Apple CNA, Android Connectivity Check, Microsoft NCSI: How Captive Portal Detection Actually Works
This definitive technical reference explains how Apple CNA, Android connectivitycheck, and Microsoft NCSI detect captive portals. It provides actionable guidance for IT managers and network architects on walled garden configuration, common failure modes, and best practices for seamless deployment.
🎧 Listen to this Guide
View Transcript
- Executive Summary
- Technical Deep-Dive
- Apple Captive Network Assistant (CNA)
- Android Connectivity Check
- Microsoft Network Connectivity Status Indicator (NCSI)
- Implementation Guide
- Walled Garden Configuration
- Deployment Steps
- Best Practices
- Troubleshooting & Risk Mitigation
- ROI & Business Impact
- References
Executive Summary
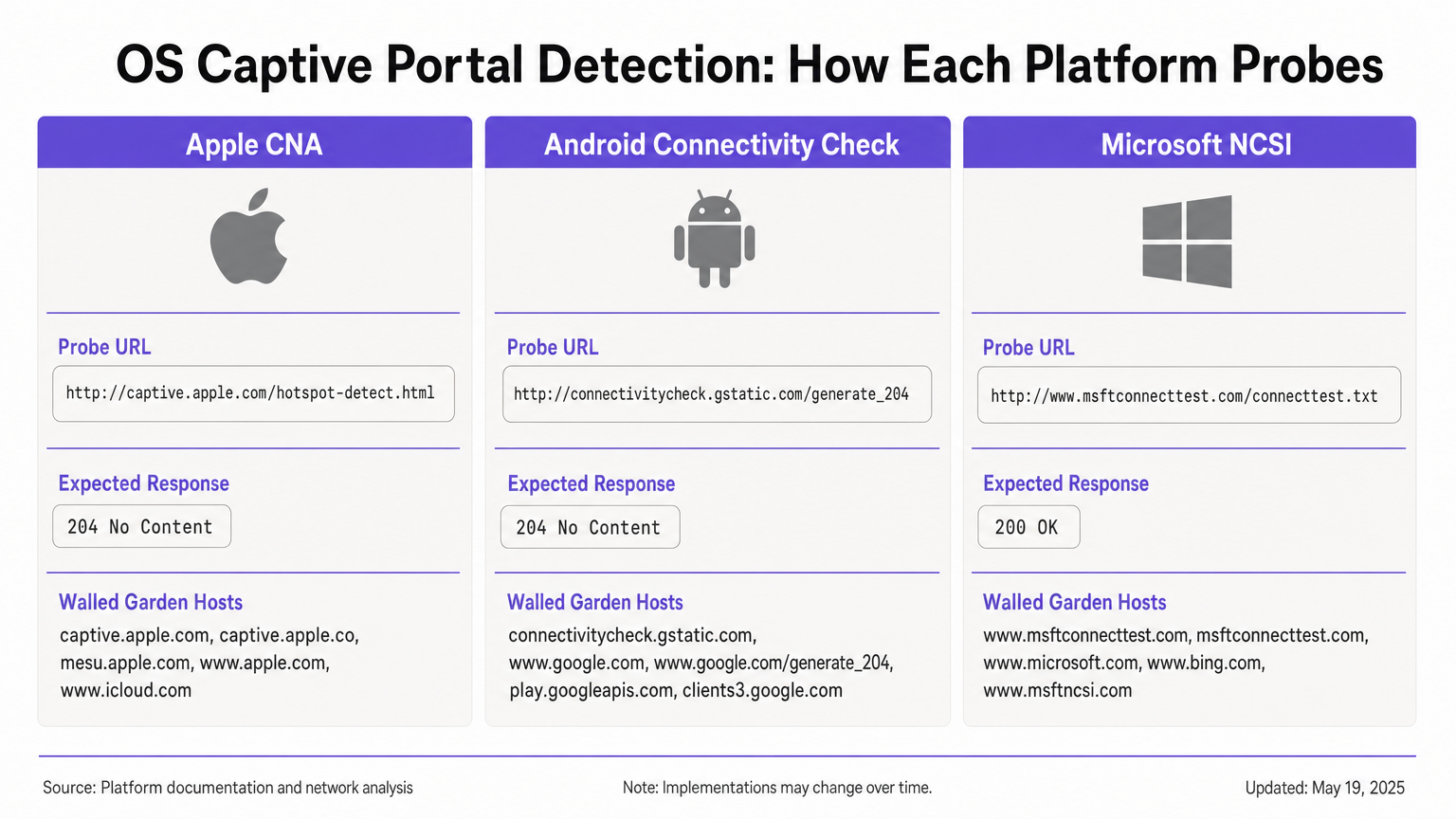
Captive portal detection is a critical yet frequently misunderstood component of enterprise networking. When a device joins a public WiFi network, the operating system runs a series of background probes to determine if internet access is available or if a captive portal is intercepting traffic. Apple, Android, and Windows each use distinct mechanisms—with different probe URLs, expected responses, and failure modes.
For IT managers and network architects deploying Guest WiFi solutions in Hospitality , Retail , or public-sector environments, misconfiguring these detection mechanisms leads to significant support overhead. Guests may see certificate warnings, fail to see the splash page, or experience endless sign-in loops. This reference guide provides the definitive technical architecture of Apple CNA, Android Connectivity Check, and Microsoft NCSI, equipping you with the actionable knowledge required to build robust, vendor-neutral walled gardens and ensure a seamless connection experience.
Technical Deep-Dive
Apple Captive Network Assistant (CNA)
When an Apple device (iOS or macOS) connects to a network, it immediately sends an HTTP GET request to its primary probe URL: http://captive.apple.com/hotspot-detect.html. The device expects an HTTP 200 OK response with a specific HTML body containing the word "Success" [1].
If the response matches this expectation, the OS assumes full internet access. If the response is anything else—such as an HTTP 302 redirect or a timeout—the OS triggers the Captive Network Assistant (CNA). The CNA opens WebSheet, a sandboxed mini-browser with limited functionality (no Safari extensions, no password saving) [2].
Critical constraint: The initial probe is HTTP. If your gateway intercepts the probe and redirects to an HTTPS URL, the CNA will fail gracefully, often resulting in a certificate warning or a blank screen. The initial redirect must remain on HTTP port 80. Furthermore, if you inadvertently allow captive.apple.com through your walled garden, the device will reach the real Apple server, receive the "Success" response, and bypass your portal entirely.
Android Connectivity Check
Android operates on a different principle. Its primary probe targets http://connectivitycheck.gstatic.com/generate_204 (with fallbacks to clients2.google.com and connectivitycheck.android.com). Instead of expecting an HTTP 200 response with specific content, Android expects an HTTP 204 No Content response [3].
If Android receives an HTTP 204, it assumes internet connectivity. If it receives a redirect or an HTTP 200 response, it flags the network as captive and displays a "Sign in to WiFi network" notification. Tapping this notification opens the full Chrome browser, allowing for a richer portal experience compared to Apple's sandboxed CNA.
Critical constraint: If your walled garden blocks connectivitycheck.gstatic.com entirely rather than intercepting and redirecting it, Android will display a "Connected, no internet" warning and will not prompt the user to sign in.
Microsoft Network Connectivity Status Indicator (NCSI)
Windows employs a dual-probe mechanism via the Network Connectivity Status Indicator (NCSI) service. Upon connection, Windows performs an HTTP GET request to http://www.msftconnecttest.com/connecttest.txt (expecting a 200 response with the text "Microsoft Connect Test") and a DNS resolution for dns.msftncsi.com [4].
If the HTTP probe is intercepted, Windows detects the portal and opens the default browser (Edge). However, Windows is prone to a post-authentication looping issue. After the user authenticates, Windows re-runs the NCSI probes. If the gateway has not yet propagated the MAC address authorisation, the probe is intercepted again, and Windows re-opens the portal, forcing the user into a sign-in loop.
Implementation Guide
To ensure reliable captive portal detection across all devices, you must configure your pre-authentication zone (walled garden) to handle the specific requirements of each OS.
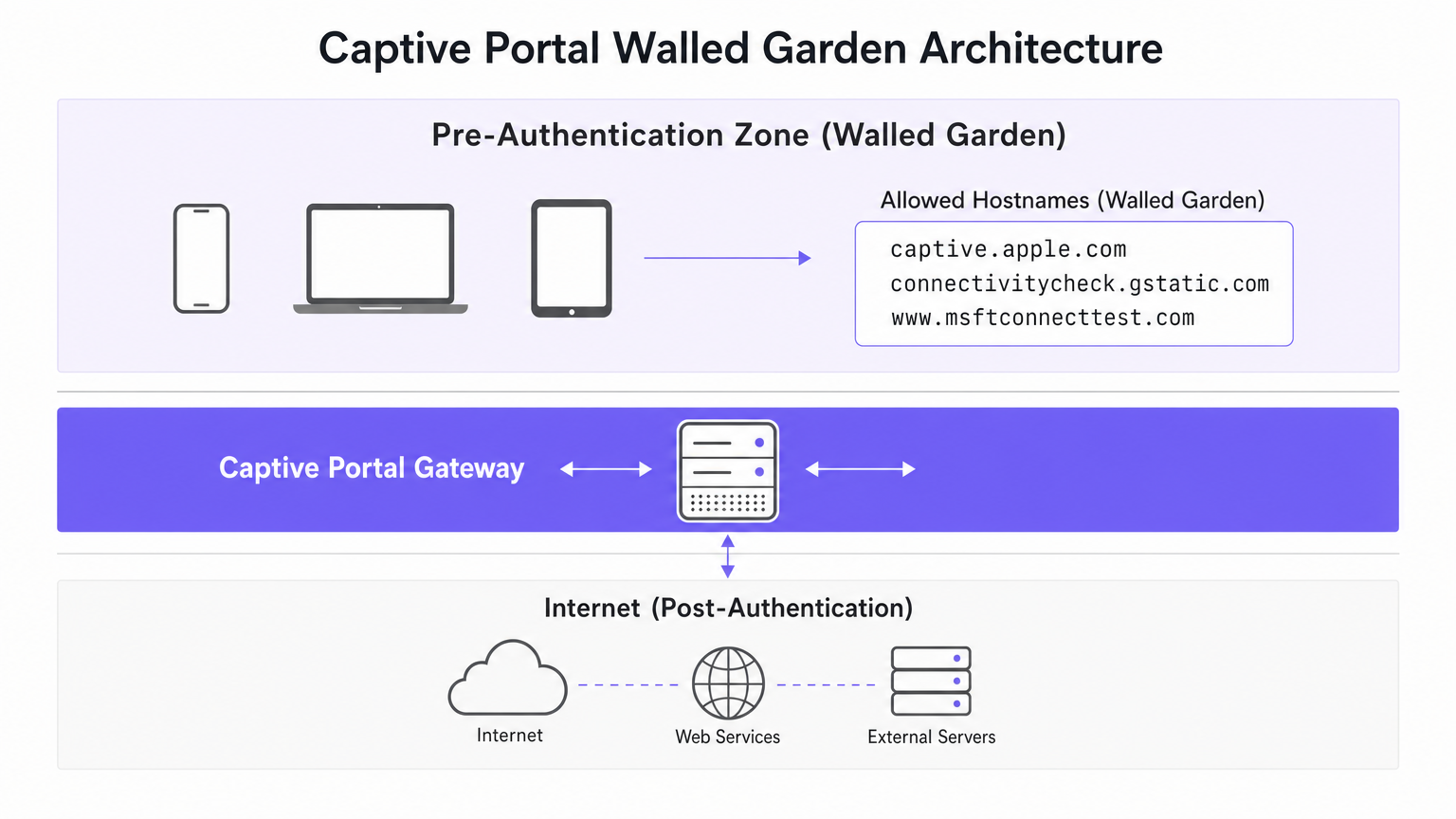
Walled Garden Configuration
Your walled garden must include the following hosts. Crucially, you must intercept and redirect HTTP traffic to these hosts, rather than simply allowing them to pass through to the internet.
- Apple:
captive.apple.com,www.apple.com,www.appleiphonecell.com,www.itools.info - Android:
connectivitycheck.gstatic.com,clients2.google.com,connectivitycheck.android.com - Windows:
www.msftconnecttest.com,dns.msftncsi.com,www.msftncsi.com(for legacy clients)
Deployment Steps
- Configure DNS Resolution: Ensure that DNS requests for the probe URLs resolve successfully within the pre-authentication zone.
- Intercept HTTP Probes: Configure your gateway to intercept HTTP GET requests to the probe URLs and return an HTTP 302 redirect to your portal's splash page.
- Maintain HTTP for Initial Redirect: The initial redirect must be served over HTTP (port 80). You may redirect the user to an HTTPS login page subsequently, but the first hop must be plaintext HTTP to satisfy Apple CNA.
- Propagate Authorisation Rapidly: Ensure your gateway immediately updates its firewall rules upon successful authentication to allow NCSI probes to pass through, preventing Windows loops.
Best Practices
- Adopt RFC 8910 (Captive Portal API): Modern operating systems (iOS 16+, Android 11+) support DHCP option 114, which provides a positive signal of a captive portal's presence via a designated API URL [5]. This eliminates reliance on probe interception and is the recommended future-proof approach.
- Test Across All Platforms: Never assume a portal works based solely on testing with an iPhone. Mandate a testing matrix that includes iOS, stock Android, and Windows 10/11 devices.
- Leverage Automated Platforms: Managing evolving probe URLs manually is error-prone. Platforms like Purple automatically update walled garden definitions as Apple, Google, and Microsoft modify their infrastructure, ensuring consistent WiFi Analytics data collection.
Troubleshooting & Risk Mitigation
| Symptom | Root Cause | Resolution |
|---|---|---|
| Apple CNA fails to open; user sees SSL warning. | Gateway intercepts probe and redirects directly to HTTPS. | Ensure the initial interception and redirect use HTTP port 80. |
| Apple device connects without showing portal. | captive.apple.com is allowed through the walled garden to the internet. |
Remove captive.apple.com from the allowlist; ensure it is intercepted. |
| Android shows "Connected, no internet". | connectivitycheck.gstatic.com is blocked by the firewall. |
Allow the probe URL in the walled garden, but intercept and redirect it. |
| Windows prompts user to sign in multiple times (looping). | Gateway is slow to apply post-authentication MAC rules; NCSI is still intercepted. | Optimise gateway rule propagation; ensure msftconnecttest.com passes post-auth. |
ROI & Business Impact
A robust captive portal detection architecture directly impacts the bottom line. In a 500-room hotel or a large retail environment, captive portal failures generate a disproportionate volume of IT support tickets. By eliminating these friction points, venues reduce support overhead, improve guest satisfaction scores, and increase the capture rate of first-party data.
When users seamlessly connect, they engage with your splash pages, enabling you to deliver targeted marketing, integrate with loyalty programs, and drive measurable revenue—as detailed in our guide to Indoor Positioning System: UWB, BLE, & WiFi Guide . For venues operating internationally, a reliable portal ensures consistent compliance data collection, supporting frameworks discussed in the Brazil LGPD and Guest WiFi: A Compliance Guide .
References
[1] Apple Support, "Use captive Wi-Fi networks on your iPhone or iPad," 2024. [2] SecureW2, "What Is Apple Captive Network Assistant?," 2023. [3] Android Developers, "Captive portal API support," Android 11 Features, 2020. [4] Microsoft Learn, "Captive Portal Detection and User Experience in Windows," Windows Hardware Developer, 2025. [5] IETF, "RFC 8910: Captive-Portal Identification in DHCP and Router Advertisements," 2020.
Key Terms & Definitions
Captive Network Assistant (CNA)
Apple's built-in mechanism for detecting captive portals and displaying them in a sandboxed mini-browser (WebSheet) rather than the full Safari browser.
IT teams must ensure their splash pages are responsive and do not rely on advanced browser features, as the CNA environment is highly constrained.
Network Connectivity Status Indicator (NCSI)
The Windows service responsible for determining internet connectivity by probing specific Microsoft domains via HTTP and DNS.
Understanding NCSI is critical for preventing the common 'Windows looping' issue where users are repeatedly prompted to sign in.
Walled Garden
A restricted network environment that allows unauthenticated users access to a specific list of approved hostnames or IP addresses.
Properly configuring the walled garden is the foundation of captive portal deployment, ensuring OS probes are handled correctly.
HTTP 204 No Content
An HTTP status code indicating the server successfully processed the request but is not returning any content.
This is the specific response Android devices expect from `connectivitycheck.gstatic.com` to confirm full internet access.
RFC 8910 (Captive Portal API)
An IETF standard that uses DHCP option 114 to explicitly notify a device of a captive portal's presence and provide the portal URL.
This modern standard replaces unreliable probe interception and is supported by newer versions of iOS and Android.
WebSheet
The sandboxed, limited-functionality mini-browser used by Apple's CNA to render captive portal splash pages.
Portal designers must test their pages in WebSheet, as it lacks features like password saving and full cookie support found in standard browsers.
MAC Authorisation
The process by which a gateway grants network access to a specific device based on its Media Access Control address after successful portal authentication.
Delays in applying MAC authorisation cause post-authentication probes (like Windows NCSI) to fail, leading to poor user experiences.
Probe Interception
The technique of capturing an operating system's background connectivity check and forcibly redirecting it to a captive portal login page.
This is the legacy, yet most common, method for triggering captive portals, requiring precise HTTP 302 redirects.
Case Studies
A 300-room hotel reports that guests using iPhones are connecting to the guest WiFi but are not being prompted with the captive portal splash page. Android and Windows users are unaffected.
- Review the walled garden (pre-authentication) allowlist on the gateway.
- Identify that
captive.apple.comhas been added as a permitted passthrough host. - Remove
captive.apple.comfrom the passthrough list. - Configure the gateway to intercept HTTP requests to
captive.apple.comand redirect them (via HTTP 302) to the portal URL.
A conference centre's IT team receives complaints that Windows 11 users are authenticating successfully but are immediately prompted to sign in again, creating an endless loop.
- Verify that the captive portal gateway is successfully authorising the client's MAC address post-authentication.
- Inspect the post-authentication firewall rules to ensure traffic to
www.msftconnecttest.comanddns.msftncsi.comis permitted. - Adjust the gateway configuration to ensure MAC authorisation is applied instantaneously, preventing subsequent NCSI probes from being intercepted.
Scenario Analysis
Q1. You are deploying a captive portal for a large retail chain. The security team insists that all network traffic, including the initial portal redirect, must be encrypted using HTTPS. What is the technical implication of this policy?
💡 Hint:Consider how Apple's Captive Network Assistant (CNA) handles initial probe requests.
Show Recommended Approach
Enforcing HTTPS for the initial redirect will break Apple CNA detection. The CNA probe is an HTTP GET request. If the gateway intercepts this and redirects to an HTTPS URL, the CNA will not follow the redirect gracefully, resulting in a certificate error or a failure to open the portal. The initial interception must use HTTP port 80; the user can subsequently be redirected to an HTTPS page for authentication.
Q2. A stadium network engineer reports that Android devices are showing a 'Connected, no internet' warning without prompting the user to sign in. How should the walled garden be adjusted?
💡 Hint:Think about the difference between blocking a probe and intercepting it.
Show Recommended Approach
The engineer needs to ensure that connectivitycheck.gstatic.com is allowed to resolve via DNS within the walled garden, but the HTTP traffic must be intercepted and redirected. Currently, the firewall is likely dropping the traffic entirely, causing Android to assume the internet is down rather than detecting a captive portal.
Q3. A venue wishes to implement RFC 8910 (Captive Portal API) to improve the user experience. What infrastructure changes are required to support this?
💡 Hint:RFC 8910 relies on a positive signal during the IP assignment phase.
Show Recommended Approach
The venue must update its DHCP server or access points to advertise DHCP option 114. This option must provide the URL of the Captive Portal API endpoint. When compatible devices (iOS 16+, Android 11+) receive this option during the DHCP handshake, they will immediately fetch the API and prompt the user, bypassing the need for HTTP probe interception.



