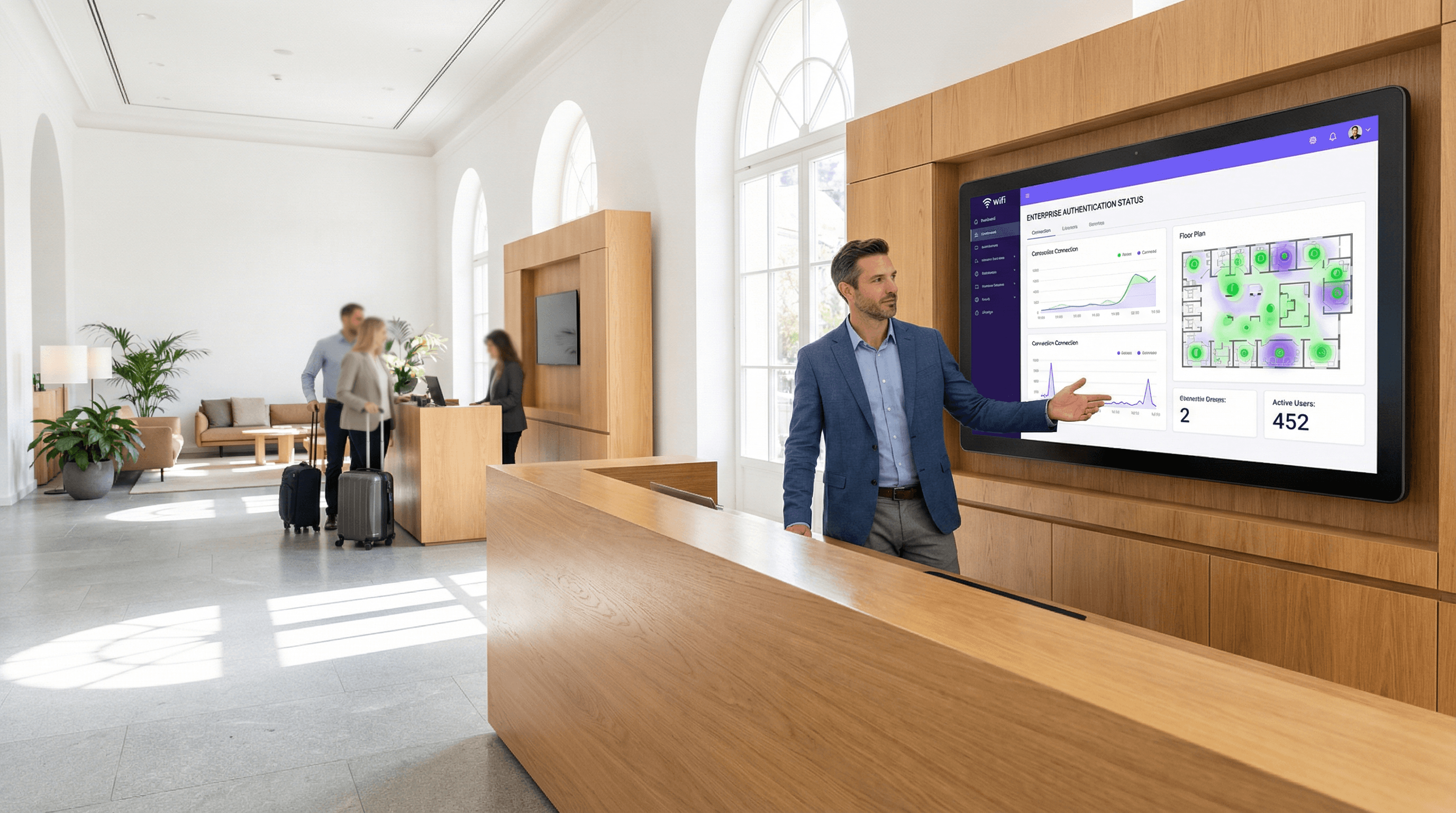
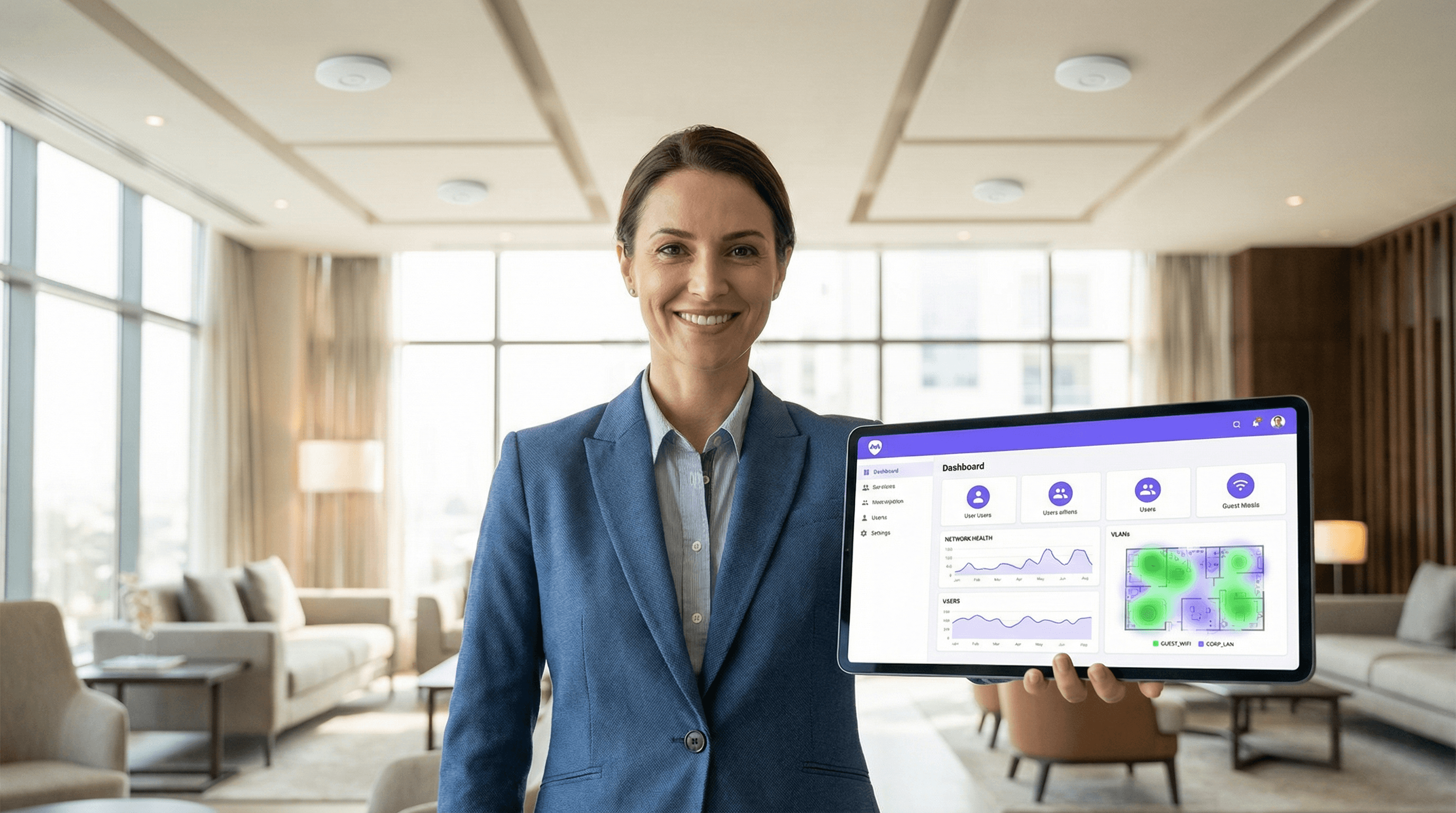
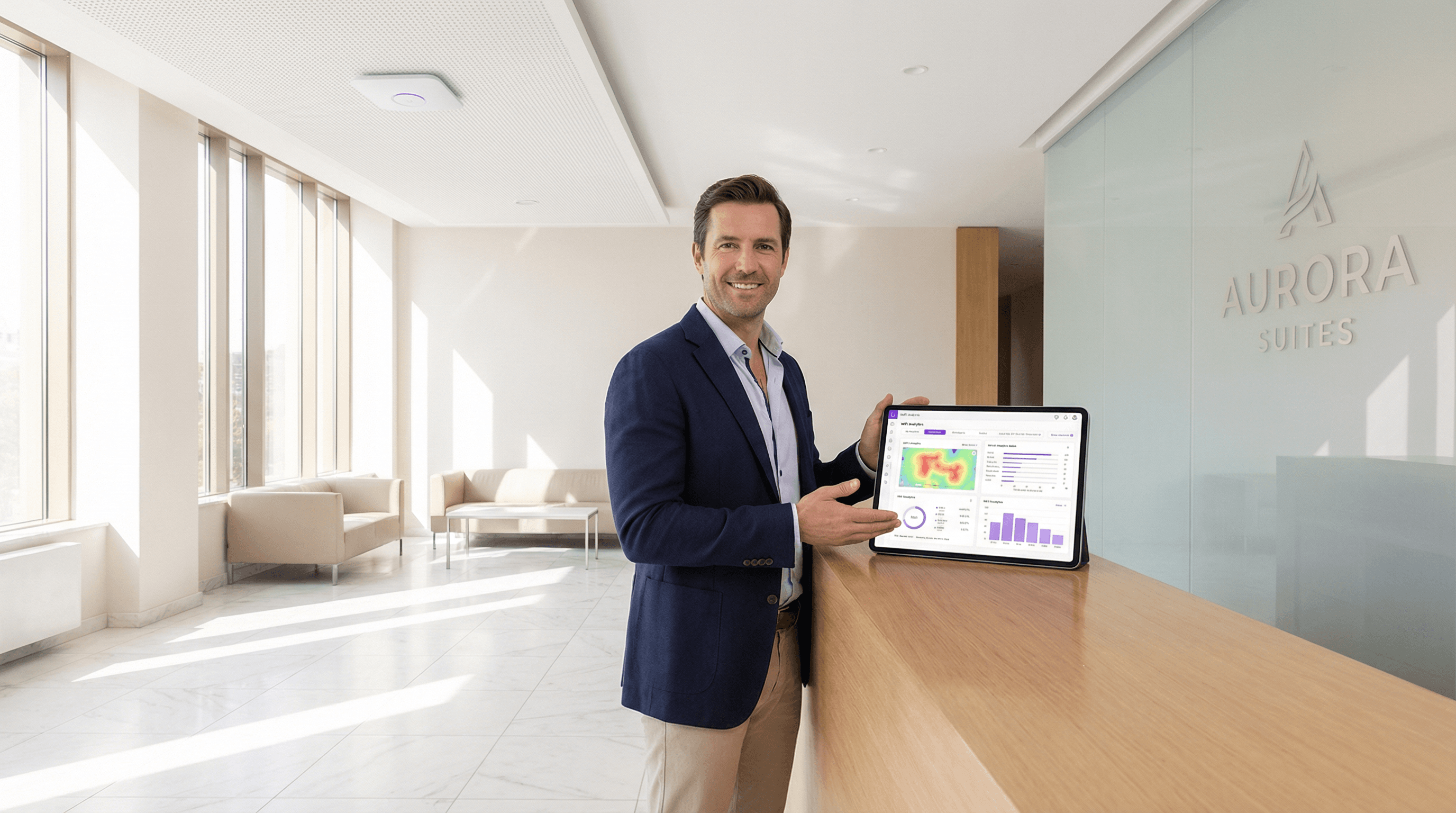
How Guest WiFi Supports Venue Analytics and Footfall Tracking
This guide provides a technical and operational framework for leveraging guest WiFi to gain deep insights into visitor behaviour within physical venues. It details how to capture and analyse data for footfall tracking and dwell time calculation, enabling IT and operations leaders to make data-driven decisions that optimize staffing, enhance venue layout, and increase business ROI.
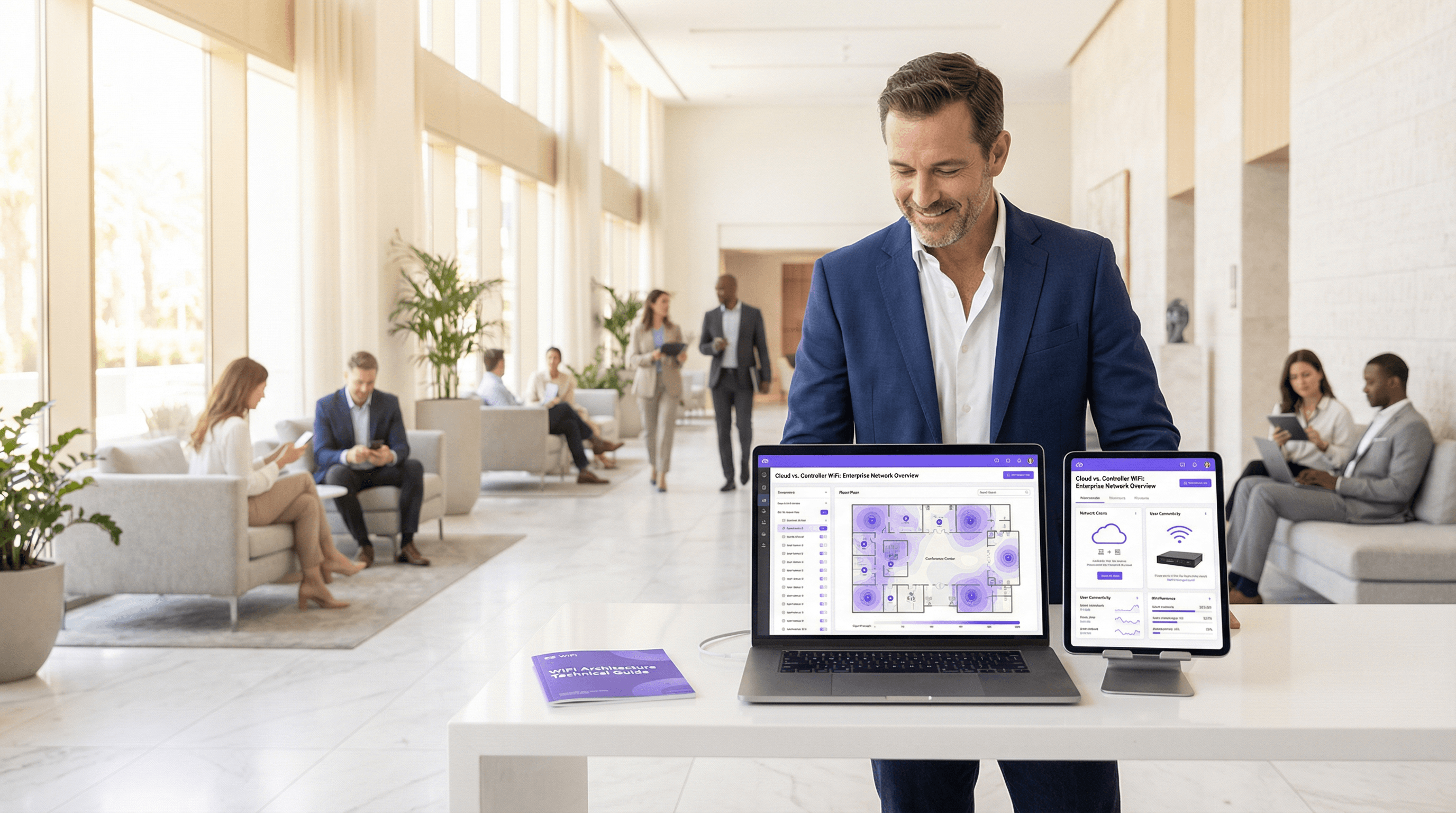
Cloud-Managed WiFi vs Controller-Based WiFi: Which Should You Choose?
This guide provides a vendor-neutral technical comparison of cloud-managed WiFi and controller-based (on-premise) WiFi architectures, helping IT managers, network architects, and CTOs make an informed deployment decision. It covers the architectural trade-offs across scalability, data sovereignty, cost model, and offline resilience, with real-world case studies from hospitality, retail, and public-sector environments. It also explains how Purple's WiFi intelligence platform integrates with either architecture to deliver guest experience management, first-party data capture, and GDPR-compliant analytics.
Multi-Tenant WiFi: Architecture and Management
This authoritative technical reference guide provides IT managers, network architects, and venue operators with a comprehensive framework for designing, deploying, and managing multi-tenant WiFi networks across complex environments such as hotels, retail centres, stadiums, and multi-dwelling units (MDUs). It covers the critical architectural differences between single-venue and multi-tenant deployments, with a focus on tenant isolation, bandwidth management, and compliance. By leveraging Purple's enterprise WiFi intelligence platform, organisations can transform shared network infrastructure into a secure, scalable, and commercially valuable service.

IPSK Explained: Identity Pre-Shared Keys for WiFi Access
This guide provides IT managers, network architects, and venue operations directors with a definitive technical reference on Identity Pre-Shared Keys (IPSK) for WiFi access — explaining the architecture, comparing it against standard PSK and 802.1X Enterprise, and delivering actionable deployment guidance for hospitality, retail, events, and public-sector environments. It addresses the critical operational challenge of providing secure, individually-managed WiFi access across mixed-device fleets — including IoT and headless devices — without the infrastructure overhead of a full 802.1X deployment. Purple's platform is positioned as the orchestration layer that automates IPSK key lifecycle management at scale.
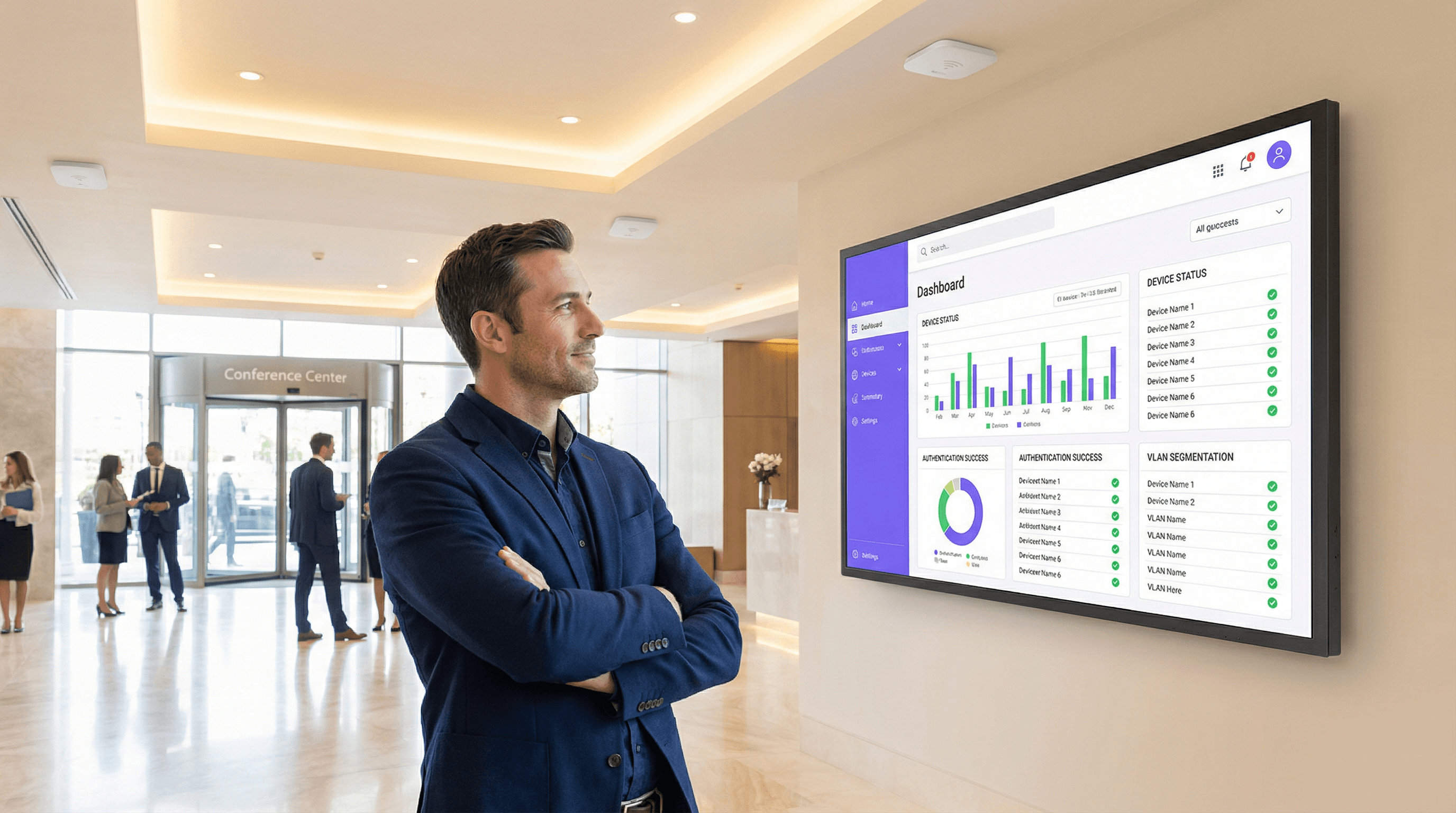
Guest WiFi vs Staff WiFi: Network Segmentation Best Practices
This guide provides an authoritative technical reference for IT managers and network architects on the critical practice of separating guest and staff WiFi through network segmentation. It covers the security risks of running a flat, unsegmented network, the technical architecture of VLAN-based isolation, and vendor-neutral implementation guidance for hospitality, retail, and public-sector venues. The guide demonstrates how proper segmentation simultaneously mitigates data breach risk, satisfies compliance mandates such as PCI DSS and GDPR, and enables guest WiFi to become a revenue-generating business asset.

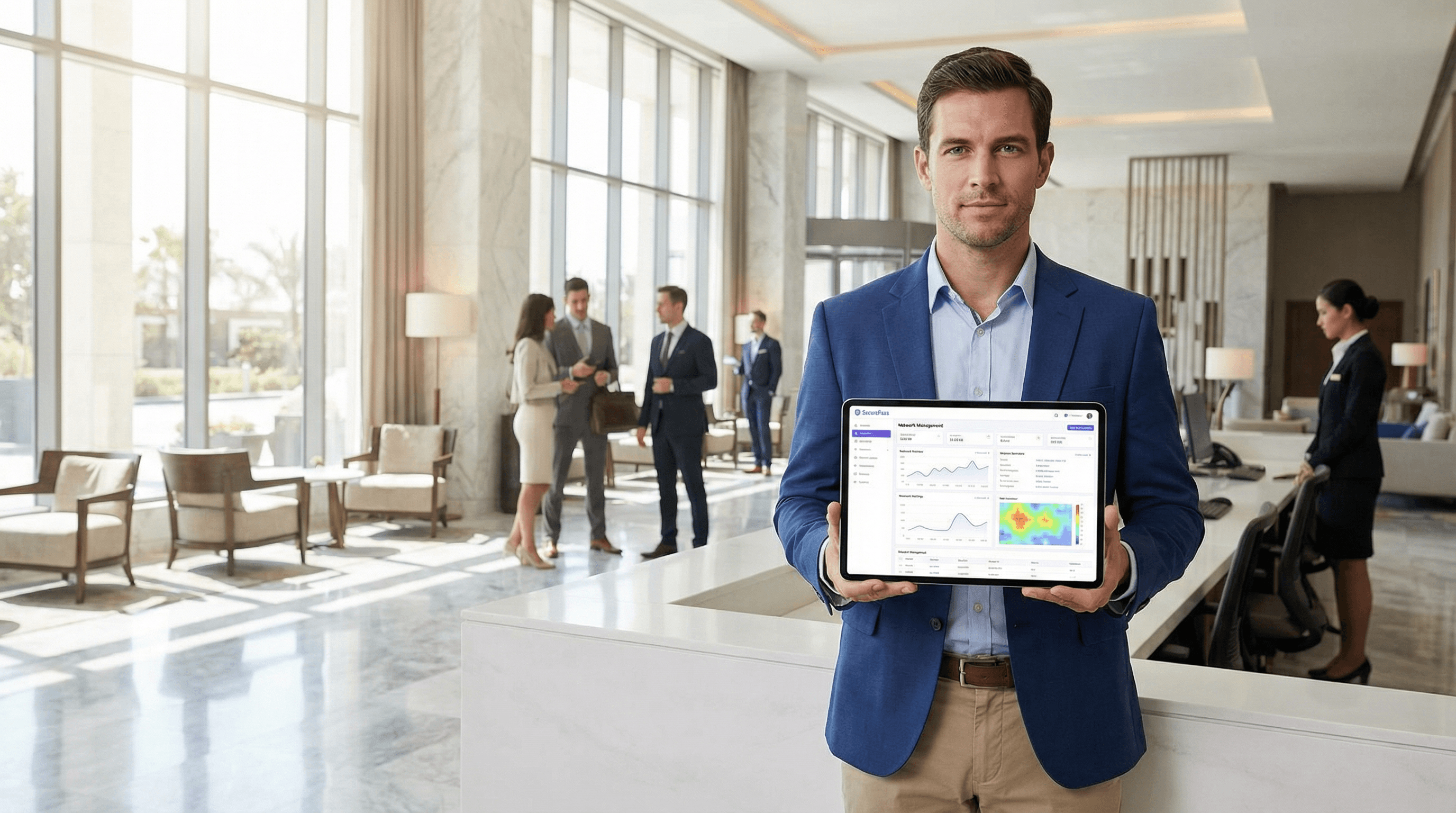
How to Set Up Purple WiFi for the First Time: A Technical Overview
This technical reference guide provides IT managers, network architects, and CTOs with a comprehensive overview of the Purple WiFi platform's initial setup process. It covers the core technical architecture, hardware integration, portal configuration, and best practices for a successful deployment in enterprise environments like hotels, retail, and stadiums. Following this guide, IT teams can confidently deploy a secure, GDPR-compliant guest WiFi solution that delivers both seamless connectivity and actionable business intelligence.



