Technical Guides
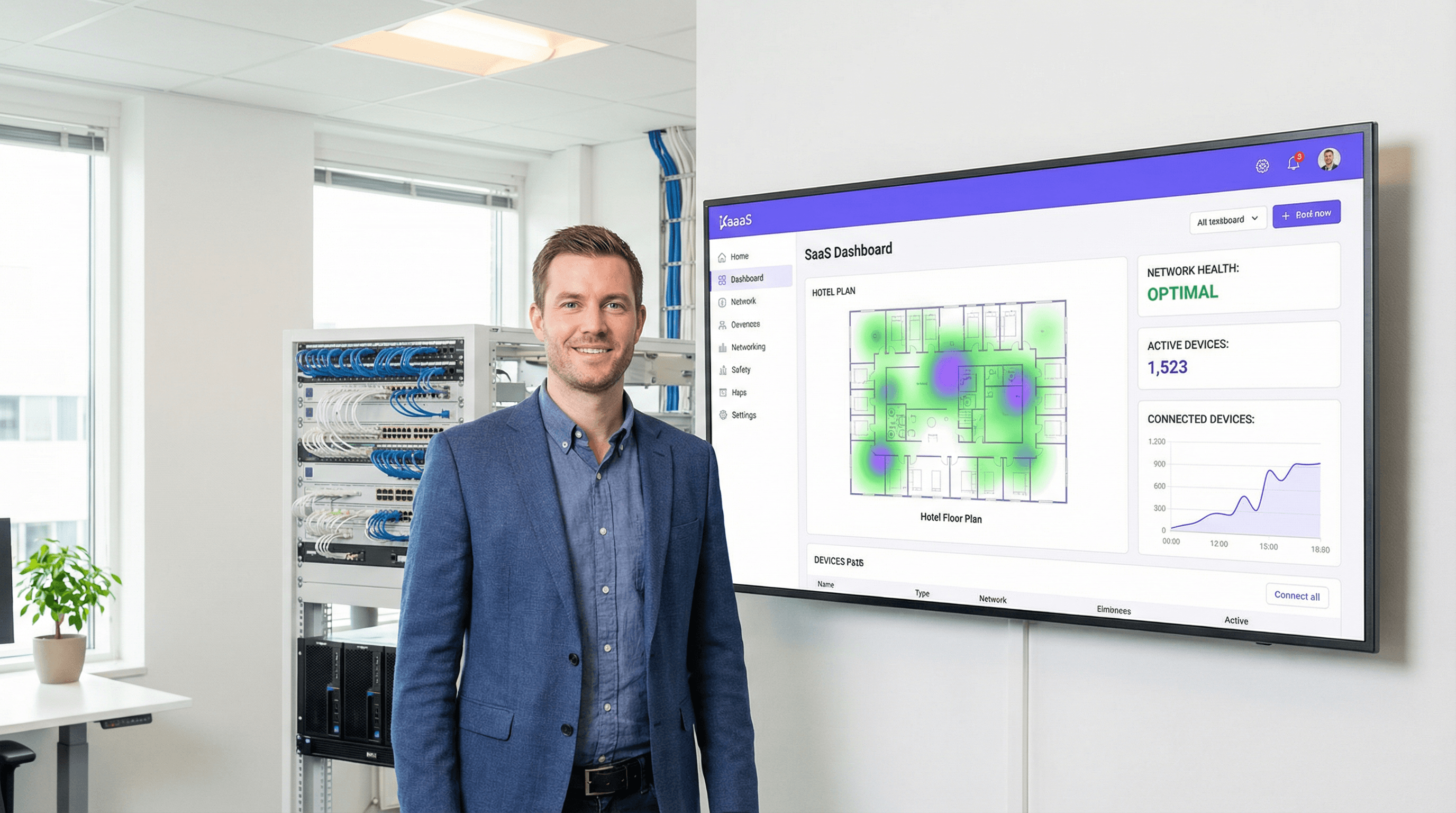
Deep, expert-led guides covering guest WiFi, analytics, captive portals, and modern venue technology. Each guide includes diagrams, worked examples, and audio podcasts.
209 guides

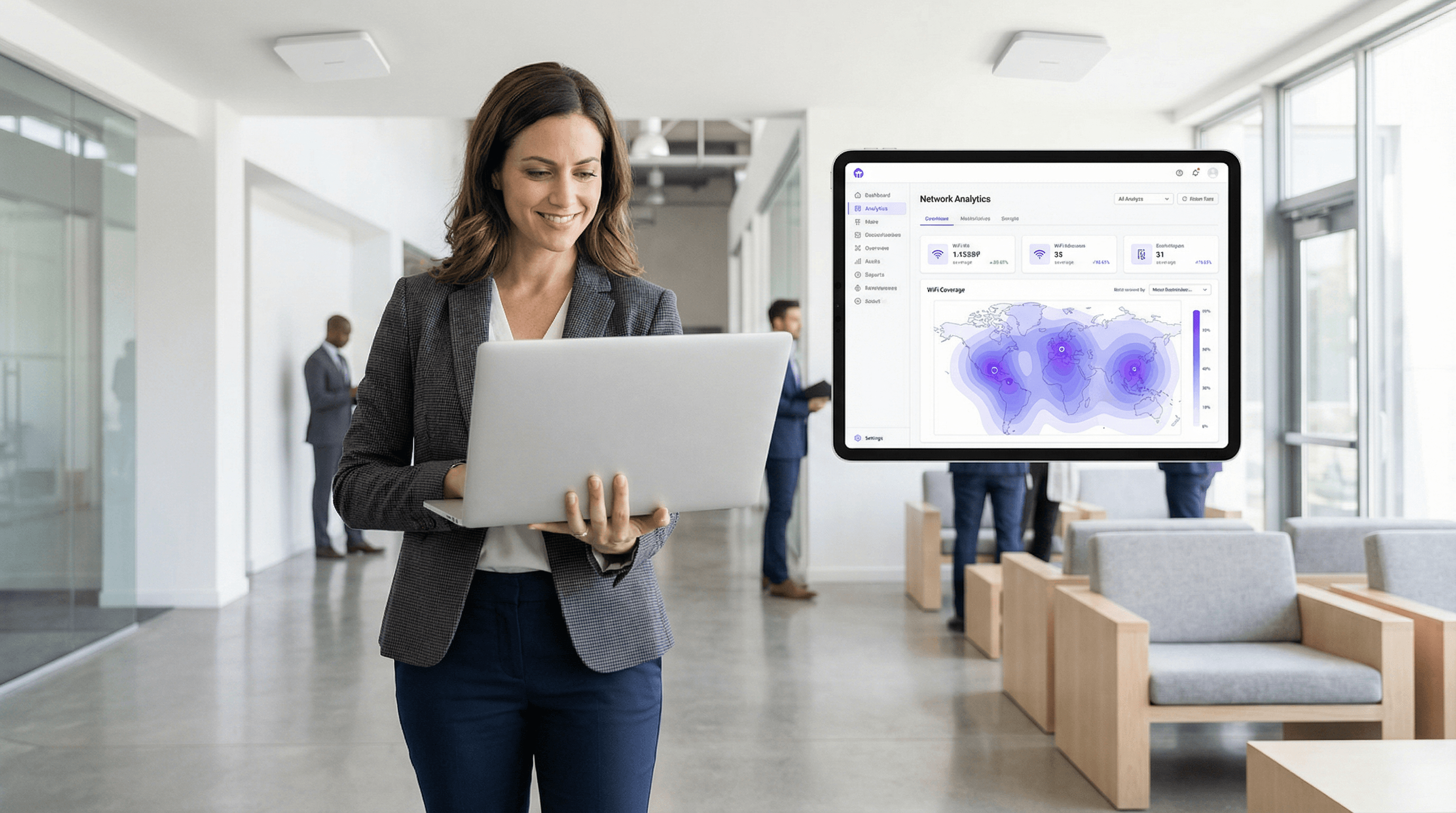
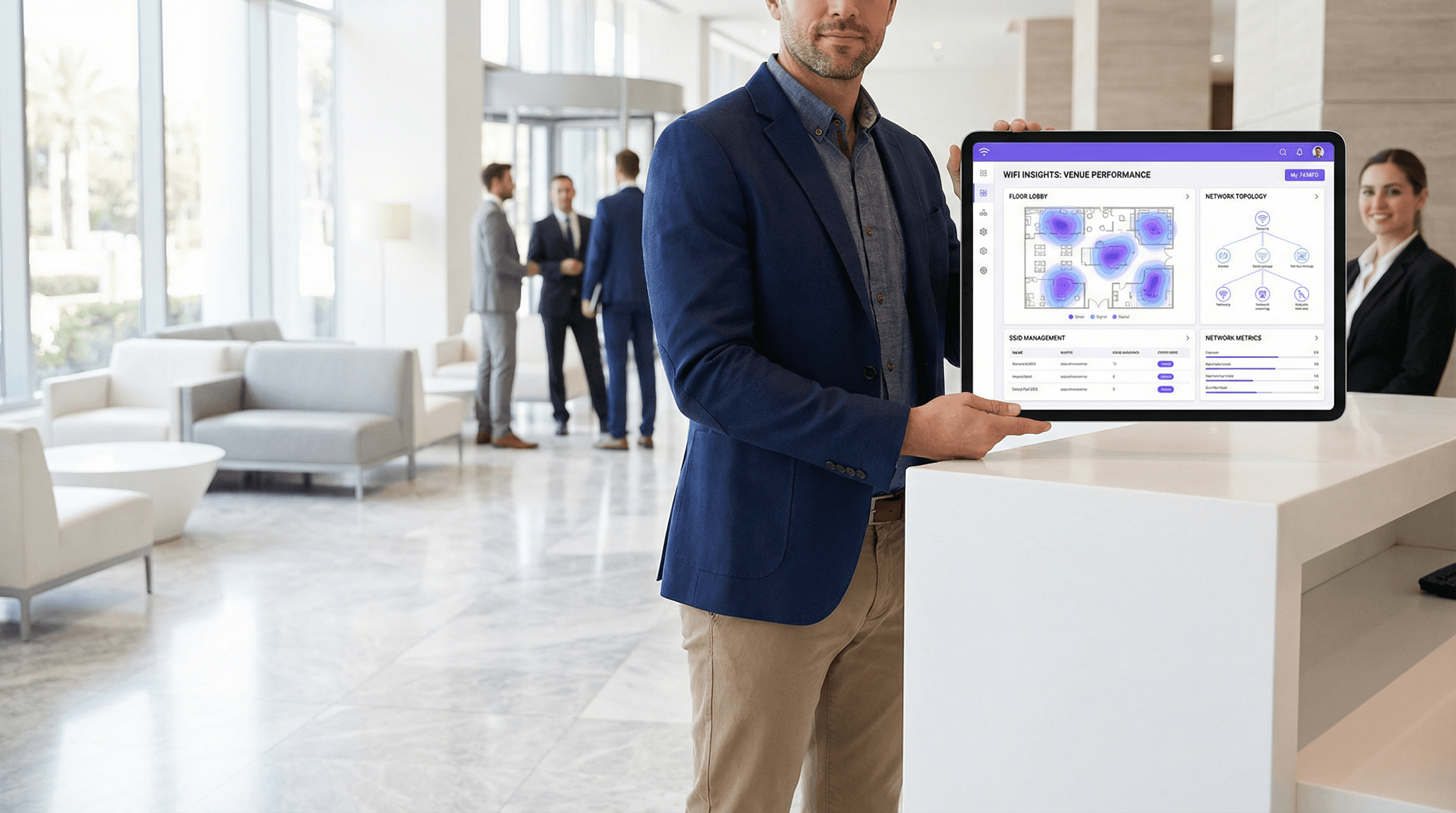
Measuring WiFi Network Performance: Key Metrics for IT Teams
A comprehensive technical reference for IT managers and network architects on the key metrics for measuring and benchmarking enterprise WiFi network performance. This guide provides actionable insights into interpreting performance data to optimize user experience and achieve business objectives in large-scale venues.
Estimote Beacons: A Comprehensive Guide to Setup, Configuration, and Use Cases
This guide provides a comprehensive technical reference for IT managers and network architects on deploying Estimote beacons. It covers setup, configuration, and advanced use cases like wayfinding, proximity marketing, and asset tracking, offering actionable guidance for achieving measurable ROI in enterprise environments.
Band Steering and Load Balancing for High-Density WiFi
This authoritative technical reference equips IT managers, network architects, and venue operations directors with the knowledge to design, configure, and optimise high-density WiFi networks using band steering and load balancing. It covers the architectural principles behind 2.4 GHz vs. 5 GHz band selection, AP load distribution strategies, and vendor-neutral configuration best practices for demanding environments such as stadiums, hotels, and conference centres. By applying these strategies, organisations can measurably improve wireless throughput, reduce user complaints, and transform their network infrastructure into a strategic business asset.

DHCP and DNS Fundamentals for WiFi Network Administrators
An authoritative technical reference for IT leaders and network administrators on the critical roles of DHCP and DNS in enterprise WiFi deployments. This guide provides practical, vendor-neutral guidance for designing, implementing, and troubleshooting robust network services in hospitality, retail, and large-venue environments.

Webhooks vs API Polling for WiFi Data: Which to Use?
This guide provides a definitive technical comparison between webhooks and API polling for retrieving WiFi intelligence data. It offers actionable guidance for IT managers, architects, and developers to help them select the optimal data integration pattern for real-time responsiveness, operational efficiency, and scalable deployments in enterprise environments.
Email Verification for WiFi Sign-In: Improving Data Quality
This guide provides IT managers, network architects, and venue operations directors with a definitive technical reference on email verification for WiFi sign-in, explaining why guest WiFi environments produce degraded email data, how Purple's Verify feature implements a layered validation architecture, and what measurable improvements operators can expect after deployment. It covers the full verification stack — from RFC 5322 syntax checking through DNS MX record validation, disposable-email blocklisting, and OTP confirmation — alongside GDPR compliance considerations and CRM integration guidance. Venue operators who act on this guidance can expect to reduce invalid email rates from an industry-average 25–35% to under 2%, materially improving marketing ROI, sender reputation, and regulatory defensibility.
Access Point Firmware Management Best Practices
This guide provides an authoritative reference on Access Point (AP) firmware management for enterprise environments. It details why a strategic approach to firmware is critical for security, performance, and compliance, offering actionable best practices for IT leaders to implement robust, scalable update processes in venues like hotels, retail chains, and stadiums.

Juniper Mist Integration with Purple WiFi
This guide provides a comprehensive technical reference for integrating Juniper Mist's AI-driven wireless platform with Purple's enterprise guest WiFi and analytics solution. It covers the full integration architecture — from the Mist external captive portal and REST API authorisation flow through to PurpleConnex Passpoint and RadSec configuration for seamless repeat-visitor connectivity. Venue operators and IT teams will find actionable deployment guidance, real-world implementation scenarios, and a clear framework for measuring the business impact of a Mist-Purple deployment.
WiFi Roaming and Handoff: 802.11r and 802.11k Explained
This guide provides a senior-level technical deep-dive into WiFi roaming protocols — specifically 802.11r (Fast BSS Transition), 802.11k (Neighbor Reports), and 802.11v (BSS Transition Management) — and their combined role in delivering seamless connectivity across enterprise venues. It equips IT managers, network architects, and venue operations directors with the architectural understanding, implementation steps, and business-impact metrics needed to deploy and validate fast roaming in hospitality, retail, events, and public-sector environments. The guide also addresses the critical interaction between roaming and captive portals, a common deployment failure point in guest WiFi networks.
SMS Authentication for WiFi: How It Works and When to Use It
A technical reference for IT managers and venue operators on implementing SMS-based WiFi authentication. This guide details the technical workflow, compares it against social login, and provides actionable best practices for deployment in enterprise environments like hotels, retail, and stadiums.
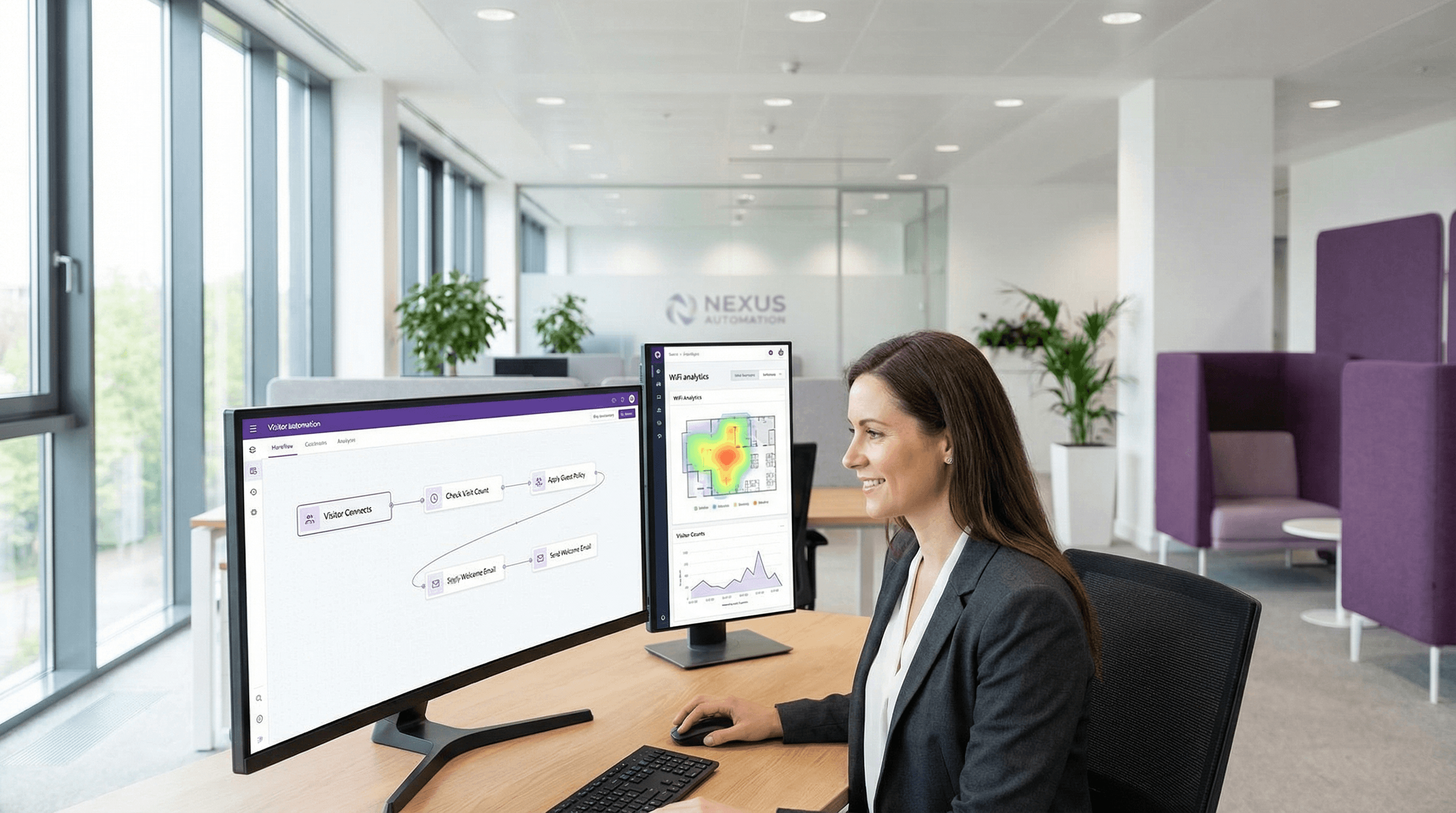
LogicFlow: Automating WiFi Events and Triggers
This authoritative technical reference guide covers Purple's LogicFlow, an enterprise-grade WiFi event automation engine that enables IT managers and network architects to build intelligent, trigger-based workflows across hospitality, retail, stadium, and public-sector venues. It details the platform's Event-Decision-Action architecture, explores the full range of available triggers, and provides concrete implementation guidance with real-world case studies from hotel and retail deployments. For venue operators and IT teams, this guide demonstrates how to transform passive WiFi infrastructure into a proactive, revenue-generating, and operationally efficient platform.
Port Forwarding for WiFi Controllers: A Configuration Guide
This guide provides a technical reference for network architects and IT managers on configuring port forwarding for on-premise WiFi controllers. It covers when port forwarding is necessary, which ports are required for major vendors, and how to mitigate the associated security risks to ensure a secure and scalable deployment.
SSID Management Best Practices for Multi-Venue Deployments
This guide provides a technical reference for IT leaders on managing SSIDs in multi-venue deployments. It debunks common myths about SSID count impacting performance and offers actionable best practices for balancing security, user experience, and network manageability across hospitality, retail, and large public venues.
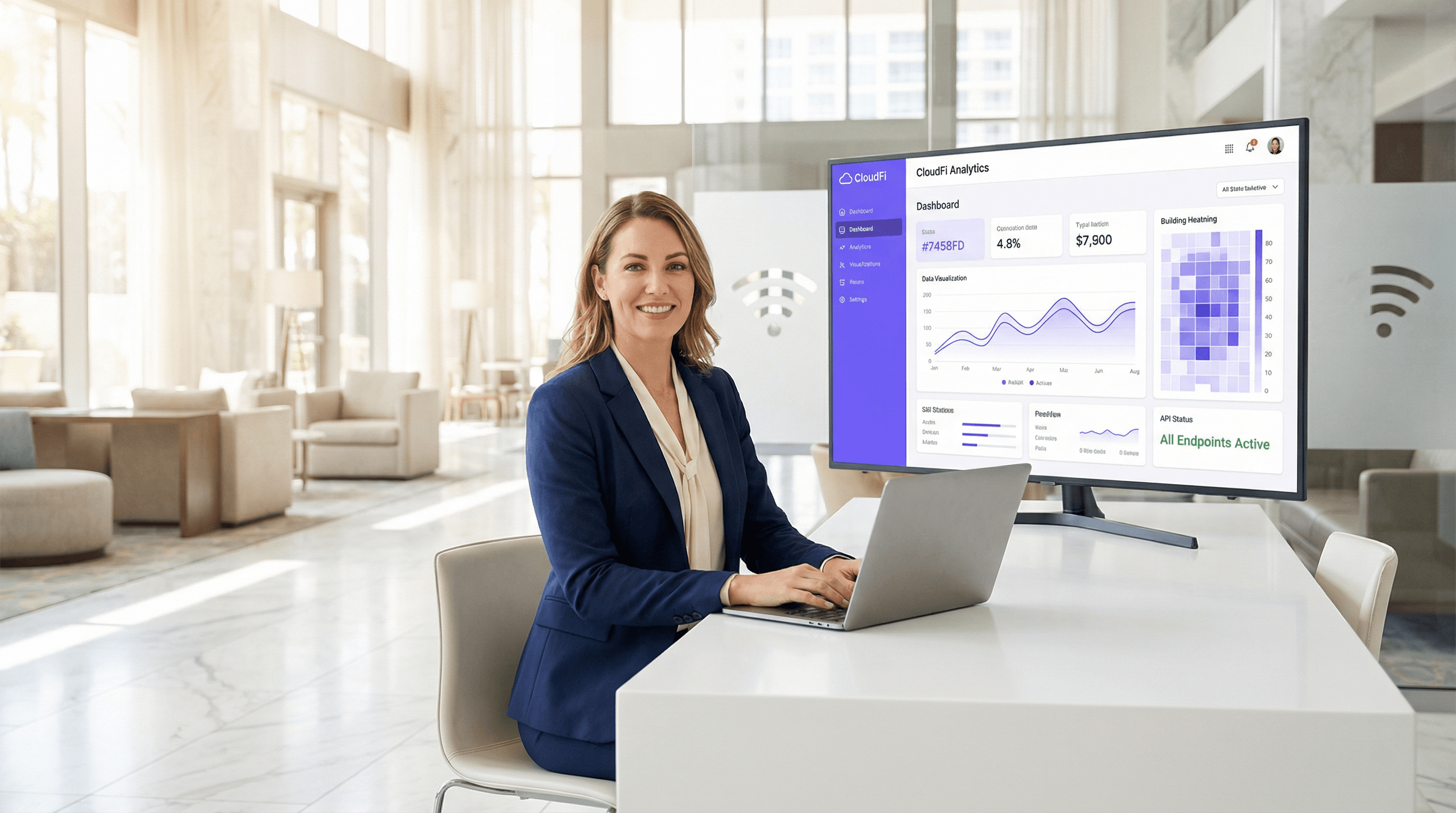
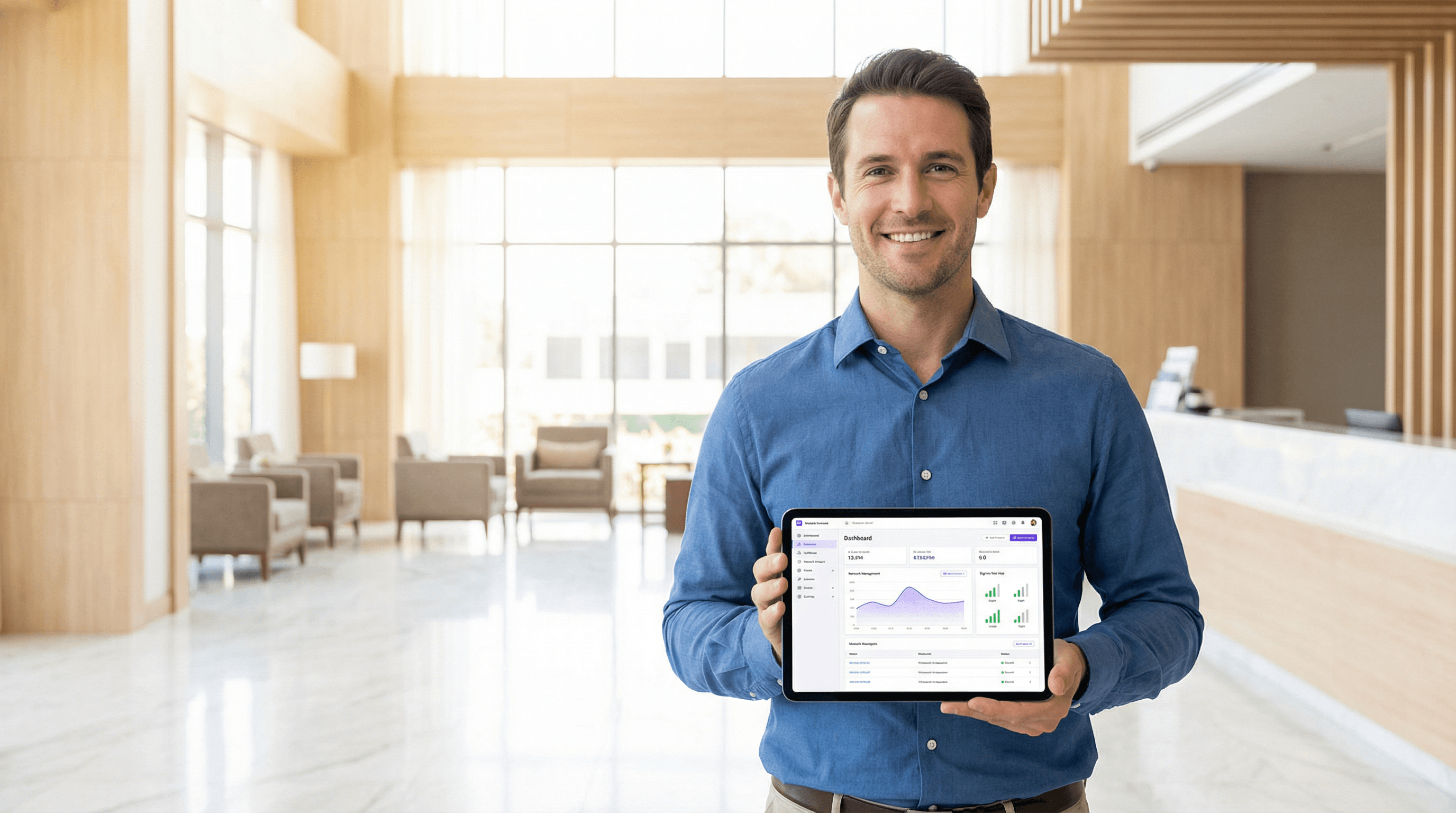
Purple Portal API: What You Can Do With It
A technical reference for IT managers and network architects on leveraging the Purple Portal API. This guide details available endpoints, authentication, and real-world use cases for integrating guest WiFi data with enterprise systems to enhance business intelligence and operational efficiency. It covers both REST API and Webhook integration patterns, with concrete case studies from hospitality, retail, and events sectors.
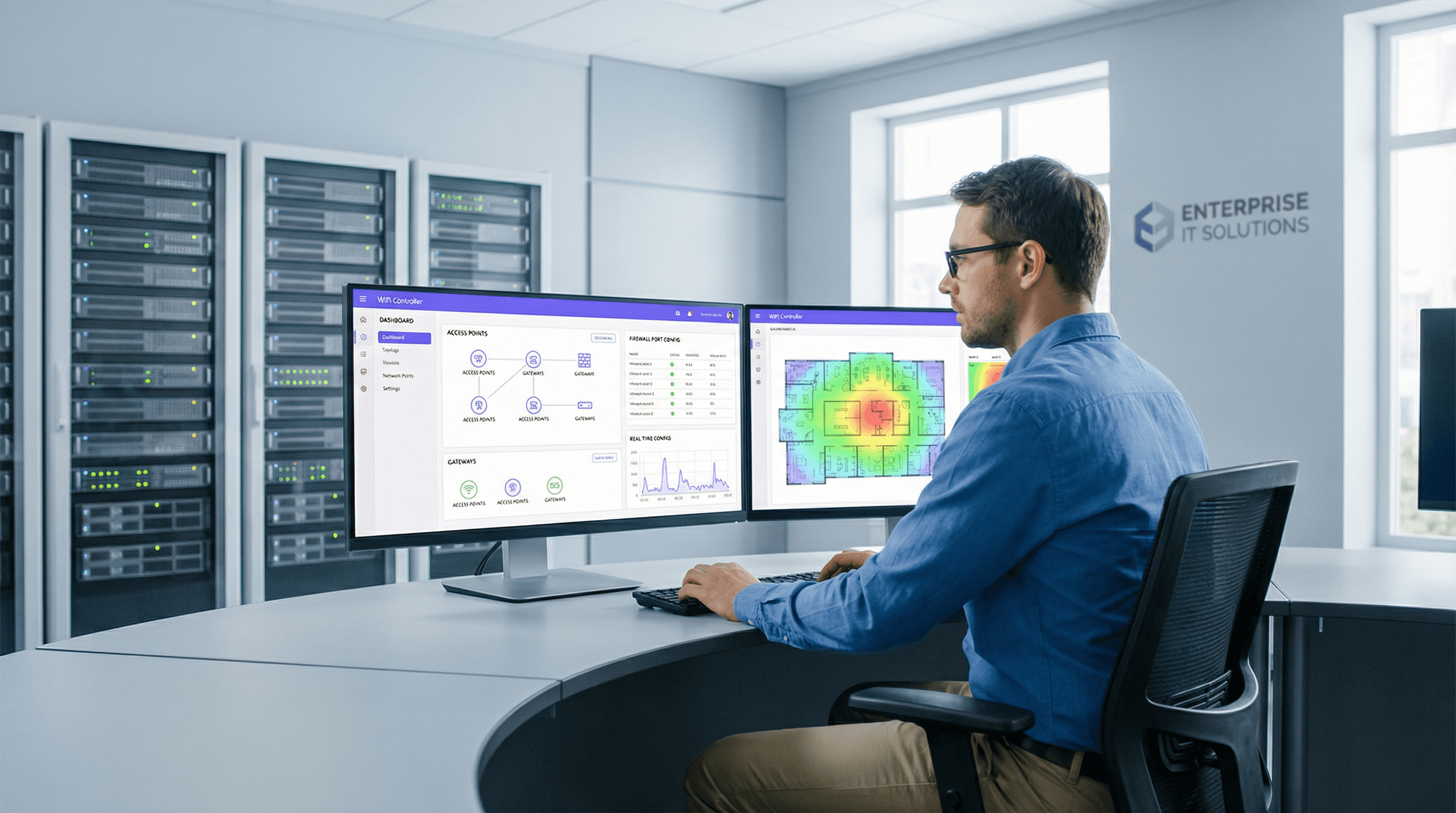
What is a WiFi Controller and Do You Need One?
This authoritative guide provides IT leaders and network architects with a practical overview of WiFi controllers, detailing their function, comparing on-premises and cloud-based models, and explaining how they integrate with WiFi intelligence platforms like Purple. It offers actionable insights for deploying scalable, secure, and high-performance wireless networks in enterprise environments such as hospitality, retail, and large venues. By the end, readers will have a clear framework for choosing the right controller architecture and understanding where a platform like Purple adds transformative business value.
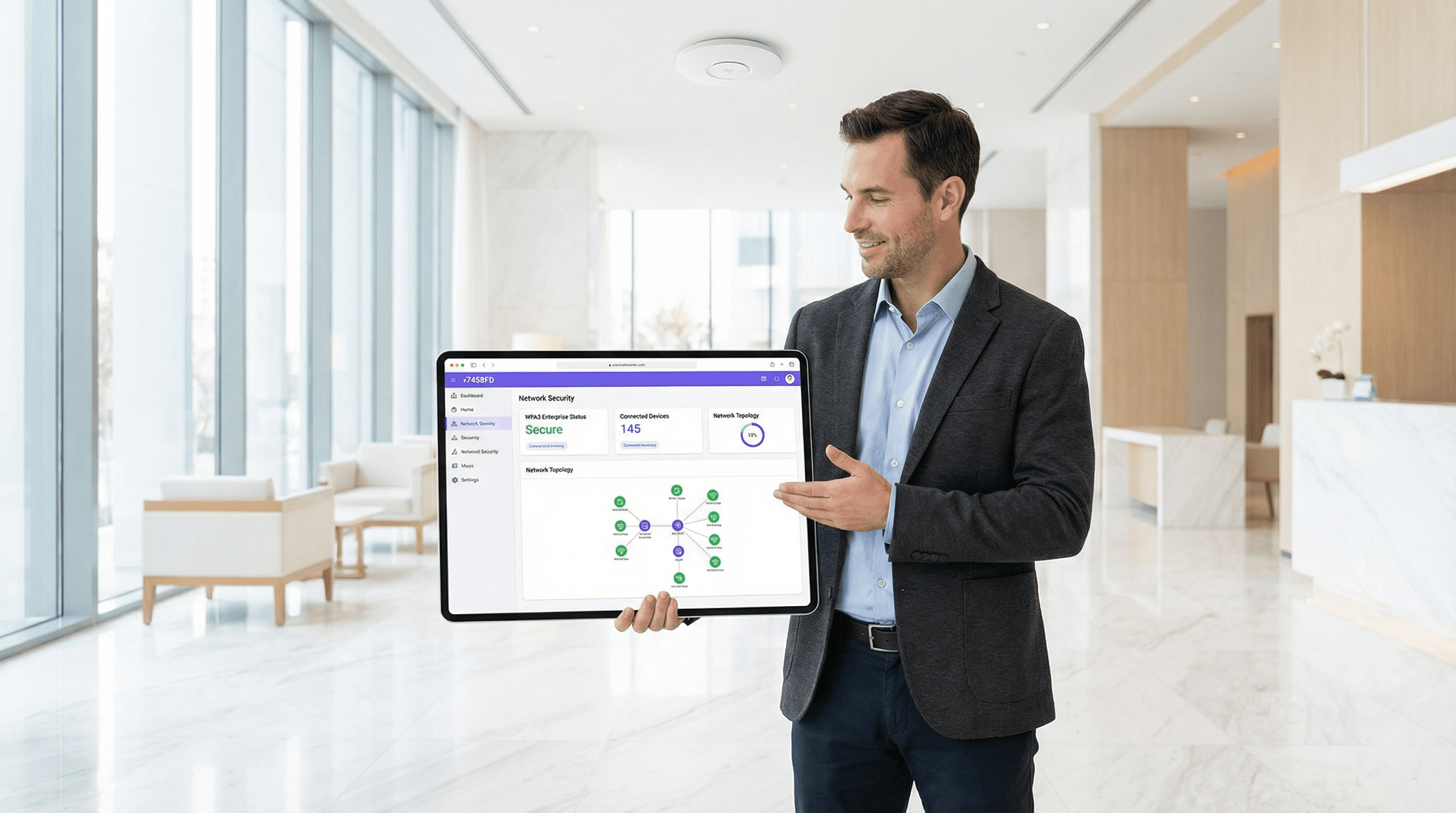
WPA2 vs WPA3: What's the Difference and Should You Upgrade?
This guide provides IT managers, network architects, and venue operations directors with a definitive, actionable comparison of WPA2 and WPA3 WiFi security protocols. It explains the critical technical differences — including SAE authentication, Perfect Forward Secrecy, and Enhanced Open — and outlines a practical, phased migration strategy using WPA3 Transition Mode. The guide is essential for any organisation operating guest or staff WiFi in hospitality, retail, events, or public-sector environments who needs to understand the upgrade case, manage device compatibility, and align their wireless security posture with modern compliance requirements.

LAN vs WAN: Understanding the Difference in WiFi Deployments
A technical reference for IT leaders and venue operators on the critical differences between LAN and WAN in enterprise WiFi deployments. This guide provides actionable architectural insights, implementation best practices, and clarifies how understanding this distinction drives ROI for guest WiFi and operational intelligence.

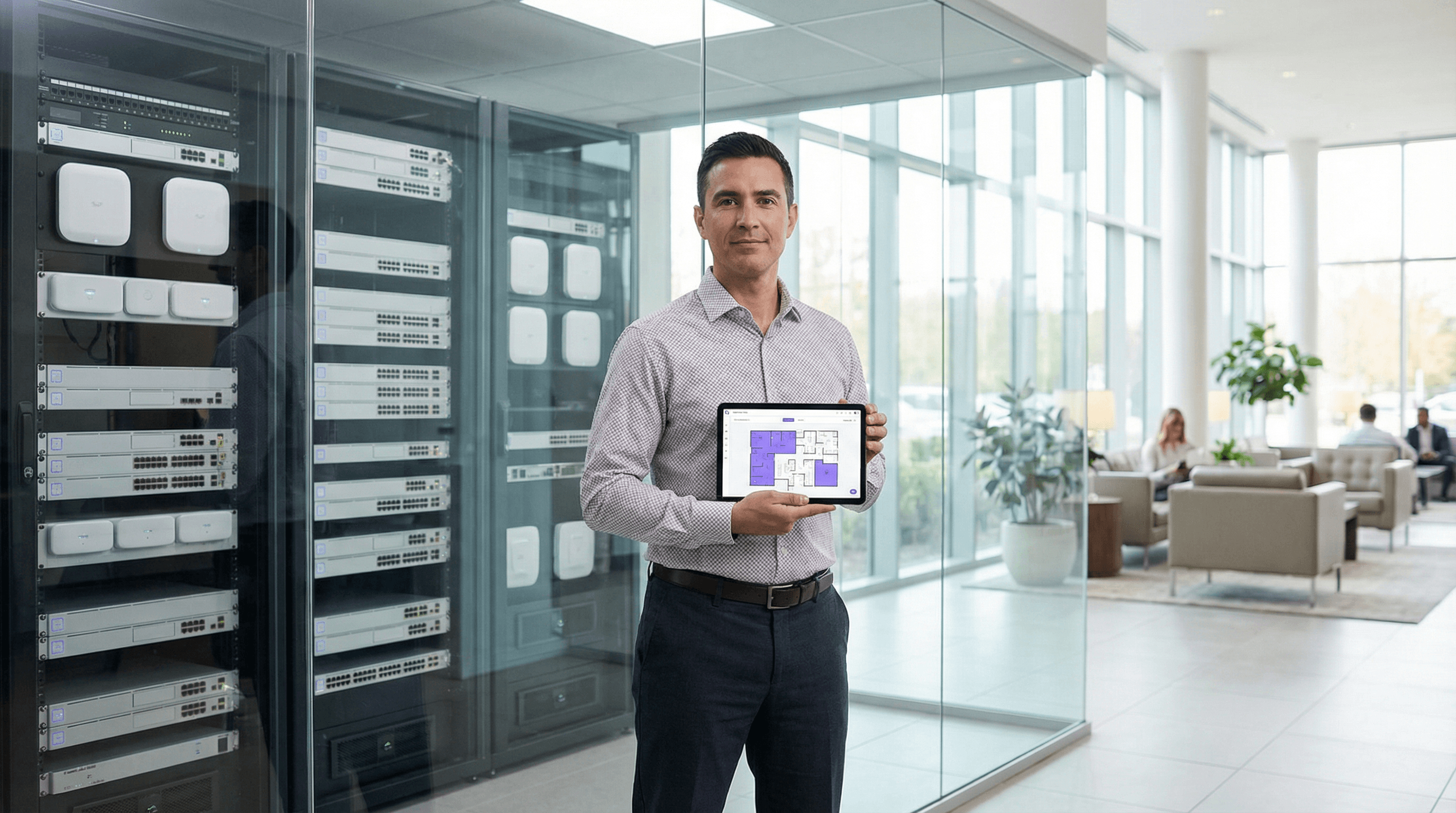
Access Point Placement and Coverage Planning for Venues
A technical reference for IT leaders on designing high-performance WiFi networks in complex venues. This guide provides actionable best practices for access point placement, coverage planning, and capacity calculation to improve guest experience and operational ROI.

Captive Portal Architecture: A Technical Deep Dive
This technical reference guide provides a comprehensive architectural breakdown of captive portal systems for enterprise guest WiFi deployments. It examines how network-level redirection, RADIUS authentication, access node policy enforcement, and walled garden configuration interact to create a secure and scalable access control framework. Designed for IT managers, network architects, and venue operations directors, this guide delivers actionable implementation guidance, real-world case studies, and compliance-aligned best practices that directly support deployment decisions in hospitality, retail, events, and public-sector environments.
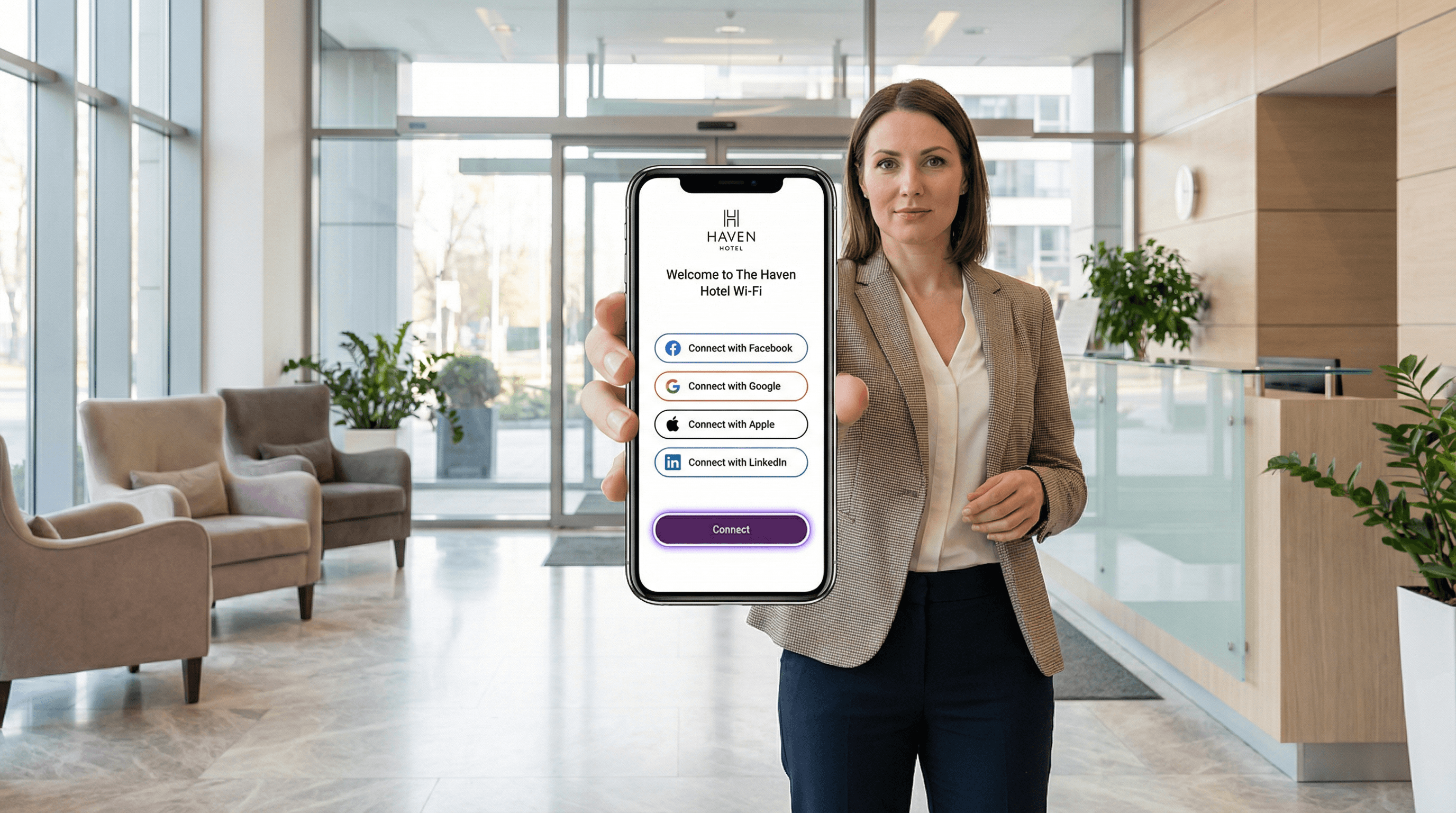
Social Login for Guest WiFi: Facebook, Google, Apple and LinkedIn
This guide provides a comprehensive technical reference for IT managers, network architects, and venue operators deploying social login on guest WiFi networks. It covers the OAuth 2.0 Authorization Code Flow underpinning Facebook, Google, Apple, and LinkedIn authentication, the specific data each platform provides, and the critical iOS compatibility constraints affecting Google OAuth in captive portal environments. Compliance obligations under UK GDPR, platform selection frameworks, and real-world deployment case studies from hospitality and retail are included to support implementation decisions this quarter.
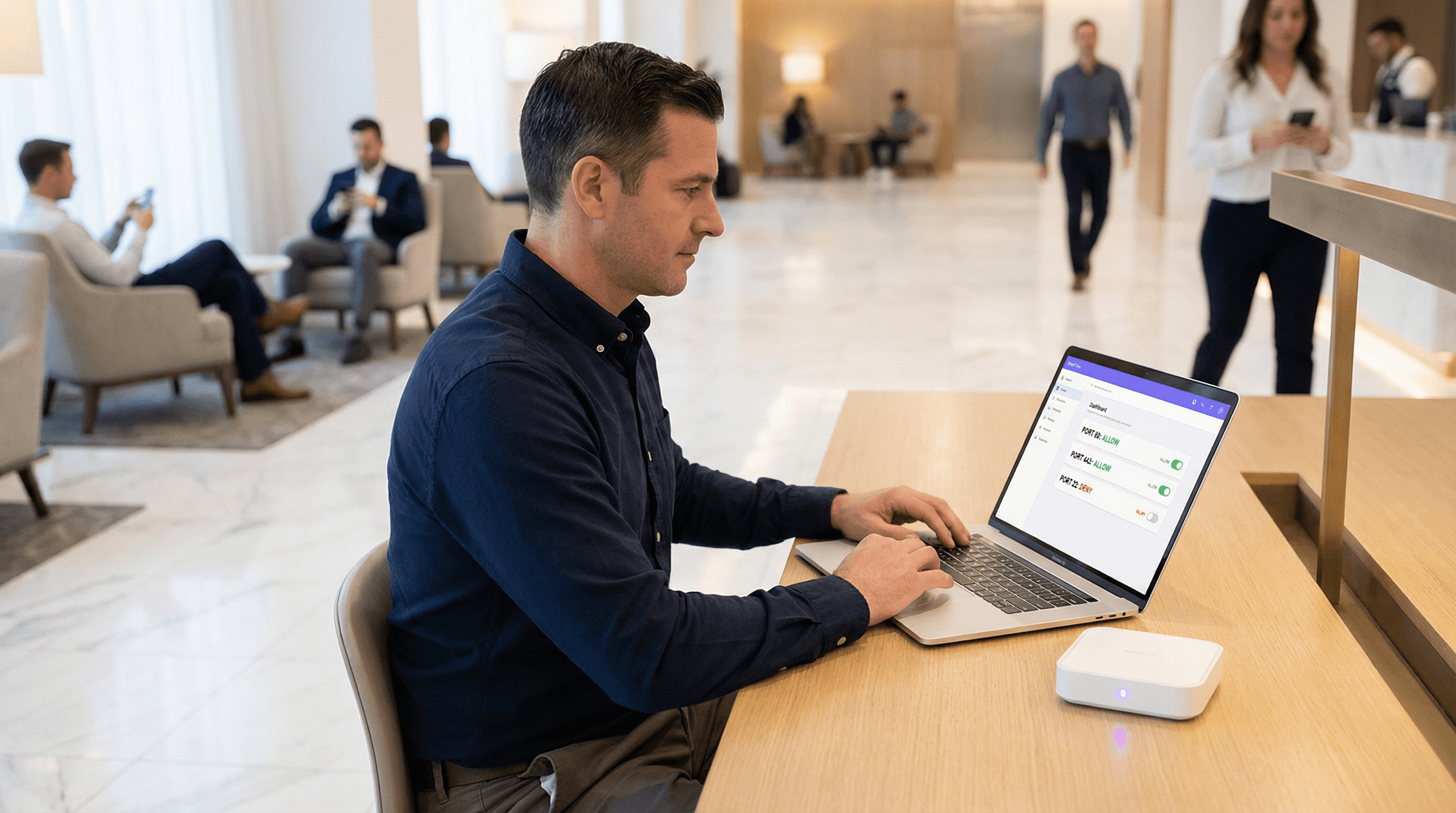
Firewall Rules for Guest WiFi Networks
This guide provides IT managers and network architects with an authoritative reference for configuring firewall rules for guest WiFi networks, specifically in support of a Purple deployment. It offers actionable, vendor-neutral guidance on network segmentation, port configuration, and security best practices to ensure both seamless guest access and robust protection of corporate assets.
VLAN Configuration for WiFi Networks
This guide provides a technical deep-dive into VLAN configuration for enterprise WiFi networks, offering actionable guidance for IT leaders and network architects. It covers VLAN fundamentals, SSID-to-VLAN mapping, implementation best practices, and the business impact of proper network segmentation for security, performance, and compliance in venues like hotels, retail chains, and stadiums.
Splash Page Design Best Practices for Guest WiFi
This guide provides IT managers, network architects, and venue operations directors with a definitive technical reference for designing and deploying high-performance guest WiFi splash pages. It covers the four core pillars of effective captive portal design — brand identity, user experience, data capture, and legal compliance — and translates them into actionable deployment guidance. By following these best practices, organisations can expect measurable improvements in guest connection rates, marketing database growth, and demonstrable ROI from their guest WiFi infrastructure.
Walled Garden Configuration for Guest WiFi
This guide provides a comprehensive, vendor-neutral technical reference for configuring walled gardens in enterprise guest WiFi deployments. It covers the architecture of pre-authentication access, the critical role of dynamic DNS resolution, social login domain whitelisting, OS captive portal probe requirements, and compliance considerations under PCI DSS and GDPR. Aimed at IT managers, network architects, and venue operations directors, it delivers actionable implementation guidance with real-world case studies from hospitality, retail, and events environments.



