Event WiFi: Planning and Deploying Temporary Wireless Networks
This guide provides IT managers, network architects, and venue operations directors with a complete technical reference for planning and deploying temporary WiFi networks at events of any scale. It covers capacity planning, hardware selection, VLAN architecture, captive portal integration, GDPR compliance, and post-event analytics — with concrete case studies from hospitality and large-scale conference environments. For event producers and AV companies, it maps the full lifecycle of an event WiFi engagement from initial site survey through to teardown and reporting.
🎧 Listen to this Guide
View Transcript
- Executive Summary
- Technical Deep-Dive
- Why Event WiFi Is Different
- Capacity Planning: The Numbers That Matter
- Backhaul: The Non-Negotiable Foundation
- Network Architecture and VLAN Design
- Radio Frequency Planning
- Captive Portal Architecture and GDPR Compliance
- Implementation Guide
- Phase 1: Site Survey and Capacity Modelling (8 Weeks Before Event)
- Phase 2: Hardware Procurement and Backhaul Ordering (6–8 Weeks Before Event)
- Phase 3: Pre-Event Configuration and Testing (1–2 Weeks Before Event)
- Phase 4: On-Site Deployment (Day Before Event)
- Phase 5: On-Site Management and Monitoring
- Best Practices
- Troubleshooting and Risk Mitigation
- DHCP Pool Exhaustion
- Authentication Server Overload
- Co-Channel Interference
- Captive Portal Redirect Failures
- Uplink Failure
- ROI and Business Impact

Executive Summary
Event WiFi is a distinct engineering discipline. Unlike permanent enterprise deployments, temporary wireless networks must absorb extreme client density within compressed timeframes, operate on borrowed or hired infrastructure, and meet compliance obligations — all while delivering a seamless user experience that reflects directly on the event brand. A failed network at a 3,000-person conference is not an inconvenience; it is a reputational and commercial incident.
This guide addresses the full deployment lifecycle: capacity modelling, hardware hire, backhaul provisioning, VLAN architecture, captive portal design, and on-site management. It is written for the IT professional who needs to make procurement and architecture decisions this quarter, not a theoretical overview of wireless standards. Where Purple's Guest WiFi and WiFi Analytics platform adds specific value — particularly around captive portal management, GDPR-compliant data capture, and post-event reporting — those integration points are called out explicitly.
Technical Deep-Dive
Why Event WiFi Is Different
The fundamental challenge of event WiFi is density combined with simultaneity. In a standard office deployment, you might have 100 devices spread across 1,000 square metres, with staggered connection times throughout the working day. At a conference keynote, you may have 2,000 devices attempting to associate within a five-minute window as attendees file into a hall. The RF environment, the DHCP infrastructure, and the authentication backend all need to be engineered for that peak load — not the average.
Three variables drive every architectural decision in an event deployment: client count, throughput requirement per user, and event duration. Get these wrong at the planning stage and no amount of on-site troubleshooting will recover the situation.
Capacity Planning: The Numbers That Matter
The industry baseline for high-density WiFi is one access point per 25–50 concurrent users, but this figure requires significant qualification. The ratio depends on the AP's radio capabilities, the expected mix of 2.4 GHz and 5 GHz clients, and whether the event involves heavy media consumption (live streaming, video calls) or lighter browsing and messaging traffic.
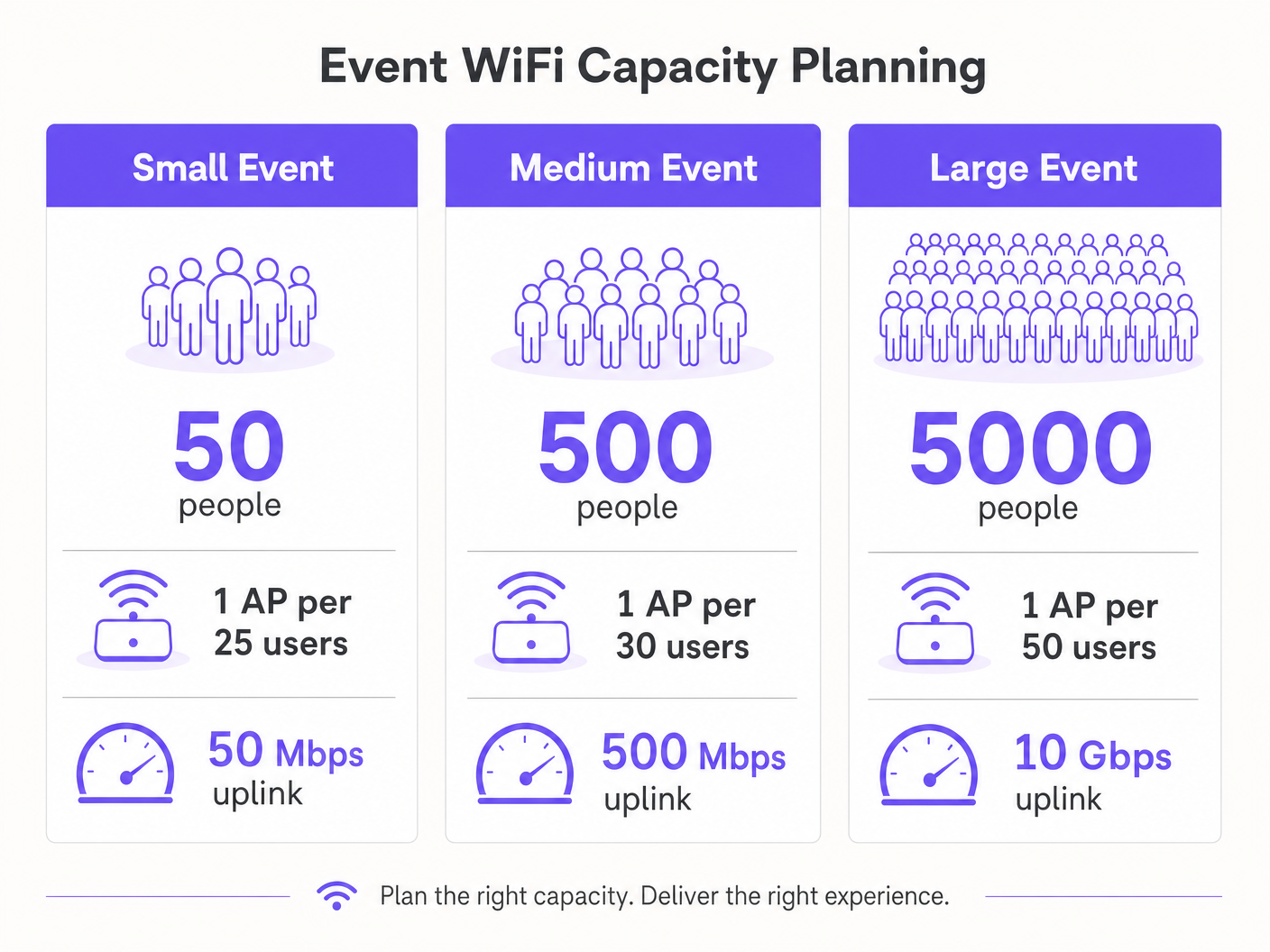
For throughput planning, a conservative estimate of 1–2 Mbps per active user is appropriate for general conference or exhibition use. For events with live streaming or broadcast-quality video requirements — such as product launches or press events — budget 5–10 Mbps per active user on the production VLAN. Your uplink must be sized to accommodate the aggregate of all VLANs simultaneously, with at least 20% headroom.
| Event Scale | Attendees | Recommended APs | Minimum Uplink | DHCP Scope |
|---|---|---|---|---|
| Small | Up to 100 | 4–6 | 50 Mbps | /24 |
| Medium | 100–500 | 15–25 | 200–500 Mbps | /23 |
| Large | 500–2,000 | 50–100 | 1–2 Gbps | /21 |
| Enterprise | 2,000+ | 100+ | 5–10 Gbps | /20 or larger |
Backhaul: The Non-Negotiable Foundation
No amount of well-designed wireless infrastructure compensates for an inadequate backhaul. For events above 200 attendees, a dedicated leased line is the only appropriate uplink solution. A leased line provides a synchronous, uncontended connection with a guaranteed SLA — typically 99.95% uptime — which is fundamentally different from the shared, asymmetric broadband that most venues have installed for their own operations.
Leased line provisioning typically requires a four-to-six-week lead time. This is the single most common planning failure in event WiFi deployments: teams that begin network design two weeks before an event and discover they cannot get a dedicated circuit in time. For events where a leased line is genuinely impractical — outdoor festivals, temporary structures — a bonded 4G/5G solution using multiple SIM cards across different carriers provides a viable alternative, though with lower guaranteed throughput and higher latency.
Network Architecture and VLAN Design
Strict network segmentation is both a performance and a compliance requirement. The recommended minimum architecture for any event deployment uses three VLANs:
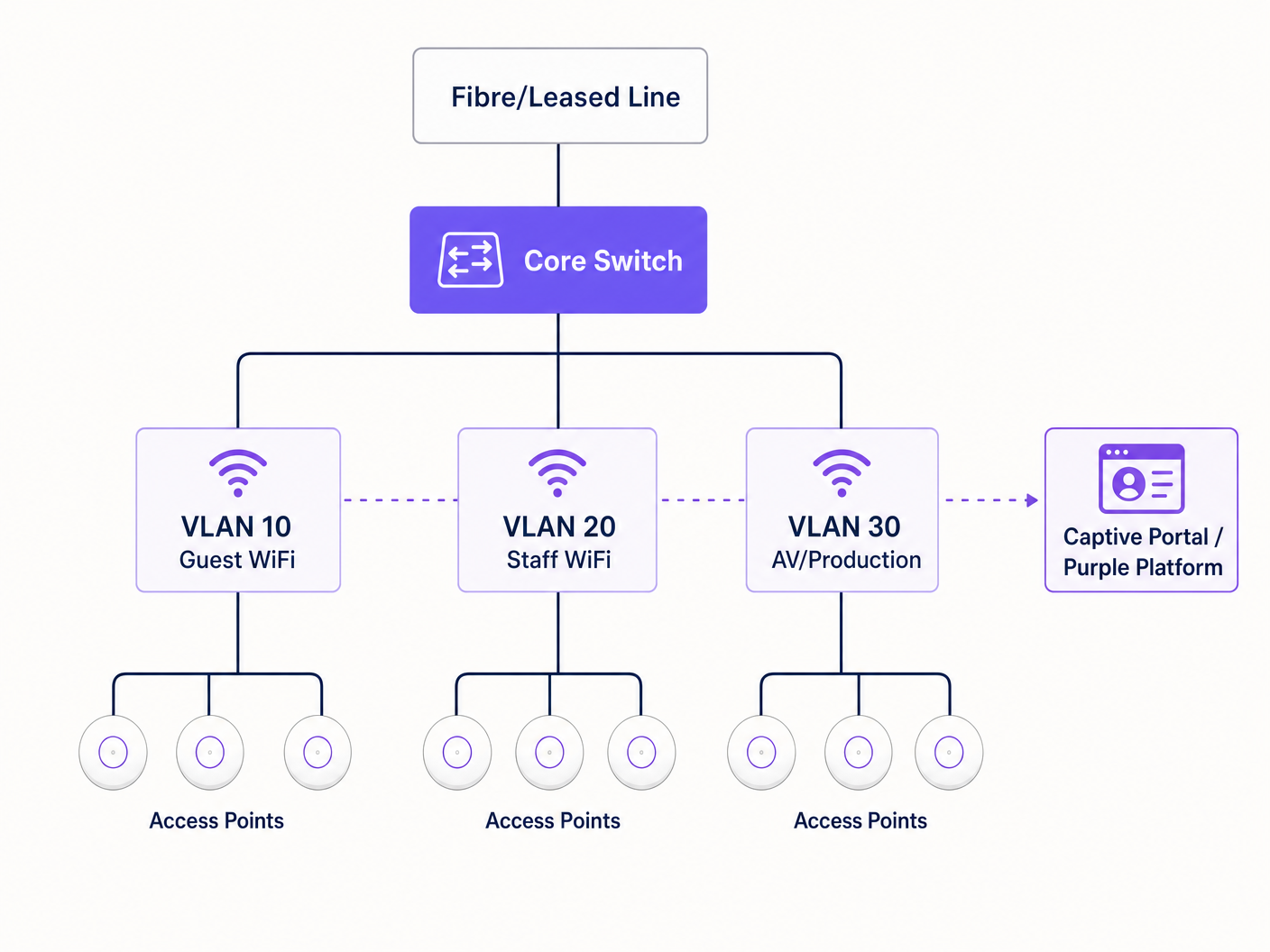
VLAN 10 — Guest WiFi: All public-facing attendee traffic. This VLAN connects to the captive portal for authentication and data capture. Client isolation must be enabled to prevent lateral movement between devices. DNS filtering should be applied to block malicious domains — see Purple's guide on protecting your network with strong DNS and security for implementation detail.
VLAN 20 — Staff and Point of Sale: Operational traffic for event staff, ticketing systems, and card payment terminals. If card payments are processed on this VLAN, PCI DSS scope applies and the VLAN must be fully isolated from the guest network with no routing between them.
VLAN 30 — AV and Production: Dedicated to broadcast equipment, presentation systems, and production crew. This VLAN typically requires the highest guaranteed throughput and lowest latency, and should be provisioned with QoS policies that prioritise it over guest traffic.
For larger events, additional VLANs for exhibitors, press, and security systems are common. Each SSID should map to a single VLAN, and inter-VLAN routing should be disabled at the core switch unless explicitly required.
Radio Frequency Planning
In high-density environments, the default behaviour of most enterprise APs — automatic channel selection and maximum transmit power — is actively harmful. Co-channel interference between adjacent APs on the same channel degrades performance far more than a slight reduction in coverage area.
The correct approach is to manually assign channels and reduce transmit power. On the 5 GHz band, use the non-overlapping channels available across the UNII-1 (36, 40, 44, 48), UNII-2 (52–64), and UNII-3 (149–165) bands. Reduce AP transmit power to 8–12 dBm in dense deployments. This creates smaller, cleaner cells with less interference, which improves aggregate throughput across the venue.
Band steering should be enabled on all APs to push 5 GHz-capable clients — which is the vast majority of modern smartphones and laptops — away from the congested 2.4 GHz spectrum. Reserve 2.4 GHz for legacy IoT devices and accessibility equipment that cannot connect to 5 GHz.
For outdoor events, the RF environment is fundamentally different. Without walls and ceilings to contain signal, coverage cells are larger and interference from adjacent deployments or consumer hotspots is harder to control. Directional sector antennas are preferable to omnidirectional APs in outdoor settings, as they allow you to focus coverage on specific zones — the main stage area, the food court, the registration queue — rather than broadcasting indiscriminately. All outdoor hardware must carry at minimum an IP55 ingress protection rating; IP67 is preferable for festival or exposed environments.
Captive Portal Architecture and GDPR Compliance
The captive portal is the user's first interaction with your event network and your primary mechanism for both compliance and data capture. A poorly designed portal that times out, fails to redirect correctly on iOS, or presents an unclear consent workflow will generate a disproportionate volume of support requests and undermine attendee confidence in the network.
From a GDPR perspective, any collection of personal data — email addresses, social login tokens, or device identifiers — requires a lawful basis, a clear privacy notice, and explicit consent for any marketing use. The consent must be granular: consent to use the WiFi is not the same as consent to receive marketing communications. Purple's Guest WiFi platform handles this consent workflow natively, presenting compliant opt-in flows and storing consent records with timestamps and IP addresses as required by Article 7 of GDPR.
The technical architecture of the captive portal matters for performance. A cloud-hosted portal that redirects authentication requests to an external server introduces latency into the login flow. At peak load — when hundreds of users are authenticating simultaneously — this latency can cause timeouts and failed logins. Purple's platform is architected for exactly this use case, with auto-scaling infrastructure that handles burst authentication loads without degradation.
Implementation Guide
Phase 1: Site Survey and Capacity Modelling (8 Weeks Before Event)
Begin with a physical site survey. Walk every area where attendees will be present and document ceiling heights, wall materials, structural obstructions, and existing infrastructure (conduit runs, power outlets, data ports). Use a WiFi survey tool — Ekahau Site Survey or iBwave are the industry standards — to model predicted coverage and identify dead zones before hardware is ordered.
At the same time, confirm the venue's existing network infrastructure. Identify available data ports, the location of the main distribution frame, and the capacity of any existing switches. Determine whether the venue's existing cabling can support PoE+ (802.3at) for the APs you intend to deploy, or whether you need to bring your own PoE switches and cabling.
Finalise your capacity model based on the expected attendee count, the event programme (a keynote session creates a very different load profile to a networking reception), and the throughput requirements of any production systems.
Phase 2: Hardware Procurement and Backhaul Ordering (6–8 Weeks Before Event)
Order your leased line immediately after the site survey. The four-to-six-week provisioning window is the critical path for the entire deployment. If the event venue already has a leased line, negotiate dedicated bandwidth allocation with the venue's IT team — do not assume that existing infrastructure will be made available.
For hardware, the choice between purchasing and hiring depends on the frequency of your events. For organisations that deploy event WiFi more than four times per year, ownership of a portable kit — enterprise APs, a managed PoE switch, a rack-mount router, and cabling — is more cost-effective than repeated hire. For one-off events, specialist event WiFi hire companies provide pre-configured hardware with on-site support, which reduces deployment risk significantly.
When specifying APs for hire or purchase, prioritise WiFi 6 (802.11ax) hardware for any deployment above 200 users. The OFDMA and BSS Colouring features of WiFi 6 provide meaningful performance improvements in high-density environments compared to WiFi 5 (802.11ac).
Phase 3: Pre-Event Configuration and Testing (1–2 Weeks Before Event)
Configure all network equipment in a staging environment before arriving on site. This includes VLAN configuration on the core switch, SSID-to-VLAN mapping on the wireless controller, DHCP scope configuration, and captive portal integration. Testing in a staging environment is far more efficient than troubleshooting on the day of the event.
For captive portal configuration, integrate Purple's platform at this stage. Configure the branded splash page, the authentication method (email, social login, or SMS), the consent workflow, and any post-authentication redirect. Test the full user journey on multiple device types — iOS, Android, Windows, and macOS all handle captive portal detection differently, and each has specific requirements for the redirect mechanism to work correctly.
Conduct a load test using a WiFi client simulator to validate that the DHCP scope, the authentication backend, and the uplink can handle the expected peak load. Tools such as Spirent or Ixia can simulate hundreds of concurrent WiFi clients for this purpose.
Phase 4: On-Site Deployment (Day Before Event)
Arrive on site with sufficient time to complete installation and testing before the venue opens to attendees. Mount APs according to the site survey plan — ceiling mounting is preferred for omnidirectional coverage; wall mounting is acceptable where ceiling access is not available. Run and label all cabling, and document the physical location of every AP with a photograph and a floor plan annotation.
Once all hardware is installed, conduct a post-installation survey using a laptop or dedicated survey device to validate coverage. Walk the entire attendee area and confirm signal strength of -65 dBm or better throughout. Identify and address any coverage gaps before the event opens.
Test the end-to-end user journey: connect a test device to each SSID, complete the captive portal authentication, and verify that internet access is available. Test card payment terminals on the staff VLAN. Confirm that AV equipment on the production VLAN can reach all required destinations.
Phase 5: On-Site Management and Monitoring
During the event, monitor the network in real time using the wireless controller's management dashboard. Key metrics to watch are: AP association counts (flag any AP that exceeds 80% of its recommended client capacity), channel utilisation, DHCP pool utilisation, and uplink throughput. Purple's WiFi Analytics platform provides an additional layer of visibility into user behaviour — dwell time, peak connection periods, and portal conversion rates — which is valuable both for real-time management and for post-event reporting.
Have a clear escalation process for network issues. Designate a single point of contact for all network-related support requests from event staff, and ensure that the on-site network engineer has remote access to all equipment via an out-of-band management connection that is independent of the guest network.
Best Practices
The following recommendations represent vendor-neutral best practices derived from large-scale event deployments across hospitality , retail , and conference environments.
Disable SSID broadcasting for staff and production networks. There is no operational reason for these SSIDs to be visible to attendees. Hiding them reduces the attack surface and prevents accidental connections.
Set aggressive DHCP lease times on the guest VLAN. A lease time of 30–60 minutes ensures that IP addresses from disconnected devices are reclaimed promptly. This is particularly important at multi-day events where the attendee population changes significantly between sessions.
Implement 802.1X authentication on staff and production VLANs. WPA3-Enterprise with 802.1X provides per-user authentication and eliminates the risk of a shared pre-shared key being compromised. For guest networks, WPA3-Personal or an open network with a captive portal is the standard approach.
Use DNS-over-HTTPS or DNS filtering on the guest VLAN. Public event networks are a target for DNS hijacking and phishing attacks. Applying DNS filtering — either through your upstream provider or through a dedicated DNS security service — provides a meaningful layer of protection for attendees. Purple's platform integrates with DNS security providers to apply this filtering at the captive portal layer.
Document everything. Create a network diagram, a cabling schedule, and an AP placement map before you arrive on site. This documentation is invaluable for troubleshooting during the event and for planning future deployments at the same venue.
For airport and transport hub deployments, additional security considerations apply — Purple's guide on airport WiFi security covers the specific threat model and mitigation strategies relevant to high-footfall public environments.
Troubleshooting and Risk Mitigation
DHCP Pool Exhaustion
This is the most common failure mode in event WiFi. Symptoms include devices that connect to the WiFi but cannot obtain an IP address, or that receive an APIPA address (169.254.x.x). The fix is to increase the DHCP scope size and reduce the lease time. Prevention is straightforward: size your DHCP scope to at least twice the expected peak client count and set lease times to 30–60 minutes.
Authentication Server Overload
At peak load, a large number of simultaneous authentication requests can overwhelm an on-premises RADIUS server or captive portal backend. This manifests as slow or failed logins. Cloud-hosted platforms like Purple auto-scale to handle burst loads, which is a significant architectural advantage over on-premises deployments for event use cases.
Co-Channel Interference
If multiple APs are operating on the same channel in close proximity, performance degrades significantly. Symptoms include low throughput despite good signal strength, and high retry rates visible in the wireless controller. The fix is to review channel assignments and ensure that adjacent APs are on non-overlapping channels. Reducing transmit power also helps by shrinking the interference radius of each AP.
Captive Portal Redirect Failures
Different operating systems use different mechanisms to detect captive portals. iOS uses a dedicated CNA (Captive Network Assistant) that makes HTTP requests to specific Apple URLs. Android uses a similar mechanism with Google's connectivity check servers. If your captive portal does not respond correctly to these probes, the portal will not open automatically and users will need to manually navigate to the portal URL. Ensure your captive portal is configured to intercept and respond to these specific probe requests.
Uplink Failure
A single point of failure on the uplink is the highest-impact risk in an event deployment. Mitigate this by provisioning a 4G/5G backup connection that activates automatically if the primary leased line fails. Most enterprise routers support dual-WAN failover with sub-second switchover times. Test the failover mechanism during the pre-event setup, not during the event itself.
ROI and Business Impact
Event WiFi is increasingly recognised not just as a utility but as a data asset. Every attendee who connects to your event network and authenticates through a captive portal is providing first-party data — email address, demographic information, and behavioural data — that has significant commercial value for event organisers, venue operators, and sponsors.
Purple's WiFi Analytics platform quantifies this value directly. Post-event reports provide data on total unique connections, peak concurrent users, average session duration, portal conversion rates, and opt-in rates for marketing communications. For a 2,000-attendee conference with a 70% portal opt-in rate, that represents 1,400 new, consented marketing contacts captured in a single event — a cost per acquisition that is difficult to match through any other channel.
For venue operators in the hospitality sector, the analytics layer provides additional value through footfall analysis and dwell time mapping. Understanding which areas of a venue attract the most engagement — and for how long — informs layout decisions, F&B placement, and sponsor positioning for future events.
The ROI calculation for event WiFi investment should account for three categories of return: operational (reduced support costs from a well-designed network versus an ad-hoc one), commercial (first-party data capture and marketing opt-ins), and reputational (the brand value of a reliable, fast network that enhances the attendee experience). For large-scale events, the commercial return alone typically justifies the infrastructure investment within two or three events.
Key Terms & Definitions
Access Point (AP)
A hardware device that creates a wireless local area network (WLAN) by transmitting and receiving WiFi signals. In event deployments, enterprise-grade APs are used rather than consumer devices, as they support multiple SSIDs, VLAN tagging, centralised management, and higher concurrent client counts.
IT teams encounter AP specifications when sizing a deployment. Key parameters are the maximum concurrent client count (typically 100–200 for enterprise APs), the supported WiFi standard (802.11ax/WiFi 6 is current best practice), and the ingress protection rating (IP55+ for outdoor use).
VLAN (Virtual Local Area Network)
A logical network segment created within a physical network infrastructure using IEEE 802.1Q tagging. VLANs allow multiple isolated networks to share the same physical switches and cabling, with traffic between VLANs controlled by routing policies.
VLANs are the primary mechanism for network segmentation in event deployments. Separating guest, staff, and production traffic onto different VLANs is both a performance best practice and a PCI DSS compliance requirement where card payments are involved.
Captive Portal
A web page presented to users when they first connect to a WiFi network, requiring authentication or acceptance of terms before internet access is granted. Captive portals are the standard mechanism for guest WiFi access control, GDPR consent capture, and first-party data collection.
The captive portal is the user's first interaction with the event network. Its performance under load — particularly during peak authentication bursts — directly affects the attendee experience. Cloud-hosted portals like Purple's platform scale automatically to handle burst loads.
DHCP (Dynamic Host Configuration Protocol)
A network protocol that automatically assigns IP addresses to devices when they connect to a network. The DHCP server maintains a pool of available addresses (the scope) and assigns them to clients for a defined period (the lease time).
DHCP pool exhaustion — where all available IP addresses are in use and new devices cannot connect — is the most common failure mode in event WiFi. Correct scope sizing and lease time configuration are critical planning steps.
Leased Line
A dedicated, synchronous, uncontended data connection between two points, provided by a telecommunications carrier with a guaranteed Service Level Agreement (SLA). Unlike broadband, a leased line provides equal upload and download speeds and is not shared with other customers.
A leased line is the recommended uplink for event WiFi deployments above 200 attendees. The key differentiator from broadband is the SLA guarantee and the uncontended nature of the connection. Provisioning typically takes 4–6 weeks.
802.11ax (WiFi 6)
The current generation WiFi standard, introducing OFDMA (Orthogonal Frequency Division Multiple Access) and MU-MIMO (Multi-User Multiple Input Multiple Output) to improve performance in high-density environments. WiFi 6 allows an AP to serve multiple clients simultaneously on the same channel, rather than sequentially.
WiFi 6 is the recommended standard for event deployments above 200 users. Its high-density performance improvements over WiFi 5 (802.11ac) are most pronounced in exactly the kind of environment that event WiFi creates: many clients, high contention, mixed device types.
GDPR (General Data Protection Regulation)
EU regulation (2016/679) governing the collection, processing, and storage of personal data. For event WiFi, GDPR requires a lawful basis for data collection, a clear privacy notice, explicit and granular consent for marketing use, and the ability to demonstrate compliance through consent records.
Any event WiFi deployment that collects personal data — email addresses, social login tokens, or device identifiers — must comply with GDPR. The captive portal is the primary compliance enforcement point. Consent for WiFi access and consent for marketing communications must be separate, granular opt-ins.
PCI DSS (Payment Card Industry Data Security Standard)
A set of security standards mandating how organisations that process, store, or transmit card payment data must protect that data. PCI DSS requires that cardholder data environments are network-segmented from any public-facing systems.
Any event that processes card payments — ticketing, F&B, merchandise — must ensure that payment systems are on a network segment that is completely isolated from the guest WiFi network. Placing payment terminals on the same VLAN as public WiFi is a PCI DSS compliance failure.
Band Steering
A wireless network feature that actively encourages dual-band capable client devices to connect to the 5 GHz band rather than 2.4 GHz, by delaying or declining association requests on 2.4 GHz from clients that are capable of 5 GHz.
In high-density event environments, the 2.4 GHz spectrum quickly becomes saturated. Band steering is a standard configuration on enterprise APs that reduces 2.4 GHz congestion by pushing capable clients to the less congested 5 GHz band.
QoS (Quality of Service)
Network traffic management techniques that prioritise certain types of traffic over others, ensuring that high-priority applications receive the bandwidth and latency they require even when the network is congested.
QoS is used in event deployments to guarantee bandwidth for production and press VLANs, and to limit the per-user throughput on the guest VLAN to prevent individual heavy users from degrading the experience for all attendees.
Case Studies
A 3,000-seat conference centre is hosting a two-day technology summit. The event includes a 2,500-person keynote hall, 12 breakout rooms of 50–150 people each, an exhibition floor with 80 exhibitor stands, and a press room with 30 journalists requiring reliable high-throughput connectivity. The venue has existing Cat6 cabling throughout but only a 200 Mbps shared broadband connection. How should the network be designed?
The first priority is backhaul. A 200 Mbps shared broadband connection is wholly inadequate for this event. A dedicated leased line of at least 2 Gbps should be ordered immediately — this is the critical path item with a 4–6 week lead time. A 4G/5G bonded backup should be provisioned as a failover.
For the wireless architecture, the keynote hall requires the most careful planning. With 2,500 potential concurrent users, plan for 60–80 APs in the hall alone, deployed at high density with reduced transmit power (8–10 dBm) and manually assigned channels. WiFi 6 APs are essential at this scale.
VLAN design: VLAN 10 (Guest/Attendee), VLAN 20 (Staff/Registration), VLAN 30 (Exhibitor), VLAN 40 (Press/Production), VLAN 50 (AV/Broadcast). The press VLAN should have guaranteed bandwidth allocation via QoS — budget 5 Mbps per journalist for video upload capability.
For exhibitors, provision a separate SSID on VLAN 30 with WPA2-PSK and a unique password per stand distributed at registration. This prevents exhibitors from accessing each other's networks while keeping the provisioning process manageable.
DHCP: Use a /20 scope for the guest VLAN (4,094 usable addresses), /24 for each operational VLAN. Set guest lease time to 30 minutes.
Captive portal: Deploy Purple's Guest WiFi platform on the attendee VLAN with email or social login authentication, a branded splash page, and explicit GDPR consent for post-event marketing. Estimated opt-in yield at 65–70%: approximately 1,600–1,750 consented marketing contacts.
A major retail chain is running a three-day outdoor pop-up event in a city centre square. Expected footfall is 500–800 visitors per day. The event includes a product demonstration area, a payment kiosk, and a social media activation zone where visitors are encouraged to share content. There is no fixed infrastructure — no cabling, no power, no existing network. How do you provision connectivity?
With no fixed infrastructure, the deployment must be entirely self-contained. The network stack consists of: a 5G bonded router (using SIM cards from two different carriers for resilience) providing the uplink; a managed PoE switch powered from a generator or portable UPS; and outdoor-rated WiFi 6 APs with IP67 ingress protection mounted on temporary rigging or event structures.
For an outdoor environment, use directional sector antennas rather than omnidirectional APs to focus coverage on the event footprint and minimise interference with the surrounding area. Position APs at height — 4–6 metres — to maximise coverage radius while reducing ground-level interference.
VLAN design: VLAN 10 (Visitor WiFi with captive portal), VLAN 20 (Staff and Payment Kiosk — PCI DSS scoped), VLAN 30 (Social Media Activation Zone — higher bandwidth allocation). The payment kiosk VLAN must be completely isolated from visitor traffic and should use a wired connection to the PoE switch rather than WiFi where possible.
For the social media activation zone, configure QoS to prioritise upload traffic (Instagram, TikTok uploads are upload-heavy) and ensure the uplink has sufficient headroom. At 800 concurrent visitors with 10% actively uploading content at any given time, budget 5 Mbps per active uploader: 80 users × 5 Mbps = 400 Mbps upload capacity required.
Captive portal: Deploy Purple's platform with a branded splash page tied to the campaign. Collect email addresses and social handles, with opt-in for post-event follow-up. The social media activation zone can be configured to automatically redirect authenticated users to the campaign hashtag page.
For weather resilience, all equipment should be housed in weatherproof enclosures rated to IP65 or above. Have a spare AP and spare PoE injector on site for rapid replacement.
Scenario Analysis
Q1. You are the IT director for a conference centre that hosts 20 events per year, ranging from 50-person boardroom meetings to 1,500-person annual conferences. The venue currently has a 500 Mbps shared broadband connection and a mix of consumer-grade WiFi routers installed by the previous IT team. Attendee complaints about WiFi quality are increasing. What is your infrastructure upgrade roadmap, and what is the business case for the investment?
💡 Hint:Consider the range of event sizes and the different network requirements for each. Think about whether a single infrastructure can serve all event types, or whether a tiered approach is needed. The business case should address both the cost of the current situation (complaints, lost business) and the revenue opportunity (data capture, premium WiFi as a service offering).
Show Recommended Approach
The upgrade roadmap has three components. First, replace the shared broadband with a dedicated leased line of at least 1 Gbps — this is the single highest-impact change and addresses the root cause of most performance complaints. Second, replace the consumer WiFi routers with a managed enterprise wireless infrastructure: a wireless controller, enterprise-grade APs deployed according to a proper site survey, and a managed PoE switch. For a venue of this size, 20–30 APs covering all event spaces is a reasonable starting point. Third, deploy a captive portal platform — Purple's Guest WiFi solution — to provide branded authentication, GDPR-compliant data capture, and analytics reporting.
The business case has two components. The cost of the current situation includes reputational damage from poor WiFi (quantifiable through attendee feedback scores), potential lost bookings from event organisers who specify WiFi quality in their venue requirements, and the IT team time spent responding to complaints. The revenue opportunity includes first-party data capture from every event (at 20 events per year with average 500 attendees and 65% opt-in, that is 6,500 new marketing contacts per year), the ability to offer premium WiFi as a billable service to event organisers, and the analytics data that informs venue layout and F&B decisions.
Q2. An outdoor music festival with 8,000 attendees has hired your company to provide event WiFi services. The site is a greenfield location with no existing infrastructure — no power, no cabling, no fixed structures. The event runs for three days. What are the five highest-risk items in this deployment, and how do you mitigate each one?
💡 Hint:Think about the dependencies that are most likely to fail in an outdoor, infrastructure-free environment. Consider weather, power, connectivity, hardware failure, and human factors. For each risk, think about both prevention and contingency.
Show Recommended Approach
Risk 1 — Uplink failure: With no fixed infrastructure, a leased line is not an option. The mitigation is a bonded 5G solution using SIM cards from at least two different carriers, with automatic failover. Budget for 4–5 SIM cards across carriers with the best coverage at the specific site location (verify this with a site visit before the event). Risk 2 — Power failure: All network equipment runs from generators. The mitigation is a UPS (uninterruptible power supply) between the generator and the network equipment, providing 15–30 minutes of runtime during generator transitions or refuelling. Have a spare generator on site. Risk 3 — Hardware failure: In an outdoor environment, hardware failure rates are higher due to weather, vibration, and physical damage. Bring 20% spare hardware — spare APs, spare PoE injectors, spare patch cables. Document the configuration of every device so that a replacement can be provisioned in under 10 minutes. Risk 4 — Weather damage: All outdoor hardware must be IP67 rated. All cabling must be run in conduit or cable management rated for outdoor use. All equipment enclosures must be sealed and elevated off the ground to prevent water ingress. Risk 5 — DHCP exhaustion: At 8,000 attendees, a standard DHCP scope will fail. Configure a /19 subnet (8,190 usable addresses) with a 30-minute lease time. Monitor the DHCP pool utilisation in real time and have a plan to expand the scope if utilisation exceeds 80%.
Q3. A legal conference is using your event WiFi service. The event organiser wants to collect attendee email addresses through the captive portal and use them for post-event marketing. The event has attendees from both the UK and the EU. What GDPR compliance requirements apply, and how should the captive portal be configured to meet them?
💡 Hint:Consider the distinction between the lawful basis for providing WiFi access and the lawful basis for marketing communications. Think about what information must be presented to users, what consent records must be kept, and how the rights of data subjects are handled.
Show Recommended Approach
Under GDPR (and the UK GDPR post-Brexit), the collection of email addresses and their use for marketing requires explicit, informed, and freely given consent. The captive portal must be configured as follows. First, the splash page must include a clear privacy notice that identifies the data controller (the event organiser), specifies what data is collected, how it will be used, and how long it will be retained. Second, consent for WiFi access and consent for marketing communications must be separate opt-ins — a single checkbox that conflates the two is non-compliant. Users must be able to access the WiFi without consenting to marketing. Third, the marketing opt-in checkbox must be unchecked by default (no pre-ticked boxes). Fourth, the consent record — including the timestamp, the IP address, and the specific consent text presented — must be stored and retrievable, as required by Article 7(1) GDPR. Fifth, the privacy notice must include information about data subject rights (access, erasure, portability) and provide a contact mechanism for exercising those rights. Purple's Guest WiFi platform handles all of these requirements natively, storing consent records with full audit trail and providing a compliant consent workflow out of the box. For a UK/EU mixed audience, the same GDPR standard applies to both — UK GDPR and EU GDPR are substantively identical in their consent requirements.



